diff options
Diffstat (limited to '')
112 files changed, 14794 insertions, 0 deletions
diff --git a/packaging/PLATFORM_SUPPORT.md b/packaging/PLATFORM_SUPPORT.md new file mode 100644 index 0000000..106c808 --- /dev/null +++ b/packaging/PLATFORM_SUPPORT.md @@ -0,0 +1,179 @@ +<!-- +title: "Netdata platform support policy" +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/PLATFORM_SUPPORT.md +--> + +# Netdata platform support policy + +Netdata defines three tiers of official support: + +- [Core](#core) +- [Intermediate](#intermediate) +- [Community](#community) + +Each tier defines different guarantees for platforms in that tier, described below in the section about that tier. + +Additionally, we define two categories for special cases that we do not support: + +- [Third-party supported platforms](#third-party-supported-platforms) +- [Previously supported platforms](#previously-supported-platforms) + +These two categories are explained further below. + +Any platforms not listed in any of these categories may or may not work. + +The following table shows a general outline of the various support tiers and categories. + +| | Bug Support | Guaranteed Configurations | CI Coverage | Native Packages | Static Build Support | +| - | ----------- | ------------------------- | ----------- | --------------- | -------------------- | +| Core | High priority | Everything but rare edge cases | Full | Yes, if we can provide them | Full | +| Intermediate | Normal priority | Common cases | Partial (CI mostly equivalent to **Core**, but possibly with some gaps, and not required to pass) | Possibly | Full | +| Community | Best Effort | Default only | None | No | Best Effort | +| Third-party Supported | Users directed to platform maintainers | None | None | No | Best Effort | +| Previously Supported | Users asked to upgrade | None | None | Yes, but only already published versions | Best Effort | + +- ‘Bug Support’: How we handle of platform-specific bugs. +- ‘Guaranteed Configurations’: Which runtime configurations for the agent we try to guarantee will work with minimal effort from users. +- ‘CI Coverage’: What level of coverage we provide for the platform in CI. +- ‘Native Packages’: Whether we provide native packages for the system package manager for the platform. +- ‘Static Build Support’: How well our static builds are expected to work on the platform. + +## Currently supported platforms + +### Core + +Platforms in the core support tier are our top priority. They are covered rigorously in our CI, usually +include official binary packages, and any platform-specific bugs receive a high priority. From the perspective +of our developers, platforms in the core support tier _must_ work, with almost no exceptions. Our [static +builds](#static-builds) are expected to work on these platforms if available. Source-based installs are expected +to work on these platforms with minimal user effort. + +| Platform | Version | Official Native Packages | Notes | +| -------- | ------- | ------------------------ | ----- | +| Alpine Linux | 3.17 | No | The latest release of Alpine Linux is guaranteed to remain at **Core** tier due to usage for our Docker images | +| Alma Linux | 9.x | x86\_64, AArch64 | Also includes support for Rocky Linux and other ABI compatible RHEL derivatives | +| Alma Linux | 8.x | x86\_64, AArch64 | Also includes support for Rocky Linux and other ABI compatible RHEL derivatives | +| CentOS | 7.x | x86\_64 | | +| Docker | 19.03 or newer | x86\_64, i386, ARMv7, AArch64, POWER8+ | See our [Docker documentation](/packaging/docker/README.md) for more info on using Netdata on Docker | +| Debian | 11.x | x86\_64, i386, ARMv7, AArch64 | | +| Debian | 10.x | x86\_64, i386, ARMv7, AArch64 | | +| Fedora | 37 | x86\_64, AArch64 | | +| Fedora | 36 | x86\_64, ARMv7, AArch64 | | +| Fedora | 35 | x86\_64, ARMv7, AArch64 | | +| openSUSE | Leap 15.4 | x86\_64, AArch64 | | +| openSUSE | Leap 15.3 | x86\_64, AArch64 | | +| Oracle Linux | 9.x | x86\_64, AArch64 | | +| Oracle Linux | 8.x | x86\_64, AArch64 | | +| Red Hat Enterprise Linux | 9.x | x86\_64, AArch64 | | +| Red Hat Enterprise Linux | 8.x | x86\_64, AArch64 | | +| Red Hat Enterprise Linux | 7.x | x86\_64 | | +| Ubuntu | 22.10 | x86\_64, ARMv7, AArch64 | | +| Ubuntu | 22.04 | x86\_64, ARMv7, AArch64 | | +| Ubuntu | 20.04 | x86\_64, ARMv7, AArch64 | | +| Ubuntu | 18.04 | x86\_64, i386, ARMv7, AArch64 | | + +### Intermediate + +Platforms in the intermediate support tier are those which Netdata wants to support, but cannot justify core level +support for. They are also covered in CI, but not as rigorously as the core tier. They may or may not include +official binary packages, and any platform-specific bugs receive a normal priority. Generally, we will add new +platforms that we officially support ourselves to the intermediate tier. Our [static builds](#static-builds) are +expected to work on these platforms if available. Source-based installs are expected to work on these platforms +with minimal user effort. + +| Platform | Version | Official Native Packages | Notes | +| -------- | ------- | ------------------------ | ----- | +| Alpine Linux | 3.16 | No | | +| Alpine Linux | 3.15 | No | | +| Alpine Linux | 3.14 | No | | +| Arch Linux | Latest | No | We officially recommend the community packages available for Arch Linux | +| Manjaro Linux | Latest | No | We officially recommend the community packages available for Arch Linux | + +### Community + +Platforms in the community support tier are those which are primarily supported by community contributors. They may +receive some support from Netdata, but are only a best-effort affair. When a community member makes a contribution +to add support for a new platform, that platform generally will start in this tier. Our [static builds](#static-builds) +are expected to work on these platforms if available. Source-based installs are usually expected to work on these +platforms, but may require some extra effort from users. + +| Platform | Version | Official Native Packages | Notes | +| -------- | ------- | ------------------------ | ----- | +| Alpine Linux | Edge | No | | +| Clear Linux | Latest | No | | +| Debian | Sid | No | | +| Fedora | Rawhide | No | | +| FreeBSD | 13-STABLE | No | Netdata is included in the FreeBSD Ports Tree, and this is the recommended installation method on FreeBSD | +| FreeBSD | 12-STABLE | No | Netdata is included in the FreeBSD Ports Tree, and this is the recommended installation method on FreeBSD | +| Gentoo | Latest | No | | +| macOS | 12 | No | Currently only works for Intel-based hardware. Requires Homebrew for dependencies | +| macOS | 11 | No | Currently only works for Intel-based hardware. Requires Homebrew for dependencies. | +| macOS | 10.15 | No | Requires Homebrew for dependencies. | +| openSUSE | Tumbleweed | No | | + +## Third-party supported platforms + +Some platform maintainers actively support Netdata on their platforms even though we do not provide official +support. Third-party supported platforms may work, but the experience of using Netdata on such platforms is not +something we can guarantee. When you use an externally supported platform and report a bug, we will either ask +you to reproduce the issue on a supported platform or submit a support request directly to the platform maintainers. + +Currently, we know of the following platforms having some degree of third-party support for Netdata: + +- NixOS: Netdata’s official installation methods do not support NixOS, but the NixOS maintainers provide their + own Netdata packages for their platform. +- Rockstor: Rockstor provides support for a Netdata add-on for their NAS platform. The Rockstor community and + developers are the primary source for support on their platform. + +## Previously supported platforms + +As platforms become end of life upstream, Netdata will stop officially supporting them. We will not actively break +things on these platforms, but we will also not make any effort to ensure that things keep working on them either. +If you report a bug on a previously supported platforms, we will ask you to reproduce the issue on a currently +supported platform. If the issue is not reproducible, it will be closed. + +We consider a platform to be end of life when the upstream maintainers of that platform stop providing official +support for it themselves, or when that platform transitions into an ‘extended security maintenance’ period. +Platforms that meet these criteria will be immediately transitioned to the **Previously Supported** category, +with no prior warning from Netdata and no deprecation notice, unlike those being dropped for technical reasons, +as our end of support should already coincide with the end of the normal support lifecycle for that platform. + +On occasion, we may also drop support for a platform due to technical limitations. In such cases, this will be +announced in the release notes of the next stable release with a deprecation notice. The platform will be supported +for _that release_, and will be removed from nightlies some time before the next release after that one. + +This is a list of platforms that we have supported in the recent past but no longer officially support: + +| Platform | Version | Notes | +| -------- | ------- | ----- | +| Alpine Linux | 3.13 | EOL as of 2022-11-01 | +| Alpine Linux | 3.12 | EOL as of 2022-05-01 | +| Debian | 9.x | EOL as of 2022-06-30 | +| Fedora | 34 | EOL as of 2022-06-07 | +| Fedora | 33 | EOL as of 2021-11-30 | +| FreeBSD | 11-STABLE | EOL as of 2021-10-30 | +| openSUSE | Leap 15.2 | EOL as of 2021-12-01 | +| Ubuntu | 21.10 | EOL as of 2022-07-31 | +| Ubuntu | 21.04 | EOL as of 2022-01-01 | + +## Static builds + +The Netdata team provides static builds of Netdata for Linux systems with a selection of common CPU +architectures. These static builds are largely self-contained, only requiring a a POSIX-compliant shell on the target +system to provide their basic functionality. Static builds are built in an Alpine Linux environment using musl. This +means that they generally do not support non-local username mappings or exotic name resolution configurations. + +We currently provide static builds for the following CPU architectures: + +- 32-bit x86 +- 64-bit x86 +- ARMv7 +- AArch64 +- POWER8+ + +## Platform-specific support considerations + +### IPMI + +Our IPMI collector is based on FreeIPMI. Due to upstream limitations in FreeIPMI, we are unable to support our +IPMI collector on POWER-based hardware. diff --git a/packaging/build_package_install_test.sh b/packaging/build_package_install_test.sh new file mode 100755 index 0000000..e3b3362 --- /dev/null +++ b/packaging/build_package_install_test.sh @@ -0,0 +1,37 @@ +#!/bin/sh +# SPDX-License-Identifier: GPL-3.0-or-later + +set -e + +# If we are not in netdata git repo, at the top level directory, FAIL +TOP_LEVEL=$(basename "$(git rev-parse --show-toplevel)") +CWD=$(git rev-parse --show-cdup || echo "") +if [ -n "${CWD}" ] || [ ! "${TOP_LEVEL}" = "netdata" ]; then + echo "Run as ./packaging/$(basename "$0") from top level directory of netdata git repository" + exit 1 +fi + +if [ $# -lt 2 ] || [ $# -gt 3 ]; then + echo "Usage: ./packaging/$(basename "$0") <distro> <distro_version> [<netdata_version>]" + exit 1 +fi + +if ! command -v docker > /dev/null; then + echo "Docker CLI not found. You need Docker to run this!" + exit 2 +fi + +DISTRO="$1" +DISTRO_VERSION="$2" +# TODO: Auto compute this? +VERSION="${3:-1.19.0}" + +TAG="netdata/netdata:${DISTRO}_${DISTRO_VERSION}" + +docker build \ + -f ./packaging/Dockerfile.packager \ + --build-arg DISTRO="$DISTRO" \ + --build-arg DISTRO_VERSION="$DISTRO_VERSION" \ + --build-arg VERSION="$VERSION" \ + -t "$TAG" . | + tee build.log diff --git a/packaging/building-native-packages-locally.md b/packaging/building-native-packages-locally.md new file mode 100644 index 0000000..d4949cf --- /dev/null +++ b/packaging/building-native-packages-locally.md @@ -0,0 +1,106 @@ +<!-- +title: How to build native (DEB/RPM) packages locally for testing +description: Instructions for developers who need to build native packages locally for testing. +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/building-native-packages-locally.md +keywords: [Netdata native package, Netdata RPM, Netdata DEB, Testing native packages Netdata] +--> + +# How to build native (DEB/RPM) packages locally for testing + +## Requirements + +To build native packages locally, you will need the following: + +* A working Docker or Podman host. +* A local copy of the source tree you want to build from. + +## Building the packages + +In the root of the source tree from which you want to build, clean up any existing files left over from a previous build +and then run: + +```bash +docker run -it --rm -e VERSION=0.1 -v $PWD:/netdata netdata/package-builders:<tag> +``` + +or + +```bash +podman run -it --rm -e VERSION=0.1 -v $PWD:/netdata netdata/package-builders:<tag> +``` + +The `<tag>` should be the lowercase distribution name with no spaces, followed by the +release of that distribution. For example, `centos7` to build on CentOS 7, or `ubuntu20.04` +to build on Ubuntu 20.04. Note that we use Alma Linux for builds on CentOS/RHEL 8 or newer. See +[netdata/package-builders](https://hub.docker.com/r/netdata/package-builders/tags) for all available tags. + +The value passed in the `VERSION` environment variable can be any version number accepted by the type of package +being built. As a general rule, it needs to start with a digit, and must include a `.` somewhere. + +Once it finishes, the built packages can be found under `artifacts/` in the source tree. + +If an error is encountered and the build is being run interactively, it will drop to a shell to allow you to +inspect the state of the container and look at build logs. + +### Detailed explanation + +The environments used for building our packages are fully self-contianed Docker images built from [Dockerfiles](https://github.com/netdata/helper-images/tree/master/package-builders) +These are published on Docker +Hub with the image name `netdata/package-builders`, and tagged using the name and version of the distribution +(with the tag corresponding to the suffix on the associated Dockerfile). + +The build code expects the following requirements to be met: + +- It expects the source tree it should build from to be located at `/netdata`, and expects that said source tree + is clean (no artifacts left over from previous builds). +- It expects an environment variable named `VERSION` to be defined, and uses this to control what version number + will be shown in the package metadata and filenames. + +Internally, the source tree gets copied to a temporary location for the build process so that the source tree can +be mounted directly from the host without worrying about leaving a dirty tree behind, any templating or file +movements required for the build to work are done, the package build command is invoked with the correct arguments, +and then the resultant packages are copied to the `artifacts/` directory in the original source tree so they are +accessible after the container exits. + +## Finding build logs after a failed build + +Build logs and artifacts can be found in the build directory, whose location varies by distribution. + +On DEB systems (Ubuntu and Debian), the build directory inside the container is located at `/usr/src/netdata` + +On RPM systems except openSUSE, the build directory inside the container is located under `/root/rpmbuild/BUILD/` +and varies based on the package version number. + +On openSUSE, the build directory inside the container is located under `/usr/src/packages/BUILD`and varies based +on the package version number. + +## Building for other architectures + +If you need to test a build for an architecture that does not match your host system, you can do so by setting up +QEMU user-mode emulation. This requires a Linux kernel with binfmt\_misc support (all modern distributions provide +this out of the box, but I’m not sure about WSL or Docker Desktop). + +The quick and easy way to do this is to run the following: + +```bash +docker run --rm --privileged multiarch/qemu-user-static --reset -p yes +``` + +or + +```bash +podman run --rm --privileged multiarch/qemu-user-static --reset -p yes +``` + +This will set up the required QEMU user-mode emulation until you reboot. Note that if using Podman, you will need +to run this as root and not as a rootless container (the package builds work fine in a rootless container though, +even if doing cross-architecture builds). + +Once you have that set up, the command to build the packages is the same as above, you just need to add a correct +`--platform` option to the `docker run` or `podman run` command. The current list of architectures we build for, +and the correct value for the `--platform` option is: + +- 32-bit ARMv7: `linux/arm/v7` +- 64-bit ARMv8: `linux/arm64/v8` +- 32-bit x86: `linux/i386` +- 64-bit x86: `linux/amd64` diff --git a/packaging/bundle-ebpf-co-re.sh b/packaging/bundle-ebpf-co-re.sh new file mode 100755 index 0000000..9d2eaf5 --- /dev/null +++ b/packaging/bundle-ebpf-co-re.sh @@ -0,0 +1,9 @@ +#!/bin/sh + +SRCDIR="${1}" + +CORE_VERSION="$(cat "${SRCDIR}/packaging/ebpf-co-re.version")" +CORE_TARBALL="netdata-ebpf-co-re-glibc-${CORE_VERSION}.tar.xz" +curl -sSL --connect-timeout 10 --retry 3 "https://github.com/netdata/ebpf-co-re/releases/download/${CORE_VERSION}/${CORE_TARBALL}" > "${CORE_TARBALL}" || exit 1 +grep "${CORE_TARBALL}" "${SRCDIR}/packaging/ebpf-co-re.checksums" | sha256sum -c - || exit 1 +tar -xaf "${CORE_TARBALL}" -C "${SRCDIR}/collectors/ebpf.plugin" || exit 1 diff --git a/packaging/bundle-ebpf.sh b/packaging/bundle-ebpf.sh new file mode 100755 index 0000000..3204345 --- /dev/null +++ b/packaging/bundle-ebpf.sh @@ -0,0 +1,19 @@ +#!/bin/sh + +SRCDIR="${1}" +PLUGINDIR="${2}" + +EBPF_VERSION="$(cat "${SRCDIR}/packaging/ebpf.version")" +EBPF_TARBALL="netdata-kernel-collector-glibc-${EBPF_VERSION}.tar.xz" + +if [ -x "${PLUGINDIR}/ebpf.plugin" ] ; then + mkdir -p "${SRCDIR}/tmp/ebpf" + curl -sSL --connect-timeout 10 --retry 3 "https://github.com/netdata/kernel-collector/releases/download/${EBPF_VERSION}/${EBPF_TARBALL}" > "${EBPF_TARBALL}" || exit 1 + grep "${EBPF_TARBALL}" "${SRCDIR}/packaging/ebpf.checksums" | sha256sum -c - || exit 1 + tar -xaf "${EBPF_TARBALL}" -C "${SRCDIR}/tmp/ebpf" || exit 1 + if [ ! -d "${PLUGINDIR}/ebpf.d" ];then + mkdir "${PLUGINDIR}/ebpf.d" + fi + # shellcheck disable=SC2046 + cp -a $(find "${SRCDIR}/tmp/ebpf" -mindepth 1 -maxdepth 1) "${PLUGINDIR}/ebpf.d" +fi diff --git a/packaging/bundle-libbpf.sh b/packaging/bundle-libbpf.sh new file mode 100755 index 0000000..7e6e22a --- /dev/null +++ b/packaging/bundle-libbpf.sh @@ -0,0 +1,27 @@ +#!/bin/bash + +if [ "$(uname -m)" = x86_64 ]; then + lib_subdir="lib64" +else + lib_subdir="lib" +fi + +if [ "${2}" != "centos7" ]; then + cp "${1}/packaging/current_libbpf.checksums" "${1}/packaging/libbpf.checksums" + cp "${1}/packaging/current_libbpf.version" "${1}/packaging/libbpf.version" +else + cp "${1}/packaging/libbpf_0_0_9.checksums" "${1}/packaging/libbpf.checksums" + cp "${1}/packaging/libbpf_0_0_9.version" "${1}/packaging/libbpf.version" +fi + +LIBBPF_TARBALL="v$(cat "${1}/packaging/libbpf.version").tar.gz" +LIBBPF_BUILD_PATH="${1}/externaldeps/libbpf/libbpf-$(cat "${1}/packaging/libbpf.version")" + +mkdir -p "${1}/externaldeps/libbpf" || exit 1 +curl -sSL --connect-timeout 10 --retry 3 "https://github.com/netdata/libbpf/archive/${LIBBPF_TARBALL}" > "${LIBBPF_TARBALL}" || exit 1 +sha256sum -c "${1}/packaging/libbpf.checksums" || exit 1 +tar -xzf "${LIBBPF_TARBALL}" -C "${1}/externaldeps/libbpf" || exit 1 +make -C "${LIBBPF_BUILD_PATH}/src" BUILD_STATIC_ONLY=1 OBJDIR=build/ DESTDIR=../ install || exit 1 +cp -a "${LIBBPF_BUILD_PATH}/usr/${lib_subdir}/libbpf.a" "${1}/externaldeps/libbpf" || exit 1 +cp -a "${LIBBPF_BUILD_PATH}/usr/include" "${1}/externaldeps/libbpf" || exit 1 +cp -a "${LIBBPF_BUILD_PATH}/include/uapi" "${1}/externaldeps/libbpf/include" || exit 1 diff --git a/packaging/bundle-protobuf.sh b/packaging/bundle-protobuf.sh new file mode 100755 index 0000000..98ab1ed --- /dev/null +++ b/packaging/bundle-protobuf.sh @@ -0,0 +1,16 @@ +#!/bin/sh + +PROTOBUF_TARBALL="protobuf-cpp-$(cat "${1}/packaging/protobuf.version").tar.gz" +PROTOBUF_BUILD_PATH="${1}/externaldeps/protobuf/protobuf-$(cat "${1}/packaging/protobuf.version")" + +mkdir -p "${1}/externaldeps/protobuf" || exit 1 +curl -sSL --connect-timeout 10 --retry 3 "https://github.com/protocolbuffers/protobuf/releases/download/v$(cat "${1}/packaging/protobuf.version")/${PROTOBUF_TARBALL}" > "${PROTOBUF_TARBALL}" || exit 1 +sha256sum -c "${1}/packaging/protobuf.checksums" || exit 1 +tar -xzf "${PROTOBUF_TARBALL}" -C "${1}/externaldeps/protobuf" || exit 1 +OLDPWD="${PWD}" +cd "${PROTOBUF_BUILD_PATH}" || exit 1 +./configure --disable-shared --without-zlib --disable-dependency-tracking --with-pic || exit 1 +make -j "$(nproc)" || exit 1 +cd "${OLDPWD}" || exit 1 + +cp -a "${PROTOBUF_BUILD_PATH}/src" "${1}/externaldeps/protobuf" || exit 1 diff --git a/packaging/check-kernel-config.sh b/packaging/check-kernel-config.sh new file mode 100755 index 0000000..ded3225 --- /dev/null +++ b/packaging/check-kernel-config.sh @@ -0,0 +1,73 @@ +#!/usr/bin/env bash + +get_kernel_version() { + r="$(uname -r | cut -f 1 -d '-')" + + read -r -a p <<< "$(echo "${r}" | tr '.' ' ')" + + printf "%03d%03d%03d" "${p[0]}" "${p[1]}" "${p[2]}" +} + +get_rh_version() { + if [ ! -f /etc/redhat-release ]; then + printf "000000000" + return + fi + + r="$(cut -f 4 -d ' ' < /etc/redhat-release)" + + read -r -a p <<< "$(echo "${r}" | tr '.' ' ')" + + printf "%03d%03d%03d" "${p[0]}" "${p[1]}" "${p[2]}" +} + +if [ "$(uname -s)" != "Linux" ]; then + echo >&2 "This does not appear to be a Linux system." + exit 1 +fi + +KERNEL_VERSION="$(uname -r)" + +if [ "$(get_kernel_version)" -lt 004014000 ] && [ "$(get_rh_version)" -lt 0070061810 ]; then + echo >&2 "WARNING: Your kernel appears to be older than 4.11 or you are using RH version older than 7.6.1810. This may still work in some cases, but probably won't." +fi + +CONFIG_PATH="" +MODULE_LOADED="" + +if modprobe configs 2> /dev/null; then + MODULE_LOADED=1 +fi + +if [ -r /proc/config.gz ]; then + CONFIG_PATH="/proc/config.gz" +elif [ -r "/lib/modules/${KERNEL_VERSION}/source/.config" ]; then + CONFIG_PATH="/lib/modules/${KERNEL_VERSION}/source/.config" +elif [ -r "/lib/modules/${KERNEL_VERSION}.x86_64/source/.config" ]; then + CONFIG_PATH="/lib/modules/${KERNEL_VERSION}.x86_64/source/.config" +elif [ -n "$(find /boot -name "config-${KERNEL_VERSION}*")" ]; then + CONFIG_PATH="$(find /boot -name "config-${KERNEL_VERSION}*" | head -n 1)" +fi + +if [ -n "${CONFIG_PATH}" ]; then + GREP='grep' + + if echo "${CONFIG_PATH}" | grep -q '.gz'; then + GREP='zgrep' + fi + + REQUIRED_CONFIG="KPROBES KPROBES_ON_FTRACE HAVE_KPROBES BPF BPF_SYSCALL BPF_JIT" + + for required_config in ${REQUIRED_CONFIG}; do + if ! "${GREP}" -q "CONFIG_${required_config}=y" "${CONFIG_PATH}"; then + echo >&2 " Missing Kernel Config: ${required_config}" + exit 1 + fi + done +fi + +if [ -n "${MODULE_LOADED}" ]; then + modprobe -r configs 2> /dev/null || true # Ignore failures from CONFIGS being builtin +fi + +exit 0 diff --git a/packaging/current_libbpf.checksums b/packaging/current_libbpf.checksums new file mode 100644 index 0000000..9a8b8f8 --- /dev/null +++ b/packaging/current_libbpf.checksums @@ -0,0 +1 @@ +63fe4ac3f6807e8ff4cd3af2ffae0091eb177fb7f6aca2f03d3f201a609b988c v1.0.1_netdata.tar.gz diff --git a/packaging/current_libbpf.version b/packaging/current_libbpf.version new file mode 100644 index 0000000..bb58ffc --- /dev/null +++ b/packaging/current_libbpf.version @@ -0,0 +1 @@ +1.0.1_netdata diff --git a/packaging/docker/Dockerfile b/packaging/docker/Dockerfile new file mode 100644 index 0000000..287c592 --- /dev/null +++ b/packaging/docker/Dockerfile @@ -0,0 +1,126 @@ +# SPDX-License-Identifier: GPL-3.0-or-later +# author : paulfantom + +# This image contains preinstalled dependencies +# hadolint ignore=DL3007 +FROM netdata/builder:latest as builder + +# One of 'nightly' or 'stable' +ARG RELEASE_CHANNEL=nightly + +ARG CFLAGS + +ENV CFLAGS=$CFLAGS + +ARG EXTRA_INSTALL_OPTS + +ENV EXTRA_INSTALL_OPTS=$EXTRA_INSTALL_OPTS + +ARG DEBUG_BUILD + +ENV DEBUG_BUILD=$DEBUG_BUILD + +# Copy source +COPY . /opt/netdata.git +WORKDIR /opt/netdata.git + +# Install from source +RUN chmod +x netdata-installer.sh && \ + cp -rp /deps/* /usr/local/ && \ + /bin/echo -e "INSTALL_TYPE='oci'\nPREBUILT_ARCH='$(uname -m)'" > ./system/.install-type && \ + CFLAGS="$(packaging/docker/gen-cflags.sh)" ./netdata-installer.sh --dont-wait --dont-start-it --use-system-protobuf \ + ${EXTRA_INSTALL_OPTS} --one-time-build "$([ "$RELEASE_CHANNEL" = stable ] && echo --stable-channel)" + +# files to one directory +RUN mkdir -p /app/usr/sbin/ \ + /app/usr/share \ + /app/usr/libexec \ + /app/usr/local \ + /app/usr/lib \ + /app/var/cache \ + /app/var/lib \ + /app/etc && \ + mv /usr/share/netdata /app/usr/share/ && \ + mv /usr/libexec/netdata /app/usr/libexec/ && \ + mv /usr/lib/netdata /app/usr/lib/ && \ + mv /var/cache/netdata /app/var/cache/ && \ + mv /var/lib/netdata /app/var/lib/ && \ + mv /etc/netdata /app/etc/ && \ + mv /usr/sbin/netdata /app/usr/sbin/ && \ + mv /usr/sbin/netdata-claim.sh /app/usr/sbin/ && \ + mv /usr/sbin/netdatacli /app/usr/sbin/ && \ + mv packaging/docker/run.sh /app/usr/sbin/ && \ + mv packaging/docker/health.sh /app/usr/sbin/ && \ + cp -rp /deps/* /app/usr/local/ && \ + chmod +x /app/usr/sbin/run.sh + +##################################################################### +# This image contains preinstalled dependencies +# hadolint ignore=DL3007 +FROM netdata/base:latest as base + +ARG OFFICIAL_IMAGE=false +ENV NETDATA_OFFICIAL_IMAGE=$OFFICIAL_IMAGE + +# Configure system +ARG NETDATA_UID=201 +ARG NETDATA_GID=201 +ENV DOCKER_GRP netdata +ENV DOCKER_USR netdata +# If DISABLE_TELEMETRY is set, it will disable anonymous stats collection and reporting +#ENV DISABLE_TELEMETRY=1 + +# Copy files over +RUN mkdir -p /opt/src /var/log/netdata && \ + # Link log files to stdout + ln -sf /dev/stdout /var/log/netdata/access.log && \ + ln -sf /dev/stdout /var/log/netdata/debug.log && \ + ln -sf /dev/stderr /var/log/netdata/error.log && \ + # fping from alpine apk is on a different location. Moving it. + ln -snf /usr/sbin/fping /usr/local/bin/fping && \ + chmod 4755 /usr/local/bin/fping && \ + # Add netdata user + addgroup -g ${NETDATA_GID} -S "${DOCKER_GRP}" && \ + adduser -S -H -s /usr/sbin/nologin -u ${NETDATA_GID} -h /etc/netdata -G "${DOCKER_GRP}" "${DOCKER_USR}" + # Fix handling of config directory + +# Long-term this should leverage BuildKit’s mount option. +COPY --from=builder /wheels /wheels +COPY --from=builder /app / + +# Apply the permissions as described in +# https://docs.netdata.cloud/docs/netdata-security/#netdata-directories, but own everything by root group due to https://github.com/netdata/netdata/pull/6543 +# hadolint ignore=DL3013 +RUN chown -R root:root \ + /etc/netdata \ + /usr/share/netdata \ + /usr/libexec/netdata && \ + chown -R netdata:root \ + /usr/lib/netdata \ + /var/cache/netdata \ + /var/lib/netdata \ + /var/log/netdata && \ + chown -R netdata:netdata /var/lib/netdata/cloud.d && \ + chmod 0700 /var/lib/netdata/cloud.d && \ + chmod 0755 /usr/libexec/netdata/plugins.d/*.plugin && \ + chmod 4755 \ + /usr/libexec/netdata/plugins.d/cgroup-network \ + /usr/libexec/netdata/plugins.d/apps.plugin && \ + if [ -f /usr/libexec/netdata/plugins.d/freeipmi.plugin ]; then \ + chmod 4755 /usr/libexec/netdata/plugins.d/freeipmi.plugin; \ + fi && \ + # Group write permissions due to: https://github.com/netdata/netdata/pull/6543 + find /var/lib/netdata /var/cache/netdata -type d -exec chmod 0770 {} \; && \ + find /var/lib/netdata /var/cache/netdata -type f -exec chmod 0660 {} \; && \ + pip --no-cache-dir install /wheels/* && \ + rm -rf /wheels && \ + cp -va /etc/netdata /etc/netdata.stock + +ENV NETDATA_LISTENER_PORT 19999 +EXPOSE $NETDATA_LISTENER_PORT + +ENTRYPOINT ["/usr/sbin/run.sh"] + +HEALTHCHECK --interval=60s --timeout=10s --retries=3 CMD /usr/sbin/health.sh + +ONBUILD ENV NETDATA_OFFICIAL_IMAGE=false diff --git a/packaging/docker/README.md b/packaging/docker/README.md new file mode 100644 index 0000000..d00262a --- /dev/null +++ b/packaging/docker/README.md @@ -0,0 +1,536 @@ +<!-- +title: "Install Netdata with Docker" +date: 2020-04-23 +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/docker/README.md +--> + +# Install the Netdata Agent with Docker + +Running the Netdata Agent in a container works best for an internal network or to quickly analyze a host. Docker helps +you get set up quickly, and doesn't install anything permanent on the system, which makes uninstalling the Agent easy. + +See our full list of Docker images at [Docker Hub](https://hub.docker.com/r/netdata/netdata). + +Starting with v1.30, Netdata collects anonymous usage information by default and sends it to a self-hosted PostHog instance within the Netdata infrastructure. Read +about the information collected, and learn how to-opt, on our [anonymous statistics](/docs/anonymous-statistics.md) +page. + +The usage statistics are _vital_ for us, as we use them to discover bugs and prioritize new features. We thank you for +_actively_ contributing to Netdata's future. + +## Limitations running the Agent in Docker + +For monitoring the whole host, running the Agent in a container can limit its capabilities. Some data, like the host OS +performance or status, is not accessible or not as detailed in a container as when running the Agent directly on the +host. + +A way around this is to provide special mounts to the Docker container so that the Agent can get visibility on host OS +information like `/sys` and `/proc` folders or even `/etc/group` and shadow files. + +Also, we now ship Docker images using an [ENTRYPOINT](https://docs.docker.com/engine/reference/builder/#entrypoint) +directive, not a COMMAND directive. Please adapt your execution scripts accordingly. You can find more information about +ENTRYPOINT vs COMMAND in the [Docker +documentation](https://docs.docker.com/engine/reference/builder/#understand-how-cmd-and-entrypoint-interact). + +Our POWER8+ Docker images do not support our FreeIPMI collector. This is a technical limitation in FreeIPMI itself, +and unfortunately not something we can realistically work around. + +## Create a new Netdata Agent container + +You can create a new Agent container using either `docker run` or Docker Compose. After using either method, you can +visit the Agent dashboard `http://NODE:19999`. + +Both methods create a [bind mount](https://docs.docker.com/storage/bind-mounts/) for Netdata's configuration files +_within the container_ at `/etc/netdata`. See the [configuration section](#configure-agent-containers) for details. If +you want to access the configuration files from your _host_ machine, see [host-editable +configuration](#host-editable-configuration). + +**`docker run`**: Use the `docker run` command, along with the following options, to start a new container. + +```bash +docker run -d --name=netdata \ + -p 19999:19999 \ + -v netdataconfig:/etc/netdata \ + -v netdatalib:/var/lib/netdata \ + -v netdatacache:/var/cache/netdata \ + -v /etc/passwd:/host/etc/passwd:ro \ + -v /etc/group:/host/etc/group:ro \ + -v /proc:/host/proc:ro \ + -v /sys:/host/sys:ro \ + -v /etc/os-release:/host/etc/os-release:ro \ + --restart unless-stopped \ + --cap-add SYS_PTRACE \ + --security-opt apparmor=unconfined \ + netdata/netdata +``` + +**Docker Compose**: Copy the following code and paste into a new file called `docker-compose.yml`, then run +`docker-compose up -d` in the same directory as the `docker-compose.yml` file to start the container. + +```yaml +version: '3' +services: + netdata: + image: netdata/netdata + container_name: netdata + hostname: example.com # set to fqdn of host + ports: + - 19999:19999 + restart: unless-stopped + cap_add: + - SYS_PTRACE + security_opt: + - apparmor:unconfined + volumes: + - netdataconfig:/etc/netdata + - netdatalib:/var/lib/netdata + - netdatacache:/var/cache/netdata + - /etc/passwd:/host/etc/passwd:ro + - /etc/group:/host/etc/group:ro + - /proc:/host/proc:ro + - /sys:/host/sys:ro + - /etc/os-release:/host/etc/os-release:ro + +volumes: + netdataconfig: + netdatalib: + netdatacache: +``` + +## Docker tags + +The official `netdata/netdata` Docker image provides the following named tags: + +* `stable`: The `stable` tag will always point to the most recently published stable build. +* `edge`: The `edge` tag will always point ot the most recently published nightly build. In most cases, this is + updated daily at around 01:00 UTC. +* `latest`: The `latest` tag will always point to the most recently published build, whether it’s a stable build + or a nightly build. This is what Docker will use by default if you do not specify a tag. + +Additionally, for each stable release, three tags are pushed, one with the full version of the release (for example, +`v1.30.0`), one with just the major and minor version (for example, `v1.30`), and one with just the major version +(for example, `v1`). The tags for the minor versions and major versions are updated whenever a release is published +that would match that tag (for example, if `v1.30.1` were to be published, the `v1.30` tag would be updated to +point to that instead of `v1.30.0`). + +## Health Checks + +Our Docker image provides integrated support for health checks through the standard Docker interfaces. + +You can control how the health checks run by using the environment variable `NETDATA_HEALTHCHECK_TARGET` as follows: + +- If left unset, the health check will attempt to access the + `/api/v1/info` endpoint of the agent. +- If set to the exact value 'cli', the health check + script will use `netdatacli ping` to determine if the agent is running + correctly or not. This is sufficient to ensure that Netdata did not + hang during startup, but does not provide a rigorous verification + that the daemon is collecting data or is otherwise usable. +- If set to anything else, the health check will treat the value as a + URL to check for a 200 status code on. In most cases, this should + start with `http://localhost:19999/` to check the agent running in + the container. + +In most cases, the default behavior of checking the `/api/v1/info` +endpoint will be sufficient. If you are using a configuration which +disables the web server or restricts access to certain APIs, you will +need to use a non-default configuration for health checks to work. + +## Configure Agent containers + +If you started an Agent container using one of the [recommended methods](#create-a-new-netdata-agent-container), and you +want to edit Netdata's configuration, you must first use `docker exec` to attach to the container. Replace `netdata` +with the name of your container. + +```bash +docker exec -it netdata bash +cd /etc/netdata +./edit-config netdata.conf +``` + +You need to restart the Agent to apply changes. Exit the container if you haven't already, then use the `docker` command +to restart the container: `docker restart netdata`. + +### Host-editable configuration + +> **Warning**: [edit-config](/docs/configure/nodes.md#the-netdata-config-directory) script doesn't work when executed on +> the host system. + +If you want to make your container's configuration directory accessible from the host system, you need to use a +[volume](https://docs.docker.com/storage/bind-mounts/) rather than a bind mount. The following commands create a +temporary `netdata_tmp` container, which is used to populate a `netdataconfig` directory, which is then mounted inside +the container at `/etc/netdata`. + +```bash +mkdir netdataconfig +docker run -d --name netdata_tmp netdata/netdata +docker cp netdata_tmp:/etc/netdata netdataconfig/ +docker rm -f netdata_tmp +``` + +**`docker run`**: Use the `docker run` command, along with the following options, to start a new container. Note the +changed `-v $(pwd)/netdataconfig/netdata:/etc/netdata:ro \` line from the recommended example above. + +```bash +docker run -d --name=netdata \ + -p 19999:19999 \ + -v $(pwd)/netdataconfig/netdata:/etc/netdata:ro \ + -v netdatalib:/var/lib/netdata \ + -v netdatacache:/var/cache/netdata \ + -v /etc/passwd:/host/etc/passwd:ro \ + -v /etc/group:/host/etc/group:ro \ + -v /proc:/host/proc:ro \ + -v /sys:/host/sys:ro \ + -v /etc/os-release:/host/etc/os-release:ro \ + --restart unless-stopped \ + --cap-add SYS_PTRACE \ + --security-opt apparmor=unconfined \ + netdata/netdata +``` + +**Docker Compose**: Copy the following code and paste into a new file called `docker-compose.yml`, then run +`docker-compose up -d` in the same directory as the `docker-compose.yml` file to start the container. Note the changed +`./netdataconfig/netdata:/etc/netdata:ro` line from the recommended example above. + +```yaml +version: '3' +services: + netdata: + image: netdata/netdata + container_name: netdata + hostname: example.com # set to fqdn of host + ports: + - 19999:19999 + restart: unless-stopped + cap_add: + - SYS_PTRACE + security_opt: + - apparmor:unconfined + volumes: + - ./netdataconfig/netdata:/etc/netdata:ro + - netdatalib:/var/lib/netdata + - netdatacache:/var/cache/netdata + - /etc/passwd:/host/etc/passwd:ro + - /etc/group:/host/etc/group:ro + - /proc:/host/proc:ro + - /sys:/host/sys:ro + - /etc/os-release:/host/etc/os-release:ro + +volumes: + netdatalib: + netdatacache: +``` + +### Change the default hostname + +You can change the hostname of a Docker container, and thus the name that appears in the local dashboard and in Netdata +Cloud, when creating a new container. If you want to change the hostname of a Netdata container _after_ you started it, +you can safely stop and remove it. Your configuration and metrics data reside in persistent volumes and are reattached to +the recreated container. + +If you use `docker-run`, use the `--hostname` option with `docker run`. + +```bash +docker run -d --name=netdata \ + --hostname=my_docker_netdata +``` + +If you use `docker-compose`, add a `hostname:` key/value pair into your `docker-compose.yml` file, then create the +container again using `docker-compose up -d`. + +```yaml +version: '3' +services: + netdata: + image: netdata/netdata + container_name: netdata + hostname: my_docker_compose_netdata + ... +``` + +If you don't want to destroy and recreate your container, you can edit the Agent's `netdata.conf` file directly. See the +above section on [configuring Agent containers](#configure-agent-containers) to find the appropriate method based on +how you created the container. + +Alternatively, you can directly use the hostname from the node running the container by mounting +`/etc/hostname` from the host in the container. With `docker run`, this can be done by adding `--volume +/etc/hostname:/etc/hostname:ro` to the options. If you are using Docker Compose, you can add an entry to the +container's `volumes` section reading `- /etc/hostname:/etc/hostname:ro`. + +### Add or remove other volumes + +Some volumes are optional depending on how you use Netdata: + +- If you don't want to use the apps.plugin functionality, you can remove the mounts of `/etc/passwd` and `/etc/group` + (they are used to get proper user and group names for the monitored host) to get slightly better security. +- Most modern linux distros supply `/etc/os-release` although some older distros only supply `/etc/lsb-release`. If + this is the case you can change the line above that mounts the file inside the container to + `-v /etc/lsb-release:/host/etc/lsb-release:ro`. +- If your host is virtualized then Netdata cannot detect it from inside the container and will output the wrong + metadata (e.g. on `/api/v1/info` queries). You can fix this by setting a variable that overrides the detection + using, e.g. `--env VIRTUALIZATION=$(systemd-detect-virt -v)`. If you are using a `docker-compose.yml` then add: + +```yaml + environment: + - VIRTUALIZATION=${VIRTUALIZATION} +``` + +This allows the information to be passed into `docker-compose` using: + +```bash +VIRTUALIZATION=$(systemd-detect-virt -v) docker-compose up +``` + +#### Files inside systemd volumes + +If a volume is used by systemd service, some files can be removed during +[reinitialization](https://github.com/netdata/netdata/issues/9916). To avoid this, you need to add +`RuntimeDirectoryPreserve=yes` to the service file. + +### Docker container names resolution + +There are a few options for resolving container names within Netdata. Some methods of doing so will allow root access to +your machine from within the container. Please read the following carefully. + +#### Docker socket proxy (safest option) + +Deploy a Docker socket proxy that accepts and filters out requests using something like +[HAProxy](/docs/Running-behind-haproxy.md) so that it restricts connections to read-only access to the CONTAINERS +endpoint. + +The reason it's safer to expose the socket to the proxy is because Netdata has a TCP port exposed outside the Docker +network. Access to the proxy container is limited to only within the network. + +Below is [an example repository (and image)](https://github.com/Tecnativa/docker-socket-proxy) that provides a proxy to +the socket. + +You run the Docker Socket Proxy in its own Docker Compose file and leave it on a private network that you can add to +other services that require access. + +```yaml +version: '3' +services: + netdata: + image: netdata/netdata + # ... rest of your config ... + ports: + - 19999:19999 + environment: + - DOCKER_HOST=proxy:2375 + proxy: + image: tecnativa/docker-socket-proxy + volumes: + - /var/run/docker.sock:/var/run/docker.sock:ro + environment: + - CONTAINERS=1 + +``` +**Note:** Replace `2375` with the port of your proxy. + +#### Giving group access to the Docker socket (less safe) + +> You should seriously consider the necessity of activating this option, as it grants to the `netdata` +user access to the privileged socket connection of docker service and therefore your whole machine. + +If you want to have your container names resolved by Netdata, make the `netdata` user be part of the group that owns the +socket. + +```yaml +version: '3' +services: + netdata: + image: netdata/netdata + # ... rest of your config ... + volumes: + # ... other volumes ... + - /var/run/docker.sock:/var/run/docker.sock:ro + environment: + - PGID=[GROUP NUMBER] +``` + +To achieve that just add environment variable `PGID=[GROUP NUMBER]` to the Netdata container, where `[GROUP NUMBER]` is +practically the group id of the group assigned to the docker socket, on your host. + +This group number can be found by running the following (if socket group ownership is docker): + +```bash +grep docker /etc/group | cut -d ':' -f 3 +``` + +#### Running as root (unsafe) + +> You should seriously consider the necessity of activating this option, as it grants to the `netdata` user access to +> the privileged socket connection of docker service, and therefore your whole machine. + +```yaml +version: '3' +services: + netdata: + image: netdata/netdata + # ... rest of your config ... + volumes: + # ... other volumes ... + - /var/run/docker.sock:/var/run/docker.sock:ro + environment: + - DOCKER_USR=root +``` + +### Docker container network interfaces monitoring + +Netdata can map a virtual interface in the system namespace to an interface inside a Docker container +when using network [bridge](https://docs.docker.com/network/bridge/) driver. To do this, the Netdata container needs +additional privileges: + +- the host PID mode. This turns on sharing between container and the host operating system the PID + address space (needed to get list of PIDs from `cgroup.procs` file). + +- `SYS_ADMIN` capability (needed to execute `setns()`). + +**docker run**: + +```bash +docker run -d --name=netdata \ + ... + --pid=host \ + --cap-add SYS_ADMIN \ + ... + netdata/netdata +``` + +**docker compose**: + +```yaml +version: '3' +services: + netdata: + image: netdata/netdata + container_name: netdata + pid: host + cap_add: + - SYS_ADMIN + ... +``` + +### Pass command line options to Netdata + +Since we use an [ENTRYPOINT](https://docs.docker.com/engine/reference/builder/#entrypoint) directive, you can provide +[Netdata daemon command line options](/daemon/README.md#command-line-options) such as the IP address Netdata will be +running on, using the [command instruction](https://docs.docker.com/engine/reference/builder/#cmd). + +## Install the Agent using Docker Compose with SSL/TLS enabled HTTP Proxy + +For a permanent installation on a public server, you should [secure the Netdata +instance](/docs/netdata-security.md). This section contains an example of how to install Netdata with an SSL +reverse proxy and basic authentication. + +You can use the following `docker-compose.yml` and Caddyfile files to run Netdata with Docker. Replace the domains and +email address for [Let's Encrypt](https://letsencrypt.org/) before starting. + +### Caddyfile + +This file needs to be placed in `/opt` with name `Caddyfile`. Here you customize your domain, and you need to provide +your email address to obtain a Let's Encrypt certificate. Certificate renewal will happen automatically and will be +executed internally by the caddy server. + +```caddyfile +netdata.example.org { + reverse_proxy netdata:19999 + tls admin@example.org +} +``` + +### docker-compose.yml + +After setting Caddyfile run this with `docker-compose up -d` to have fully functioning Netdata setup behind HTTP reverse +proxy. + +```yaml +version: '3' +volumes: + caddy_data: + caddy_config: + +services: + caddy: + image: caddy:2 + ports: + - "80:80" + - "443:443" + volumes: + - /opt/Caddyfile:/etc/caddy/Caddyfile + - caddy_data:/data + - caddy_config:/config + netdata: + restart: always + hostname: netdata.example.org + image: netdata/netdata + cap_add: + - SYS_PTRACE + security_opt: + - apparmor:unconfined + volumes: + - netdatalib:/var/lib/netdata + - netdatacache:/var/cache/netdata + - /etc/passwd:/host/etc/passwd:ro + - /etc/group:/host/etc/group:ro + - /proc:/host/proc:ro + - /sys:/host/sys:ro + - /var/run/docker.sock:/var/run/docker.sock:ro + +volumes: + netdatalib: + netdatacache: +``` + +### Restrict access with basic auth + +You can restrict access by following [official caddy guide](https://caddyserver.com/docs/caddyfile/directives/basicauth#basicauth) and adding lines to +Caddyfile. + +## Publish a test image to your own repository + +At Netdata, we provide multiple ways of testing your Docker images using your own repositories. +You may either use the command line tools available or take advantage of our Travis CI infrastructure. + +### Inside Netdata organization, using Travis CI + +To enable Travis CI integration on your own repositories (Docker and GitHub), you need to be part of the Netdata +organization. + +Once you have contacted the Netdata owners to setup you up on GitHub and Travis, execute the following steps + +- Preparation + - Have Netdata forked on your personal GitHub account + - Get a GitHub token: Go to **GitHub settings** -> **Developer Settings** -> **Personal access tokens**, and + generate a new token with full access to `repo_hook`, read-only access to `admin:org`, `public_repo`, + `repo_deployment`, `repo:status`, and `user:email` settings enabled. This will be your `GITHUB_TOKEN` that is + described later in the instructions, so keep it somewhere safe. + - Contact the Netdata team and seek for permissions on `https://scan.coverity.com` should you require Travis to be + able to push your forked code to coverity for analysis and report. Once you are setup, you should have your + email you used in coverity and a token from them. These will be your `COVERITY_SCAN_SUBMIT_EMAIL` and + `COVERITY_SCAN_TOKEN` that we will refer to later. + - Have a valid Docker hub account, the credentials from this account will be your `DOCKER_USERNAME` and + `DOCKER_PWD` mentioned later. + +- Setting up Travis CI for your own fork (Detailed instructions provided by Travis team [here](https://docs.travis-ci.com/user/tutorial/)) + - Login to travis with your own GITHUB credentials (There is Open Auth access) + - Go to your profile settings, under [repositories](https://travis-ci.com/account/repositories) section and setup + your Netdata fork to be built by Travis CI. + - Once the repository has been setup, go to repository settings within Travis CI (usually under + `https://travis-ci.com/NETDATA_DEVELOPER/netdata/settings`, where `NETDATA_DEVELOPER` is your GitHub handle), + and select your desired settings. + +- While in Travis settings, under Netdata repository settings in the Environment Variables section, you need to add + the following: + - `DOCKER_USERNAME` and `DOCKER_PWD` variables so that Travis can log in to your Docker Hub account and publish + Docker images there. + - `REPOSITORY` variable to `NETDATA_DEVELOPER/netdata`, where `NETDATA_DEVELOPER` is your GitHub handle again. + - `GITHUB_TOKEN` variable with the token generated on the preparation step, for Travis workflows to function + properly. + - `COVERITY_SCAN_SUBMIT_EMAIL` and `COVERITY_SCAN_TOKEN` variables to enable Travis to submit your code for + analysis to Coverity. + +Having followed these instructions, your forked repository should be all set up for integration with Travis CI. Happy +testing! + + diff --git a/packaging/docker/gen-cflags.sh b/packaging/docker/gen-cflags.sh new file mode 100755 index 0000000..3a80b73 --- /dev/null +++ b/packaging/docker/gen-cflags.sh @@ -0,0 +1,9 @@ +#!/bin/sh + +if [ -n "${CFLAGS}" ]; then + echo "${CFLAGS}" +elif [ -n "${DEBUG_BUILD}" ]; then + echo "-Og -ggdb -pipe" +else + echo "-O2 -pipe" +fi diff --git a/packaging/docker/health.sh b/packaging/docker/health.sh new file mode 100755 index 0000000..00adf97 --- /dev/null +++ b/packaging/docker/health.sh @@ -0,0 +1,18 @@ +#!/bin/sh +# +# This is the script that gets run for our Docker image health checks. + +if [ -z "${NETDATA_HEALTHCHECK_TARGET}" ] ; then + # If users didn't request something else, query `/api/v1/info`. + PORT=${NETDATA_LISTENER_PORT:-19999} + NETDATA_HEALTHCHECK_TARGET="http://localhost:${PORT}/api/v1/info" +fi + +case "${NETDATA_HEALTHCHECK_TARGET}" in + cli) + netdatacli ping || exit 1 + ;; + *) + curl -sSL "${NETDATA_HEALTHCHECK_TARGET}" || exit 1 + ;; +esac diff --git a/packaging/docker/run.sh b/packaging/docker/run.sh new file mode 100755 index 0000000..1e00125 --- /dev/null +++ b/packaging/docker/run.sh @@ -0,0 +1,62 @@ +#!/usr/bin/env bash +# +# Entry point script for netdata +# +# Copyright: 2018 and later Netdata Inc. +# SPDX-License-Identifier: GPL-3.0-or-later +# +# Author : Pavlos Emm. Katsoulakis <paul@netdata.cloud> +# Author : Austin S. Hemmelgarn <austin@netdata.cloud> +set -e + +if [ ! -w / ] && [ "${EUID}" -eq 0 ]; then + echo >&2 "WARNING: This Docker host appears to not properly support newer stat system calls. This is known to cause issues with Netdata (most notably, nodes running on such hosts **cannot be claimed**)." + echo >&2 "WARNING: For more information, see https://learn.netdata.cloud/docs/agent/claim#known-issues-on-older-hosts-with-seccomp-enabled" +fi + +if [ ! "${DISABLE_TELEMETRY:-0}" -eq 0 ] || + [ -n "$DISABLE_TELEMETRY" ] || + [ ! "${DO_NOT_TRACK:-0}" -eq 0 ] || + [ -n "$DO_NOT_TRACK" ]; then + touch /etc/netdata/.opt-out-from-anonymous-statistics +fi + +BALENA_PGID=$(stat -c %g /var/run/balena.sock 2>/dev/null || true) +DOCKER_PGID=$(stat -c %g /var/run/docker.sock 2>/dev/null || true) + +re='^[0-9]+$' +if [[ $BALENA_PGID =~ $re ]]; then + echo "Netdata detected balena-engine.sock" + DOCKER_HOST='/var/run/balena-engine.sock' + PGID="$BALENA_PGID" +elif [[ $DOCKER_PGID =~ $re ]]; then + echo "Netdata detected docker.sock" + DOCKER_HOST="/var/run/docker.sock" + PGID="$DOCKER_PGID" +fi +export PGID +export DOCKER_HOST + +if [ -n "${PGID}" ]; then + echo "Creating docker group ${PGID}" + addgroup -g "${PGID}" "docker" || echo >&2 "Could not add group docker with ID ${PGID}, its already there probably" + echo "Assign netdata user to docker group ${PGID}" + usermod -a -G "${PGID}" "${DOCKER_USR}" || echo >&2 "Could not add netdata user to group docker with ID ${PGID}" +fi + +if mountpoint -q /etc/netdata && [ -z "$(ls -A /etc/netdata)" ]; then + echo "Copying stock configuration to /etc/netdata" + cp -a /etc/netdata.stock/. /etc/netdata +fi + +if [ -n "${NETDATA_CLAIM_URL}" ] && [ -n "${NETDATA_CLAIM_TOKEN}" ] && [ ! -f /var/lib/netdata/cloud.d/claimed_id ]; then + # shellcheck disable=SC2086 + /usr/sbin/netdata-claim.sh -token="${NETDATA_CLAIM_TOKEN}" \ + -url="${NETDATA_CLAIM_URL}" \ + ${NETDATA_CLAIM_ROOMS:+-rooms="${NETDATA_CLAIM_ROOMS}"} \ + ${NETDATA_CLAIM_PROXY:+-proxy="${NETDATA_CLAIM_PROXY}"} \ + ${NETDATA_EXTRA_CLAIM_OPTS} \ + -daemon-not-running +fi + +exec /usr/sbin/netdata -u "${DOCKER_USR}" -D -s /host -p "${NETDATA_LISTENER_PORT}" "$@" diff --git a/packaging/ebpf-co-re.checksums b/packaging/ebpf-co-re.checksums new file mode 100644 index 0000000..da7cb05 --- /dev/null +++ b/packaging/ebpf-co-re.checksums @@ -0,0 +1 @@ +9fe4fccc160ca9e0fd0ffd8894dbf6e5fddcf9ca3a4ee04cb645bb7703e8cef2 netdata-ebpf-co-re-glibc-v1.0.1.tar.xz diff --git a/packaging/ebpf-co-re.version b/packaging/ebpf-co-re.version new file mode 100644 index 0000000..b18d465 --- /dev/null +++ b/packaging/ebpf-co-re.version @@ -0,0 +1 @@ +v1.0.1 diff --git a/packaging/ebpf.checksums b/packaging/ebpf.checksums new file mode 100644 index 0000000..e5afcb8 --- /dev/null +++ b/packaging/ebpf.checksums @@ -0,0 +1,3 @@ +e3836908a5cfd5a1b6c71463645ed7040be1a4890767844b744fe1054910b51f ./netdata-kernel-collector-glibc-v1.0.1.tar.xz +091382fece7a470e505df4c655d834a8a49e50aa2a2fec4a52a324ab0ccd9870 ./netdata-kernel-collector-musl-v1.0.1.tar.xz +11497ccb4f2cdac0d80b00bf97d2f1633c972e8720abdda2a63bd0de95859840 ./netdata-kernel-collector-static-v1.0.1.tar.xz diff --git a/packaging/ebpf.version b/packaging/ebpf.version new file mode 100644 index 0000000..b18d465 --- /dev/null +++ b/packaging/ebpf.version @@ -0,0 +1 @@ +v1.0.1 diff --git a/packaging/go.d.checksums b/packaging/go.d.checksums new file mode 100644 index 0000000..806a45f --- /dev/null +++ b/packaging/go.d.checksums @@ -0,0 +1,17 @@ +67335df67f1629d9dc6dc559f91d26499f023b43a3fb2cece22d7c2919653dae *config.tar.gz +cae0acc8c19112c35927ccd4ef53f594c8d805467f204db84305ca8ddfccfcfa *go.d.plugin-v0.45.0.darwin-amd64.tar.gz +dcaddcea32a26392db7f13867226c62ba87aeb00c93931d1fc10d0641eb04e3a *go.d.plugin-v0.45.0.darwin-arm64.tar.gz +e89153033d2b8d6b59f163f1419ebaaae8414054f1a33bca52f76651848b528d *go.d.plugin-v0.45.0.freebsd-386.tar.gz +da3ba485995a60879cb51819ac2f9ecf81d23f64a0afb584bdc134a1fe4a2251 *go.d.plugin-v0.45.0.freebsd-amd64.tar.gz +ca1e153ac90714c0956a7ed4bcf14bf263f2c65a1876e9c8c24dd1b2bcd5b74a *go.d.plugin-v0.45.0.freebsd-arm.tar.gz +e25fcd7c3fa8aed01efff8ea25c3276de65d2efacff70fa4670a970272ffbba3 *go.d.plugin-v0.45.0.freebsd-arm64.tar.gz +7bfd345bdc30292a9145e4397b15a9004d78049006702727cd5a52900531dfa1 *go.d.plugin-v0.45.0.linux-386.tar.gz +7a6dd92ab6892aedd0a257ffbded54a0efa7cf95fb7f738387c8d7394e57eb09 *go.d.plugin-v0.45.0.linux-amd64.tar.gz +834a26c486a579991d76dc07625e135bf13fe4387627076bdbbb14bcb55ff978 *go.d.plugin-v0.45.0.linux-arm.tar.gz +1dda73a062ba20d2996334d878fd74207ad49b9f164530a5ad2144c70947d5a8 *go.d.plugin-v0.45.0.linux-arm64.tar.gz +8b52e67cf1e4d11776d5c5c8a4e246412caa1cffd36bafa5a8cb38a8e1867dee *go.d.plugin-v0.45.0.linux-mips.tar.gz +9a95f9df3527693a0a92c7b8ef1bec537e84014c75f32604adce4540e924576e *go.d.plugin-v0.45.0.linux-mips64.tar.gz +4ce0ec6068edf8218f68785f6ce258ed76ffea50a5953f7f75b9a48e1d912a81 *go.d.plugin-v0.45.0.linux-mips64le.tar.gz +360812ea936768926b38031c9dff2ecda2c80733e875f1c317371dee9d56a76c *go.d.plugin-v0.45.0.linux-mipsle.tar.gz +d7b594d84d47a0d2c6265c8fa9317285a53821f3e9aac5d31bcce0c8706fb369 *go.d.plugin-v0.45.0.linux-ppc64.tar.gz +dc29665076eecfb05d63ac243f97bd4d09f8dedae8c5285b349bd227e34ce249 *go.d.plugin-v0.45.0.linux-ppc64le.tar.gz diff --git a/packaging/go.d.version b/packaging/go.d.version new file mode 100644 index 0000000..67d3cf4 --- /dev/null +++ b/packaging/go.d.version @@ -0,0 +1 @@ +v0.45.0 diff --git a/packaging/installer/README.md b/packaging/installer/README.md new file mode 100644 index 0000000..3a4237d --- /dev/null +++ b/packaging/installer/README.md @@ -0,0 +1,218 @@ +<!-- +title: "Installation guide" +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/README.md +--> + +import { Install, InstallBox } from '@site/src/components/Install/' + +import { OneLineInstallWget, OneLineInstallCurl } from '@site/src/components/OneLineInstall/' + +# Installation guide + +Netdata is a monitoring agent designed to run on all your systems: physical and virtual servers, containers, even +IoT/edge devices. Netdata runs on Linux, FreeBSD, macOS, Kubernetes, Docker, and all their derivatives. + +The best way to install Netdata is with our [**automatic one-line installation +script**](#automatic-one-line-installation-script), which works with all Linux distributions and most macOS environments. + +If you want to install Netdata with Docker, on a Kubernetes cluster, or a different operating system, see [Have a +different operating system, or want to try another +method?](#have-a-different-operating-system-or-want-to-try-another-method) + +Some third parties, such as the packaging teams at various Linux distributions, distribute old, broken, or altered +packages. We recommend you install Netdata using one of the methods listed below to guarantee you get the latest +checksum-verified packages. + +Netdata collects anonymous usage information by default and sends it to our self hosted [PostHog](https://github.com/PostHog/posthog) installation. PostHog is an open source product analytics platform, you can read +about the information collected, and learn how to-opt, on our [anonymous statistics](/docs/anonymous-statistics.md) +page. + +The usage statistics are _vital_ for us, as we use them to discover bugs and prioritize new features. We thank you for +_actively_ contributing to Netdata's future. + +## Automatic one-line installation script + +  + +This method is fully automatic on all Linux distributions, including Ubuntu, Debian, Fedora, CentOS, and others, as well as on mac OS environments. + +To install Netdata, including all dependencies required to connect to Netdata Cloud, and get _automatic nightly +updates_, run the following as your normal user: + +<OneLineInstallWget/> + +Or, if you have cURL but not wget (such as on macOS): + +<OneLineInstallCurl/> + +This script will preferentially use native DEB/RPM packages if we provide them for your platform. + +To see more information about this installation script, including how to disable automatic updates, get nightly vs. +stable releases, or disable anonymous statistics, see the [`kickstart.sh` method +page](/packaging/installer/methods/kickstart.md). + +Scroll down for details about [automatic updates](#automatic-updates) or [nightly vs. stable +releases](#nightly-vs-stable-releases). + +### Post-installation + +When you're finished with installation, check out our [single-node](/docs/quickstart/single-node.md) or +[infrastructure](/docs/quickstart/infrastructure.md) monitoring quickstart guides based on your use case. + +Or, skip straight to [configuring the Netdata Agent](/docs/configure/nodes.md). + +Read through Netdata's [documentation](https://learn.netdata.cloud/docs), which is structured based on actions and +solutions, to enable features like health monitoring, alarm notifications, long-term metrics storage, exporting to +external databases, and more. + +## Have a different operating system, or want to try another method? + +Netdata works on many different platforms. To see all supported platforms, check out our [platform support +policy](/packaging/PLATFORM_SUPPORT.md). + +Below, you can find a few additional installation methods, followed by separate instructions for a variety of unique +operating systems. + +### Alternative methods + +<Install> + <InstallBox + to="/docs/agent/packaging/installer/methods/kickstart" + os="General Linux with one-line installer (recommended)" + svg="linux" /> + <InstallBox + to="/docs/agent/packaging/docker" + os="Run with Docker" + svg="docker" /> + <InstallBox + to="/docs/agent/packaging/installer/methods/kubernetes" + os="Deploy on Kubernetes" + svg="kubernetes" /> + <InstallBox + to="/docs/agent/packaging/installer/methods/macos" + os="Install on macOS" + svg="macos" /> + <InstallBox + to="/docs/agent/packaging/installer/methods/manual" + os="Linux from Git" + svg="linux" /> + <InstallBox + to="/docs/agent/packaging/installer/methods/source" + os="Linux from source" + svg="linux" /> + <InstallBox + to="/docs/agent/packaging/installer/methods/offline" + os="Linux for offline nodes" + svg="linux" /> +</Install> + +## Automatic updates + +By default, Netdata's installation scripts enable automatic updates for both nightly and stable release channels. + +If you would prefer to update your Netdata agent manually, you can disable automatic updates by using the `--no-updates` +option when you install or update Netdata using the [automatic one-line installation +script](#automatic-one-line-installation-script). + +```bash +wget -O /tmp/netdata-kickstart.sh https://my-netdata.io/kickstart.sh && sh /tmp/netdata-kickstart.sh --no-updates +``` + +With automatic updates disabled, you can choose exactly when and how you [update +Netdata](/packaging/installer/UPDATE.md). + +### Network usage of Netdata’s automatic updater + +The auto-update functionality set up by the installation scripts requires working internet access to function +correctly. In particular, it currently requires access to GitHub (to check if a newer version of the updater script +is available or not, as well as potentially fetching build-time dependencies that are bundled as part of the install), +and Google Cloud Storage (to check for newer versions of Netdata and download the sources if there is a newer version). + +Note that the auto-update functionality will check for updates to itself independently of updates to Netdata, +and will try to use the latest version of the updater script whenever possible. This is intended to reduce the +amount of effort required by users to get updates working again in the event of a bug in the updater code. + +## Nightly vs. stable releases + +The Netdata team maintains two releases of the Netdata agent: **nightly** and **stable**. By default, Netdata's +installation scripts will give you **automatic, nightly** updates, as that is our recommended configuration. + +**Nightly**: We create nightly builds every 24 hours. They contain fully-tested code that fixes bugs or security flaws, +or introduces new features to Netdata. Every nightly release is a candidate for then becoming a stable release—when +we're ready, we simply change the release tags on GitHub. That means nightly releases are stable and proven to function +correctly in the vast majority of Netdata use cases. That's why nightly is the _best choice for most Netdata users_. + +**Stable**: We create stable releases whenever we believe the code has reached a major milestone. Most often, stable +releases correlate with the introduction of new, significant features. Stable releases might be a better choice for +those who run Netdata in _mission-critical production systems_, as updates will come more infrequently, and only after +the community helps fix any bugs that might have been introduced in previous releases. + +**Pros of using nightly releases:** + +- Get the latest features and bug fixes as soon as they're available +- Receive security-related fixes immediately +- Use stable, fully-tested code that's always improving +- Leverage the same Netdata experience our community is using + +**Pros of using stable releases:** + +- Protect yourself from the rare instance when major bugs slip through our testing and negatively affect a Netdata + installation +- Retain more control over the Netdata version you use + +## Troubleshooting and known issues + +We are tracking a few issues related to installation and packaging. + +### Older distributions (Ubuntu 14.04, Debian 8, CentOS 6) and OpenSSL + +If you're running an older Linux distribution or one that has reached EOL, such as Ubuntu 14.04 LTS, Debian 8, or CentOS +6, your Agent may not be able to securely connect to Netdata Cloud due to an outdated version of OpenSSL. These old +versions of OpenSSL cannot perform [hostname validation](https://wiki.openssl.org/index.php/Hostname_validation), which +helps securely encrypt SSL connections. + +If you choose to continue using the outdated version of OpenSSL, your node will still connect to Netdata Cloud, albeit +with hostname verification disabled. Without verification, your Netdata Cloud connection could be vulnerable to +man-in-the-middle attacks. + +### CentOS 6 and CentOS 8 + +To install the Agent on certain CentOS and RHEL systems, you must enable non-default repositories, such as EPEL or +PowerTools, to gather hard dependencies. See the [CentOS 6](/packaging/installer/methods/manual.md#centos--rhel-6x) and +[CentOS 8](/packaging/installer/methods/manual.md#centos--rhel-8x) sections for more information. + +### Access to file is not permitted + +If you see an error similar to `Access to file is not permitted: /usr/share/netdata/web//index.html` when you try to +visit the Agent dashboard at `http://NODE:19999`, you need to update Netdata's permissions to match those of your +system. + +Run `ls -la /usr/share/netdata/web/index.html` to find the file's permissions. You may need to change this path based on +the error you're seeing in your browser. In the below example, the file is owned by the user `root` and the group +`root`. + +```bash +ls -la /usr/share/netdata/web/index.html +-rw-r--r--. 1 root root 89377 May 5 06:30 /usr/share/netdata/web/index.html +``` + +These files need to have the same user and group used to install your netdata. Suppose you installed netdata with user +`netdata` and group `netdata`, in this scenario you will need to run the following command to fix the error: + +```bash +# chown -R netdata.netdata /usr/share/netdata/web +``` + +### Multiple versions of OpenSSL + +We've received reports from the community about issues with running the `kickstart.sh` script on systems that have both +a distribution-installed version of OpenSSL and a manually-installed local version. The Agent's installer cannot handle +both. + +### Clang compiler on Linux + +Our current build process has some issues when using certain configurations of the `clang` C compiler on Linux. See [the +section on `nonrepresentable section on output` +errors](/packaging/installer/methods/manual.md#nonrepresentable-section-on-output-errors) for a workaround. + + diff --git a/packaging/installer/REINSTALL.md b/packaging/installer/REINSTALL.md new file mode 100644 index 0000000..1356c70 --- /dev/null +++ b/packaging/installer/REINSTALL.md @@ -0,0 +1,72 @@ +<!-- +title: "Reinstall the Netdata Agent" +description: "Troubleshooting installation issues or force an update of the Netdata Agent by reinstalling it using the same method you used during installation." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/REINSTALL.md +--> + +# Reinstall the Netdata Agent + +In certain situations, such as needing to enable a feature or troubleshoot an issue, you may need to reinstall the +Netdata Agent on your node. + +## One-line installer script (`kickstart.sh`) + +### Reinstalling with the same install type + +Run the one-line installer script with the `--reinstall` parameter to reinstall the Netdata Agent. This will preserve +any [user configuration](/docs/configure/nodes.md) in `netdata.conf` or other files, and will keep the same install +type that was used for the original install. + +If you used any [optional +parameters](/packaging/installer/methods/kickstart.md#optional-parameters-to-alter-your-installation) during initial +installation, you need to pass them to the script again during reinstallation. If you cannot remember which options you +used, read the contents of the `.environment` file and look for a `REINSTALL_OPTIONS` line. This line contains a list of +optional parameters. + +```bash +wget -O /tmp/netdata-kickstart.sh https://my-netdata.io/kickstart.sh && sh /tmp/netdata-kickstart.sh --reinstall +``` + +### Performing a clean reinstall + +Run the one-line installer script with the `--reinstall-clean` parameter to perform a clean reinstall of the +Netdata Agent. This will wipe all existing configuration and historical data, but can be useful sometimes for +getting a badly broken installation working again. Unlike the regular `--reinstall` parameter, this may use a +different install type than the original install used. + +If you used any [optional +parameters](/packaging/installer/methods/kickstart.md#optional-parameters-to-alter-your-installation) during initial +installation, you need to pass them to the script again during reinstallation. If you cannot remember which options you +used, read the contents of the `.environment` file and look for a `REINSTALL_OPTIONS` line. This line contains a list of +optional parameters. + +```bash +wget -O /tmp/netdata-kickstart.sh https://my-netdata.io/kickstart.sh && sh /tmp/netdata-kickstart.sh --reinstall-clean +``` + +### Changing the install type of an existing installation + +The clean reinstall procedure outlined above can also be used to manually change the install type for an existing +installation. Without any extra parameters, it will automatically pick the preferred installation type for your +system, even if that has changed since the original install. If you want to force use of a specific install type, +you can use the `--native-only`, `--static-only`, or `--build-only` parameter to control which install type gets +used, just like with a new install. + +When using the `--reinstall-clean` option to change the install type, you will need to manually preserve any +configuration or historical data you want to keep. The following directories may need to be preserved: + +- `/etc/netdata` (`/opt/netdata/etc/netdata` for static installs): For agent configuration. +- `/var/lib/netdata` (`/opt/netdata/var/lib/netdata` for static installs): For claiming configuration. +- `/var/cache/netdata` (`/opt/netdata/var/cache/netdata` for static installs): For historical data. + +When copying these directories back after the reinstall, you may need to update file ownership by running `chown +-R netdata:netdata` on them. + +## Troubleshooting + +If you still experience problems with your Netdata Agent installation after following one of these processes, the next +best route is to [uninstall](/packaging/installer/UNINSTALL.md) and then try a fresh installation using the [one-line +installer](/packaging/installer/methods/kickstart.md). + +You can also post to our [community forums](https://community.netdata.cloud/c/support/13) or create a new [bug +report](https://github.com/netdata/netdata/issues/new?assignees=&labels=bug%2Cneeds+triage&template=BUG_REPORT.yml). diff --git a/packaging/installer/UNINSTALL.md b/packaging/installer/UNINSTALL.md new file mode 100644 index 0000000..af2314f --- /dev/null +++ b/packaging/installer/UNINSTALL.md @@ -0,0 +1,92 @@ +<!-- +title: "Uninstall Netdata" +description: "If you are no longer interested in using the Netdata Agent, use the self-contained uninstaller to remove all traces of binaries and configuration files." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/UNINSTALL.md +--> + +# Uninstall Netdata + +> ⚠️ If you're having trouble updating Netdata, moving from one installation method to another, or generally having +> issues with your Netdata Agent installation, consider our [**reinstall Netdata** +> doc](/packaging/installer/REINSTALL.md) instead of removing the Netdata Agent entirely. + +The recommended method to uninstall Netdata on a system is to use our kickstart installer script with the `--uninstall` option like so: + +```sh +wget -O /tmp/netdata-kickstart.sh https://my-netdata.io/kickstart.sh && sh /tmp/netdata-kickstart.sh --uninstall +``` + +Or (if you have curl but not wget): + +```sh +curl https://my-netdata.io/kickstart.sh > /tmp/netdata-kickstart.sh && sh /tmp/netdata-kickstart.sh --uninstall +``` + +This will work in most cases without you needing to do anything more other than accepting removal of configuration +and data files. You can confirm whether this approach will work for you by adding `--dry-run` to the list of +options. If that produces a line with a message like `Would attempt to uninstall existing install`, then this +method will work on your system. + +If you used a non-standard installation prefix, you may need to specify that prefix using the `--old-install-prefix` +option when uninstalling this way. + +## Unofficial installs + +If you used a third-party package to install Netdata, then the above method will usually not work, and you will +need to use whatever mechanism you used to originally install Netdata to uninstall it. + +## Uninstalling manually + +Most official installs of Netdata include an uninstaller script that can be manually invoked instead of using the +kickstart script (internally, the kickstart script also uses this uninstaller script, it just handles the process +outlined below for you). + +This uninstaller script is self-contained other than requiring a `.environment` file that was generated during +installation. In most cases, this will be found in `/etc/netdata/.environment`, though if you used a non-standard +installation prefix it will usually be located in a similar place under that prefix. + +A workflow for uninstallation looks like this: + +1. Find your `.environment` file, which is usually `/etc/netdata/.environment` in a default installation. +2. If you cannot find that file and would like to uninstall Netdata, then create a new file with the following content: + +```sh +NETDATA_PREFIX="<installation prefix>" # put what you used as a parameter to shell installed `--install` flag. Otherwise it should be empty +NETDATA_ADDED_TO_GROUPS="<additional groups>" # Additional groups for a user running the Netdata process +``` + +3. Run `netdata-uninstaller.sh` as follows + + 3.1 **Interactive mode (Default)** + + The default mode in the uninstaller script is **interactive**. This means that the script provides you + the option to reply with "yes" (`y`/`Y`) or "no" (`n`/`N`) to control the removal of each Netdata asset in + the filesystem. + + ```sh + ${NETDATA_PREFIX}/usr/libexec/netdata/netdata-uninstaller.sh --yes --env <environment_file> + ``` + + 3.2 **Non-interactive mode** + + If you are sure and you know what you are doing, you can speed up the removal of the Netdata assets from the + filesystem without any questions by using the force option (`-f`/`--force`). This option will remove all the + Netdata assets in a **non-interactive** mode. + + ```sh + ${NETDATA_PREFIX}/usr/libexec/netdata/netdata-uninstaller.sh --yes --force --env <environment_file> + ``` + +Note: Existing installations may still need to download the file if it's not present. To execute uninstall in that case, +run the following commands: + +```sh +wget https://raw.githubusercontent.com/netdata/netdata/master/packaging/installer/netdata-uninstaller.sh +chmod +x ./netdata-uninstaller.sh +./netdata-uninstaller.sh --yes --env <environment_file> +``` + +The default `environment_file` is `/etc/netdata/.environment`. + +> Note: This uninstallation method assumes previous installation with `netdata-installer.sh` or the kickstart script. +> Using it when Netdata was installed in some other way will usually not work correctly, and may make it harder to uninstall Netdata. diff --git a/packaging/installer/UPDATE.md b/packaging/installer/UPDATE.md new file mode 100644 index 0000000..009e970 --- /dev/null +++ b/packaging/installer/UPDATE.md @@ -0,0 +1,174 @@ +<!-- +title: "Update the Netdata Agent" +description: "If you opted out of automatic updates, you need to update your Netdata Agent to the latest nightly or stable version." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/UPDATE.md +--> + +# Update the Netdata Agent + +By default, the Netdata Agent automatically updates with the latest nightly or stable version depending on which +you installed. If you opted out of automatic updates, you need to update your Netdata Agent to the latest nightly +or stable version. You can also [enable or disable automatic updates on an existing install](#control-automatic-updates). + +> 💡 Looking to reinstall the Netdata Agent to enable a feature, update an Agent that cannot update automatically, or +> troubleshoot an error during the installation process? See our [reinstallation doc](/packaging/installer/REINSTALL.md) +> for reinstallation steps. + +Before you update the Netdata Agent, check to see if your Netdata Agent is already up-to-date by clicking on the update +icon in the local Agent dashboard's top navigation. This modal informs you whether your Agent needs an update or not. + +The exact update method to use depends on the install type: + +- Installs with an install type of 'custom' usually indicate installing a third-party package through the system + package manager. To update these installs, you should update the package just like you would any other package + on your system. +- Installs with an install type starting with `binpkg` or ending with `build` or `static` can be updated using + our [regular update method](#updates-for-most-systems). +- Installs with an install type of 'oci' were created from our official Docker images, and should be updated + using our [Docker](#docker) update procedure. +- macOS users should check [our update instructions for macOS](#macos). +- Manually built installs should check [our update instructions for manual builds](#manual-installation-from-git). + +## Determine which installation method you used + +Starting with netdata v1.33.0, you can use Netdata itself to determine the installation type by running: + +```bash +netdata -W buildinfo | grep 'Install type:' +``` + +If you are using an older version of Netdata, or the above command produces no output, you can run our one-line +installation script in dry-run mode to attempt to determine what method to use to update by running the following +command: + +```bash +wget -O /tmp/netdata-kickstart.sh https://my-netdata.io/kickstart.sh && sh /tmp/netdata-kickstart.sh --dry-run +``` + +Note that if you installed Netdata using an installation prefix, you will need to add an `--install` option +specifying that prefix to make sure it finds the existing install. + +If you see a line starting with `--- Would attempt to update existing installation by running the updater script +located at:`, then our [regular update method](#updates-for-most-systems) will work for you. + +Otherwise, it should either indicate that the installation type is not supported (which probably means you either +have a `custom` instal or built Netdata manually) or indicate that it would create a new install (which means that +you either used a non-standard install path, or that you don’t actually have Netdata installed). + +## Updates for most systems + +In most cases, you can update netdata using our one-line installation script. This script will automatically +run the update script that was installed as part of the initial install (even if you disabled automatic updates) +and preserve the existing install options you specified. + +If you installed Netdata using an installation prefix, you will need to add an `--install` option specifying +that prefix to this command to make sure it finds Netdata. + +```bash +wget -O /tmp/netdata-kickstart.sh https://my-netdata.io/kickstart.sh && sh /tmp/netdata-kickstart.sh +``` + +### Issues with older binpkg installs + +The above command is known not to work with binpkg type installs for stable releases with a version number of +v1.33.1 or earlier, and nightly builds with a version number of v1.33.1-93 or earlier. If you have such a system, +the above command will report that it found an existing install, and then issue a warning about not being able to +find the updater script. + +On such installs, you can update Netdata using your distribution package manager. + +### If the kickstart script does not work + +If the above command fails, you can [reinstall +Netdata](/packaging/installer/REINSTALL.md#one-line-installer-script-kickstartsh) to get the latest version. This +also preserves your [configuration](/docs/configure/nodes.md) in `netdata.conf` or other files just like updating +normally would, though you will need to specify any installation options you used originally again. + +## Docker + +Docker-based installations do not update automatically. To update an Netdata Agent running in a Docker container, you +must pull the [latest image from Docker Hub](https://hub.docker.com/r/netdata/netdata), stop and remove the container, +and re-create it using the latest image. + +First, pull the latest version of the image. + +```bash +docker pull netdata/netdata:latest +``` + +Next, to stop and remove any containers using the `netdata/netdata` image. Replace `netdata` if you changed it from the +default. + +```bash +docker stop netdata +docker rm netdata +``` + +You can now re-create your Netdata container using the `docker` command or a `docker-compose.yml` file. See our [Docker +installation instructions](/packaging/docker/README.md#create-a-new-netdata-agent-container) for details. + +## macOS + +If you installed Netdata on your macOS system using Homebrew, you can explicitly request an update: + +```bash +brew upgrade netdata +``` + +Homebrew downloads the latest Netdata via the +[formulae](https://github.com/Homebrew/homebrew-core/blob/master/Formula/netdata.rb), ensures all dependencies are met, +and updates Netdata via reinstallation. + +If you instead installed Netdata using our one-line installation script, you can use our [regular update +instructions](#updates-for-most-systems) to update Netdata. + +## Manual installation from Git + +If you installed [Netdata manually from Git](/packaging/installer/methods/manual.md), you can run that installer again +to update your agent. First, run our automatic requirements installer, which works on many Linux distributions, to +ensure your system has the dependencies necessary for new features. + +```bash +bash <(curl -sSL https://raw.githubusercontent.com/netdata/netdata/master/packaging/installer/install-required-packages.sh) +``` + +Navigate to the directory where you first cloned the Netdata repository, pull the latest source code, and run +`netdata-install.sh` again. This process compiles Netdata with the latest source code and updates it via reinstallation. + +```bash +cd /path/to/netdata/git +git pull origin master +sudo ./netdata-installer.sh +``` + +> ⚠️ If you installed Netdata with any optional parameters, such as `--no-updates` to disable automatic updates, and +> want to retain those settings, you need to set them again during this process. + +## Control automatic updates + +Starting with Netdata v1.34.0, you can easily enable or disable automatic updates on an existing installation +using the updater script. + +For most installs on Linux, you can enable auto-updates with: + +```bash +/usr/libexec/netdata/netdata-updater.sh --enable-auto-updates +``` + +and disable them with: + +```bash +/usr/libexec/netdata/netdata-updater.sh --disable-auto-updates +``` + +For static installs, instead use: + +```bash +/opt/netdata/usr/libexec/netdata/netdata-updater.sh --enable-auto-updates +``` + +and: + +```bash +/opt/netdata/usr/libexec/netdata/netdata-updater.sh --disable-auto-updates +``` diff --git a/packaging/installer/dependencies/alpine.sh b/packaging/installer/dependencies/alpine.sh new file mode 100755 index 0000000..65999dc --- /dev/null +++ b/packaging/installer/dependencies/alpine.sh @@ -0,0 +1,99 @@ +#!/usr/bin/env bash +# Package tree used for installing netdata on distribution: +# << Alpine: [3.12] [3.13] [3.14] [3.15] [edge] >> + +set -e + +NON_INTERACTIVE=0 +DONT_WAIT=0 + +package_tree=" + alpine-sdk + git + gcc + g++ + automake + autoconf + cmake + make + libatomic + libtool + pkgconfig + tar + curl + gzip + libuv-dev + lz4-dev + openssl-dev + elfutils-dev + python3 + zlib-dev + util-linux-dev + libmnl-dev + json-c-dev + " + +usage() { + cat << EOF +OPTIONS: +[--dont-wait] [--non-interactive] [ ] +EOF +} + +check_flags() { + while [ -n "${1}" ]; do + case "${1}" in + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift + done + + if [ "${DONT_WAIT}" -eq 0 ] && [ "${NON_INTERACTIVE}" -eq 0 ]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi +} + +# shellcheck disable=2068 +check_flags ${@} + +packages_to_install= + +for package in $package_tree; do + if apk -e info "$package" &> /dev/null; then + echo "Package '${package}' is installed" + else + echo "Package '${package}' is NOT installed" + packages_to_install="$packages_to_install $package" + fi +done + +if [[ -z $packages_to_install ]]; then + echo "All required packages are already installed. Skipping .." +else + echo "packages_to_install:" "$packages_to_install" + opts="--force-broken-world" + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + else + opts="${opts} -i" + fi + # shellcheck disable=SC2086 + apk add ${opts} $packages_to_install +fi diff --git a/packaging/installer/dependencies/arch.sh b/packaging/installer/dependencies/arch.sh new file mode 100755 index 0000000..cdda527 --- /dev/null +++ b/packaging/installer/dependencies/arch.sh @@ -0,0 +1,99 @@ +#!/usr/bin/env bash +# Package tree used for installing netdata on distribution: +# << ArchLinux: [base] [base-devel] >> | << Manjaro >> + +set -e + +NON_INTERACTIVE=0 +DONT_WAIT=0 + +declare -a package_tree=( + gcc + make + autoconf + autoconf-archive + autogen + automake + libtool + cmake + zlib + util-linux + libmnl + json-c + libuv + lz4 + openssl + libelf + git + pkgconfig + tar + curl + gzip + python3 + binutils +) + +usage() { + cat << EOF +OPTIONS: +[--dont-wait] [--non-interactive] [ ] +EOF +} + +check_flags() { + while [ -n "${1}" ]; do + case "${1}" in + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift + done + + if [ "${DONT_WAIT}" -eq 0 ] && [ "${NON_INTERACTIVE}" -eq 0 ]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi +} + +# shellcheck disable=SC2068 +check_flags ${@} + +packages_to_install= + +# shellcheck disable=SC2068 +for package in ${package_tree[@]}; do + if pacman -Qn "$package" &> /dev/null; then + echo "Package '${package}' is installed" + else + echo "Package '$package' is NOT installed" + packages_to_install="$packages_to_install $package" + fi +done + +if [[ -z $packages_to_install ]]; then + echo "All required packages are already installed. Skipping .." +else + echo "packages_to_install: " "${packages_to_install[@]}" + opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="--noconfirm" + fi + # shellcheck disable=SC2068 + pacman -Sy ${opts} ${packages_to_install[@]} +fi diff --git a/packaging/installer/dependencies/centos.sh b/packaging/installer/dependencies/centos.sh new file mode 100755 index 0000000..a05bce8 --- /dev/null +++ b/packaging/installer/dependencies/centos.sh @@ -0,0 +1,196 @@ +#!/usr/bin/env bash +# Package tree used for installing netdata on distribution: +# << CentOS: [7] [8] >> + +set -e + +declare -a package_tree=( + gcc + gcc-c++ + make + autoconf + autoconf-archive + automake + libatomic + libtool + pkgconfig + cmake + zlib-devel + libuuid-devel + libmnl-devel + json-c-devel + libuv-devel + lz4-devel + openssl-devel + python3 + elfutils-libelf-devel + git + tar + curl + gzip +) + +os_version() { + if [[ -f /etc/os-release ]]; then + # shellcheck disable=SC2002 + cat /etc/os-release | grep VERSION_ID | cut -d'=' -f2 | cut -d'"' -f2 + else + echo "Error: Cannot determine OS version!" + exit 1 + fi +} + +prompt() { + if [[ "${NON_INTERACTIVE}" == "1" ]]; then + echo >&2 "Running in non-interactive mode, assuming yes (y)" + echo >&2 " > Would have prompted for ${1} ..." + return 0 + fi + + while true; do + read -r -p "${1} [y/n] " yn + case $yn in + [Yy]*) return 0 ;; + [Nn]*) return 1 ;; + *) echo >&2 "Please answer with yes (y) or no (n)." ;; + esac + done +} + +usage() { + cat << EOF +OPTIONS: +[--dont-wait] [--non-interactive] [ ] +EOF +} + +check_flags() { + while [ -n "${1}" ]; do + case "${1}" in + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift + done + + if [[ "${DONT_WAIT}" == "0" ]] && [[ "${NON_INTERACTIVE}" == "0" ]]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi +} + +validate_tree_centos() { + local opts= + export local package_manager= + if [[ "${NON_INTERACTIVE}" == "1" ]]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + + echo >&2 " > CentOS Version: $(os_version) ..." + + if [[ $(os_version) =~ ^9(\..*)?$ ]]; then + package_manager=dnf + echo >&2 " > Checking for config-manager ..." + if ! dnf config-manager --help &> /dev/null; then + if prompt "config-manager not found, shall I install it?"; then + dnf ${opts} install 'dnf-command(config-manager)' + fi + fi + + echo >&2 " > Checking for CRB ..." + if ! dnf repolist | grep CRB; then + if prompt "CRB not found, shall I install it?"; then + dnf ${opts} config-manager --set-enabled crb + fi + fi + elif [[ $(os_version) =~ ^8(\..*)?$ ]]; then + package_manager=dnf + echo >&2 " > Checking for config-manager ..." + if ! dnf config-manager --help &> /dev/null; then + if prompt "config-manager not found, shall I install it?"; then + dnf ${opts} install 'dnf-command(config-manager)' + fi + fi + + echo >&2 " > Checking for PowerTools ..." + if ! dnf repolist | grep PowerTools; then + if prompt "PowerTools not found, shall I install it?"; then + dnf ${opts} config-manager --set-enabled powertools || enable_powertools_repo + fi + fi + + echo >&2 " > Updating libarchive ..." + dnf ${opts} install libarchive + + elif [[ $(os_version) =~ ^7(\..*)?$ ]]; then + package_manager=yum + echo >&2 " > Checking for EPEL ..." + if ! rpm -qa | grep epel-release > /dev/null; then + if prompt "EPEL not found, shall I install it?"; then + yum ${opts} install epel-release + fi + fi + yum makecache + fi +} + +enable_powertools_repo() { + if ! dnf repolist | grep -q powertools; then + cat > /etc/yum.repos.d/powertools.repo <<-EOF + [powertools] + name=CentOS Linux \$releasever - PowerTools + mirrorlist=http://mirrorlist.centos.org/?release=\$releasever&arch=\$basearch&repo=PowerTools&infra=\$infra + #baseurl=http://mirror.centos.org/\$contentdir/\$releasever/PowerTools/\$basearch/os/ + gpgcheck=1 + enabled=1 + gpgkey=file:///etc/pki/rpm-gpg/RPM-GPG-KEY-centosofficial +EOF + else + echo "Something went wrong!" + exit 1 + fi +} + +# shellcheck disable=SC2068 +check_flags ${@} +validate_tree_centos + +packages_to_install= + +for package in "${package_tree[@]}"; do + if rpm -q "$package" &> /dev/null; then + echo "Package '${package}' is installed" + else + echo "Package '$package' is NOT installed" + packages_to_install="$packages_to_install $package" + fi +done + +if [[ -z $packages_to_install ]]; then + echo "All required packages are already installed. Skipping .." +else + echo "packages_to_install:" "${packages_to_install[@]}" + opts= + if [[ "${NON_INTERACTIVE}" == "1" ]]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + # shellcheck disable=SC2068 + ${package_manager} install ${opts} ${packages_to_install[@]} +fi diff --git a/packaging/installer/dependencies/clearlinux.sh b/packaging/installer/dependencies/clearlinux.sh new file mode 100755 index 0000000..832dac5 --- /dev/null +++ b/packaging/installer/dependencies/clearlinux.sh @@ -0,0 +1,87 @@ +#!/usr/bin/env bash +# Package tree used for installing netdata on distribution: +# << ClearLinux: [base] >> + +set -e + +NON_INTERACTIVE=0 +DONT_WAIT=0 + +declare -a package_tree=( + c-basic + make + sysadmin-basic + devpkg-zlib + devpkg-util-linux + devpkg-libmnl + devpkg-json-c + devpkg-libuv + devpkg-lz4 + devpkg-openssl + devpkg-elfutils + git + findutils + curl + gzip + python3-basic +) + +usage() { + cat << EOF +OPTIONS: +[--dont-wait] [--non-interactive] [ ] +EOF +} + +check_flags() { + while [ -n "${1}" ]; do + case "${1}" in + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift + done + + if [ "${DONT_WAIT}" -eq 0 ] && [ "${NON_INTERACTIVE}" -eq 0 ]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi +} + +# shellcheck disable=SC2068 +check_flags ${@} + +packages_to_install= + +# shellcheck disable=SC2068 +for package in ${package_tree[@]}; do + if [[ "$(swupd bundle-info "$package" | grep Status | cut -d':' -f2)" == " Not installed" ]]; then + echo "Package '$package' is NOT installed" + packages_to_install="$packages_to_install $package" + else + echo "Package '$package' is installed" + fi +done + +if [[ -z $packages_to_install ]]; then + echo "All required packages are already installed. Skipping .." +else + echo "packages_to_install: " "${packages_to_install[@]}" + # shellcheck disable=SC2068 + swupd bundle-add ${packages_to_install[@]} +fi diff --git a/packaging/installer/dependencies/debian.sh b/packaging/installer/dependencies/debian.sh new file mode 100755 index 0000000..a2c421a --- /dev/null +++ b/packaging/installer/dependencies/debian.sh @@ -0,0 +1,104 @@ +#!/usr/bin/env bash +# Package tree used for installing netdata on distribution: +# << Debian: [9] [10] [11] >> + +set -e + +NON_INTERACTIVE=0 +DONT_WAIT=0 + +package_tree=" + git + gcc + g++ + make + automake + cmake + autoconf + autoconf-archive + autogen + libatomic1 + libtool + pkg-config + tar + curl + gzip + zlib1g-dev + uuid-dev + libmnl-dev + libjson-c-dev + libuv1-dev + liblz4-dev + libssl-dev + libelf-dev + python + python3 + " + +usage() { + cat << EOF +OPTIONS: +[--dont-wait] [--non-interactive] [ ] +EOF +} + +check_flags() { + while [ -n "${1}" ]; do + case "${1}" in + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift + done + + if [ "${DONT_WAIT}" -eq 0 ] && [ "${NON_INTERACTIVE}" -eq 0 ]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi +} + +# shellcheck disable=2068 +check_flags ${@} + +packages_to_install= + +for package in $package_tree; do + if dpkg -s "$package" &> /dev/null; then + echo "Package '${package}' is installed" + else + echo "Package '${package}' is NOT installed" + packages_to_install="$packages_to_install $package" + fi +done + +if [[ -z "$packages_to_install" ]]; then + echo "All required packages are already installed. Skipping .." +else + echo "packages_to_install:" "$packages_to_install" + opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + # shellcheck disable=SC2034 + DEBIAN_FRONTEND="noninteractive" + opts="${opts} -yq" + fi + echo "Running apt-get update and updating your APT caches ..." + apt-get update + # shellcheck disable=2086 + apt-get install ${opts} $packages_to_install +fi diff --git a/packaging/installer/dependencies/fedora.sh b/packaging/installer/dependencies/fedora.sh new file mode 100755 index 0000000..a1c3a1d --- /dev/null +++ b/packaging/installer/dependencies/fedora.sh @@ -0,0 +1,118 @@ +#!/usr/bin/env bash +# Package tree used for installing netdata on distribution: +# << Fedora: [24->35] >> + +set -e + +NON_INTERACTIVE=0 +DONT_WAIT=0 + +os_version() { + if [[ -f /etc/os-release ]]; then + # shellcheck disable=SC2002 + cat /etc/os-release | grep VERSION_ID | cut -d'=' -f2 + else + echo "Error: Cannot determine OS version!" + exit 1 + fi +} + +if [[ $(os_version) -gt 24 ]]; then + ulogd_pkg= +else + ulogd_pkg=ulogd +fi + +declare -a package_tree=( + findutils + gcc + gcc-c++ + make + autoconf + autoconf-archive + autogen + automake + libatomic + libtool + cmake + zlib-devel + libuuid-devel + libmnl-devel + json-c-devel + libuv-devel + lz4-devel + openssl-devel + elfutils-libelf-devel + git + pkgconfig + tar + curl + gzip + python3 + "${ulogd_pkg}" +) + +usage() { + cat << EOF +OPTIONS: +[--dont-wait] [--non-interactive] [ ] +EOF +} + +check_flags() { + while [ -n "${1}" ]; do + case "${1}" in + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift + done + + if [ "${DONT_WAIT}" -eq 0 ] && [ "${NON_INTERACTIVE}" -eq 0 ]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi +} + +# shellcheck disable=SC2068 +check_flags ${@} + +packages_to_install= + +# shellcheck disable=SC2068 +for package in ${package_tree[@]}; do + if rpm -q "$package" &> /dev/null; then + echo "Package '${package}' is installed" + else + echo "Package '$package' is NOT installed" + packages_to_install="$packages_to_install $package" + fi +done + +if [[ -z $packages_to_install ]]; then + echo "All required packages are already installed. Skipping .." +else + echo "packages_to_install:" "${packages_to_install[@]}" + opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + # shellcheck disable=SC2068 + dnf install ${opts} ${packages_to_install[@]} +fi diff --git a/packaging/installer/dependencies/freebsd.sh b/packaging/installer/dependencies/freebsd.sh new file mode 100755 index 0000000..9145135 --- /dev/null +++ b/packaging/installer/dependencies/freebsd.sh @@ -0,0 +1,142 @@ +#!/usr/bin/env bash +# Package tree used for installing netdata on distribution: +# << FreeBSD >> + +set -e + +NON_INTERACTIVE=0 +DONT_WAIT=0 + +package_tree=" + git + autoconf + autoconf-archive + autogen + automake + libtool + pkgconf + cmake + curl + gzip + lzlib + e2fsprogs-libuuid + json-c + libuv + liblz4 + openssl + python3 + " + +prompt() { + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode, assuming yes (y)" + echo >&2 " > Would have prompted for ${1} ..." + return 0 + fi + + while true; do + read -r -p "${1} [y/n] " yn + case $yn in + [Yy]*) return 0 ;; + [Nn]*) return 1 ;; + *) echo >&2 "Please answer with yes (y) or no (n)." ;; + esac + done +} + +usage() { + cat << EOF +OPTIONS: +[--dont-wait] [--non-interactive] [ ] +EOF +} + +check_flags() { + while [ -n "${1}" ]; do + case "${1}" in + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift + done + + if [ "${DONT_WAIT}" -eq 0 ] && [ "${NON_INTERACTIVE}" -eq 0 ]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi +} + +validate_tree_freebsd() { + opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + + echo >&2 " > Checking for gmake ..." + if ! pkg query %n-%v | grep -q gmake; then + if prompt "gmake is required to build on FreeBSD and is not installed. Shall I install it?"; then + pkg install ${opts} gmake + fi + fi +} + +enable_repo () { + if ! dnf repolist | grep -q codeready; then +cat >> /etc/yum.repos.d/oracle-linux-ol8.repo <<-EOF + +[ol8_codeready_builder] +name=Oracle Linux \$releasever CodeReady Builder (\$basearch) +baseurl=http://yum.oracle.com/repo/OracleLinux/OL8/codeready/builder/\$basearch +gpgkey=file:///etc/pki/rpm-gpg/RPM-GPG-KEY-oracle +gpgcheck=1 +enabled=1 +EOF + else + echo "Something went wrong!" + exit 1 + fi +} + +# shellcheck disable=SC2068 +check_flags ${@} +validate_tree_freebsd + +packages_to_install= + +for package in $package_tree; do + if pkg info -Ix "$package" &> /dev/null; then + echo "Package '${package}' is installed" + else + echo "Package '${package}' is NOT installed" + packages_to_install="$packages_to_install $package" + fi +done + +if [[ -z "$packages_to_install" ]]; then + echo "All required packages are already installed. Skipping .." +else + echo "packages_to_install:" "$packages_to_install" + opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + # shellcheck disable=SC2086 + pkg install ${opts} $packages_to_install +fi diff --git a/packaging/installer/dependencies/gentoo.sh b/packaging/installer/dependencies/gentoo.sh new file mode 100755 index 0000000..e7ed644 --- /dev/null +++ b/packaging/installer/dependencies/gentoo.sh @@ -0,0 +1,97 @@ +#!/usr/bin/env bash +# Package tree used for installing netdata on distribution: +# << Gentoo >> | << Pentoo >> + +set -e + +NON_INTERACTIVE=0 +DONT_WAIT=0 + +package_tree=" + dev-vcs/git + sys-apps/findutils + sys-devel/gcc + sys-devel/make + sys-devel/autoconf + sys-devel/autoconf-archive + sys-devel/autogen + sys-devel/automake + virtual/pkgconfig + dev-util/cmake + app-arch/tar + net-misc/curl + app-arch/gzip + sys-apps/util-linux + net-libs/libmnl + dev-libs/json-c + dev-libs/libuv + app-arch/lz4 + dev-libs/openssl + virtual/libelf + dev-lang/python + dev-libs/libuv + " +usage() { + cat << EOF +OPTIONS: +[--dont-wait] [--non-interactive] [ ] +EOF +} + +check_flags() { + while [ -n "${1}" ]; do + case "${1}" in + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift + done + + if [ "${DONT_WAIT}" -eq 0 ] && [ "${NON_INTERACTIVE}" -eq 0 ]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi +} + +# shellcheck disable=SC2068 +check_flags ${@} + +packages_to_install= + +# shellcheck disable=SC2068 +for package in $package_tree; do + if qlist -IRv "$package" &> /dev/null; then + echo "Package '${package}' is installed" + else + echo "Package '${package}' is NOT installed" + packages_to_install="$packages_to_install $package" + fi +done + +if [[ -z "$packages_to_install" ]]; then + echo "All required packages are already installed. Skipping .." +else + echo "packages_to_install:" "$packages_to_install" + opts="--ask" + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="" + fi + # shellcheck disable=SC2086 + emerge ${opts} $packages_to_install +fi diff --git a/packaging/installer/dependencies/macos.sh b/packaging/installer/dependencies/macos.sh new file mode 100755 index 0000000..e69de29 --- /dev/null +++ b/packaging/installer/dependencies/macos.sh diff --git a/packaging/installer/dependencies/ol.sh b/packaging/installer/dependencies/ol.sh new file mode 100755 index 0000000..0f1f90e --- /dev/null +++ b/packaging/installer/dependencies/ol.sh @@ -0,0 +1,156 @@ +#!/usr/bin/env bash +# Package tree used for installing netdata on distribution: +# << Oracle Linux: [8, 9] >> + +set -e + +NON_INTERACTIVE=0 +DONT_WAIT=0 + +declare -a package_tree=( + gcc + gcc-c++ + make + autoconf + autoconf-archive + autogen + automake + libatomic + libtool + pkgconfig + cmake + tar + zlib-devel + libuuid-devel + libmnl-devel + json-c-devel + libuv-devel + lz4-devel + openssl-devel + python3 + elfutils-libelf-devel + git + curl + gzip +) + +prompt() { + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode, assuming yes (y)" + echo >&2 " > Would have prompted for ${1} ..." + return 0 + fi + + while true; do + read -r -p "${1} [y/n] " yn + case $yn in + [Yy]*) return 0 ;; + [Nn]*) return 1 ;; + *) echo >&2 "Please answer with yes (y) or no (n)." ;; + esac + done +} + +usage() { + cat << EOF +OPTIONS: +[--dont-wait] [--non-interactive] [ ] +EOF +} + +check_flags() { + while [ -n "${1}" ]; do + case "${1}" in + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift + done + + if [ "${DONT_WAIT}" -eq 0 ] && [ "${NON_INTERACTIVE}" -eq 0 ]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi +} + +validate_tree_ol() { + opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + + # shellcheck disable=SC1091 + source /etc/os-release + + # shellcheck disable=SC2153 + version="$(echo "${VERSION}" | cut -f 1 -d '.')" + + echo >&2 " > Checking for config-manager ..." + if ! dnf config-manager &> /dev/null; then + if prompt "config-manager not found, shall I install it?"; then + dnf ${opts} install 'dnf-command(config-manager)' + fi + fi + + echo " > Checking for CodeReady Builder ..." + if [[ "${version}" =~ ^8(\..*)?$ ]]; then + if ! dnf repolist enabled | grep ol8_codeready_builder; then + if prompt "CodeReadyBuilder not found, shall I install it?"; then + dnf ${opts} config-manager --set-enabled ol8_codeready_builder || enable_repo + fi + fi + elif [[ "${version}" =~ ^9(\..*)?$ ]]; then + if ! dnf repolist enabled | grep ol9_codeready_builder; then + if prompt "CodeReadyBuilder not found, shall I install it?"; then + dnf ${opts} config-manager --set-enabled ol9_codeready_builder || enable_repo + fi + fi + fi + + dnf makecache --refresh +} + +# shellcheck disable=SC2068 +check_flags ${@} +validate_tree_ol + +packages_to_install= + +# shellcheck disable=SC2068 +for package in ${package_tree[@]}; do + if rpm -q "$package" &> /dev/null; then + echo "Package '${package}' is installed" + else + echo "Package '$package' is NOT installed" + packages_to_install="$packages_to_install $package" + fi +done + +if [[ -z $packages_to_install ]]; then + echo "All required packages are already installed. Skipping .." +else + opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + echo "packages_to_install:" "${packages_to_install[@]}" + # shellcheck disable=SC2068 + dnf install ${opts} ${packages_to_install[@]} +fi diff --git a/packaging/installer/dependencies/opensuse.sh b/packaging/installer/dependencies/opensuse.sh new file mode 100755 index 0000000..b1f0c21 --- /dev/null +++ b/packaging/installer/dependencies/opensuse.sh @@ -0,0 +1,102 @@ +#!/usr/bin/env bash +# Package tree used for installing netdata on distribution: +# << opeSUSE >> +# supported versions: leap/15.3 and tumbleweed +# it may work with SLES as well, although we have not tested with it + +set -e + +NON_INTERACTIVE=0 +DONT_WAIT=0 + +declare -a package_tree=( + gcc + gcc-c++ + make + autoconf + autoconf-archive + autogen + automake + libatomic1 + libtool + pkg-config + cmake + zlib-devel + libuuid-devel + libmnl-devel + libjson-c-devel + libuv-devel + liblz4-devel + libopenssl-devel + libelf-devel + git + tar + curl + gzip + python3 +) + +usage() { + cat << EOF +OPTIONS: +[--dont-wait] [--non-interactive] [ ] +EOF +} + +check_flags() { + while [ -n "${1}" ]; do + case "${1}" in + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift + done + + if [ "${DONT_WAIT}" -eq 0 ] && [ "${NON_INTERACTIVE}" -eq 0 ]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi +} + +# shellcheck disable=SC2068 +check_flags ${@} + +packages_to_install= + +# shellcheck disable=SC2068 +for package in ${package_tree[@]}; do + if zypper search -i "$package" &> /dev/null; then + echo "Package '${package}' is installed" + else + echo "Package '$package' is NOT installed" + packages_to_install="$packages_to_install $package" + fi +done + +if [[ -z $packages_to_install ]]; then + echo "All required packages are already installed. Skipping .." +else + echo "packages_to_install:" "${packages_to_install[@]}" + opts="--ignore-unknown" + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="--non-interactive" + fi + # shellcheck disable=SC2068 + zypper ${opts} install ${packages_to_install[@]} +fi diff --git a/packaging/installer/dependencies/rhel.sh b/packaging/installer/dependencies/rhel.sh new file mode 100755 index 0000000..e69de29 --- /dev/null +++ b/packaging/installer/dependencies/rhel.sh diff --git a/packaging/installer/dependencies/rockylinux.sh b/packaging/installer/dependencies/rockylinux.sh new file mode 100755 index 0000000..63981df --- /dev/null +++ b/packaging/installer/dependencies/rockylinux.sh @@ -0,0 +1,162 @@ +#!/usr/bin/env bash +# Package tree used for installing netdata on distribution: +# << Rocky Linux:[8.5] >> + +set -e + +NON_INTERACTIVE=0 +DONT_WAIT=0 + +declare -a package_tree=( + gcc + gcc-c++ + make + autoconf + autoconf-archive + autogen + automake + libatomic + libtool + pkgconfig + cmake + zlib-devel + libuuid-devel + libmnl-devel + json-c-devel + libuv-devel + lz4-devel + openssl-devel + python3 + elfutils-libelf-devel + git + tar + curl + gzip +) + +prompt() { + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode, assuming yes (y)" + echo >&2 " > Would have prompted for ${1} ..." + return 0 + fi + + while true; do + read -r -p "${1} [y/n] " yn + case $yn in + [Yy]*) return 0 ;; + [Nn]*) return 1 ;; + *) echo >&2 "Please answer with yes (y) or no (n)." ;; + esac + done +} + +usage() { + cat << EOF +OPTIONS: +[--dont-wait] [--non-interactive] [ ] +EOF +} + +check_flags() { + while [ -n "${1}" ]; do + case "${1}" in + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift + done + + if [ "${DONT_WAIT}" -eq 0 ] && [ "${NON_INTERACTIVE}" -eq 0 ]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi +} + +validate_tree_rockylinux() { + local opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + + echo >&2 " > Checking for config-manager ..." + if ! dnf config-manager; then + if prompt "config-manager not found, shall I install it?"; then + dnf ${opts} install 'dnf-command(config-manager)' + fi + fi + + echo >&2 " > Checking for PowerTools ..." + if ! dnf repolist | grep PowerTools; then + if prompt "PowerTools not found, shall I install it?"; then + dnf ${opts} config-manager --set-enabled powertools || enable_powertools_repo + fi + fi + + echo >&2 " > Updating libarchive ..." + dnf ${opts} install libarchive + + dnf makecache --refresh +} + +enable_powertools_repo() { + if ! dnf repolist | grep -q powertools; then + cat > /etc/yum.repos.d/powertools.repo <<-EOF + [powertools] + name=Rocky Linux \$releasever - PowerTools + mirrorlist=https://mirrors.rockylinux.org/mirrorlist?arch=\$basearch&repo=PowerTools-\$releasever + #baseurl=http://dl.rockylinux.org/\$contentdir/\$releasever/PowerTools/\$basearch/os/ + gpgcheck=1 + enabled=1 + gpgkey=file:///etc/pki/rpm-gpg/RPM-GPG-KEY-rockyofficial +EOF + else + echo "Something went wrong!" + exit 1 + fi +} + +# shellcheck disable=SC2068 +check_flags ${@} +validate_tree_rockylinux + +packages_to_install= + +# shellcheck disable=SC2068 +for package in ${package_tree[@]}; do + if rpm -q "$package" &> /dev/null; then + echo "Package '${package}' is installed" + else + echo "Package '$package' is NOT installed" + packages_to_install="$packages_to_install $package" + fi +done + +if [[ -z $packages_to_install ]]; then + echo "All required packages are already installed. Skipping .." +else + echo "packages_to_install:" "${packages_to_install[@]}" + opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + # shellcheck disable=SC2068 + dnf install ${opts} ${packages_to_install[@]} +fi diff --git a/packaging/installer/dependencies/sabayon.sh b/packaging/installer/dependencies/sabayon.sh new file mode 100755 index 0000000..e69de29 --- /dev/null +++ b/packaging/installer/dependencies/sabayon.sh diff --git a/packaging/installer/dependencies/ubuntu.sh b/packaging/installer/dependencies/ubuntu.sh new file mode 100755 index 0000000..295dbf0 --- /dev/null +++ b/packaging/installer/dependencies/ubuntu.sh @@ -0,0 +1,101 @@ +#!/usr/bin/env bash +# Package tree used for installing netdata on distribution: +# << Ubuntu: [18.04] [20.04] [20.10] [21.04] [21.10] >> | << Linux Mint >> + +set -e + +NON_INTERACTIVE=0 +DONT_WAIT=0 + +package_tree=" + git + gcc + g++ + make + automake + cmake + autoconf + autoconf-archive + autogen + libatomic1 + libtool + pkg-config + tar + curl + gzip + zlib1g-dev + uuid-dev + libmnl-dev + libjson-c-dev + libuv1-dev + liblz4-dev + libssl-dev + libelf-dev + python3 + " +usage() { + cat << EOF +OPTIONS: +[--dont-wait] [--non-interactive] [ ] +EOF +} + +check_flags() { + while [ -n "${1}" ]; do + case "${1}" in + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift + done + + if [ "${DONT_WAIT}" -eq 0 ] && [ "${NON_INTERACTIVE}" -eq 0 ]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi +} + +# shellcheck disable=SC2068 +check_flags ${@} + +packages_to_install= + +for package in $package_tree; do + if dpkg -s "$package" &> /dev/null; then + echo "Package '${package}' is installed" + else + echo "Package '${package}' is NOT installed" + packages_to_install="$packages_to_install $package" + fi +done + +if [[ -z "$packages_to_install" ]]; then + echo "All required packages are already installed. Skipping .." +else + echo "packages_to_install:" "$packages_to_install" + opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + export DEBIAN_FRONTEND="noninteractive" + opts="${opts} -yq" + fi + echo "Running apt-get update and updating your APT caches ..." + apt-get update + # shellcheck disable=SC2086 + apt-get install ${opts} $packages_to_install +fi diff --git a/packaging/installer/functions.sh b/packaging/installer/functions.sh new file mode 100644 index 0000000..e354ac6 --- /dev/null +++ b/packaging/installer/functions.sh @@ -0,0 +1,1073 @@ +#!/bin/sh + +# SPDX-License-Identifier: GPL-3.0-or-later + +# next unused error code: L0003 + +# make sure we have a UID +[ -z "${UID}" ] && UID="$(id -u)" +# ----------------------------------------------------------------------------- + +setup_terminal() { + TPUT_RESET="" + TPUT_BLACK="" + TPUT_RED="" + TPUT_GREEN="" + TPUT_YELLOW="" + TPUT_BLUE="" + TPUT_PURPLE="" + TPUT_CYAN="" + TPUT_WHITE="" + TPUT_BGBLACK="" + TPUT_BGRED="" + TPUT_BGGREEN="" + TPUT_BGYELLOW="" + TPUT_BGBLUE="" + TPUT_BGPURPLE="" + TPUT_BGCYAN="" + TPUT_BGWHITE="" + TPUT_BOLD="" + TPUT_DIM="" + TPUT_UNDERLINED="" + TPUT_BLINK="" + TPUT_INVERTED="" + TPUT_STANDOUT="" + TPUT_BELL="" + TPUT_CLEAR="" + + # Is stderr on the terminal? If not, then fail + test -t 2 || return 1 + + if command -v tput 1> /dev/null 2>&1; then + if [ $(($(tput colors 2> /dev/null))) -ge 8 ]; then + # Enable colors + TPUT_RESET="$(tput sgr 0)" + # shellcheck disable=SC2034 + TPUT_BLACK="$(tput setaf 0)" + # shellcheck disable=SC2034 + TPUT_RED="$(tput setaf 1)" + TPUT_GREEN="$(tput setaf 2)" + # shellcheck disable=SC2034 + TPUT_YELLOW="$(tput setaf 3)" + # shellcheck disable=SC2034 + TPUT_BLUE="$(tput setaf 4)" + # shellcheck disable=SC2034 + TPUT_PURPLE="$(tput setaf 5)" + # shellcheck disable=SC2034 + TPUT_CYAN="$(tput setaf 6)" + TPUT_WHITE="$(tput setaf 7)" + # shellcheck disable=SC2034 + TPUT_BGBLACK="$(tput setab 0)" + TPUT_BGRED="$(tput setab 1)" + TPUT_BGGREEN="$(tput setab 2)" + # shellcheck disable=SC2034 + TPUT_BGYELLOW="$(tput setab 3)" + # shellcheck disable=SC2034 + TPUT_BGBLUE="$(tput setab 4)" + # shellcheck disable=SC2034 + TPUT_BGPURPLE="$(tput setab 5)" + # shellcheck disable=SC2034 + TPUT_BGCYAN="$(tput setab 6)" + # shellcheck disable=SC2034 + TPUT_BGWHITE="$(tput setab 7)" + TPUT_BOLD="$(tput bold)" + TPUT_DIM="$(tput dim)" + # shellcheck disable=SC2034 + TPUT_UNDERLINED="$(tput smul)" + # shellcheck disable=SC2034 + TPUT_BLINK="$(tput blink)" + # shellcheck disable=SC2034 + TPUT_INVERTED="$(tput rev)" + # shellcheck disable=SC2034 + TPUT_STANDOUT="$(tput smso)" + # shellcheck disable=SC2034 + TPUT_BELL="$(tput bel)" + # shellcheck disable=SC2034 + TPUT_CLEAR="$(tput clear)" + fi + fi + + return 0 +} +setup_terminal || echo > /dev/null + +progress() { + echo >&2 " --- ${TPUT_DIM}${TPUT_BOLD}${*}${TPUT_RESET} --- " +} + +get() { + url="${1}" + if command -v curl > /dev/null 2>&1; then + curl -q -o - -sSL --connect-timeout 10 --retry 3 "${url}" + elif command -v wget > /dev/null 2>&1; then + wget -T 15 -O - "${url}" + else + fatal "I need curl or wget to proceed, but neither is available on this system." "L0002" + fi +} + +download_file() { + url="${1}" + dest="${2}" + name="${3}" + opt="${4}" + + if command -v curl > /dev/null 2>&1; then + run curl -q -sSL --connect-timeout 10 --retry 3 --output "${dest}" "${url}" + elif command -v wget > /dev/null 2>&1; then + run wget -T 15 -O "${dest}" "${url}" + else + echo >&2 + echo >&2 "Downloading ${name} from '${url}' failed because of missing mandatory packages." + if [ -n "$opt" ]; then + echo >&2 "Either add packages or disable it by issuing '--disable-${opt}' in the installer" + fi + echo >&2 + + run_failed "I need curl or wget to proceed, but neither is available on this system." + fi +} + +# ----------------------------------------------------------------------------- +# external component handling + +fetch_and_verify() { + component="${1}" + url="${2}" + base_name="${3}" + tmp="${4}" + override="${5}" + + if [ -z "${override}" ]; then + download_file "${url}" "${tmp}/${base_name}" "${component}" + else + progress "Using provided ${component} archive ${override}" + run cp "${override}" "${tmp}/${base_name}" + fi + + if [ ! -f "${tmp}/${base_name}" ] || [ ! -s "${tmp}/${base_name}" ]; then + run_failed "Unable to find usable archive for ${component}" + return 1 + fi + + grep "${base_name}\$" "${INSTALLER_DIR}/packaging/${component}.checksums" > "${tmp}/sha256sums.txt" 2> /dev/null + + # Checksum validation + if ! (cd "${tmp}" && safe_sha256sum -c "sha256sums.txt"); then + run_failed "${component} files checksum validation failed." + return 1 + fi +} + +# ----------------------------------------------------------------------------- + +netdata_banner() { + l1=" ^" \ + l2=" |.-. .-. .-. .-. .-. .-. .-. .-. .-. .-. .-. .-. .-" \ + l4=" +----+-----+-----+-----+-----+-----+-----+-----+-----+-----+-----+-----+--->" \ + space=" " + l3f=" | '-' '-' '-' '-' '-'" + l3e=" '-' '-' '-' '-' '-' " + + netdata="netdata" + chartcolor="${TPUT_DIM}" + + echo >&2 + echo >&2 "${chartcolor}${l1}${TPUT_RESET}" + echo >&2 "${chartcolor}${l2%-. .-. .-. .-. .-. .-. .-. .-}${space}${TPUT_RESET}${TPUT_BOLD}${TPUT_GREEN}${netdata}${TPUT_RESET}${chartcolor}${l2# |.-. .-. .-. .-. .-. .-. .-. }${TPUT_RESET}" + echo >&2 "${chartcolor}${l3f}${l3e}${TPUT_RESET}" + echo >&2 "${chartcolor}${l4}${TPUT_RESET}" + echo >&2 +} + +# ----------------------------------------------------------------------------- +# portable service command + +service_cmd="$(command -v service 2> /dev/null || true)" +rcservice_cmd="$(command -v rc-service 2> /dev/null || true)" +systemctl_cmd="$(command -v systemctl 2> /dev/null || true)" +service() { + + cmd="${1}" + action="${2}" + + if [ -n "${systemctl_cmd}" ]; then + run "${systemctl_cmd}" "${action}" "${cmd}" + return $? + elif [ -n "${service_cmd}" ]; then + run "${service_cmd}" "${cmd}" "${action}" + return $? + elif [ -n "${rcservice_cmd}" ]; then + run "${rcservice_cmd}" "${cmd}" "${action}" + return $? + fi + return 1 +} + +# ----------------------------------------------------------------------------- +# portable pidof + +safe_pidof() { + pidof_cmd="$(command -v pidof 2> /dev/null)" + if [ -n "${pidof_cmd}" ]; then + ${pidof_cmd} "${@}" + return $? + else + ps -acxo pid,comm | + sed "s/^ *//g" | + grep netdata | + cut -d ' ' -f 1 + return $? + fi +} + +# ----------------------------------------------------------------------------- +find_processors() { + # Most UNIX systems have `nproc` as part of their userland (including Linux and BSD) + if command -v nproc > /dev/null; then + nproc && return + fi + + # macOS has no nproc but it may have gnproc installed from Homebrew or from Macports. + if command -v gnproc > /dev/null; then + gnproc && return + fi + + if [ -f "/proc/cpuinfo" ]; then + # linux + cpus=$(grep -c ^processor /proc/cpuinfo) + else + # freebsd + cpus=$(sysctl hw.ncpu 2> /dev/null | grep ^hw.ncpu | cut -d ' ' -f 2) + fi + if [ -z "${cpus}" ] || [ $((cpus)) -lt 1 ]; then + echo 1 + else + echo "${cpus}" + fi +} + +# ----------------------------------------------------------------------------- +exit_reason() { + if [ -n "${NETDATA_SAVE_WARNINGS}" ]; then + EXIT_REASON="${1}" + EXIT_CODE="${2}" + if [ -n "${NETDATA_PROPAGATE_WARNINGS}" ]; then + if [ -n "${NETDATA_SCRIPT_STATUS_PATH}" ]; then + { + echo "EXIT_REASON=\"${EXIT_REASON}\"" + echo "EXIT_CODE=\"${EXIT_CODE}\"" + echo "NETDATA_WARNINGS=\"${NETDATA_WARNINGS}${SAVED_WARNINGS}\"" + } >> "${NETDATA_SCRIPT_STATUS_PATH}" + else + export EXIT_REASON + export EXIT_CODE + export NETDATA_WARNINGS="${NETDATA_WARNINGS}${SAVED_WARNINGS}" + fi + fi + fi +} + +fatal() { + printf >&2 "%s ABORTED %s %s \n\n" "${TPUT_BGRED}${TPUT_WHITE}${TPUT_BOLD}" "${TPUT_RESET}" "${1}" + if [ -n "${NETDATA_SAVE_WARNINGS}" ]; then + SAVED_WARNINGS="${SAVED_WARNINGS}\n - ${1}" + fi + exit_reason "${1}" "${2}" + exit 1 +} + +warning() { + printf >&2 "%s WARNING %s %s\n\n" "${TPUT_BGYELLOW}${TPUT_BLACK}${TPUT_BOLD}" "${TPUT_RESET}" "${1}" + if [ -n "${NETDATA_SAVE_WARNINGS}" ]; then + SAVED_WARNINGS="${SAVED_WARNINGS}\n - ${1}" + fi +} + +run_ok() { + printf >&2 "%s OK %s %s\n\n" "${TPUT_BGGREEN}${TPUT_WHITE}${TPUT_BOLD}" "${TPUT_RESET}" "${1:-''}" +} + +run_failed() { + printf >&2 "%s FAILED %s %s\n\n" "${TPUT_BGRED}${TPUT_WHITE}${TPUT_BOLD}" "${TPUT_RESET}" "${1:-''}" + if [ -n "${NETDATA_SAVE_WARNINGS}" ] && [ -n "${1:-''}" ]; then + SAVED_WARNINGS="${SAVED_WARNINGS}\n - ${1}" + fi +} + +ESCAPED_PRINT_METHOD= +if printf "%s " test > /dev/null 2>&1; then + ESCAPED_PRINT_METHOD="printfq" +fi +escaped_print() { + if [ "${ESCAPED_PRINT_METHOD}" = "printfq" ]; then + printf "%s " "${@}" + else + printf "%s" "${*}" + fi + return 0 +} + +run_logfile="/dev/null" +run() { + local_user="${USER--}" + local_dir="${PWD}" + if [ "${UID}" = "0" ]; then + info="[root ${local_dir}]# " + info_console="[${TPUT_DIM}${local_dir}${TPUT_RESET}]# " + else + info="[${local_user} ${local_dir}]$ " + info_console="[${TPUT_DIM}${local_dir}${TPUT_RESET}]$ " + fi + + { + printf "%s" "${info}" + escaped_print "${@}" + printf "%s" " ... " + } >> "${run_logfile}" + + printf >&2 "%s" "${info_console}${TPUT_BOLD}${TPUT_YELLOW}" + escaped_print >&2 "${@}" + printf >&2 "%s\n" "${TPUT_RESET}" + + "${@}" + + ret=$? + if [ ${ret} -ne 0 ]; then + run_failed + printf >> "${run_logfile}" "FAILED with exit code %s\n" "${ret}" + if [ -n "${NETDATA_SAVE_WARNINGS}" ]; then + SAVED_WARNINGS="${SAVED_WARNINGS}\n - Command '${*}' failed with exit code ${ret}." + fi + else + run_ok + printf >> "${run_logfile}" "OK\n" + fi + + return ${ret} +} + +iscontainer() { + # man systemd-detect-virt + cmd=$(command -v systemd-detect-virt 2> /dev/null) + if [ -n "${cmd}" ] && [ -x "${cmd}" ]; then + "${cmd}" --container > /dev/null 2>&1 && return 0 + fi + + # /proc/1/sched exposes the host's pid of our init ! + # http://stackoverflow.com/a/37016302 + pid=$(head -n 1 /proc/1/sched 2> /dev/null | { + # shellcheck disable=SC2034 + IFS='(),#:' read -r name pid th threads + echo "$pid" + }) + if [ -n "${pid}" ]; then + pid=$((pid + 0)) + [ ${pid} -gt 1 ] && return 0 + fi + + # lxc sets environment variable 'container' + # shellcheck disable=SC2154 + [ -n "${container}" ] && return 0 + + # docker creates /.dockerenv + # http://stackoverflow.com/a/25518345 + [ -f "/.dockerenv" ] && return 0 + + # ubuntu and debian supply /bin/running-in-container + # https://www.apt-browse.org/browse/ubuntu/trusty/main/i386/upstart/1.12.1-0ubuntu4/file/bin/running-in-container + if [ -x "/bin/running-in-container" ]; then + "/bin/running-in-container" > /dev/null 2>&1 && return 0 + fi + + return 1 +} + +get_os_key() { + if [ -f /etc/os-release ]; then + # shellcheck disable=SC1091 + . /etc/os-release || return 1 + echo "${ID}-${VERSION_ID}" + + elif [ -f /etc/redhat-release ]; then + cat /etc/redhat-release + else + echo "unknown" + fi +} + +issystemd() { + pids='' + p='' + myns='' + ns='' + systemctl='' + + # if the directory /lib/systemd/system OR /usr/lib/systemd/system (SLES 12.x) does not exit, it is not systemd + if [ ! -d /lib/systemd/system ] && [ ! -d /usr/lib/systemd/system ]; then + return 1 + fi + + # if there is no systemctl command, it is not systemd + systemctl=$(command -v systemctl 2> /dev/null) + if [ -z "${systemctl}" ] || [ ! -x "${systemctl}" ]; then + return 1 + fi + + # if pid 1 is systemd, it is systemd + [ "$(basename "$(readlink /proc/1/exe)" 2> /dev/null)" = "systemd" ] && return 0 + + # if systemd is not running, it is not systemd + pids=$(safe_pidof systemd 2> /dev/null) + [ -z "${pids}" ] && return 1 + + # check if the running systemd processes are not in our namespace + myns="$(readlink /proc/self/ns/pid 2> /dev/null)" + for p in ${pids}; do + ns="$(readlink "/proc/${p}/ns/pid" 2> /dev/null)" + + # if pid of systemd is in our namespace, it is systemd + [ -n "${myns}" ] && [ "${myns}" = "${ns}" ] && return 0 + done + + # else, it is not systemd + return 1 +} + +get_systemd_service_dir() { + if [ -w "/lib/systemd/system" ]; then + echo "/lib/systemd/system" + elif [ -w "/usr/lib/systemd/system" ]; then + echo "/usr/lib/systemd/system" + elif [ -w "/etc/systemd/system" ]; then + echo "/etc/systemd/system" + fi +} + +install_non_systemd_init() { + [ "${UID}" != 0 ] && return 1 + key="$(get_os_key)" + + if [ -d /etc/init.d ] && [ ! -f /etc/init.d/netdata ]; then + if expr "${key}" : "^(gentoo|alpine).*"; then + echo >&2 "Installing OpenRC init file..." + run cp system/netdata-openrc /etc/init.d/netdata && + run chmod 755 /etc/init.d/netdata && + run rc-update add netdata default && + return 0 + + elif expr "${key}" : "^devuan*" || [ "${key}" = "debian-7" ] || [ "${key}" = "ubuntu-12.04" ] || [ "${key}" = "ubuntu-14.04" ]; then + echo >&2 "Installing LSB init file..." + run cp system/netdata-lsb /etc/init.d/netdata && + run chmod 755 /etc/init.d/netdata && + run update-rc.d netdata defaults && + run update-rc.d netdata enable && + return 0 + elif expr "${key}" : "^(amzn-201[5678]|ol|CentOS release 6|Red Hat Enterprise Linux Server release 6|Scientific Linux CERN SLC release 6|CloudLinux Server release 6).*"; then + echo >&2 "Installing init.d file..." + run cp system/netdata-init-d /etc/init.d/netdata && + run chmod 755 /etc/init.d/netdata && + run chkconfig netdata on && + return 0 + else + warning "Could not determine what type of init script to install on this system." + return 1 + fi + elif [ -f /etc/init.d/netdata ]; then + echo >&2 "file '/etc/init.d/netdata' already exists." + return 0 + else + warning "Could not determine what type of init script to install on this system." + fi + + return 1 +} + +run_install_service_script() { + if [ -z "${tmpdir}" ]; then + tmpdir="${TMPDIR:-/tmp}" + fi + + # shellcheck disable=SC2154 + save_path="${tmpdir}/netdata-service-cmds" + # shellcheck disable=SC2068 + "${NETDATA_PREFIX}/usr/libexec/netdata/install-service.sh" --save-cmds "${save_path}" ${@} + + case $? in + 0) + if [ -r "${save_path}" ]; then + # shellcheck disable=SC1090 + . "${save_path}" + fi + + if [ -z "${NETDATA_INSTALLER_START_CMD}" ]; then + if [ -n "${NETDATA_START_CMD}" ]; then + NETDATA_INSTALLER_START_CMD="${NETDATA_START_CMD}" + else + NETDATA_INSTALLER_START_CMD="netdata" + fi + fi + ;; + 1) + if [ -z "${NETDATA_SERVICE_WARNED_1}" ]; then + warning "Intenral error encountered while attempting to install or manage Netdata as a system service. This is probably a bug." + NETDATA_SERVICE_WARNED_1=1 + fi + ;; + 2) + if [ -z "${NETDATA_SERVICE_WARNED_2}" ]; then + warning "Failed to detect system service manager type. Cannot cleanly install or manage Netdata as a system service. If you are running this script in a container, this is expected and can safely be ignored." + NETDATA_SERVICE_WARNED_2=1 + fi + ;; + 3) + if [ -z "${NETDATA_SERVICE_WARNED_3}" ]; then + warning "Detected an unsupported system service manager. Manual setup will be required to manage Netdata as a system service." + NETDATA_SERVICE_WARNED_3=1 + fi + ;; + 4) + if [ -z "${NETDATA_SERVICE_WARNED_4}" ]; then + warning "Detected a supported system service manager, but failed to install Netdata as a system service. Usually this is a result of incorrect permissions. Manually running ${NETDATA_PREFIX}/usr/libexec/netdata/install-service.sh may provide more information about the exact issue." + NETDATA_SERVICE_WARNED_4=1 + fi + ;; + 5) + if [ -z "${NETDATA_SERVICE_WARNED_5}" ]; then + warning "We do not support managing Netdata as a system service on this platform. Manual setup will be required." + NETDATA_SERVICE_WARNED_5=1 + fi + ;; + esac +} + +install_netdata_service() { + if [ "${UID}" -eq 0 ]; then + if [ -x "${NETDATA_PREFIX}/usr/libexec/netdata/install-service.sh" ]; then + run_install_service_script && return 0 + else + # This is used by netdata-installer.sh + # shellcheck disable=SC2034 + NETDATA_STOP_CMD="netdatacli shutdown-agent" + + NETDATA_START_CMD="netdata" + NETDATA_INSTALLER_START_CMD="" + + uname="$(uname 2> /dev/null)" + + if [ "${uname}" = "Darwin" ]; then + if [ -f "/Library/LaunchDaemons/com.github.netdata.plist" ]; then + echo >&2 "file '/Library/LaunchDaemons/com.github.netdata.plist' already exists." + return 0 + else + echo >&2 "Installing MacOS X plist file..." + # This is used by netdata-installer.sh + # shellcheck disable=SC2034 + run cp system/netdata.plist /Library/LaunchDaemons/com.github.netdata.plist && + run launchctl load /Library/LaunchDaemons/com.github.netdata.plist && + NETDATA_START_CMD="launchctl start com.github.netdata" && + NETDATA_STOP_CMD="launchctl stop com.github.netdata" + return 0 + fi + + elif [ "${uname}" = "FreeBSD" ]; then + # This is used by netdata-installer.sh + # shellcheck disable=SC2034 + run cp system/netdata-freebsd /etc/rc.d/netdata && NETDATA_START_CMD="service netdata start" && + NETDATA_STOP_CMD="service netdata stop" && + NETDATA_INSTALLER_START_CMD="service netdata onestart" && + myret=$? + + echo >&2 "Note: To explicitly enable netdata automatic start, set 'netdata_enable' to 'YES' in /etc/rc.conf" + echo >&2 "" + + return ${myret} + + elif issystemd; then + # systemd is running on this system + NETDATA_START_CMD="systemctl start netdata" + # This is used by netdata-installer.sh + # shellcheck disable=SC2034 + NETDATA_STOP_CMD="systemctl stop netdata" + NETDATA_INSTALLER_START_CMD="${NETDATA_START_CMD}" + + SYSTEMD_DIRECTORY="$(get_systemd_service_dir)" + + if [ "${SYSTEMD_DIRECTORY}x" != "x" ]; then + ENABLE_NETDATA_IF_PREVIOUSLY_ENABLED="run systemctl enable netdata" + IS_NETDATA_ENABLED="$(systemctl is-enabled netdata 2> /dev/null || echo "Netdata not there")" + if [ "${IS_NETDATA_ENABLED}" = "disabled" ]; then + echo >&2 "Netdata was there and disabled, make sure we don't re-enable it ourselves" + ENABLE_NETDATA_IF_PREVIOUSLY_ENABLED="true" + fi + + echo >&2 "Installing systemd service..." + run cp system/netdata.service "${SYSTEMD_DIRECTORY}/netdata.service" && + run systemctl daemon-reload && + ${ENABLE_NETDATA_IF_PREVIOUSLY_ENABLED} && + return 0 + else + warning "Could not find a systemd service directory, unable to install Netdata systemd service." + fi + else + install_non_systemd_init + ret=$? + + if [ ${ret} -eq 0 ]; then + if [ -n "${service_cmd}" ]; then + NETDATA_START_CMD="service netdata start" + # This is used by netdata-installer.sh + # shellcheck disable=SC2034 + NETDATA_STOP_CMD="service netdata stop" + elif [ -n "${rcservice_cmd}" ]; then + NETDATA_START_CMD="rc-service netdata start" + # This is used by netdata-installer.sh + # shellcheck disable=SC2034 + NETDATA_STOP_CMD="rc-service netdata stop" + fi + NETDATA_INSTALLER_START_CMD="${NETDATA_START_CMD}" + fi + + return ${ret} + fi + fi + fi + + return 1 +} + +# ----------------------------------------------------------------------------- +# stop netdata + +pidisnetdata() { + if [ -d /proc/self ]; then + if [ -z "$1" ] || [ ! -f "/proc/$1/stat" ]; then + return 1 + fi + [ "$(cut -d '(' -f 2 "/proc/$1/stat" | cut -d ')' -f 1)" = "netdata" ] && return 0 + return 1 + fi + return 0 +} + +stop_netdata_on_pid() { + pid="${1}" + ret=0 + count=0 + + pidisnetdata "${pid}" || return 0 + + printf >&2 "Stopping netdata on pid %s ..." "${pid}" + while [ -n "${pid}" ] && [ ${ret} -eq 0 ]; do + if [ ${count} -gt 24 ]; then + warning "Cannot stop netdata agent with PID ${pid}." + return 1 + fi + + count=$((count + 1)) + + pidisnetdata "${pid}" || ret=1 + if [ ${ret} -eq 1 ]; then + break + fi + + if [ ${count} -lt 12 ]; then + run kill "${pid}" 2> /dev/null + ret=$? + else + run kill -9 "${pid}" 2> /dev/null + ret=$? + fi + + test ${ret} -eq 0 && printf >&2 "." && sleep 5 + + done + + echo >&2 + if [ ${ret} -eq 0 ]; then + warning "Failed to stop netdata agent process with PID ${pid}." + return 1 + fi + + echo >&2 "netdata on pid ${pid} stopped." + return 0 +} + +netdata_pids() { + myns="$(readlink /proc/self/ns/pid 2> /dev/null)" + + for p in \ + $(cat /var/run/netdata.pid 2> /dev/null) \ + $(cat /var/run/netdata/netdata.pid 2> /dev/null) \ + $(safe_pidof netdata 2> /dev/null); do + ns="$(readlink "/proc/${p}/ns/pid" 2> /dev/null)" + + if [ -z "${myns}" ] || [ -z "${ns}" ] || [ "${myns}" = "${ns}" ]; then + pidisnetdata "${p}" && echo "${p}" + fi + done +} + +stop_all_netdata() { + stop_success=0 + + if [ -x "${NETDATA_PREFIX}/usr/libexec/netdata/install-service.sh" ]; then + run_install_service_script --cmds-only + fi + + if [ "${UID}" -eq 0 ]; then + + uname="$(uname 2>/dev/null)" + + # Any of these may fail, but we need to not bail if they do. + if [ -n "${NETDATA_STOP_CMD}" ]; then + if ${NETDATA_STOP_CMD}; then + stop_success=1 + sleep 5 + fi + elif issystemd; then + if systemctl stop netdata; then + stop_success=1 + sleep 5 + fi + elif [ "${uname}" = "Darwin" ]; then + if launchctl stop netdata; then + stop_success=1 + sleep 5 + fi + elif [ "${uname}" = "FreeBSD" ]; then + if /etc/rc.d/netdata stop; then + stop_success=1 + sleep 5 + fi + else + if service netdata stop; then + stop_success=1 + sleep 5 + fi + fi + fi + + if [ "$stop_success" = "0" ]; then + if [ -n "$(netdata_pids)" ] && [ -n "$(command -v netdatacli)" ]; then + netdatacli shutdown-agent + sleep 20 + fi + + for p in $(netdata_pids); do + # shellcheck disable=SC2086 + stop_netdata_on_pid ${p} + done + fi +} + +# ----------------------------------------------------------------------------- +# restart netdata + +restart_netdata() { + netdata="${1}" + shift + + started=0 + + progress "Restarting netdata instance" + + if [ -x "${NETDATA_PREFIX}/usr/libexec/netdata/install-service.sh" ]; then + run_install_service_script --cmds-only + fi + + if [ -z "${NETDATA_INSTALLER_START_CMD}" ]; then + if [ -n "${NETDATA_START_CMD}" ]; then + NETDATA_INSTALLER_START_CMD="${NETDATA_START_CMD}" + else + NETDATA_INSTALLER_START_CMD="${netdata}" + fi + fi + + if [ "${UID}" -eq 0 ]; then + echo >&2 + echo >&2 "Stopping all netdata threads" + run stop_all_netdata + + echo >&2 "Starting netdata using command '${NETDATA_INSTALLER_START_CMD}'" + # shellcheck disable=SC2086 + run ${NETDATA_INSTALLER_START_CMD} && started=1 + + if [ ${started} -eq 1 ] && sleep 5 && [ -z "$(netdata_pids)" ]; then + echo >&2 "Ooops! it seems netdata is not started." + started=0 + fi + + if [ ${started} -eq 0 ]; then + echo >&2 "Attempting another netdata start using command '${NETDATA_INSTALLER_START_CMD}'" + # shellcheck disable=SC2086 + run ${NETDATA_INSTALLER_START_CMD} && started=1 + fi + + if [ ${started} -eq 1 ] && sleep 5 && [ -z "$(netdata_pids)" ]; then + echo >&2 "Hm... it seems netdata is still not started." + started=0 + fi + fi + + + if [ ${started} -eq 0 ]; then + # still not started... another forced attempt, just run the binary + warning "Netdata service still not started, attempting another forced restart by running '${netdata} ${*}'" + run stop_all_netdata + run "${netdata}" "${@}" + return $? + fi + + return 0 +} + +# ----------------------------------------------------------------------------- +# install netdata logrotate + +install_netdata_logrotate() { + if [ "${UID}" -eq 0 ]; then + if [ -d /etc/logrotate.d ]; then + if [ ! -f /etc/logrotate.d/netdata ]; then + run cp system/netdata.logrotate /etc/logrotate.d/netdata + fi + + if [ -f /etc/logrotate.d/netdata ]; then + run chmod 644 /etc/logrotate.d/netdata + fi + + return 0 + fi + fi + + return 1 +} + +# ----------------------------------------------------------------------------- +# create netdata.conf + +create_netdata_conf() { + path="${1}" + url="${2}" + + if [ -s "${path}" ]; then + return 0 + fi + + if [ -n "$url" ]; then + echo >&2 "Downloading default configuration from netdata..." + sleep 5 + + # remove a possibly obsolete configuration file + [ -f "${path}.new" ] && rm "${path}.new" + + # disable a proxy to get data from the local netdata + export http_proxy= + export https_proxy= + + if command -v curl 1> /dev/null 2>&1; then + run curl -sSL --connect-timeout 10 --retry 3 "${url}" > "${path}.new" + elif command -v wget 1> /dev/null 2>&1; then + run wget -T 15 -O - "${url}" > "${path}.new" + fi + + if [ -s "${path}.new" ]; then + run mv "${path}.new" "${path}" + run_ok "New configuration saved for you to edit at ${path}" + else + [ -f "${path}.new" ] && rm "${path}.new" + run_failed "Cannot download configuration from netdata daemon using url '${url}'" + url='' + fi + fi + + if [ -z "$url" ]; then + echo "# netdata can generate its own config which is available at 'http://<netdata_ip>/netdata.conf'" > "${path}" + echo "# You can download it with command like: 'wget -O ${path} http://localhost:19999/netdata.conf'" >> "${path}" + fi + +} + +portable_add_user() { + username="${1}" + homedir="${2}" + + [ -z "${homedir}" ] && homedir="/tmp" + + # Check if user exists + if cut -d ':' -f 1 < /etc/passwd | grep "^${username}$" 1> /dev/null 2>&1; then + echo >&2 "User '${username}' already exists." + return 0 + fi + + echo >&2 "Adding ${username} user account with home ${homedir} ..." + + nologin="$(command -v nologin || echo '/bin/false')" + + # Linux + if command -v useradd 1> /dev/null 2>&1; then + run useradd -r -g "${username}" -c "${username}" -s "${nologin}" --no-create-home -d "${homedir}" "${username}" && return 0 + fi + + # FreeBSD + if command -v pw 1> /dev/null 2>&1; then + run pw useradd "${username}" -d "${homedir}" -g "${username}" -s "${nologin}" && return 0 + fi + + # BusyBox + if command -v adduser 1> /dev/null 2>&1; then + run adduser -h "${homedir}" -s "${nologin}" -D -G "${username}" "${username}" && return 0 + fi + + # mac OS + if command -v sysadminctl 1> /dev/null 2>&1; then + run sysadminctl -addUser "${username}" && return 0 + fi + + warning "Failed to add ${username} user account!" + + return 1 +} + +portable_add_group() { + groupname="${1}" + + # Check if group exist + if cut -d ':' -f 1 < /etc/group | grep "^${groupname}$" 1> /dev/null 2>&1; then + echo >&2 "Group '${groupname}' already exists." + return 0 + fi + + echo >&2 "Adding ${groupname} user group ..." + + # Linux + if command -v groupadd 1> /dev/null 2>&1; then + run groupadd -r "${groupname}" && return 0 + fi + + # FreeBSD + if command -v pw 1> /dev/null 2>&1; then + run pw groupadd "${groupname}" && return 0 + fi + + # BusyBox + if command -v addgroup 1> /dev/null 2>&1; then + run addgroup "${groupname}" && return 0 + fi + + # mac OS + if command -v dseditgroup 1> /dev/null 2>&1; then + dseditgroup -o create "${groupname}" && return 0 + fi + + warning >&2 "Failed to add ${groupname} user group !" + return 1 +} + +portable_add_user_to_group() { + groupname="${1}" + username="${2}" + + # Check if group exist + if ! cut -d ':' -f 1 < /etc/group | grep "^${groupname}$" > /dev/null 2>&1; then + echo >&2 "Group '${groupname}' does not exist." + # Don’t treat this as a failure, if the group does not exist we should not be trying to add the user to it. + return 0 + fi + + # Check if user is in group + if expr ",$(grep "^${groupname}:" < /etc/group | cut -d ':' -f 4)," : ",""${username}"","; then + # username is already there + echo >&2 "User '${username}' is already in group '${groupname}'." + return 0 + else + # username is not in group + echo >&2 "Adding ${username} user to the ${groupname} group ..." + + # Linux + if command -v usermod 1> /dev/null 2>&1; then + run usermod -a -G "${groupname}" "${username}" && return 0 + fi + + # FreeBSD + if command -v pw 1> /dev/null 2>&1; then + run pw groupmod "${groupname}" -m "${username}" && return 0 + fi + + # BusyBox + if command -v addgroup 1> /dev/null 2>&1; then + run addgroup "${username}" "${groupname}" && return 0 + fi + + # mac OS + if command -v dseditgroup 1> /dev/null 2>&1; then + dseditgroup -u "${username}" "${groupname}" && return 0 + fi + + warning >&2 "Failed to add user ${username} to group ${groupname}!" + return 1 + fi +} + +safe_sha256sum() { + # Within the context of the installer, we only use -c option that is common between the two commands + # We will have to reconsider if we start non-common options + if command -v sha256sum > /dev/null 2>&1; then + sha256sum "$@" + elif command -v shasum > /dev/null 2>&1; then + shasum -a 256 "$@" + else + fatal "I could not find a suitable checksum binary to use" "L0001" + fi +} + +_get_scheduler_type() { + if _get_intervaldir > /dev/null ; then + echo 'interval' + elif issystemd ; then + echo 'systemd' + elif [ -d /etc/cron.d ] ; then + echo 'crontab' + else + echo 'none' + fi +} + +_get_intervaldir() { + if [ -d /etc/cron.daily ]; then + echo /etc/cron.daily + elif [ -d /etc/periodic/daily ]; then + echo /etc/periodic/daily + else + return 1 + fi + + return 0 +} + +install_netdata_updater() { + if [ "${INSTALLER_DIR}" ] && [ -f "${INSTALLER_DIR}/packaging/installer/netdata-updater.sh" ]; then + cat "${INSTALLER_DIR}/packaging/installer/netdata-updater.sh" > "${NETDATA_PREFIX}/usr/libexec/netdata/netdata-updater.sh" || return 1 + fi + + if [ "${NETDATA_SOURCE_DIR}" ] && [ -f "${NETDATA_SOURCE_DIR}/packaging/installer/netdata-updater.sh" ]; then + cat "${NETDATA_SOURCE_DIR}/packaging/installer/netdata-updater.sh" > "${NETDATA_PREFIX}/usr/libexec/netdata/netdata-updater.sh" || return 1 + fi + + if issystemd && [ -n "$(get_systemd_service_dir)" ]; then + cat "${NETDATA_SOURCE_DIR}/system/netdata-updater.timer" > "$(get_systemd_service_dir)/netdata-updater.timer" + cat "${NETDATA_SOURCE_DIR}/system/netdata-updater.service" > "$(get_systemd_service_dir)/netdata-updater.service" + fi + + sed -i -e "s|THIS_SHOULD_BE_REPLACED_BY_INSTALLER_SCRIPT|${NETDATA_USER_CONFIG_DIR}/.environment|" "${NETDATA_PREFIX}/usr/libexec/netdata/netdata-updater.sh" || return 1 + + chmod 0755 "${NETDATA_PREFIX}/usr/libexec/netdata/netdata-updater.sh" + echo >&2 "Update script is located at ${TPUT_GREEN}${TPUT_BOLD}${NETDATA_PREFIX}/usr/libexec/netdata/netdata-updater.sh${TPUT_RESET}" + echo >&2 + + return 0 +} + +set_netdata_updater_channel() { + sed -i -e "s/^RELEASE_CHANNEL=.*/RELEASE_CHANNEL=\"${RELEASE_CHANNEL}\"/" "${NETDATA_USER_CONFIG_DIR}/.environment" +} diff --git a/packaging/installer/install-required-packages.sh b/packaging/installer/install-required-packages.sh new file mode 100755 index 0000000..6547dd8 --- /dev/null +++ b/packaging/installer/install-required-packages.sh @@ -0,0 +1,2073 @@ +#!/usr/bin/env bash +# shellcheck disable=SC2034 +# We use lots of computed variable names in here, so we need to disable shellcheck 2034 + +export PATH="${PATH}:/bin:/sbin:/usr/bin:/usr/sbin:/usr/local/bin:/usr/local/sbin" +export LC_ALL=C + +# Be nice on production environments +renice 19 $$ > /dev/null 2> /dev/null + +ME="${0}" + +if [ "${BASH_VERSINFO[0]}" -lt "4" ]; then + echo >&2 "Sorry! This script needs BASH version 4+, but you have BASH version ${BASH_VERSION}" + exit 1 +fi + +# These options control which packages we are going to install +# They can be pre-set, but also can be controlled with command line options +PACKAGES_NETDATA=${PACKAGES_NETDATA-1} +PACKAGES_NETDATA_PYTHON=${PACKAGES_NETDATA_PYTHON-0} +PACKAGES_NETDATA_PYTHON3=${PACKAGES_NETDATA_PYTHON3-1} +PACKAGES_NETDATA_PYTHON_MONGO=${PACKAGES_NETDATA_PYTHON_MONGO-0} +PACKAGES_DEBUG=${PACKAGES_DEBUG-0} +PACKAGES_IPRANGE=${PACKAGES_IPRANGE-0} +PACKAGES_FIREHOL=${PACKAGES_FIREHOL-0} +PACKAGES_FIREQOS=${PACKAGES_FIREQOS-0} +PACKAGES_UPDATE_IPSETS=${PACKAGES_UPDATE_IPSETS-0} +PACKAGES_NETDATA_DEMO_SITE=${PACKAGES_NETDATA_DEMO_SITE-0} +PACKAGES_NETDATA_SENSORS=${PACKAGES_NETDATA_SENSORS-0} +PACKAGES_NETDATA_DATABASE=${PACKAGES_NETDATA_DATABASE-1} +PACKAGES_NETDATA_EBPF=${PACKAGES_NETDATA_EBPF-1} + +# needed commands +lsb_release=$(command -v lsb_release 2> /dev/null) + +# Check which package managers are available +apk=$(command -v apk 2> /dev/null) +apt_get=$(command -v apt-get 2> /dev/null) +brew=$(command -v brew 2> /dev/null) +pkg=$(command -v pkg 2> /dev/null) +dnf=$(command -v dnf 2> /dev/null) +emerge=$(command -v emerge 2> /dev/null) +equo=$(command -v equo 2> /dev/null) +pacman=$(command -v pacman 2> /dev/null) +swupd=$(command -v swupd 2> /dev/null) +yum=$(command -v yum 2> /dev/null) +zypper=$(command -v zypper 2> /dev/null) + +distribution= +release= +version= +codename= +package_installer= +tree= +detection= +NAME= +ID= +ID_LIKE= +VERSION= +VERSION_ID= + +usage() { + cat << EOF +OPTIONS: + +${ME} [--dont-wait] [--non-interactive] \\ + [distribution DD [version VV] [codename CN]] [installer IN] [packages] + +Supported distributions (DD): + + - arch (all Arch Linux derivatives) + - centos (all CentOS derivatives) + - gentoo (all Gentoo Linux derivatives) + - sabayon (all Sabayon Linux derivatives) + - debian, ubuntu (all Debian and Ubuntu derivatives) + - redhat, fedora (all Red Hat and Fedora derivatives) + - suse, opensuse (all SUSE and openSUSE derivatives) + - clearlinux (all Clear Linux derivatives) + - macos (Apple's macOS) + +Supported installers (IN): + + - apt-get all Debian / Ubuntu Linux derivatives + - dnf newer Red Hat / Fedora Linux + - emerge all Gentoo Linux derivatives + - equo all Sabayon Linux derivatives + - pacman all Arch Linux derivatives + - yum all Red Hat / Fedora / CentOS Linux derivatives + - zypper all SUSE Linux derivatives + - apk all Alpine derivatives + - swupd all Clear Linux derivatives + - brew macOS Homebrew + - pkg FreeBSD Ports + +Supported packages (you can append many of them): + + - netdata-all all packages required to install netdata + including python, sensors, etc + + - netdata minimum packages required to install netdata + (includes python) + + - python install python + + - python3 install python3 + + - python-pymongo install python-pymongo (or python3-pymongo for python3) + + - sensors install lm_sensors for monitoring h/w sensors + + - firehol-all packages required for FireHOL, FireQOS, update-ipsets + - firehol packages required for FireHOL + - fireqos packages required for FireQOS + - update-ipsets packages required for update-ipsets + + - demo packages required for running a netdata demo site + (includes nginx and various debugging tools) + + +If you don't supply the --dont-wait option, the program +will ask you before touching your system. + +EOF +} + +release2lsb_release() { + # loads the given /etc/x-release file + # this file is normally a single line containing something like + # + # X Linux release 1.2.3 (release-name) + # + # It attempts to parse it + # If it succeeds, it returns 0 + # otherwise it returns 1 + + local file="${1}" x DISTRIB_ID="" DISTRIB_RELEASE="" DISTRIB_CODENAME="" + echo >&2 "Loading ${file} ..." + + x="$(grep -v "^$" "${file}" | head -n 1)" + + if [[ "${x}" =~ ^.*[[:space:]]+Linux[[:space:]]+release[[:space:]]+.*[[:space:]]+(.*)[[:space:]]*$ ]]; then + eval "$(echo "${x}" | sed "s|^\(.*\)[[:space:]]\+Linux[[:space:]]\+release[[:space:]]\+\(.*\)[[:space:]]\+(\(.*\))[[:space:]]*$|DISTRIB_ID=\"\1\"\nDISTRIB_RELEASE=\"\2\"\nDISTRIB_CODENAME=\"\3\"|g" | grep "^DISTRIB")" + elif [[ "${x}" =~ ^.*[[:space:]]+Linux[[:space:]]+release[[:space:]]+.*[[:space:]]+$ ]]; then + eval "$(echo "${x}" | sed "s|^\(.*\)[[:space:]]\+Linux[[:space:]]\+release[[:space:]]\+\(.*\)[[:space:]]*$|DISTRIB_ID=\"\1\"\nDISTRIB_RELEASE=\"\2\"|g" | grep "^DISTRIB")" + elif [[ "${x}" =~ ^.*[[:space:]]+release[[:space:]]+.*[[:space:]]+(.*)[[:space:]]*$ ]]; then + eval "$(echo "${x}" | sed "s|^\(.*\)[[:space:]]\+release[[:space:]]\+\(.*\)[[:space:]]\+(\(.*\))[[:space:]]*$|DISTRIB_ID=\"\1\"\nDISTRIB_RELEASE=\"\2\"\nDISTRIB_CODENAME=\"\3\"|g" | grep "^DISTRIB")" + elif [[ "${x}" =~ ^.*[[:space:]]+release[[:space:]]+.*[[:space:]]+$ ]]; then + eval "$(echo "${x}" | sed "s|^\(.*\)[[:space:]]\+release[[:space:]]\+\(.*\)[[:space:]]*$|DISTRIB_ID=\"\1\"\nDISTRIB_RELEASE=\"\2\"|g" | grep "^DISTRIB")" + fi + + distribution="${DISTRIB_ID}" + version="${DISTRIB_RELEASE}" + codename="${DISTRIB_CODENAME}" + + [ -z "${distribution}" ] && echo >&2 "Cannot parse this lsb-release: ${x}" && return 1 + detection="${file}" + return 0 +} + +get_os_release() { + # Loads the /etc/os-release or /usr/lib/os-release file(s) + # Only the required fields are loaded + # + # If it manages to load a valid os-release, it returns 0 + # otherwise it returns 1 + # + # It searches the ID_LIKE field for a compatible distribution + + os_release_file= + if [ -s "/etc/os-release" ]; then + os_release_file="/etc/os-release" + elif [ -s "/usr/lib/os-release" ]; then + os_release_file="/usr/lib/os-release" + else + echo >&2 "Cannot find an os-release file ..." + return 1 + fi + + local x + echo >&2 "Loading ${os_release_file} ..." + + eval "$(grep -E "^(NAME|ID|ID_LIKE|VERSION|VERSION_ID)=" "${os_release_file}")" + for x in "${ID}" ${ID_LIKE}; do + case "${x,,}" in + almalinux | alpine | arch | centos | clear-linux-os | debian | fedora | gentoo | manjaro | opensuse-leap | ol | rhel | rocky | sabayon | sles | suse | ubuntu) + distribution="${x}" + version="${VERSION_ID}" + codename="${VERSION}" + detection="${os_release_file}" + break + ;; + *) + echo >&2 "Unknown distribution ID: ${x}" + ;; + esac + done + [ -z "${distribution}" ] && echo >&2 "Cannot find valid distribution in: ${ID} ${ID_LIKE}" && return 1 + + [ -z "${distribution}" ] && return 1 + return 0 +} + +get_lsb_release() { + # Loads the /etc/lsb-release file + # If it fails, it attempts to run the command: lsb_release -a + # and parse its output + # + # If it manages to find the lsb-release, it returns 0 + # otherwise it returns 1 + + if [ -f "/etc/lsb-release" ]; then + echo >&2 "Loading /etc/lsb-release ..." + local DISTRIB_ID="" DISTRIB_RELEASE="" DISTRIB_CODENAME="" + eval "$(grep -E "^(DISTRIB_ID|DISTRIB_RELEASE|DISTRIB_CODENAME)=" /etc/lsb-release)" + distribution="${DISTRIB_ID}" + version="${DISTRIB_RELEASE}" + codename="${DISTRIB_CODENAME}" + detection="/etc/lsb-release" + fi + + if [ -z "${distribution}" ] && [ -n "${lsb_release}" ]; then + echo >&2 "Cannot find distribution with /etc/lsb-release" + echo >&2 "Running command: lsb_release ..." + eval "declare -A release=( $(lsb_release -a 2> /dev/null | sed -e "s|^\(.*\):[[:space:]]*\(.*\)$|[\1]=\"\2\"|g") )" + distribution="${release["Distributor ID"]}" + version="${release[Release]}" + codename="${release[Codename]}" + detection="lsb_release" + fi + + [ -z "${distribution}" ] && echo >&2 "Cannot find valid distribution with lsb-release" && return 1 + return 0 +} + +find_etc_any_release() { + # Check for any of the known /etc/x-release files + # If it finds one, it loads it and returns 0 + # otherwise it returns 1 + + if [ -f "/etc/arch-release" ]; then + release2lsb_release "/etc/arch-release" && return 0 + fi + + if [ -f "/etc/centos-release" ]; then + release2lsb_release "/etc/centos-release" && return 0 + fi + + if [ -f "/etc/redhat-release" ]; then + release2lsb_release "/etc/redhat-release" && return 0 + fi + + if [ -f "/etc/SuSe-release" ]; then + release2lsb_release "/etc/SuSe-release" && return 0 + fi + + return 1 +} + +autodetect_distribution() { + # autodetection of distribution/OS + case "$(uname -s)" in + "Linux") + get_os_release || get_lsb_release || find_etc_any_release + ;; + "FreeBSD") + distribution="freebsd" + version="$(uname -r)" + detection="uname" + ;; + "Darwin") + distribution="macos" + version="$(uname -r)" + detection="uname" + + if [ ${EUID} -eq 0 ]; then + echo >&2 "This script does not support running as EUID 0 on macOS. Please run it as a regular user." + exit 1 + fi + ;; + *) + return 1 + ;; + esac +} + +user_picks_distribution() { + # let the user pick a distribution + + echo >&2 + echo >&2 "I NEED YOUR HELP" + echo >&2 "It seems I cannot detect your system automatically." + + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + echo >&2 " > Bailing out..." + exit 1 + fi + + if [ -z "${equo}" ] && [ -z "${emerge}" ] && [ -z "${apt_get}" ] && [ -z "${yum}" ] && [ -z "${dnf}" ] && [ -z "${pacman}" ] && [ -z "${apk}" ] && [ -z "${swupd}" ]; then + echo >&2 "And it seems I cannot find a known package manager in this system." + echo >&2 "Please open a github issue to help us support your system too." + exit 1 + fi + + local opts= + echo >&2 "I found though that the following installers are available:" + echo >&2 + [ -n "${apt_get}" ] && echo >&2 " - Debian/Ubuntu based (installer is: apt-get)" && opts="apt-get ${opts}" + [ -n "${yum}" ] && echo >&2 " - Red Hat/Fedora/CentOS based (installer is: yum)" && opts="yum ${opts}" + [ -n "${dnf}" ] && echo >&2 " - Red Hat/Fedora/CentOS based (installer is: dnf)" && opts="dnf ${opts}" + [ -n "${zypper}" ] && echo >&2 " - SuSe based (installer is: zypper)" && opts="zypper ${opts}" + [ -n "${pacman}" ] && echo >&2 " - Arch Linux based (installer is: pacman)" && opts="pacman ${opts}" + [ -n "${emerge}" ] && echo >&2 " - Gentoo based (installer is: emerge)" && opts="emerge ${opts}" + [ -n "${equo}" ] && echo >&2 " - Sabayon based (installer is: equo)" && opts="equo ${opts}" + [ -n "${apk}" ] && echo >&2 " - Alpine Linux based (installer is: apk)" && opts="apk ${opts}" + [ -n "${swupd}" ] && echo >&2 " - Clear Linux based (installer is: swupd)" && opts="swupd ${opts}" + [ -n "${brew}" ] && echo >&2 " - macOS based (installer is: brew)" && opts="brew ${opts}" + # XXX: This is being removed in another PR. + echo >&2 + + REPLY= + while [ -z "${REPLY}" ]; do + echo "To proceed please write one of these:" + echo "${opts// /, }" + if ! read -r -p ">" REPLY; then + continue + fi + + if [ "${REPLY}" = "yum" ] && [ -z "${distribution}" ]; then + REPLY= + while [ -z "${REPLY}" ]; do + if ! read -r -p "yum in centos, rhel, ol or fedora? > "; then + continue + fi + + case "${REPLY,,}" in + fedora | rhel) + distribution="rhel" + ;; + ol) + distribution="ol" + ;; + centos) + distribution="centos" + ;; + *) + echo >&2 "Please enter 'centos', 'fedora', 'ol' or 'rhel'." + REPLY= + ;; + esac + done + REPLY="yum" + fi + check_package_manager "${REPLY}" || REPLY= + done +} + +detect_package_manager_from_distribution() { + case "${1,,}" in + arch* | manjaro*) + package_installer="install_pacman" + tree="arch" + if [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${pacman}" ]; then + echo >&2 "command 'pacman' is required to install packages on a '${distribution} ${version}' system." + exit 1 + fi + ;; + + sabayon*) + package_installer="install_equo" + tree="sabayon" + if [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${equo}" ]; then + echo >&2 "command 'equo' is required to install packages on a '${distribution} ${version}' system." + # Maybe offer to fall back on emerge? Both installers exist in Sabayon... + exit 1 + fi + ;; + + alpine*) + package_installer="install_apk" + tree="alpine" + if [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${apk}" ]; then + echo >&2 "command 'apk' is required to install packages on a '${distribution} ${version}' system." + exit 1 + fi + ;; + + gentoo*) + package_installer="install_emerge" + tree="gentoo" + if [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${emerge}" ]; then + echo >&2 "command 'emerge' is required to install packages on a '${distribution} ${version}' system." + exit 1 + fi + ;; + + debian* | ubuntu*) + package_installer="install_apt_get" + tree="debian" + if [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${apt_get}" ]; then + echo >&2 "command 'apt-get' is required to install packages on a '${distribution} ${version}' system." + exit 1 + fi + ;; + + centos* | clearos* | rocky* | almalinux*) + package_installer="" + tree="centos" + [ -n "${yum}" ] && package_installer="install_yum" + [ -n "${dnf}" ] && package_installer="install_dnf" + if [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${package_installer}" ]; then + echo >&2 "command 'yum' or 'dnf' is required to install packages on a '${distribution} ${version}' system." + exit 1 + fi + ;; + + fedora* | redhat* | red\ hat* | rhel*) + package_installer= + tree="rhel" + [ -n "${yum}" ] && package_installer="install_yum" + [ -n "${dnf}" ] && package_installer="install_dnf" + if [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${package_installer}" ]; then + echo >&2 "command 'yum' or 'dnf' is required to install packages on a '${distribution} ${version}' system." + exit 1 + fi + ;; + + ol*) + package_installer= + tree="ol" + [ -n "${yum}" ] && package_installer="install_yum" + [ -n "${dnf}" ] && package_installer="install_dnf" + if [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${package_installer}" ]; then + echo >&2 "command 'yum' or 'dnf' is required to install packages on a '${distribution} ${version}' system." + exit 1 + fi + ;; + + suse* | opensuse* | sles*) + package_installer="install_zypper" + tree="suse" + if [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${zypper}" ]; then + echo >&2 "command 'zypper' is required to install packages on a '${distribution} ${version}' system." + exit 1 + fi + ;; + + clear-linux* | clearlinux*) + package_installer="install_swupd" + tree="clearlinux" + if [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${swupd}" ]; then + echo >&2 "command 'swupd' is required to install packages on a '${distribution} ${version}' system." + exit 1 + fi + ;; + + freebsd) + package_installer="install_pkg" + tree="freebsd" + if [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${pkg}" ]; then + echo >&2 "command 'pkg' is required to install packages on a '${distribution} ${version}' system." + exit 1 + fi + ;; + macos) + package_installer="install_brew" + tree="macos" + if [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${brew}" ]; then + echo >&2 "command 'brew' is required to install packages on a '${distribution} ${version}' system." + exit 1 + fi + ;; + + *) + # oops! unknown system + user_picks_distribution + ;; + esac +} + +# XXX: This is being removed in another PR. +check_package_manager() { + # This is called only when the user is selecting a package manager + # It is used to verify the user selection is right + + echo >&2 "Checking package manager: ${1}" + + case "${1}" in + apt-get) + [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${apt_get}" ] && echo >&2 "${1} is not available." && return 1 + package_installer="install_apt_get" + tree="debian" + detection="user-input" + return 0 + ;; + + dnf) + [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${dnf}" ] && echo >&2 "${1} is not available." && return 1 + package_installer="install_dnf" + if [ "${distribution}" = "centos" ]; then + tree="centos" + elif [ "${distribution}" = "ol" ]; then + tree="ol" + else + tree="rhel" + fi + detection="user-input" + return 0 + ;; + + apk) + [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${apk}" ] && echo >&2 "${1} is not available." && return 1 + package_installer="install_apk" + tree="alpine" + detection="user-input" + return 0 + ;; + + equo) + [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${equo}" ] && echo >&2 "${1} is not available." && return 1 + package_installer="install_equo" + tree="sabayon" + detection="user-input" + return 0 + ;; + + emerge) + [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${emerge}" ] && echo >&2 "${1} is not available." && return 1 + package_installer="install_emerge" + tree="gentoo" + detection="user-input" + return 0 + ;; + + pacman) + [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${pacman}" ] && echo >&2 "${1} is not available." && return 1 + package_installer="install_pacman" + tree="arch" + detection="user-input" + + return 0 + ;; + + zypper) + [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${zypper}" ] && echo >&2 "${1} is not available." && return 1 + package_installer="install_zypper" + tree="suse" + detection="user-input" + return 0 + ;; + + yum) + [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${yum}" ] && echo >&2 "${1} is not available." && return 1 + package_installer="install_yum" + if [ "${distribution}" = "centos" ]; then + tree="centos" + elif [ "${distribution}" = "ol" ]; then + tree="ol" + else + tree="rhel" + fi + detection="user-input" + return 0 + ;; + + swupd) + [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${swupd}" ] && echo >&2 "${1} is not available." && return 1 + package_installer="install_swupd" + tree="clear-linux" + detection="user-input" + return 0 + ;; + + brew) + [ "${IGNORE_INSTALLED}" -eq 0 ] && [ -z "${brew}" ] && echo >&2 "${1} is not available." && return 1 + package_installer="install_brew" + tree="macos" + detection="user-input" + + return 0 + ;; + + *) + echo >&2 "Invalid package manager: '${1}'." + return 1 + ;; + esac +} + +require_cmd() { + # check if any of the commands given as argument + # are present on this system + # If any of them is available, it returns 0 + # otherwise 1 + + [ "${IGNORE_INSTALLED}" -eq 1 ] && return 1 + + local wanted found + for wanted in "${@}"; do + if command -v "${wanted}" > /dev/null 2>&1; then + found="$(command -v "$wanted" 2> /dev/null)" + fi + [ -n "${found}" ] && [ -x "${found}" ] && return 0 + done + return 1 +} + +declare -A pkg_find=( + ['gentoo']="sys-apps/findutils" + ['fedora']="findutils" + ['clearlinux']="findutils" + ['macos']="NOTREQUIRED" + ['freebsd']="NOTREQUIRED" + ['default']="WARNING|" +) + +declare -A pkg_distro_sdk=( + ['alpine']="alpine-sdk" + ['default']="NOTREQUIRED" +) + +declare -A pkg_autoconf=( + ['gentoo']="sys-devel/autoconf" + ['clearlinux']="c-basic" + ['default']="autoconf" +) + +# required to compile netdata with --enable-sse +# https://github.com/firehol/netdata/pull/450 +declare -A pkg_autoconf_archive=( + ['gentoo']="sys-devel/autoconf-archive" + ['clearlinux']="c-basic" + ['alpine']="WARNING|" + ['default']="autoconf-archive" + + # exceptions + ['centos-6']="WARNING|" + ['rhel-6']="WARNING|" + ['rhel-7']="WARNING|" +) + +declare -A pkg_autogen=( + ['gentoo']="sys-devel/autogen" + ['clearlinux']="c-basic" + ['alpine']="WARNING|" + ['default']="autogen" + + # exceptions + ['centos-6']="WARNING|" + ['rhel-6']="WARNING|" + ['centos-9']="NOTREQUIRED|" + ['rhel-9']="NOTREQUIRED|" +) + +declare -A pkg_automake=( + ['gentoo']="sys-devel/automake" + ['clearlinux']="c-basic" + ['default']="automake" +) + +# Required to build libwebsockets and libmosquitto on some systems. +declare -A pkg_cmake=( + ['gentoo']="dev-util/cmake" + ['clearlinux']="c-basic" + ['default']="cmake" +) + +declare -A pkg_json_c_dev=( + ['alpine']="json-c-dev" + ['arch']="json-c" + ['clearlinux']="devpkg-json-c" + ['debian']="libjson-c-dev" + ['gentoo']="dev-libs/json-c" + ['sabayon']="dev-libs/json-c" + ['suse']="libjson-c-devel" + ['freebsd']="json-c" + ['macos']="json-c" + ['default']="json-c-devel" +) + +declare -A pkg_libatomic=( + ['arch']="NOTREQUIRED" + ['clearlinux']="NOTREQUIRED" + ['debian']="libatomic1" + ['freebsd']="NOTREQUIRED" + ['gentoo']="NOTREQUIRED" + ['macos']="NOTREQUIRED" + ['sabayon']="NOTREQUIRED" + ['suse']="libatomic1" + ['ubuntu']="libatomic1" + ['default']="libatomic" +) + +declare -A pkg_bridge_utils=( + ['gentoo']="net-misc/bridge-utils" + ['clearlinux']="network-basic" + ['macos']="WARNING|" + ['default']="bridge-utils" +) + +declare -A pkg_curl=( + ['gentoo']="net-misc/curl" + ['sabayon']="net-misc/curl" + ['default']="curl" +) + +declare -A pkg_gzip=( + ['gentoo']="app-arch/gzip" + ['macos']="NOTREQUIRED" + ['default']="gzip" +) + +declare -A pkg_tar=( + ['gentoo']="app-arch/tar" + ['clearlinux']="os-core-update" + ['macos']="NOTREQUIRED" + ['default']="tar" +) + +declare -A pkg_git=( + ['gentoo']="dev-vcs/git" + ['default']="git" +) + +declare -A pkg_gcc=( + ['gentoo']="sys-devel/gcc" + ['clearlinux']="c-basic" + ['macos']="NOTREQUIRED" + ['default']="gcc" +) + +# g++, required for building protobuf +# All three cases of this not being required are systems that implicitly +# include g++ when installing gcc. +declare -A pkg_gxx=( + ['alpine']="g++" + ['arch']="NOTREQUIRED" + ['clearlinux']="c-basic" + ['debian']="g++" + ['gentoo']="NOTREQUIRED" + ['macos']="NOTREQUIRED" + ['ubuntu']="g++" + ['freebsd']="NOTREQUIRED" + ['default']="gcc-c++" +) + +declare -A pkg_gdb=( + ['gentoo']="sys-devel/gdb" + ['macos']="NOTREQUIRED" + ['default']="gdb" +) + +declare -A pkg_iotop=( + ['gentoo']="sys-process/iotop" + ['macos']="WARNING|" + ['default']="iotop" +) + +declare -A pkg_iproute2=( + ['alpine']="iproute2" + ['debian']="iproute2" + ['gentoo']="sys-apps/iproute2" + ['sabayon']="sys-apps/iproute2" + ['clearlinux']="iproute2" + ['macos']="WARNING|" + ['default']="iproute" + + # exceptions + ['ubuntu-12.04']="iproute" +) + +declare -A pkg_ipset=( + ['gentoo']="net-firewall/ipset" + ['clearlinux']="network-basic" + ['macos']="WARNING|" + ['default']="ipset" +) + +declare -A pkg_jq=( + ['gentoo']="app-misc/jq" + ['default']="jq" +) + +declare -A pkg_iptables=( + ['gentoo']="net-firewall/iptables" + ['macos']="WARNING|" + ['default']="iptables" +) + +declare -A pkg_libz_dev=( + ['alpine']="zlib-dev" + ['arch']="zlib" + ['centos']="zlib-devel" + ['debian']="zlib1g-dev" + ['gentoo']="sys-libs/zlib" + ['sabayon']="sys-libs/zlib" + ['rhel']="zlib-devel" + ['ol']="zlib-devel" + ['suse']="zlib-devel" + ['clearlinux']="devpkg-zlib" + ['macos']="NOTREQUIRED" + ['freebsd']="lzlib" + ['default']="" +) + +declare -A pkg_libuuid_dev=( + ['alpine']="util-linux-dev" + ['arch']="util-linux" + ['centos']="libuuid-devel" + ['clearlinux']="devpkg-util-linux" + ['debian']="uuid-dev" + ['gentoo']="sys-apps/util-linux" + ['sabayon']="sys-apps/util-linux" + ['rhel']="libuuid-devel" + ['ol']="libuuid-devel" + ['suse']="libuuid-devel" + ['macos']="ossp-uuid" + ['freebsd']="e2fsprogs-libuuid" + ['default']="" +) + +declare -A pkg_libmnl_dev=( + ['alpine']="libmnl-dev" + ['arch']="libmnl" + ['centos']="libmnl-devel" + ['debian']="libmnl-dev" + ['gentoo']="net-libs/libmnl" + ['sabayon']="net-libs/libmnl" + ['rhel']="libmnl-devel" + ['ol']="libmnl-devel" + ['suse']="libmnl-devel" + ['clearlinux']="devpkg-libmnl" + ['macos']="NOTREQUIRED" + ['default']="" +) + +declare -A pkg_lm_sensors=( + ['alpine']="lm_sensors" + ['arch']="lm_sensors" + ['centos']="lm_sensors" + ['debian']="lm-sensors" + ['gentoo']="sys-apps/lm-sensors" + ['sabayon']="sys-apps/lm_sensors" + ['rhel']="lm_sensors" + ['suse']="sensors" + ['clearlinux']="lm-sensors" + ['macos']="WARNING|" + ['freebsd']="NOTREQUIRED" + ['default']="lm_sensors" +) + +declare -A pkg_logwatch=( + ['gentoo']="sys-apps/logwatch" + ['clearlinux']="WARNING|" + ['macos']="WARNING|" + ['default']="logwatch" +) + +declare -A pkg_lxc=( + ['gentoo']="app-emulation/lxc" + ['clearlinux']="WARNING|" + ['macos']="WARNING|" + ['default']="lxc" +) + +declare -A pkg_mailutils=( + ['gentoo']="net-mail/mailutils" + ['clearlinux']="WARNING|" + ['macos']="WARNING|" + ['default']="mailutils" +) + +declare -A pkg_make=( + ['gentoo']="sys-devel/make" + ['macos']="NOTREQUIRED" + ['freebsd']="gmake" + ['default']="make" +) + +declare -A pkg_nginx=( + ['gentoo']="www-servers/nginx" + ['default']="nginx" +) + +declare -A pkg_postfix=( + ['gentoo']="mail-mta/postfix" + ['macos']="WARNING|" + ['default']="postfix" +) + +declare -A pkg_pkg_config=( + ['alpine']="pkgconfig" + ['arch']="pkgconfig" + ['centos']="pkgconfig" + ['debian']="pkg-config" + ['gentoo']="virtual/pkgconfig" + ['sabayon']="virtual/pkgconfig" + ['rhel']="pkgconfig" + ['ol']="pkgconfig" + ['suse']="pkg-config" + ['freebsd']="pkgconf" + ['clearlinux']="c-basic" + ['default']="pkg-config" +) + +declare -A pkg_python=( + ['gentoo']="dev-lang/python" + ['sabayon']="dev-lang/python:2.7" + ['clearlinux']="python-basic" + ['default']="python" + + # Exceptions + ['macos']="WARNING|" + ['centos-8']="python2" +) + +declare -A pkg_python_pip=( + ['alpine']="py-pip" + ['gentoo']="dev-python/pip" + ['sabayon']="dev-python/pip" + ['clearlinux']="python-basic" + ['macos']="WARNING|" + ['default']="python-pip" +) + +declare -A pkg_python3_pip=( + ['alpine']="py3-pip" + ['arch']="python-pip" + ['gentoo']="dev-python/pip" + ['sabayon']="dev-python/pip" + ['clearlinux']="python3-basic" + ['macos']="NOTREQUIRED" + ['default']="python3-pip" +) + +declare -A pkg_python_pymongo=( + ['alpine']="WARNING|" + ['arch']="python2-pymongo" + ['centos']="WARNING|" + ['debian']="python-pymongo" + ['gentoo']="dev-python/pymongo" + ['suse']="python-pymongo" + ['clearlinux']="WARNING|" + ['rhel']="WARNING|" + ['ol']="WARNING|" + ['macos']="WARNING|" + ['default']="python-pymongo" +) + +declare -A pkg_python3_pymongo=( + ['alpine']="WARNING|" + ['arch']="python-pymongo" + ['centos']="WARNING|" + ['debian']="python3-pymongo" + ['gentoo']="dev-python/pymongo" + ['suse']="python3-pymongo" + ['clearlinux']="WARNING|" + ['rhel']="WARNING|" + ['ol']="WARNING|" + ['freebsd']="py37-pymongo" + ['macos']="WARNING|" + ['default']="python3-pymongo" + + ['centos-7']="python36-pymongo" + ['centos-8']="python3-pymongo" + ['rhel-7']="python36-pymongo" + ['rhel-8']="python3-pymongo" + ['ol-8']="python3-pymongo" +) + +declare -A pkg_python_requests=( + ['alpine']="py-requests" + ['arch']="python2-requests" + ['centos']="python-requests" + ['debian']="python-requests" + ['gentoo']="dev-python/requests" + ['sabayon']="dev-python/requests" + ['rhel']="python-requests" + ['suse']="python-requests" + ['clearlinux']="python-extras" + ['macos']="WARNING|" + ['default']="python-requests" + ['alpine-3.1.4']="WARNING|" + ['alpine-3.2.3']="WARNING|" +) + +declare -A pkg_python3_requests=( + ['alpine']="py3-requests" + ['arch']="python-requests" + ['centos']="WARNING|" + ['debian']="WARNING|" + ['gentoo']="dev-python/requests" + ['sabayon']="dev-python/requests" + ['rhel']="WARNING|" + ['suse']="WARNING|" + ['clearlinux']="python-extras" + ['macos']="WARNING|" + ['default']="WARNING|" + + ['centos-7']="python36-requests" + ['centos-8']="python3-requests" + ['rhel-7']="python36-requests" + ['rhel-8']="python3-requests" + ['ol-8']="python3-requests" +) + +declare -A pkg_lz4=( + ['alpine']="lz4-dev" + ['debian']="liblz4-dev" + ['ubuntu']="liblz4-dev" + ['suse']="liblz4-devel" + ['gentoo']="app-arch/lz4" + ['clearlinux']="devpkg-lz4" + ['arch']="lz4" + ['macos']="lz4" + ['freebsd']="liblz4" + ['default']="lz4-devel" +) + +declare -A pkg_libuv=( + ['alpine']="libuv-dev" + ['debian']="libuv1-dev" + ['ubuntu']="libuv1-dev" + ['gentoo']="dev-libs/libuv" + ['arch']="libuv" + ['clearlinux']="devpkg-libuv" + ['macos']="libuv" + ['freebsd']="libuv" + ['default']="libuv-devel" +) + +declare -A pkg_openssl=( + ['alpine']="openssl-dev" + ['debian']="libssl-dev" + ['ubuntu']="libssl-dev" + ['suse']="libopenssl-devel" + ['clearlinux']="devpkg-openssl" + ['gentoo']="dev-libs/openssl" + ['arch']="openssl" + ['freebsd']="openssl" + ['macos']="openssl" + ['default']="openssl-devel" +) + +declare -A pkg_python3=( + ['gentoo']="dev-lang/python" + ['sabayon']="dev-lang/python:3.4" + ['clearlinux']="python3-basic" + ['macos']="python" + ['default']="python3" + + # exceptions + ['centos-6']="WARNING|" +) + +declare -A pkg_screen=( + ['gentoo']="app-misc/screen" + ['sabayon']="app-misc/screen" + ['clearlinux']="sysadmin-basic" + ['default']="screen" +) + +declare -A pkg_sudo=( + ['gentoo']="app-admin/sudo" + ['macos']="NOTREQUIRED" + ['default']="sudo" +) + +declare -A pkg_sysstat=( + ['gentoo']="app-admin/sysstat" + ['macos']="WARNING|" + ['default']="sysstat" +) + +declare -A pkg_tcpdump=( + ['gentoo']="net-analyzer/tcpdump" + ['clearlinux']="network-basic" + ['default']="tcpdump" +) + +declare -A pkg_traceroute=( + ['alpine']=" " + ['gentoo']="net-analyzer/traceroute" + ['clearlinux']="network-basic" + ['macos']="NOTREQUIRED" + ['default']="traceroute" +) + +declare -A pkg_valgrind=( + ['gentoo']="dev-util/valgrind" + ['default']="valgrind" +) + +declare -A pkg_ulogd=( + ['centos']="WARNING|" + ['rhel']="WARNING|" + ['ol']="WARNING|" + ['clearlinux']="WARNING|" + ['gentoo']="app-admin/ulogd" + ['arch']="ulogd" + ['macos']="WARNING|" + ['default']="ulogd2" +) + +declare -A pkg_unzip=( + ['gentoo']="app-arch/unzip" + ['macos']="NOTREQUIRED" + ['default']="unzip" +) + +declare -A pkg_zip=( + ['gentoo']="app-arch/zip" + ['macos']="NOTREQUIRED" + ['default']="zip" +) + +declare -A pkg_libelf=( + ['alpine']="elfutils-dev" + ['arch']="libelf" + ['gentoo']="virtual/libelf" + ['sabayon']="virtual/libelf" + ['debian']="libelf-dev" + ['ubuntu']="libelf-dev" + ['fedora']="elfutils-libelf-devel" + ['centos']="elfutils-libelf-devel" + ['rhel']="elfutils-libelf-devel" + ['ol']="elfutils-libelf-devel" + ['clearlinux']="devpkg-elfutils" + ['suse']="libelf-devel" + ['macos']="NOTREQUIRED" + ['freebsd']="NOTREQUIRED" + ['default']="libelf-devel" + + # exceptions + ['alpine-3.5']="libelf-dev" + ['alpine-3.4']="libelf-dev" + ['alpine-3.3']="libelf-dev" +) + +validate_package_trees() { + if type -t validate_tree_${tree} > /dev/null; then + validate_tree_${tree} + fi +} + +validate_installed_package() { + validate_${package_installer} "${p}" +} + +suitable_package() { + local package="${1//-/_}" p="" v="${version//.*/}" + + echo >&2 "Searching for ${package} ..." + + eval "p=\${pkg_${package}['${distribution,,}-${version,,}']}" + [ -z "${p}" ] && eval "p=\${pkg_${package}['${distribution,,}-${v,,}']}" + [ -z "${p}" ] && eval "p=\${pkg_${package}['${distribution,,}']}" + [ -z "${p}" ] && eval "p=\${pkg_${package}['${tree}-${version}']}" + [ -z "${p}" ] && eval "p=\${pkg_${package}['${tree}-${v}']}" + [ -z "${p}" ] && eval "p=\${pkg_${package}['${tree}']}" + [ -z "${p}" ] && eval "p=\${pkg_${package}['default']}" + + if [[ "${p/|*/}" =~ ^(ERROR|WARNING|INFO)$ ]]; then + echo >&2 "${p/|*/}" + echo >&2 "package ${1} is not available in this system." + if [ -z "${p/*|/}" ]; then + echo >&2 "You may try to install without it." + else + echo >&2 "${p/*|/}" + fi + echo >&2 + return 1 + elif [ "${p}" = "NOTREQUIRED" ]; then + return 0 + elif [ -z "${p}" ]; then + echo >&2 "WARNING" + echo >&2 "package ${1} is not available in this system." + echo >&2 + return 1 + else + if [ "${IGNORE_INSTALLED}" -eq 0 ]; then + validate_installed_package "${p}" + else + echo "${p}" + fi + return 0 + fi +} + +packages() { + # detect the packages we need to install on this system + + # ------------------------------------------------------------------------- + # basic build environment + + suitable_package distro-sdk + suitable_package libatomic + + require_cmd git || suitable_package git + require_cmd find || suitable_package find + + require_cmd gcc || require_cmd clang || + require_cmd gcc-multilib || suitable_package gcc + require_cmd g++ || require_cmd clang++ || suitable_package gxx + + require_cmd make || suitable_package make + require_cmd autoconf || suitable_package autoconf + suitable_package autoconf-archive + require_cmd autogen || suitable_package autogen + require_cmd automake || suitable_package automake + require_cmd pkg-config || suitable_package pkg-config + require_cmd cmake || suitable_package cmake + + # ------------------------------------------------------------------------- + # debugging tools for development + + if [ "${PACKAGES_DEBUG}" -ne 0 ]; then + require_cmd traceroute || suitable_package traceroute + require_cmd tcpdump || suitable_package tcpdump + require_cmd screen || suitable_package screen + + if [ "${PACKAGES_NETDATA}" -ne 0 ]; then + require_cmd gdb || suitable_package gdb + require_cmd valgrind || suitable_package valgrind + fi + fi + + # ------------------------------------------------------------------------- + # common command line tools + + if [ "${PACKAGES_NETDATA}" -ne 0 ]; then + require_cmd tar || suitable_package tar + require_cmd curl || suitable_package curl + require_cmd gzip || suitable_package gzip + fi + + # ------------------------------------------------------------------------- + # firehol/fireqos/update-ipsets command line tools + + if [ "${PACKAGES_FIREQOS}" -ne 0 ]; then + require_cmd ip || suitable_package iproute2 + fi + + if [ "${PACKAGES_FIREHOL}" -ne 0 ]; then + require_cmd iptables || suitable_package iptables + require_cmd ipset || suitable_package ipset + require_cmd ulogd ulogd2 || suitable_package ulogd + require_cmd traceroute || suitable_package traceroute + require_cmd bridge || suitable_package bridge-utils + fi + + if [ "${PACKAGES_UPDATE_IPSETS}" -ne 0 ]; then + require_cmd ipset || suitable_package ipset + require_cmd zip || suitable_package zip + require_cmd funzip || suitable_package unzip + fi + + # ------------------------------------------------------------------------- + # netdata libraries + + if [ "${PACKAGES_NETDATA}" -ne 0 ]; then + suitable_package libz-dev + suitable_package libuuid-dev + suitable_package libmnl-dev + suitable_package json-c-dev + fi + + # ------------------------------------------------------------------------- + # sensors + + if [ "${PACKAGES_NETDATA_SENSORS}" -ne 0 ]; then + require_cmd sensors || suitable_package lm_sensors + fi + + # ------------------------------------------------------------------------- + # netdata database + if [ "${PACKAGES_NETDATA_DATABASE}" -ne 0 ]; then + suitable_package libuv + suitable_package lz4 + suitable_package openssl + fi + + # ------------------------------------------------------------------------- + # ebpf plugin + if [ "${PACKAGES_NETDATA_EBPF}" -ne 0 ]; then + suitable_package libelf + fi + + # ------------------------------------------------------------------------- + # python2 + + if [ "${PACKAGES_NETDATA_PYTHON}" -ne 0 ]; then + require_cmd python || suitable_package python + + [ "${PACKAGES_NETDATA_PYTHON_MONGO}" -ne 0 ] && suitable_package python-pymongo + # suitable_package python-requests + # suitable_package python-pip + fi + + # ------------------------------------------------------------------------- + # python3 + + if [ "${PACKAGES_NETDATA_PYTHON3}" -ne 0 ]; then + require_cmd python3 || suitable_package python3 + + [ "${PACKAGES_NETDATA_PYTHON_MONGO}" -ne 0 ] && suitable_package python3-pymongo + # suitable_package python3-requests + # suitable_package python3-pip + fi + + # ------------------------------------------------------------------------- + # applications needed for the netdata demo sites + + if [ "${PACKAGES_NETDATA_DEMO_SITE}" -ne 0 ]; then + require_cmd sudo || suitable_package sudo + require_cmd jq || suitable_package jq + require_cmd nginx || suitable_package nginx + require_cmd postconf || suitable_package postfix + require_cmd lxc-create || suitable_package lxc + require_cmd logwatch || suitable_package logwatch + require_cmd mail || suitable_package mailutils + require_cmd iostat || suitable_package sysstat + require_cmd iotop || suitable_package iotop + fi +} + +DRYRUN=0 +run() { + + printf >&2 "%q " "${@}" + printf >&2 "\n" + + if [ ! "${DRYRUN}" -eq 1 ]; then + "${@}" + return $? + fi + return 0 +} + +sudo= +if [ ${UID} -ne 0 ]; then + sudo="sudo" +fi + +# ----------------------------------------------------------------------------- +# debian / ubuntu + +validate_install_apt_get() { + echo >&2 " > Checking if package '${*}' is installed..." + [ "$(dpkg-query -W --showformat='${Status}\n' "${*}")" = "install ok installed" ] || echo "${*}" +} + +install_apt_get() { + local opts="" + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + # http://serverfault.com/questions/227190/how-do-i-ask-apt-get-to-skip-any-interactive-post-install-configuration-steps + export DEBIAN_FRONTEND="noninteractive" + opts="${opts} -yq" + fi + + read -r -a apt_opts <<< "$opts" + + # update apt repository caches + + echo >&2 "NOTE: Running apt-get update and updating your APT caches ..." + if [ "${version}" = 8 ]; then + echo >&2 "WARNING: You seem to be on Debian 8 (jessie) which is old enough we have to disable Check-Valid-Until checks" + if ! cat /etc/apt/sources.list /etc/apt/sources.list.d/* 2> /dev/null | grep -q jessie-backports; then + echo >&2 "We also have to enable the jessie-backports repository" + if prompt "Is this okay?"; then + ${sudo} /bin/sh -c 'echo "deb http://archive.debian.org/debian/ jessie-backports main contrib non-free" >> /etc/apt/sources.list.d/99-archived.list' + fi + fi + run ${sudo} apt-get "${apt_opts[@]}" -o Acquire::Check-Valid-Until=false update + else + run ${sudo} apt-get "${apt_opts[@]}" update + fi + + # install the required packages + run ${sudo} apt-get "${apt_opts[@]}" install "${@}" +} + +# ----------------------------------------------------------------------------- +# centos / rhel + +prompt() { + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode, assuming yes (y)" + echo >&2 " > Would have prompted for ${1} ..." + return 0 + fi + + while true; do + read -r -p "${1} [y/n] " yn + case $yn in + [Yy]*) return 0 ;; + [Nn]*) return 1 ;; + *) echo >&2 "Please answer with yes (y) or no (n)." ;; + esac + done +} + +validate_tree_freebsd() { + local opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + + echo >&2 " > FreeBSD Version: ${version} ..." + + make="make" + echo >&2 " > Checking for gmake ..." + if ! pkg query %n-%v | grep -q gmake; then + if prompt "gmake is required to build on FreeBSD and is not installed. Shall I install it?"; then + run ${sudo} pkg install ${opts} gmake + fi + fi +} + +validate_tree_ol() { + local opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + + if [[ "${version}" =~ ^8(\..*)?$ ]]; then + echo " > Checking for CodeReady Builder ..." + if ! run ${sudo} dnf repolist | grep -q codeready; then + if prompt "CodeReady Builder not found, shall I install it?"; then + cat > /etc/yum.repos.d/ol8_codeready.repo <<-EOF + [ol8_codeready_builder] + name=Oracle Linux \$releasever CodeReady Builder (\$basearch) + baseurl=http://yum.oracle.com/repo/OracleLinux/OL8/codeready/builder/\$basearch + gpgkey=file:///etc/pki/rpm-gpg/RPM-GPG-KEY-oracle + gpgcheck=1 + enabled=1 + EOF + fi + fi + elif [[ "${version}" =~ ^9(\..*)?$ ]]; then + echo " > Checking for CodeReady Builder ..." + if ! run ${sudo} dnf repolist enabled | grep -q codeready; then + if prompt "CodeReady Builder not enabled, shall I enable it?"; then + run ${sudo} dnf config-manager --set-enabled ol9_codeready_builder + fi + fi + fi +} + +validate_tree_centos() { + local opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + + echo >&2 " > CentOS Version: ${version} ..." + + if [[ "${version}" =~ ^9(\..*)?$ ]]; then + echo >&2 " > Checking for config-manager ..." + if ! run ${sudo} dnf config-manager --help; then + if prompt "config-manager not found, shall I install it?"; then + run ${sudo} dnf ${opts} install 'dnf-command(config-manager)' + fi + fi + + echo >&2 " > Checking for CRB ..." + if ! run dnf ${sudo} repolist | grep CRB; then + if prompt "CRB not found, shall I install it?"; then + run ${sudo} dnf ${opts} config-manager --set-enabled crb + fi + fi + elif [[ "${version}" =~ ^8(\..*)?$ ]]; then + echo >&2 " > Checking for config-manager ..." + if ! run ${sudo} yum config-manager --help; then + if prompt "config-manager not found, shall I install it?"; then + run ${sudo} yum ${opts} install 'dnf-command(config-manager)' + fi + fi + + echo >&2 " > Checking for PowerTools ..." + if ! run yum ${sudo} repolist | grep PowerTools; then + if prompt "PowerTools not found, shall I install it?"; then + run ${sudo} yum ${opts} config-manager --set-enabled powertools + fi + fi + + echo >&2 " > Updating libarchive ..." + run ${sudo} yum ${opts} install libarchive + + elif [[ "${version}" =~ ^7(\..*)?$ ]]; then + echo >&2 " > Checking for EPEL ..." + if ! rpm -qa | grep epel-release > /dev/null; then + if prompt "EPEL not found, shall I install it?"; then + run ${sudo} yum ${opts} install epel-release + fi + fi + elif [[ "${version}" =~ ^6\..*$ ]]; then + echo >&2 " > Detected CentOS 6.x ..." + echo >&2 " > Checking for Okay ..." + if ! rpm -qa | grep okay > /dev/null; then + if prompt "okay not found, shall I install it?"; then + run ${sudo} yum ${opts} install http://repo.okay.com.mx/centos/6/x86_64/release/okay-release-1-3.el6.noarch.rpm + fi + fi + + fi +} + +validate_install_yum() { + echo >&2 " > Checking if package '${*}' is installed..." + yum list installed "${*}" > /dev/null 2>&1 || echo "${*}" +} + +install_yum() { + # download the latest package info + if [ "${DRYRUN}" -eq 1 ]; then + echo >&2 " >> IMPORTANT << " + echo >&2 " Please make sure your system is up to date" + echo >&2 " by running: ${sudo} yum update " + echo >&2 + fi + + local opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + # http://unix.stackexchange.com/questions/87822/does-yum-have-an-equivalent-to-apt-aptitudes-debian-frontend-noninteractive + opts="-y" + fi + + read -r -a yum_opts <<< "${opts}" + + # install the required packages + run ${sudo} yum "${yum_opts[@]}" install "${@}" +} + +# ----------------------------------------------------------------------------- +# fedora + +validate_install_dnf() { + echo >&2 " > Checking if package '${*}' is installed..." + dnf list installed "${*}" > /dev/null 2>&1 || echo "${*}" +} + +install_dnf() { + # download the latest package info + if [ "${DRYRUN}" -eq 1 ]; then + echo >&2 " >> IMPORTANT << " + echo >&2 " Please make sure your system is up to date" + echo >&2 " by running: ${sudo} dnf update " + echo >&2 + fi + + local opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + # man dnf + opts="-y" + fi + + # install the required packages + # --setopt=strict=0 allows dnf to proceed + # installing whatever is available + # even if a package is not found + opts="$opts --setopt=strict=0" + read -r -a dnf_opts <<< "$opts" + run ${sudo} dnf "${dnf_opts[@]}" install "${@}" +} + +# ----------------------------------------------------------------------------- +# gentoo + +validate_install_emerge() { + echo "${*}" +} + +install_emerge() { + # download the latest package info + # we don't do this for emerge - it is very slow + # and most users are expected to do this daily + # emerge --sync + if [ "${DRYRUN}" -eq 1 ]; then + echo >&2 " >> IMPORTANT << " + echo >&2 " Please make sure your system is up to date" + echo >&2 " by running: ${sudo} emerge --sync or ${sudo} eix-sync " + echo >&2 + fi + + local opts="--ask" + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="" + fi + + read -r -a emerge_opts <<< "$opts" + + # install the required packages + run ${sudo} emerge "${emerge_opts[@]}" -v --noreplace "${@}" +} + +# ----------------------------------------------------------------------------- +# alpine + +validate_install_apk() { + echo "${*}" +} + +install_apk() { + # download the latest package info + if [ "${DRYRUN}" -eq 1 ]; then + echo >&2 " >> IMPORTANT << " + echo >&2 " Please make sure your system is up to date" + echo >&2 " by running: ${sudo} apk update " + echo >&2 + fi + + local opts="--force-broken-world" + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + else + opts="${opts} -i" + fi + + read -r -a apk_opts <<< "$opts" + + # install the required packages + run ${sudo} apk add "${apk_opts[@]}" "${@}" +} + +# ----------------------------------------------------------------------------- +# sabayon + +validate_install_equo() { + echo >&2 " > Checking if package '${*}' is installed..." + equo s --installed "${*}" > /dev/null 2>&1 || echo "${*}" +} + +install_equo() { + # download the latest package info + if [ "${DRYRUN}" -eq 1 ]; then + echo >&2 " >> IMPORTANT << " + echo >&2 " Please make sure your system is up to date" + echo >&2 " by running: ${sudo} equo up " + echo >&2 + fi + + local opts="-av" + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="-v" + fi + + read -r -a equo_opts <<< "$opts" + + # install the required packages + run ${sudo} equo i "${equo_opts[@]}" "${@}" +} + +# ----------------------------------------------------------------------------- +# arch + +PACMAN_DB_SYNCED=0 +validate_install_pacman() { + + if [ ${PACMAN_DB_SYNCED} -eq 0 ]; then + echo >&2 " > Running pacman -Sy to sync the database" + local x + x=$(pacman -Sy) + [ -z "${x}" ] && echo "${*}" + PACMAN_DB_SYNCED=1 + fi + echo >&2 " > Checking if package '${*}' is installed..." + + # In pacman, you can utilize alternative flags to exactly match package names, + # but is highly likely we require pattern matching too in this so we keep -s and match + # the exceptional cases like so + local x="" + case "${package}" in + "gcc") + # Temporary workaround: In archlinux, default installation includes runtime libs under package "gcc" + # These are not sufficient for netdata install, so we need to make sure that the appropriate libraries are there + # by ensuring devel libs are available + x=$(pacman -Qs "${*}" | grep "base-devel") + ;; + "tar") + x=$(pacman -Qs "${*}" | grep "local/tar") + ;; + "make") + x=$(pacman -Qs "${*}" | grep "local/make ") + ;; + *) + x=$(pacman -Qs "${*}") + ;; + esac + + [ -z "${x}" ] && echo "${*}" +} + +install_pacman() { + # download the latest package info + if [ "${DRYRUN}" -eq 1 ]; then + echo >&2 " >> IMPORTANT << " + echo >&2 " Please make sure your system is up to date" + echo >&2 " by running: ${sudo} pacman -Syu " + echo >&2 + fi + + # install the required packages + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + # http://unix.stackexchange.com/questions/52277/pacman-option-to-assume-yes-to-every-question/52278 + # Try the noconfirm option, if that fails, go with the legacy way for non-interactive + run ${sudo} pacman --noconfirm --needed -S "${@}" || yes | run ${sudo} pacman --needed -S "${@}" + else + run ${sudo} pacman --needed -S "${@}" + fi +} + +# ----------------------------------------------------------------------------- +# suse / opensuse + +validate_install_zypper() { + rpm -q "${*}" > /dev/null 2>&1 || echo "${*}" +} + +install_zypper() { + # download the latest package info + if [ "${DRYRUN}" -eq 1 ]; then + echo >&2 " >> IMPORTANT << " + echo >&2 " Please make sure your system is up to date" + echo >&2 " by running: ${sudo} zypper update " + echo >&2 + fi + + local opts="--ignore-unknown" + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + # http://unix.stackexchange.com/questions/82016/how-to-use-zypper-in-bash-scripts-for-someone-coming-from-apt-get + opts="${opts} --non-interactive" + fi + + read -r -a zypper_opts <<< "$opts" + + # install the required packages + run ${sudo} zypper "${zypper_opts[@]}" install "${@}" +} + +# ----------------------------------------------------------------------------- +# clearlinux + +validate_install_swupd() { + swupd bundle-list | grep -q "${*}" || echo "${*}" +} + +install_swupd() { + # download the latest package info + if [ "${DRYRUN}" -eq 1 ]; then + echo >&2 " >> IMPORTANT << " + echo >&2 " Please make sure your system is up to date" + echo >&2 " by running: ${sudo} swupd update " + echo >&2 + fi + + run ${sudo} swupd bundle-add "${@}" +} + +# ----------------------------------------------------------------------------- +# macOS + +validate_install_pkg() { + pkg query %n-%v | grep -q "${*}" || echo "${*}" +} + +validate_install_brew() { + brew list | grep -q "${*}" || echo "${*}" +} + +install_pkg() { + # download the latest package info + if [ "${DRYRUN}" -eq 1 ]; then + echo >&2 " >> IMPORTANT << " + echo >&2 " Please make sure your system is up to date" + echo >&2 " by running: pkg update " + echo >&2 + fi + + local opts= + if [ "${NON_INTERACTIVE}" -eq 1 ]; then + echo >&2 "Running in non-interactive mode" + opts="-y" + fi + + read -r -a pkg_opts <<< "${opts}" + + run ${sudo} pkg install "${pkg_opts[@]}" "${@}" +} + +install_brew() { + # download the latest package info + if [ "${DRYRUN}" -eq 1 ]; then + echo >&2 " >> IMPORTANT << " + echo >&2 " Please make sure your system is up to date" + echo >&2 " by running: brew upgrade " + echo >&2 + fi + + run brew install "${@}" +} + +# ----------------------------------------------------------------------------- + +install_failed() { + local ret="${1}" + cat << EOF + + + +We are very sorry! + +Installation of required packages failed. + +What to do now: + + 1. Make sure your system is updated. + Most of the times, updating your system will resolve the issue. + + 2. If the error message is about a specific package, try removing + that package from the command and run it again. + Depending on the broken package, you may be able to continue. + + 3. Let us know. We may be able to help. + Open a github issue with the above log, at: + + https://github.com/netdata/netdata/issues + + +EOF + remote_log "FAILED" "${ret}" + exit 1 +} + +remote_log() { + # log success or failure on our system + # to help us solve installation issues + curl > /dev/null 2>&1 -Ss --max-time 3 "https://registry.my-netdata.io/log/installer?status=${1}&error=${2}&distribution=${distribution}&version=${version}&installer=${package_installer}&tree=${tree}&detection=${detection}&netdata=${PACKAGES_NETDATA}&python=${PACKAGES_NETDATA_PYTHON}&python3=${PACKAGES_NETDATA_PYTHON3}&pymongo=${PACKAGES_NETDATA_PYTHON_MONGO}&sensors=${PACKAGES_NETDATA_SENSORS}&database=${PACKAGES_NETDATA_DATABASE}&ebpf=${PACKAGES_NETDATA_EBPF}&firehol=${PACKAGES_FIREHOL}&fireqos=${PACKAGES_FIREQOS}&iprange=${PACKAGES_IPRANGE}&update_ipsets=${PACKAGES_UPDATE_IPSETS}&demo=${PACKAGES_NETDATA_DEMO_SITE}" +} + +if [ -z "${1}" ]; then + usage + exit 1 +fi + +pv=$(python --version 2>&1) +if [ "${tree}" = macos ]; then + pv=3 +elif [[ "${pv}" =~ ^Python\ 2.* ]]; then + pv=2 +elif [[ "${pv}" =~ ^Python\ 3.* ]]; then + pv=3 +elif [[ "${tree}" == "centos" ]] && [ "${version}" -lt 8 ]; then + pv=2 +else + pv=3 +fi + +# parse command line arguments +DONT_WAIT=0 +NON_INTERACTIVE=0 +IGNORE_INSTALLED=0 +while [ -n "${1}" ]; do + case "${1}" in + distribution) + distribution="${2}" + shift + ;; + + version) + version="${2}" + shift + ;; + + codename) + codename="${2}" + shift + ;; + + installer) + check_package_manager "${2}" || exit 1 + shift + ;; + + dont-wait | --dont-wait | -n) + DONT_WAIT=1 + ;; + + non-interactive | --non-interactive | -y) + NON_INTERACTIVE=1 + ;; + + ignore-installed | --ignore-installed | -i) + IGNORE_INSTALLED=1 + ;; + + netdata-all) + PACKAGES_NETDATA=1 + if [ "${pv}" -eq 2 ]; then + PACKAGES_NETDATA_PYTHON=1 + PACKAGES_NETDATA_PYTHON_MONGO=1 + else + PACKAGES_NETDATA_PYTHON3=1 + PACKAGES_NETDATA_PYTHON3_MONGO=1 + fi + PACKAGES_NETDATA_SENSORS=1 + PACKAGES_NETDATA_DATABASE=1 + PACKAGES_NETDATA_EBPF=1 + ;; + + netdata) + PACKAGES_NETDATA=1 + PACKAGES_NETDATA_PYTHON3=1 + PACKAGES_NETDATA_DATABASE=1 + PACKAGES_NETDATA_EBPF=1 + ;; + + python | netdata-python) + PACKAGES_NETDATA_PYTHON=1 + ;; + + python3 | netdata-python3) + PACKAGES_NETDATA_PYTHON3=1 + ;; + + python-pymongo) + if [ "${pv}" -eq 2 ]; then + PACKAGES_NETDATA_PYTHON=1 + PACKAGES_NETDATA_PYTHON_MONGO=1 + else + PACKAGES_NETDATA_PYTHON3=1 + PACKAGES_NETDATA_PYTHON3_MONGO=1 + fi + ;; + + sensors | netdata-sensors) + PACKAGES_NETDATA=1 + PACKAGES_NETDATA_PYTHON3=1 + PACKAGES_NETDATA_SENSORS=1 + PACKAGES_NETDATA_DATABASE=1 + ;; + + firehol | update-ipsets | firehol-all | fireqos) + PACKAGES_IPRANGE=1 + PACKAGES_FIREHOL=1 + PACKAGES_FIREQOS=1 + PACKAGES_IPRANGE=1 + PACKAGES_UPDATE_IPSETS=1 + ;; + + demo | all) + PACKAGES_NETDATA=1 + if [ "${pv}" -eq 2 ]; then + PACKAGES_NETDATA_PYTHON=1 + PACKAGES_NETDATA_PYTHON_MONGO=1 + else + PACKAGES_NETDATA_PYTHON3=1 + PACKAGES_NETDATA_PYTHON3_MONGO=1 + fi + PACKAGES_DEBUG=1 + PACKAGES_IPRANGE=1 + PACKAGES_FIREHOL=1 + PACKAGES_FIREQOS=1 + PACKAGES_UPDATE_IPSETS=1 + PACKAGES_NETDATA_DEMO_SITE=1 + PACKAGES_NETDATA_DATABASE=1 + PACKAGES_NETDATA_EBPF=1 + ;; + + help | -h | --help) + usage + exit 1 + ;; + + *) + echo >&2 "ERROR: Cannot understand option '${1}'" + echo >&2 + usage + exit 1 + ;; + esac + shift +done + +# Check for missing core commands like grep, warn the user to install it and bail out cleanly +if ! command -v grep > /dev/null 2>&1; then + echo >&2 + echo >&2 "ERROR: 'grep' is required for the install to run correctly and was not found on the system." + echo >&2 "Please install grep and run the installer again." + echo >&2 + exit 1 +fi + +if [ -z "${package_installer}" ] || [ -z "${tree}" ]; then + if [ -z "${distribution}" ]; then + # we dont know the distribution + autodetect_distribution || user_picks_distribution + fi + + # When no package installer is detected, try again from distro info if any + if [ -z "${package_installer}" ]; then + detect_package_manager_from_distribution "${distribution}" + fi + + # Validate package manager trees + validate_package_trees +fi + +[ "${detection}" = "/etc/os-release" ] && cat << EOF + +/etc/os-release information: +NAME : ${NAME} +VERSION : ${VERSION} +ID : ${ID} +ID_LIKE : ${ID_LIKE} +VERSION_ID : ${VERSION_ID} +EOF + +cat << EOF + +We detected these: +Distribution : ${distribution} +Version : ${version} +Codename : ${codename} +Package Manager : ${package_installer} +Packages Tree : ${tree} +Detection Method: ${detection} +Default Python v: ${pv} $([ ${pv} -eq 2 ] && [ "${PACKAGES_NETDATA_PYTHON3}" -eq 1 ] && echo "(will install python3 too)") + +EOF + +mapfile -t PACKAGES_TO_INSTALL < <(packages | sort -u) + +if [ ${#PACKAGES_TO_INSTALL[@]} -gt 0 ]; then + echo >&2 + echo >&2 "The following command will be run:" + echo >&2 + DRYRUN=1 + "${package_installer}" "${PACKAGES_TO_INSTALL[@]}" + DRYRUN=0 + echo >&2 + echo >&2 + + if [ "${DONT_WAIT}" -eq 0 ] && [ "${NON_INTERACTIVE}" -eq 0 ]; then + read -r -p "Press ENTER to run it > " || exit 1 + fi + + "${package_installer}" "${PACKAGES_TO_INSTALL[@]}" || install_failed $? + + echo >&2 + echo >&2 "All Done! - Now proceed to the next step." + echo >&2 + +else + echo >&2 + echo >&2 "All required packages are already installed. Now proceed to the next step." + echo >&2 +fi + +remote_log "OK" + +exit 0 diff --git a/packaging/installer/kickstart-ng.sh b/packaging/installer/kickstart-ng.sh new file mode 120000 index 0000000..71d605e --- /dev/null +++ b/packaging/installer/kickstart-ng.sh @@ -0,0 +1 @@ +kickstart.sh
\ No newline at end of file diff --git a/packaging/installer/kickstart-static64.sh b/packaging/installer/kickstart-static64.sh new file mode 120000 index 0000000..71d605e --- /dev/null +++ b/packaging/installer/kickstart-static64.sh @@ -0,0 +1 @@ +kickstart.sh
\ No newline at end of file diff --git a/packaging/installer/kickstart.sh b/packaging/installer/kickstart.sh new file mode 100755 index 0000000..295fcdc --- /dev/null +++ b/packaging/installer/kickstart.sh @@ -0,0 +1,2278 @@ +#!/bin/sh +# +# SPDX-License-Identifier: GPL-3.0-or-later +# +# Next unused error code: F050D + +# ====================================================================== +# Constants + +AGENT_BUG_REPORT_URL="https://github.com/netdata/netdata/issues/new/choose" +CLOUD_BUG_REPORT_URL="https://github.com/netdata/netdata-cloud/issues/new/choose" +DEFAULT_RELEASE_CHANNEL="nightly" +DISCORD_INVITE="https://discord.gg/5ygS846fR6" +DISCUSSIONS_URL="https://github.com/netdata/netdata/discussions" +DOCS_URL="https://learn.netdata.cloud/docs/" +FORUM_URL="https://community.netdata.cloud/" +KICKSTART_OPTIONS="${*}" +KICKSTART_SOURCE="$( + self=${0} + while [ -L "${self}" ] + do + cd "${self%/*}" || exit 1 + self=$(readlink "${self}") + done + cd "${self%/*}" || exit 1 + echo "$(pwd -P)/${self##*/}" +)" +PACKAGES_SCRIPT="https://raw.githubusercontent.com/netdata/netdata/master/packaging/installer/install-required-packages.sh" +PATH="${PATH}:/usr/local/bin:/usr/local/sbin" +PUBLIC_CLOUD_URL="https://app.netdata.cloud" +REPOCONFIG_URL_PREFIX="https://packagecloud.io/netdata/netdata-repoconfig/packages" +REPOCONFIG_VERSION="1-2" +START_TIME="$(date +%s)" +STATIC_INSTALL_ARCHES="x86_64 armv7l aarch64 ppc64le" +TELEMETRY_URL="https://posthog.netdata.cloud/capture/" + +# ====================================================================== +# Defaults for environment variables + +DRY_RUN=0 +SELECTED_INSTALL_METHOD="none" +INSTALL_TYPE="unknown" +INSTALL_PREFIX="" +NETDATA_AUTO_UPDATES="default" +NETDATA_CLAIM_ONLY=0 +NETDATA_CLAIM_URL="api.netdata.cloud" +NETDATA_COMMAND="default" +NETDATA_DISABLE_CLOUD=0 +NETDATA_ONLY_BUILD=0 +NETDATA_ONLY_NATIVE=0 +NETDATA_ONLY_STATIC=0 +NETDATA_OFFLINE_INSTALL_SOURCE="" +NETDATA_REQUIRE_CLOUD=1 +NETDATA_WARNINGS="" +RELEASE_CHANNEL="default" + +if [ -n "$DISABLE_TELEMETRY" ]; then + NETDATA_DISABLE_TELEMETRY="${DISABLE_TELEMETRY}" +elif [ -n "$DO_NOT_TRACK" ]; then + NETDATA_DISABLE_TELEMETRY="${DO_NOT_TRACK}" +else + NETDATA_DISABLE_TELEMETRY=0 +fi + +NETDATA_TARBALL_BASEURL="${NETDATA_TARBALL_BASEURL:-https://storage.googleapis.com/netdata-nightlies}" +NETDATA_INSTALLER_OPTIONS="${NETDATA_INSTALLER_OPTIONS:-""}" +TELEMETRY_API_KEY="${NETDATA_POSTHOG_API_KEY:-mqkwGT0JNFqO-zX2t0mW6Tec9yooaVu7xCBlXtHnt5Y}" + +if echo "${0}" | grep -q 'kickstart-static64'; then + NETDATA_ONLY_STATIC=1 +fi + +if [ ! -t 1 ]; then + INTERACTIVE=0 +else + INTERACTIVE=1 +fi + +# ====================================================================== +# Shared messages used in multiple places throughout the script. + +BADCACHE_MSG="Usually this is a result of an older copy of the file being cached somewhere upstream and can be resolved by retrying in an hour" +BADNET_MSG="This is usually a result of a networking issue" +ERROR_F0003="Could not find a usable HTTP client. Either curl or wget is required to proceed with installation." + +# ====================================================================== +# Core program logic + +main() { + case "${ACTION}" in + uninstall) + uninstall + printf >&2 "Finished uninstalling the Netdata Agent." + deferred_warnings + cleanup + trap - EXIT + exit 0 + ;; + reinstall-clean) + NEW_INSTALL_PREFIX="${INSTALL_PREFIX}" + uninstall + cleanup + + ACTION= + INSTALL_PREFIX="${NEW_INSTALL_PREFIX}" + # shellcheck disable=SC2086 + main + + trap - EXIT + exit 0 + ;; + prepare-offline) + prepare_offline_install_source "${OFFLINE_TARGET}" + deferred_warnings + trap - EXIT + exit 0 + ;; + esac + + set_tmpdir + + if [ -n "${INSTALL_VERSION}" ]; then + if echo "${INSTALL_VERSION}" | grep -E -o "^[[:digit:]]+\.[[:digit:]]+\.[[:digit:]]+$" > /dev/null 2>&1; then + NEW_SELECTED_RELEASE_CHANNEL="stable" + else + NEW_SELECTED_RELEASE_CHANNEL="nightly" + fi + + if ! [ "${NEW_SELECTED_RELEASE_CHANNEL}" = "${SELECTED_RELEASE_CHANNEL}" ]; then + warning "Selected release channel does not match this version and it will be changed automatically." + SELECTED_RELEASE_CHANNEL="${NEW_SELECTED_RELEASE_CHANNEL}" + fi + fi + + case "${SYSTYPE}" in + Linux) install_on_linux ;; + Darwin) install_on_macos ;; + FreeBSD) install_on_freebsd ;; + esac + + if [ -n "${NETDATA_CLAIM_TOKEN}" ]; then + claim + elif [ "${NETDATA_DISABLE_CLOUD}" -eq 1 ]; then + soft_disable_cloud + fi + + set_auto_updates + + printf >&2 "%s\n\n" "Successfully installed the Netdata Agent." + deferred_warnings + success_banner + telemetry_event INSTALL_SUCCESS "" "" + cleanup + trap - EXIT +} + +# ====================================================================== +# Usage info + +usage() { + cat << HEREDOC +USAGE: kickstart.sh [options] + where options include: + + --non-interactive Do not prompt for user input. (default: prompt if there is a controlling terminal) + --interactive Prompt for user input even if there is no controlling terminal. + --dont-start-it Do not start the agent by default (only for static installs or local builds) + --dry-run Report what we would do with the given options on this system, but don’t actually do anything. + --release-channel Specify the release channel to use for the install (default: ${DEFAULT_RELEASE_CHANNEL}) + --stable-channel Equivalent to "--release-channel stable" + --nightly-channel Equivalent to "--release-channel nightly" + --no-updates Do not enable automatic updates (default: enable automatic updates using the best supported scheduling method) + --auto-update Enable automatic updates. + --auto-update-type Specify a particular scheduling type for auto-updates (valid types: systemd, interval, crontab) + --disable-telemetry Opt-out of anonymous statistics. + --repositories-only Only install appropriate repository configuration packages (only for native install). + --native-only Only install if native binary packages are available. + --static-only Only install if a static build is available. + --build-only Only install using a local build. + --reinstall Explicitly reinstall instead of updating any existing install. + --reinstall-even-if-unsafe Even try to reinstall if we don't think we can do so safely (implies --reinstall). + --disable-cloud Disable support for Netdata Cloud (default: detect) + --require-cloud Only install if Netdata Cloud can be enabled. Overrides --disable-cloud. + --install <path> This option is deprecated and will be removed in a future version, use --install-prefix instead. + --install-prefix <path> Specify an installation prefix for local builds (default: autodetect based on system type). + --old-install-prefix <path> Specify an old local builds installation prefix for uninstall/reinstall (if it's not default). + --install-version <version> Specify the version of Netdata to install. + --claim-token Use a specified token for claiming to Netdata Cloud. + --claim-rooms When claiming, add the node to the specified rooms. + --claim-only If there is an existing install, only try to claim it, not update it. + --claim-* Specify other options for the claiming script. + --no-cleanup Don't do any cleanup steps. This is intended to help with debugging the installer. + --uninstall Uninstall an existing installation of Netdata. + --reinstall-clean Clean reinstall Netdata. + --local-build-options Specify additional options to pass to the installer code when building locally. Only valid if --build-only is also specified. + --static-install-options Specify additional options to pass to the static installer code. Only valid if --static-only is also specified. + --prepare-offline-install-source Instead of installing the agent, prepare a directory that can be used to install on another system without needing to download anything. + +Additionally, this script may use the following environment variables: + + TMPDIR: Used to specify where to put temporary files. On most systems, the default we select + automatically should be fine. The user running the script needs to both be able to + write files to the temporary directory, and run files from that location. + ROOTCMD: Used to specify a command to use to run another command with root privileges if needed. By + default we try to use sudo, doas, or pkexec (in that order of preference), but if + you need special options for one of those to work, or have a different tool to do + the same thing on your system, you can specify it here. + DISABLE_TELEMETRY If set to a value other than 0, behave as if \`--disable-telemetry\` was specified. + +HEREDOC +} + +# ====================================================================== +# Telemetry functions + +telemetry_event() { + if [ "${NETDATA_DISABLE_TELEMETRY}" -eq 1 ] || [ "${DRY_RUN}" -eq 1 ]; then + return 0 + fi + + now="$(date +%s)" + total_duration="$((now - START_TIME))" + + if [ -e "/etc/os-release" ]; then + eval "$(grep -E "^(NAME|ID|ID_LIKE|VERSION|VERSION_ID)=" < /etc/os-release | sed 's/^/HOST_/')" + fi + + if [ -z "${HOST_NAME}" ] || [ -z "${HOST_VERSION}" ] || [ -z "${HOST_ID}" ]; then + if [ -f "/etc/lsb-release" ]; then + DISTRIB_ID="unknown" + DISTRIB_RELEASE="unknown" + DISTRIB_CODENAME="unknown" + eval "$(grep -E "^(DISTRIB_ID|DISTRIB_RELEASE|DISTRIB_CODENAME)=" < /etc/lsb-release)" + if [ -z "${HOST_NAME}" ]; then HOST_NAME="${DISTRIB_ID}"; fi + if [ -z "${HOST_VERSION}" ]; then HOST_VERSION="${DISTRIB_RELEASE}"; fi + if [ -z "${HOST_ID}" ]; then HOST_ID="${DISTRIB_CODENAME}"; fi + fi + fi + + KERNEL_NAME="$(uname -s)" + + if [ "${KERNEL_NAME}" = FreeBSD ]; then + TOTAL_RAM="$(sysctl -n hw.physmem)" + elif [ "${KERNEL_NAME}" = Darwin ]; then + TOTAL_RAM="$(sysctl -n hw.memsize)" + elif [ -r /proc/meminfo ]; then + TOTAL_RAM="$(grep -F MemTotal /proc/meminfo | cut -f 2 -d ':' | sed -e 's/^[[:space:]]*//' -e 's/[[:space:]]*$//' | cut -f 1 -d ' ')" + TOTAL_RAM="$((TOTAL_RAM * 1024))" + fi + + if [ "${KERNEL_NAME}" = Darwin ] && command -v ioreg >/dev/null 2>&1; then + DISTINCT_ID="macos-$(ioreg -rd1 -c IOPlatformExpertDevice | awk '/IOPlatformUUID/ { split($0, line, "\""); printf("%s\n", line[4]); }')" + elif [ -f /etc/machine-id ]; then + DISTINCT_ID="machine-$(cat /etc/machine-id)" + elif [ -f /var/db/dbus/machine-id ]; then + DISTINCT_ID="dbus-$(cat /var/db/dbus/machine-id)" + elif [ -f /var/lib/dbus/machine-id ]; then + DISTINCT_ID="dbus-$(cat /var/lib/dbus/machine-id)" + elif command -v uuidgen > /dev/null 2>&1; then + DISTINCT_ID="uuid-$(uuidgen | tr '[:upper:]' '[:lower:]')" + else + DISTINCT_ID="null" + fi + + REQ_BODY="$(cat << EOF +{ + "api_key": "${TELEMETRY_API_KEY}", + "event": "${1}", + "properties": { + "distinct_id": "${DISTINCT_ID}", + "event_source": "agent installer", + "\$current_url": "agent installer", + "\$pathname": "netdata-installer", + "\$host": "installer.netdata.io", + "\$ip": "127.0.0.1", + "script_variant": "kickstart-ng", + "error_code": "${3}", + "error_message": "${2}", + "install_options": "${KICKSTART_OPTIONS}", + "install_interactivity": "${INTERACTIVE}", + "install_auto_updates": "${NETDATA_AUTO_UPDATES}", + "install_command": "${NETDATA_COMMAND}", + "total_runtime": "${total_duration}", + "selected_install_method": "${SELECTED_INSTALL_METHOD}", + "netdata_release_channel": "${RELEASE_CHANNEL:-null}", + "netdata_install_type": "${INSTALL_TYPE}", + "host_os_name": "${HOST_NAME:-unknown}", + "host_os_id": "${HOST_ID:-unknown}", + "host_os_id_like": "${HOST_ID_LIKE:-unknown}", + "host_os_version": "${HOST_VERSION:-unknown}", + "host_os_version_id": "${HOST_VERSION_ID:-unknown}", + "system_kernel_name": "${KERNEL_NAME}", + "system_kernel_version": "$(uname -r)", + "system_architecture": "$(uname -m)", + "system_total_ram": "${TOTAL_RAM:-unknown}" + } +} +EOF +)" + + if command -v curl > /dev/null 2>&1; then + curl --silent -o /dev/null -X POST --max-time 2 --header "Content-Type: application/json" -d "${REQ_BODY}" "${TELEMETRY_URL}" > /dev/null + elif command -v wget > /dev/null 2>&1; then + wget -q -O - --no-check-certificate \ + --method POST \ + --timeout=1 \ + --header 'Content-Type: application/json' \ + --body-data "${REQ_BODY}" \ + "${TELEMETRY_URL}" > /dev/null + fi +} + +trap_handler() { + code="${1}" + lineno="${2}" + + deferred_warnings + + printf >&2 "%s\n\n" "${TPUT_BGRED}${TPUT_WHITE}${TPUT_BOLD} ERROR ${TPUT_RESET} Installer exited unexpectedly (${code}-${lineno})" + + case "${code}" in + 0) + printf >&2 "%s\n" "This is almost certainly the result of a bug. If you have time, please report it at ${AGENT_BUG_REPORT_URL}." + ;; + *) + printf >&2 "%s\n" "This is probably a result of a transient issue on your system. Things should work correctly if you try again." + printf >&2 "%s\n" "If you continue to experience this issue, you can reacn out to us for support on:" + support_list + ;; + esac + + telemetry_event INSTALL_CRASH "Installer exited unexpectedly (${code}-${lineno})" "E${code}-${lineno}" + + trap - EXIT + + cleanup + + exit 1 +} + +trap 'trap_handler 0 ${LINENO}' EXIT +trap 'trap_handler 1 0' HUP +trap 'trap_handler 2 0' INT +trap 'trap_handler 3 0' QUIT +trap 'trap_handler 13 0' PIPE +trap 'trap_handler 15 0' TERM + +# ====================================================================== +# Utility functions + +setup_terminal() { + TPUT_RESET="" + TPUT_WHITE="" + TPUT_BGRED="" + TPUT_BGGREEN="" + TPUT_BOLD="" + TPUT_DIM="" + + # Is stderr on the terminal? If not, then fail + test -t 2 || return 1 + + if command -v tput > /dev/null 2>&1; then + if num_colors=$(tput colors 2> /dev/null) && [ "${num_colors:-0}" -ge 8 ]; then + # Enable colors + TPUT_RESET="$(tput sgr 0)" + TPUT_WHITE="$(tput setaf 7)" + TPUT_BGRED="$(tput setab 1)" + TPUT_BGGREEN="$(tput setab 2)" + TPUT_BOLD="$(tput bold)" + TPUT_DIM="$(tput dim)" + fi + fi + + echo "${TPUT_RESET}" + + return 0 +} + +support_list() { + printf >&2 "%s\n" " - GitHub: ${DISCUSSIONS_URL}" + printf >&2 "%s\n" " - Discord: ${DISCORD_INVITE}" + printf >&2 "%s\n" " - Our community forums: ${FORUM_URL}" +} + +success_banner() { + printf >&2 "%s\n\n" "Official documentation can be found online at ${DOCS_URL}." + + if [ -z "${CLAIM_TOKEN}" ]; then + printf >&2 "%s\n\n" "Looking to monitor all of your infrastructure with Netdata? Check out Netdata Cloud at ${PUBLIC_CLOUD_URL}." + fi + + printf >&2 "%s\n" "Join our community and connect with us on:" + support_list +} + +cleanup() { + if [ -z "${NO_CLEANUP}" ] && [ -n "${tmpdir}" ]; then + cd || true + ${ROOTCMD} rm -rf "${tmpdir}" + fi +} + +deferred_warnings() { + if [ -n "${NETDATA_WARNINGS}" ]; then + printf >&2 "%s\n" "The following non-fatal warnings or errors were encountered:" + # shellcheck disable=SC2059 + printf >&2 "${NETDATA_WARNINGS}" + printf >&2 "\n\n" + fi +} + +fatal() { + deferred_warnings + printf >&2 "%s\n\n" "${TPUT_BGRED}${TPUT_WHITE}${TPUT_BOLD} ABORTED ${TPUT_RESET} ${1}" + printf >&2 "%s\n" "For community support, you can connect with us on:" + support_list + telemetry_event "INSTALL_FAILED" "${1}" "${2}" + cleanup + trap - EXIT + exit 1 +} + +ESCAPED_PRINT_METHOD= +# shellcheck disable=SC3050 +if printf "%s " test > /dev/null 2>&1; then + ESCAPED_PRINT_METHOD="printfq" +fi + +escaped_print() { + if [ "${ESCAPED_PRINT_METHOD}" = "printfq" ]; then + # shellcheck disable=SC3050 + printf "%s " "${@}" + else + printf "%s" "${*}" + fi + return 0 +} + +progress() { + echo >&2 " --- ${TPUT_BOLD}${*}${TPUT_RESET} --- " +} + +run_logfile="/dev/null" +run() { + user="${USER--}" + dir="${PWD}" + + if [ "$(id -u)" = "0" ]; then + info="[root ${dir}]# " + info_console="[${TPUT_DIM}${dir}${TPUT_RESET}]# " + else + info="[${user} ${dir}]$ " + info_console="[${TPUT_DIM}${dir}${TPUT_RESET}]$ " + fi + + if [ "${DRY_RUN}" -eq 1 ]; then + printf >&2 "%s" "Would run command:\n" + fi + + { + printf "%s" "${info}" + escaped_print "${@}" + printf " ... " + } >> "${run_logfile}" + + printf >&2 "%s" "${info_console}${TPUT_BOLD}" + escaped_print >&2 "${@}" + printf >&2 "%s\n" "${TPUT_RESET}" + + if [ "${DRY_RUN}" -ne 1 ]; then + "${@}" + ret=$? + else + ret=0 + fi + + if [ ${ret} -ne 0 ]; then + printf >&2 "%s\n\n" "${TPUT_BGRED}${TPUT_WHITE}${TPUT_BOLD} FAILED ${TPUT_RESET}" + printf "%s\n" "FAILED with exit code ${ret}" >> "${run_logfile}" + # shellcheck disable=SC2089 + NETDATA_WARNINGS="${NETDATA_WARNINGS}\n - Command \"${*}\" failed with exit code ${ret}." + else + printf >&2 "%s\n\n" "${TPUT_BGGREEN}${TPUT_WHITE}${TPUT_BOLD} OK ${TPUT_RESET}" + printf "OK\n" >> "${run_logfile}" + fi + + return ${ret} +} + +run_script() { + set_tmpdir + + export NETDATA_SCRIPT_STATUS_PATH="${tmpdir}/.script-status" + + export NETDATA_SAVE_WARNINGS=1 + export NETDATA_PROPAGATE_WARNINGS=1 + # shellcheck disable=SC2090 + export NETDATA_WARNINGS="${NETDATA_WARNINGS}" + + # shellcheck disable=SC2086 + run ${ROOTCMD} "${@}" + + if [ -r "${NETDATA_SCRIPT_STATUS_PATH}" ]; then + # shellcheck disable=SC1090 + . "${NETDATA_SCRIPT_STATUS_PATH}" + rm -f "${NETDATA_SCRIPT_STATUS_PATH}" + fi +} + +warning() { + printf >&2 "%s\n\n" "${TPUT_BGRED}${TPUT_WHITE}${TPUT_BOLD} WARNING ${TPUT_RESET} ${*}" + NETDATA_WARNINGS="${NETDATA_WARNINGS}\n - ${*}" +} + +_cannot_use_tmpdir() { + testfile="$(TMPDIR="${1}" mktemp -q -t netdata-test.XXXXXXXXXX)" + ret=0 + + if [ -z "${testfile}" ]; then + return "${ret}" + fi + + if printf '#!/bin/sh\necho SUCCESS\n' > "${testfile}"; then + if chmod +x "${testfile}"; then + if [ "$("${testfile}")" = "SUCCESS" ]; then + ret=1 + fi + fi + fi + + rm -f "${testfile}" + return "${ret}" +} + +create_tmp_directory() { + if [ -z "${TMPDIR}" ] || _cannot_use_tmpdir "${TMPDIR}"; then + if _cannot_use_tmpdir /tmp; then + if _cannot_use_tmpdir "${PWD}"; then + fatal "Unable to find a usable temporary directory. Please set \$TMPDIR to a path that is both writable and allows execution of files and try again." F0400 + else + TMPDIR="${PWD}" + fi + else + TMPDIR="/tmp" + fi + fi + + mktemp -d -t netdata-kickstart-XXXXXXXXXX +} + +set_tmpdir() { + if [ -z "${tmpdir}" ] || [ ! -d "${tmpdir}" ]; then + tmpdir="$(create_tmp_directory)" + progress "Using ${tmpdir} as a temporary directory." + cd "${tmpdir}" || fatal "Failed to change current working directory to ${tmpdir}." F000A + fi +} + +check_for_remote_file() { + url="${1}" + + if echo "${url}" | grep -Eq "^file:///"; then + [ -e "${url#file://}" ] || return 1 + elif command -v curl > /dev/null 2>&1; then + curl --output /dev/null --silent --head --fail "${url}" || return 1 + elif command -v wget > /dev/null 2>&1; then + wget -S --spider "${url}" 2>&1 | grep -q 'HTTP/1.1 200 OK' || return 1 + else + fatal "${ERROR_F0003}" F0003 + fi +} + +download() { + url="${1}" + dest="${2}" + + if echo "${url}" | grep -Eq "^file:///"; then + run cp "${url#file://}" "${dest}" || return 1 + elif command -v curl > /dev/null 2>&1; then + run curl --fail -q -sSL --connect-timeout 10 --retry 3 --output "${dest}" "${url}" || return 1 + elif command -v wget > /dev/null 2>&1; then + run wget -T 15 -O "${dest}" "${url}" || return 1 + else + fatal "${ERROR_F0003}" F0003 + fi +} + +get_redirect() { + url="${1}" + + if command -v curl > /dev/null 2>&1; then + run sh -c "curl ${url} -s -L -I -o /dev/null -w '%{url_effective}' | grep -o '[^/]*$'" || return 1 + elif command -v wget > /dev/null 2>&1; then + run sh -c "wget --max-redirect=0 ${url} 2>&1 | grep Location | cut -d ' ' -f2 | grep -o '[^/]*$'" || return 1 + else + fatal "${ERROR_F0003}" F0003 + fi +} + +safe_sha256sum() { + # Within the context of the installer, we only use -c option that is common between the two commands + # We will have to reconsider if we start using non-common options + if command -v shasum > /dev/null 2>&1; then + shasum -a 256 "$@" + elif command -v sha256sum > /dev/null 2>&1; then + sha256sum "$@" + else + fatal "Could not find a usable checksum tool. Either sha256sum, or a version of shasum supporting SHA256 checksums is required to proceed with installation." F0004 + fi +} + +get_system_info() { + case "$(uname -s)" in + Linux) + SYSTYPE="Linux" + + os_release_file= + if [ -s "/etc/os-release" ] && [ -r "/etc/os-release" ]; then + os_release_file="/etc/os-release" + elif [ -s "/usr/lib/os-release" ] && [ -r "/usr/lib/os-release" ]; then + os_release_file="/usr/lib/os-release" + else + warning "Cannot find usable OS release information. Native packages will not be available for this install." + fi + + if [ -n "${os_release_file}" ]; then + # shellcheck disable=SC1090 + . "${os_release_file}" + + DISTRO="${ID}" + SYSVERSION="${VERSION_ID}" + SYSCODENAME="${VERSION_CODENAME}" + SYSARCH="$(uname -m)" + + supported_compat_names="debian ubuntu centos fedora opensuse ol arch" + + if str_in_list "${DISTRO}" "${supported_compat_names}"; then + DISTRO_COMPAT_NAME="${DISTRO}" + else + case "${DISTRO}" in + opensuse-leap) + DISTRO_COMPAT_NAME="opensuse" + ;; + cloudlinux|almalinux|rocky|rhel) + DISTRO_COMPAT_NAME="centos" + ;; + artix|manjaro|obarun) + DISTRO_COMPAT_NAME="arch" + ;; + *) + DISTRO_COMPAT_NAME="unknown" + ;; + esac + fi + + case "${DISTRO_COMPAT_NAME}" in + centos|ol) + SYSVERSION=$(echo "$SYSVERSION" | cut -d'.' -f1) + ;; + esac + else + DISTRO="unknown" + DISTRO_COMPAT_NAME="unknown" + SYSVERSION="unknown" + SYSCODENAME="unknown" + SYSARCH="$(uname -m)" + fi + ;; + Darwin) + SYSTYPE="Darwin" + SYSVERSION="$(sw_vers -buildVersion)" + SYSARCH="$(uname -m)" + ;; + FreeBSD) + SYSTYPE="FreeBSD" + SYSVERSION="$(uname -K)" + SYSARCH="$(uname -m)" + ;; + *) + fatal "Unsupported system type detected. Netdata cannot be installed on this system using this script." F0200 + ;; + esac +} + +str_in_list() { + printf "%s\n" "${2}" | tr ' ' "\n" | grep -qE "^${1}\$" + return $? +} + +confirm_root_support() { + if [ "$(id -u)" -ne "0" ]; then + if [ -z "${ROOTCMD}" ] && command -v sudo > /dev/null; then + if [ "${INTERACTIVE}" -eq 0 ]; then + ROOTCMD="sudo -n" + else + ROOTCMD="sudo" + fi + fi + + if [ -z "${ROOTCMD}" ] && command -v doas > /dev/null; then + if [ "${INTERACTIVE}" -eq 0 ]; then + ROOTCMD="doas -n" + else + ROOTCMD="doas" + fi + fi + + if [ -z "${ROOTCMD}" ] && command -v pkexec > /dev/null; then + ROOTCMD="pkexec" + fi + + if [ -z "${ROOTCMD}" ]; then + fatal "We need root privileges to continue, but cannot find a way to gain them (we support sudo, doas, and pkexec). Either re-run this script as root, or set \$ROOTCMD to a command that can be used to gain root privileges." F0201 + fi + fi +} + +confirm() { + prompt="${1} [y/n]" + + while true; do + echo "${prompt}" + read -r yn + + case "$yn" in + [Yy]*) return 0;; + [Nn]*) return 1;; + *) echo "Please answer yes or no.";; + esac + done +} + +# ====================================================================== +# Existing install handling code + +update() { + updater="${ndprefix}/usr/libexec/netdata/netdata-updater.sh" + + if [ -x "${updater}" ]; then + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would attempt to update existing installation by running the updater script located at: ${updater}" + return 0 + fi + + if [ "${INTERACTIVE}" -eq 0 ]; then + opts="--non-interactive" + else + opts="--interactive" + fi + + if run_script "${updater}" ${opts} --not-running-from-cron; then + progress "Updated existing install at ${ndprefix}" + return 0 + else + if [ -n "${EXIT_REASON}" ]; then + fatal "Failed to update existing Netdata install at ${ndprefix}: ${EXIT_REASON}" "${EXIT_CODE}" + else + fatal "Failed to update existing Netdata install at ${ndprefix}: Encountered an unhandled error in the updater. Further information about this error may be displayed above." U0000 + fi + fi + else + warning "Could not find a usable copy of the updater script. We are unable to update this system in place." + return 1 + fi +} + +uninstall() { + set_tmpdir + get_system_info + detect_existing_install + + if [ -n "${OLD_INSTALL_PREFIX}" ]; then + INSTALL_PREFIX="$(echo "${OLD_INSTALL_PREFIX}/" | sed 's/$/netdata/g')" + else + INSTALL_PREFIX="${ndprefix}" + fi + + uninstaller="${INSTALL_PREFIX}/usr/libexec/netdata/netdata-uninstaller.sh" + uninstaller_url="https://raw.githubusercontent.com/netdata/netdata/master/packaging/installer/netdata-uninstaller.sh" + + if [ $INTERACTIVE = 0 ]; then + FLAGS="--yes --force" + else + FLAGS="--yes" + fi + + if [ -x "${uninstaller}" ]; then + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would attempt to uninstall existing install with uninstaller script found at: ${uninstaller}" + return 0 + else + progress "Found existing netdata-uninstaller. Running it.." + if ! run_script "${uninstaller}" ${FLAGS}; then + warning "Uninstaller failed. Some parts of Netdata may still be present on the system." + fi + fi + else + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would download installer script from: ${uninstaller_url}" + progress "Would attempt to uninstall existing install with downloaded uninstaller script." + return 0 + else + progress "Downloading netdata-uninstaller ..." + download "${uninstaller_url}" "${tmpdir}/netdata-uninstaller.sh" + chmod +x "${tmpdir}/netdata-uninstaller.sh" + if ! run_script "${tmpdir}/netdata-uninstaller.sh" ${FLAGS}; then + warning "Uninstaller failed. Some parts of Netdata may still be present on the system." + fi + fi + fi +} + +detect_existing_install() { + set_tmpdir + + progress "Checking for existing installations of Netdata..." + + if pkg_installed netdata; then + ndprefix="/" + EXISTING_INSTALL_IS_NATIVE="1" + else + EXISTING_INSTALL_IS_NATIVE="0" + if [ -n "${INSTALL_PREFIX}" ]; then + searchpath="${INSTALL_PREFIX}/bin:${INSTALL_PREFIX}/sbin:${INSTALL_PREFIX}/usr/bin:${INSTALL_PREFIX}/usr/sbin:${PATH}" + searchpath="${INSTALL_PREFIX}/netdata/bin:${INSTALL_PREFIX}/netdata/sbin:${INSTALL_PREFIX}/netdata/usr/bin:${INSTALL_PREFIX}/netdata/usr/sbin:${searchpath}" + else + searchpath="${PATH}" + fi + + ndpath="$(PATH="${searchpath}" command -v netdata 2>/dev/null)" + + if [ -z "$ndpath" ] && [ -x /opt/netdata/bin/netdata ]; then + ndpath="/opt/netdata/bin/netdata" + fi + + if [ -n "${ndpath}" ]; then + case "${ndpath}" in + */usr/bin/netdata|*/usr/sbin/netdata) ndprefix="$(dirname "$(dirname "$(dirname "${ndpath}")")")" ;; + *) ndprefix="$(dirname "$(dirname "${ndpath}")")" ;; + esac + fi + + if echo "${ndprefix}" | grep -Eq '^/usr$'; then + ndprefix="$(dirname "${ndprefix}")" + fi + fi + + if [ -n "${ndprefix}" ]; then + typefile="${ndprefix}/etc/netdata/.install-type" + if [ -r "${typefile}" ]; then + ${ROOTCMD} sh -c "cat \"${typefile}\" > \"${tmpdir}/install-type\"" + # shellcheck disable=SC1090,SC1091 + . "${tmpdir}/install-type" + else + INSTALL_TYPE="unknown" + fi + + envfile="${ndprefix}/etc/netdata/.environment" + if [ "${INSTALL_TYPE}" = "unknown" ] || [ "${INSTALL_TYPE}" = "custom" ]; then + if [ -r "${envfile}" ]; then + ${ROOTCMD} sh -c "cat \"${envfile}\" > \"${tmpdir}/environment\"" + # shellcheck disable=SC1091 + . "${tmpdir}/environment" + if [ -n "${NETDATA_IS_STATIC_INSTALL}" ]; then + if [ "${NETDATA_IS_STATIC_INSTALL}" = "yes" ]; then + INSTALL_TYPE="legacy-static" + else + INSTALL_TYPE="legacy-build" + fi + fi + fi + fi + fi +} + +handle_existing_install() { + detect_existing_install + + if [ -z "${ndprefix}" ] || [ -z "${INSTALL_TYPE}" ]; then + progress "No existing installations of netdata found, assuming this is a fresh install." + return 0 + fi + + case "${INSTALL_TYPE}" in + kickstart-*|legacy-*|binpkg-*|manual-static|unknown) + if [ "${INSTALL_TYPE}" = "unknown" ]; then + if [ "${EXISTING_INSTALL_IS_NATIVE}" -eq 1 ]; then + warning "Found an existing netdata install managed by the system package manager, but could not determine the install type. Usually this means you installed an unsupported third-party netdata package." + else + warning "Found an existing netdata install at ${ndprefix}, but could not determine the install type. Usually this means you installed Netdata through your distribution’s regular package repositories or some other unsupported method." + fi + else + progress "Found an existing netdata install at ${ndprefix}, with installation type '${INSTALL_TYPE}'." + fi + + if [ -n "${NETDATA_REINSTALL}" ] || [ -n "${NETDATA_UNSAFE_REINSTALL}" ]; then + progress "Found an existing netdata install at ${ndprefix}, but user requested reinstall, continuing." + + case "${INSTALL_TYPE}" in + binpkg-*) NETDATA_ONLY_NATIVE=1 ;; + *-build) NETDATA_ONLY_BUILD=1 ;; + *-static) NETDATA_ONLY_STATIC=1 ;; + *) + if [ -n "${NETDATA_UNSAFE_REINSTALL}" ]; then + warning "Reinstalling over top of a ${INSTALL_TYPE} installation may be unsafe, but the user has requested we proceed." + elif [ "${INTERACTIVE}" -eq 0 ]; then + fatal "User requested reinstall, but we cannot safely reinstall over top of a ${INSTALL_TYPE} installation, exiting." F0104 + else + if [ "${EXISTING_INSTALL_IS_NATIVE}" ]; then + reinstall_prompt="Reinstalling over top of an existing install managed by the system package manager is known to cause things to break, are you sure you want to continue?" + else + reinstall_prompt="Reinstalling over top of a ${INSTALL_TYPE} installation may be unsafe, do you want to continue?" + fi + + if confirm "${reinstall_prompt}"; then + progress "OK, continuing." + else + fatal "Cancelling reinstallation at user request." F0105 + fi + fi + ;; + esac + + return 0 + elif [ "${INSTALL_TYPE}" = "unknown" ]; then + claimonly_notice="If you just want to claim this install, you should re-run this command with the --claim-only option instead." + if [ "${EXISTING_INSTALL_IS_NATIVE}" -eq 1 ]; then + failmsg="Attempting to update an installation managed by the system package manager is known to not work in most cases. If you are trying to install the latest version of Netdata, you will need to manually uninstall it through your system package manager. ${claimonly_notice}" + promptmsg="Attempting to update an installation managed by the system package manager is known to not work in most cases. If you are trying to install the latest version of Netdata, you will need to manually uninstall it through your system package manager. ${claimonly_notice} Are you sure you want to continue?" + else + failmsg="We do not support trying to update or claim installations when we cannot determine the install type. You will need to uninstall the existing install using the same method you used to install it to proceed. ${claimonly_notice}" + promptmsg="Attempting to update an existing install is not officially supported. It may work, but it also might break your system. ${claimonly_notice} Are you sure you want to continue?" + fi + if [ "${INTERACTIVE}" -eq 0 ] && [ "${NETDATA_CLAIM_ONLY}" -eq 0 ]; then + fatal "${failmsg}" F0106 + elif [ "${INTERACTIVE}" -eq 1 ] && [ "${NETDATA_CLAIM_ONLY}" -eq 0 ]; then + if confirm "${promptmsg}"; then + progress "OK, continuing" + else + fatal "Cancelling update of unknown installation type at user request." F050C + fi + fi + fi + + ret=0 + + if [ "${NETDATA_CLAIM_ONLY}" -eq 0 ]; then + if ! update; then + warning "Failed to update existing Netdata install at ${ndprefix}." + else + progress "Successfully updated existing netdata install at ${ndprefix}." + fi + else + warning "Not updating existing install at ${ndprefix}." + fi + + if [ -n "${NETDATA_CLAIM_TOKEN}" ]; then + progress "Attempting to claim existing install at ${ndprefix}." + INSTALL_PREFIX="${ndprefix}" + claim + ret=$? + elif [ "${NETDATA_CLAIM_ONLY}" -eq 1 ]; then + fatal "User asked to claim, but did not proide a claiming token." F0202 + else + progress "Not attempting to claim existing install at ${ndprefix} (no claiming token provided)." + fi + + deferred_warnings + success_banner + cleanup + trap - EXIT + exit $ret + ;; + oci) + fatal "This is an OCI container, use the regular container lifecycle management commands for your container tools instead of this script for managing it." F0203 + ;; + *) + if [ -n "${NETDATA_REINSTALL}" ] || [ -n "${NETDATA_UNSAFE_REINSTALL}" ]; then + if [ -n "${NETDATA_UNSAFE_REINSTALL}" ]; then + warning "Reinstalling over top of a ${INSTALL_TYPE} installation may be unsafe, but the user has requested we proceed." + elif [ "${INTERACTIVE}" -eq 0 ]; then + fatal "User requested reinstall, but we cannot safely reinstall over top of a ${INSTALL_TYPE} installation, exiting." F0104 + else + if confirm "Reinstalling over top of a ${INSTALL_TYPE} installation may be unsafe, do you want to continue?"; then + progress "OK, continuing." + else + fatal "Cancelling reinstallation at user request." F0105 + fi + fi + else + if [ -n "${NETDATA_CLAIM_TOKEN}" ]; then + progress "Attempting to claim existing install at ${ndprefix}." + INSTALL_PREFIX="${ndprefix}" + claim + ret=$? + + cleanup + trap - EXIT + exit $ret + elif [ "${NETDATA_CLAIM_ONLY}" -eq 1 ]; then + fatal "User asked to claim, but did not proide a claiming token." F0202 + else + fatal "Found an existing netdata install at ${ndprefix}, but the install type is '${INSTALL_TYPE}', which is not supported by this script, refusing to proceed." F0103 + fi + fi + ;; + esac +} + +soft_disable_cloud() { + set_tmpdir + + cloud_prefix="${INSTALL_PREFIX}/var/lib/netdata/cloud.d" + + run ${ROOTCMD} mkdir -p "${cloud_prefix}" + + cat > "${tmpdir}/cloud.conf" << EOF +[global] + enabled = no +EOF + + run ${ROOTCMD} cp "${tmpdir}/cloud.conf" "${cloud_prefix}/cloud.conf" + + if [ -z "${NETDATA_NO_START}" ]; then + case "${SYSTYPE}" in + Darwin) run ${ROOTCMD} launchctl kickstart -k com.github.netdata ;; + FreeBSD) run ${ROOTCMD} service netdata restart ;; + Linux) + initpath="$(${ROOTCMD} readlink /proc/1/exe)" + + if command -v service > /dev/null 2>&1; then + run ${ROOTCMD} service netdata restart + elif command -v rc-service > /dev/null 2>&1; then + run ${ROOTCMD} rc-service netdata restart + elif [ "$(basename "${initpath}" 2> /dev/null)" = "systemd" ]; then + run ${ROOTCMD} systemctl restart netdata + elif [ -f /etc/init.d/netdata ]; then + run ${ROOTCMD} /etc/init.d/netdata restart + fi + ;; + esac + fi +} + +confirm_install_prefix() { + if [ -n "${INSTALL_PREFIX}" ] && [ "${NETDATA_ONLY_BUILD}" -ne 1 ]; then + fatal "The --install-prefix and --install options are only supported together with the --build-only option." F0204 + fi + + if [ -n "${INSTALL_PREFIX}" ]; then + NETDATA_INSTALLER_OPTIONS="${NETDATA_INSTALLER_OPTIONS} --install-prefix ${INSTALL_PREFIX}" + else + case "${SYSTYPE}" in + Darwin) + INSTALL_PREFIX="/usr/local/netdata" + NETDATA_INSTALLER_OPTIONS="${NETDATA_INSTALLER_OPTIONS} --install-no-prefix ${INSTALL_PREFIX}" + ;; + FreeBSD) + INSTALL_PREFIX="/usr/local" + NETDATA_INSTALLER_OPTIONS="${NETDATA_INSTALLER_OPTIONS} --install-no-prefix ${INSTALL_PREFIX}" + ;; + esac + fi +} + +# ====================================================================== +# Claiming support code + +check_claim_opts() { +# shellcheck disable=SC2235,SC2030 + if [ -z "${NETDATA_CLAIM_TOKEN}" ] && [ -n "${NETDATA_CLAIM_ROOMS}" ]; then + fatal "Invalid claiming options, claim rooms may only be specified when a token is specified." F0204 + elif [ -z "${NETDATA_CLAIM_TOKEN}" ] && [ -n "${NETDATA_CLAIM_EXTRA}" ]; then + fatal "Invalid claiming options, a claiming token must be specified." F0204 + elif [ "${NETDATA_DISABLE_CLOUD}" -eq 1 ] && [ -n "${NETDATA_CLAIM_TOKEN}" ]; then + fatal "Cloud explicitly disabled, but automatic claiming requested. Either enable Netdata Cloud, or remove the --claim-* options." F0204 + fi +} + +is_netdata_running() { + if command -v pgrep > /dev/null 2>&1; then + if pgrep netdata; then + return 0 + else + return 1 + fi + else + if [ -z "${INSTALL_PREFIX}" ]; then + NETDATACLI_PATH=/usr/sbin/netdatacli + elif [ "${INSTALL_PREFIX}" = "/opt/netdata" ]; then + NETDATACLI_PATH="/opt/netdata/bin/netdatacli" + else + NETDATACLI_PATH="${INSTALL_PREFIX}/netdata/usr/sbin/netdatacli" + fi + + if "${NETDATACLI_PATH}" ping > /dev/null 2>&1; then + return 0 + else + return 1 + fi + fi +} + +claim() { + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would attempt to claim agent to ${NETDATA_CLAIM_URL}" + else + progress "Attempting to claim agent to ${NETDATA_CLAIM_URL}" + fi + + progress "Attempting to claim agent to ${NETDATA_CLAIM_URL}" + if command -v netdata-claim.sh > /dev/null 2>&1; then + NETDATA_CLAIM_PATH="$(command -v netdata-claim.sh)" + elif [ -z "${INSTALL_PREFIX}" ] || [ "${INSTALL_PREFIX}" = "/" ]; then + NETDATA_CLAIM_PATH=/usr/sbin/netdata-claim.sh + elif [ "${INSTALL_PREFIX}" = "/opt/netdata" ]; then + NETDATA_CLAIM_PATH="/opt/netdata/bin/netdata-claim.sh" + elif [ ! -d "${INSTALL_PREFIX}/netdata" ]; then + if [ -d "${INSTALL_PREFIX}/usr" ]; then + NETDATA_CLAIM_PATH="${INSTALL_PREFIX}/usr/sbin/netdata-claim.sh" + else + NETDATA_CLAIM_PATH="${INSTALL_PREFIX}/sbin/netdata-claim.sh" + fi + else + NETDATA_CLAIM_PATH="${INSTALL_PREFIX}/netdata/usr/sbin/netdata-claim.sh" + fi + + if [ ! -x "${NETDATA_CLAIM_PATH}" ]; then + fatal "Unable to find usable claiming script. Reinstalling Netdata may resolve this." F050B + fi + + if ! is_netdata_running; then + NETDATA_CLAIM_EXTRA="${NETDATA_CLAIM_EXTRA} -daemon-not-running" + fi + + # shellcheck disable=SC2086 + run ${ROOTCMD} "${NETDATA_CLAIM_PATH}" -token="${NETDATA_CLAIM_TOKEN}" -rooms="${NETDATA_CLAIM_ROOMS}" -url="${NETDATA_CLAIM_URL}" ${NETDATA_CLAIM_EXTRA} + case $? in + 0) + progress "Successfully claimed node" + return 0 + ;; + 1) + warning "Unable to claim node due to invalid claiming options. If you are seeing this message, you’ve probably found a bug and should open a bug report at ${AGENT_BUG_REPORT_URL}" + ;; + 2) + warning "Unable to claim node due to issues creating the claiming directory or preparing the local claiming key. Make sure you have a working openssl command and that ${INSTALL_PREFIX}/var/lib/netdata/cloud.d exists, then try again." + ;; + 3) + warning "Unable to claim node due to missing dependencies. Usually this means that the Netdata Agent was built without support for Netdata Cloud. If you built the agent from source, please install all needed dependencies for Cloud support. If you used the regular installation script and see this error, please file a bug report at ${AGENT_BUG_REPORT_URL}." + ;; + 4) + warning "Failed to claim node due to inability to connect to ${NETDATA_CLAIM_URL}. Usually this either means that the specified claiming URL is wrong, or that you are having networking problems." + ;; + 5) + progress "Successfully claimed node, but was not able to notify the Netdata Agent. You will need to restart the Netdata service on this node before it will show up in the Cloud." + return 0 + ;; + 8) + warning "Failed to claim node due to an invalid agent ID. You can usually resolve this by removing ${INSTALL_PREFIX}/var/lib/netdata/registry/netdata.public.unique.id and restarting the agent. Then try to claim it again using the same options." + ;; + 9) + warning "Failed to claim node due to an invalid node name. This probably means you tried to specify a custom name for this node (for example, using the --claim-hostname option), but the hostname itself was either empty or consisted solely of whitespace. You can resolve this by specifying a valid host name and trying again." + ;; + 10) + warning "Failed to claim node due to an invalid room ID. This issue is most likely caused by a typo. Please check if the room(s) you are trying to add appear on the list of rooms provided to the --claim-rooms option ('${NETDATA_CLAIM_ROOMS}'). Then verify if the rooms are visible in Netdata Cloud and try again." + ;; + 11) + warning "Failed to claim node due to an issue with the generated RSA key pair. You can usually resolve this by removing all files in ${INSTALL_PREFIX}/var/lib/netdata/cloud.d and then trying again." + ;; + 12) + warning "Failed to claim node due to an invalid or expired claiming token. Please check that the token specified with the --claim-token option ('${NETDATA_CLAIM_TOKEN}') matches what you see in the Cloud and try again." + ;; + 13) + warning "Failed to claim node because the Cloud thinks it is already claimed. If this node was created by cloning a VM or as a container from a template, please remove the file ${INSTALL_PREFIX}/var/lib/netdata/registry/netdata.public.unique.id and restart the agent. Then try to claim it again with the same options. Otherwise, if you are certain this node has never been claimed before, you can use the --claim-id option to specify a new node ID to use for claiming, for example by using the uuidgen command like so: --claim-id \"\$(uuidgen)\"" + ;; + 14) + warning "Failed to claim node because the node is already in the process of being claimed. You should not need to do anything to resolve this, the node should show up properly in the Cloud soon. If it does not, please report a bug at ${AGENT_BUG_REPORT_URL}." + ;; + 15|16|17) + warning "Failed to claim node due to an internal server error in the Cloud. Please retry claiming this node later, and if you still see this message file a bug report at ${CLOUD_BUG_REPORT_URL}." + ;; + 18) + warning "Unable to claim node because this Netdata installation does not have a unique ID yet. Make sure the agent is running and started up correctly, and then try again." + ;; + *) + warning "Failed to claim node for an unknown reason. This usually means either networking problems or a bug. Please retry claiming later, and if you still see this message file a bug report at ${AGENT_BUG_REPORT_URL}" + ;; + esac + + if [ -z "${NETDATA_NEW_INSTALL}" ]; then + deferred_warnings + printf >&2 "%s\n" "For community support, you can connect with us on:" + support_list + cleanup + trap - EXIT + exit 1 + fi +} + +# ====================================================================== +# Auto-update handling code. +set_auto_updates() { + if [ -x "${INSTALL_PREFIX}/usr/libexec/netdata/netdata-updater.sh" ]; then + updater="${INSTALL_PREFIX}/usr/libexec/netdata/netdata-updater.sh" + elif [ -x "${INSTALL_PREFIX}/netdata/usr/libexec/netdata/netdata-updater.sh" ]; then + updater="${INSTALL_PREFIX}/netdata/usr/libexec/netdata/netdata-updater.sh" + else + warning "Could not find netdata-updater.sh. This means that auto-updates cannot (currently) be enabled on this system. See https://learn.netdata.cloud/docs/agent/packaging/installer/update for more information about updating Netdata." + return 0 + fi + + if [ "${AUTO_UPDATE}" -eq 1 ]; then + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would have attempted to enable automatic updates." + # This first case is for catching using a new kickstart script with an old build. It can be safely removed after v1.34.0 is released. + elif ! grep -q '\-\-enable-auto-updates' ${updater}; then + echo + elif ! ${ROOTCMD} ${updater} --enable-auto-updates "${NETDATA_AUTO_UPDATE_TYPE}"; then + warning "Failed to enable auto updates. Netdata will still work, but you will need to update manually." + fi + else + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would have attempted to disable automatic updates." + else + ${ROOTCMD} ${updater} --disable-auto-updates + fi + fi +} + +# ====================================================================== +# Native package install code. + +# Check for an already installed package with a given name. +pkg_installed() { + case "${SYSTYPE}" in + Linux) + case "${DISTRO_COMPAT_NAME}" in + debian|ubuntu) + # shellcheck disable=SC2016 + dpkg-query --show --showformat '${Status}' "${1}" 2>&1 | cut -f 1 -d ' ' | grep -q '^install$' + return $? + ;; + centos|fedora|opensuse|ol) + rpm -q "${1}" > /dev/null 2>&1 + return $? + ;; + alpine) + apk -e info "${1}" > /dev/null 2>&1 + return $? + ;; + arch) + pacman -Qi "${1}" > /dev/null 2>&1 + return $? + ;; + *) + return 1 + ;; + esac + ;; + Darwin) + if command -v brew > /dev/null 2>&1; then + brew list "${1}" > /dev/null 2>&1 + return $? + else + return 1 + fi + ;; + FreeBSD) + if pkg -N > /dev/null 2>&1; then + pkg info "${1}" > /dev/null 2>&1 + return $? + else + return 1 + fi + ;; + *) return 1 ;; + esac +} + +# Check for the existence of a usable netdata package in the repo. +netdata_avail_check() { + case "${DISTRO_COMPAT_NAME}" in + debian|ubuntu) + env DEBIAN_FRONTEND=noninteractive apt-cache policy netdata | grep -q packagecloud.io/netdata/netdata; + return $? + ;; + centos|fedora|ol) + # shellcheck disable=SC2086 + ${pm_cmd} search --nogpgcheck -v netdata | grep -qE 'Repo *: netdata(-edge)?$' + return $? + ;; + opensuse) + zypper packages -r "$(zypper repos | grep -E 'netdata |netdata-edge ' | cut -f 1 -d '|' | tr -d ' ')" | grep -E 'netdata ' + return $? + ;; + *) + return 1 + ;; + esac +} + +# Check for any distro-specific dependencies we know we need. +check_special_native_deps() { + if [ "${DISTRO_COMPAT_NAME}" = "centos" ] && [ "${SYSVERSION}" = "7" ]; then + progress "Checking for libuv availability." + if ${pm_cmd} search --nogpgcheck -v libuv | grep -q "No matches found"; then + progress "libuv not found, checking for EPEL availability." + if ${pm_cmd} search --nogpgcheck -v epel-release | grep -q "No matches found"; then + warning "Unable to find a suitable source for libuv, cannot install using native packages on this system." + return 1 + else + progress "EPEL is available, attempting to install so that required dependencies are available." + + # shellcheck disable=SC2086 + if ! run ${ROOTCMD} env ${env} ${pm_cmd} install ${pkg_install_opts} epel-release; then + warning "Failed to install EPEL, even though it is required to install native packages on this system." + return 1 + fi + fi + else + return 0 + fi + fi +} + +try_package_install() { + failed_refresh_msg="Failed to refresh repository metadata. ${BADNET_MSG} or by misconfiguration of one or more rpackage repositories in the system package manager configuration." + + if [ -z "${DISTRO}" ] || [ "${DISTRO}" = "unknown" ]; then + warning "Unable to determine Linux distribution for native packages." + return 2 + fi + + set_tmpdir + + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would attempt to install using native packages..." + else + progress "Attempting to install using native packages..." + fi + + if [ "${SELECTED_RELEASE_CHANNEL}" = "nightly" ]; then + release="-edge" + else + release="" + fi + + if [ "${INTERACTIVE}" = "0" ]; then + interactive_opts="-y" + env="DEBIAN_FRONTEND=noninteractive" + else + interactive_opts="" + env="" + fi + + case "${DISTRO_COMPAT_NAME}" in + debian) + needs_early_refresh=1 + pm_cmd="apt-get" + repo_subcmd="update" + repo_prefix="debian/${SYSCODENAME}" + pkg_type="deb" + pkg_suffix="_all" + pkg_vsep="_" + pkg_install_opts="${interactive_opts}" + repo_update_opts="${interactive_opts}" + uninstall_subcmd="purge" + INSTALL_TYPE="binpkg-deb" + NATIVE_VERSION="${INSTALL_VERSION:+"=${INSTALL_VERSION}"}" + ;; + ubuntu) + needs_early_refresh=1 + pm_cmd="apt-get" + repo_subcmd="update" + repo_prefix="ubuntu/${SYSCODENAME}" + pkg_type="deb" + pkg_suffix="_all" + pkg_vsep="_" + pkg_install_opts="${interactive_opts}" + repo_update_opts="${interactive_opts}" + uninstall_subcmd="purge" + INSTALL_TYPE="binpkg-deb" + NATIVE_VERSION="${INSTALL_VERSION:+"=${INSTALL_VERSION}"}" + ;; + centos) + if command -v dnf > /dev/null; then + pm_cmd="dnf" + repo_subcmd="makecache" + else + pm_cmd="yum" + fi + repo_prefix="el/${SYSVERSION}" + pkg_type="rpm" + pkg_suffix=".noarch" + pkg_vsep="-" + pkg_install_opts="${interactive_opts}" + repo_update_opts="${interactive_opts}" + uninstall_subcmd="remove" + INSTALL_TYPE="binpkg-rpm" + NATIVE_VERSION="${INSTALL_VERSION:+"-${INSTALL_VERSION}.${SYSARCH}"}" + ;; + fedora) + if command -v dnf > /dev/null; then + pm_cmd="dnf" + repo_subcmd="makecache" + else + pm_cmd="yum" + fi + repo_prefix="fedora/${SYSVERSION}" + pkg_type="rpm" + pkg_suffix=".noarch" + pkg_vsep="-" + pkg_install_opts="${interactive_opts}" + repo_update_opts="${interactive_opts}" + uninstall_subcmd="remove" + INSTALL_TYPE="binpkg-rpm" + NATIVE_VERSION="${INSTALL_VERSION:+"-${INSTALL_VERSION}.${SYSARCH}"}" + ;; + opensuse) + pm_cmd="zypper" + repo_subcmd="--gpg-auto-import-keys refresh" + repo_prefix="opensuse/${SYSVERSION}" + pkg_type="rpm" + pkg_suffix=".noarch" + pkg_vsep="-" + pkg_install_opts="${interactive_opts} --allow-unsigned-rpm" + repo_update_opts="" + uninstall_subcmd="remove" + INSTALL_TYPE="binpkg-rpm" + NATIVE_VERSION="${INSTALL_VERSION:+"-${INSTALL_VERSION}.${SYSARCH}"}" + ;; + ol) + if command -v dnf > /dev/null; then + pm_cmd="dnf" + repo_subcmd="makecache" + else + pm_cmd="yum" + fi + repo_prefix="ol/${SYSVERSION}" + pkg_type="rpm" + pkg_suffix=".noarch" + pkg_vsep="-" + pkg_install_opts="${interactive_opts}" + repo_update_opts="${interactive_opts}" + uninstall_subcmd="remove" + INSTALL_TYPE="binpkg-rpm" + NATIVE_VERSION="${INSTALL_VERSION:+"-${INSTALL_VERSION}.${SYSARCH}"}" + ;; + *) + warning "We do not provide native packages for ${DISTRO}." + return 2 + ;; + esac + + if [ -n "${INSTALL_VERSION}" ]; then + if echo "${INSTALL_VERSION}" | grep -q "nightly"; then + new_release="-edge" + else + new_release= + fi + + if { [ -n "${new_release}" ] && [ -z "${release}" ]; } || { [ -z "${new_release}" ] && [ -n "${release}" ]; }; then + warning "Selected release channel does not match this version and it will be changed automatically." + fi + + release="${new_release}" + fi + + repoconfig_name="netdata-repo${release}" + repoconfig_file="${repoconfig_name}${pkg_vsep}${REPOCONFIG_VERSION}${pkg_suffix}.${pkg_type}" + repoconfig_url="${REPOCONFIG_URL_PREFIX}/${repo_prefix}/${repoconfig_file}/download.${pkg_type}" + + if ! pkg_installed "${repoconfig_name}"; then + progress "Checking for availability of repository configuration package." + if ! check_for_remote_file "${repoconfig_url}"; then + warning "No repository configuration package available for ${DISTRO} ${SYSVERSION}. Cannot install native packages on this system." + return 2 + fi + + if ! download "${repoconfig_url}" "${tmpdir}/${repoconfig_file}"; then + fatal "Failed to download repository configuration package. ${BADNET_MSG}." F0209 + fi + + if [ -n "${needs_early_refresh}" ]; then + # shellcheck disable=SC2086 + if ! run ${ROOTCMD} env ${env} ${pm_cmd} ${repo_subcmd} ${repo_update_opts}; then + warning "${failed_refresh_msg}" + return 2 + fi + fi + + # shellcheck disable=SC2086 + if ! run ${ROOTCMD} env ${env} ${pm_cmd} install ${pkg_install_opts} "${tmpdir}/${repoconfig_file}"; then + warning "Failed to install repository configuration package." + return 2 + fi + + if [ -n "${repo_subcmd}" ]; then + # shellcheck disable=SC2086 + if ! run ${ROOTCMD} env ${env} ${pm_cmd} ${repo_subcmd} ${repo_update_opts}; then + fatal "${failed_refresh_msg}" F0205 + fi + fi + else + progress "Repository configuration is already present, attempting to install netdata." + fi + + if [ "${REPO_ACTION}" = "repositories-only" ]; then + progress "Successfully installed repository configuraion package." + deferred_warnings + cleanup + trap - EXIT + exit 1 + fi + + if ! check_special_native_deps; then + warning "Could not find secondary dependencies for ${DISTRO} on ${SYSARCH}." + if [ -z "${NO_CLEANUP}" ]; then + progress "Attempting to uninstall repository configuration package." + # shellcheck disable=SC2086 + run ${ROOTCMD} env ${env} ${pm_cmd} ${uninstall_subcmd} ${pkg_install_opts} "${repoconfig_name}" + fi + return 2 + fi + + if ! netdata_avail_check "${DISTRO_COMPAT_NAME}"; then + warning "Could not find a usable native package for ${DISTRO} on ${SYSARCH}." + if [ -z "${NO_CLEANUP}" ]; then + progress "Attempting to uninstall repository configuration package." + # shellcheck disable=SC2086 + run ${ROOTCMD} env ${env} ${pm_cmd} ${uninstall_subcmd} ${pkg_install_opts} "${repoconfig_name}" + fi + return 2 + fi + + if [ "${NETDATA_DISABLE_TELEMETRY}" -eq 1 ]; then + run ${ROOTCMD} mkdir -p "/etc/netdata" + run ${ROOTCMD} touch "/etc/netdata/.opt-out-from-anonymous-statistics" + fi + + # shellcheck disable=SC2086 + if ! run ${ROOTCMD} env ${env} ${pm_cmd} install ${pkg_install_opts} "netdata${NATIVE_VERSION}"; then + warning "Failed to install Netdata package." + if [ -z "${NO_CLEANUP}" ]; then + progress "Attempting to uninstall repository configuration package." + # shellcheck disable=SC2086 + run ${ROOTCMD} env ${env} ${pm_cmd} ${uninstall_subcmd} ${pkg_install_opts} "${repoconfig_name}" + fi + return 2 + fi +} + +# ====================================================================== +# Static build install code +# shellcheck disable=SC2034,SC2086,SC2126 +set_static_archive_urls() { + if [ -z "${2}" ]; then + arch="${SYSARCH}" + else + arch="${2}" + fi + + if [ -n "${NETDATA_OFFLINE_INSTALL_SOURCE}" ]; then + path="$(cd "${NETDATA_OFFLINE_INSTALL_SOURCE}" || exit 1; pwd)" + export NETDATA_STATIC_ARCHIVE_URL="file://${path}/netdata-${arch}-latest.gz.run" + export NETDATA_STATIC_ARCHIVE_CHECKSUM_URL="file://${path}/sha256sums.txt" + elif [ "${1}" = "stable" ]; then + if [ -n "${INSTALL_VERSION}" ]; then + export NETDATA_STATIC_ARCHIVE_OLD_URL="https://github.com/netdata/netdata/releases/download/v${INSTALL_VERSION}/netdata-v${INSTALL_VERSION}.gz.run" + export NETDATA_STATIC_ARCHIVE_URL="https://github.com/netdata/netdata/releases/download/v${INSTALL_VERSION}/netdata-${arch}-v${INSTALL_VERSION}.gz.run" + export NETDATA_STATIC_ARCHIVE_CHECKSUM_URL="https://github.com/netdata/netdata/releases/download/v${INSTALL_VERSION}/sha256sums.txt" + else + latest="$(get_redirect "https://github.com/netdata/netdata/releases/latest")" + export NETDATA_STATIC_ARCHIVE_URL="https://github.com/netdata/netdata/releases/download/${latest}/netdata-${arch}-latest.gz.run" + export NETDATA_STATIC_ARCHIVE_CHECKSUM_URL="https://github.com/netdata/netdata/releases/download/${latest}/sha256sums.txt" + fi + else + if [ -n "${INSTALL_VERSION}" ]; then + export NETDATA_STATIC_ARCHIVE_URL="${NETDATA_TARBALL_BASEURL}/netdata-${arch}-v${INSTALL_VERSION}.gz.run" + export NETDATA_STATIC_ARCHIVE_OLD_URL="${NETDATA_TARBALL_BASEURL}/netdata-v${INSTALL_VERSION}.gz.run" + export NETDATA_STATIC_ARCHIVE_CHECKSUM_URL="${NETDATA_TARBALL_BASEURL}/sha256sums.txt" + else + export NETDATA_STATIC_ARCHIVE_URL="${NETDATA_TARBALL_BASEURL}/netdata-${arch}-latest.gz.run" + export NETDATA_STATIC_ARCHIVE_CHECKSUM_URL="${NETDATA_TARBALL_BASEURL}/sha256sums.txt" + fi + fi +} + +try_static_install() { + set_static_archive_urls "${SELECTED_RELEASE_CHANNEL}" + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would attempt to install using static build..." + else + progress "Attempting to install using static build..." + fi + + # Check status code first, so that we can provide nicer fallback for dry runs. + if check_for_remote_file "${NETDATA_STATIC_ARCHIVE_URL}"; then + if [ -n "${NETDATA_OFFLINE_INSTALL_SOURCE}" ]; then + netdata_agent="$(basename "${NETDATA_STATIC_ARCHIVE_URL#"file://"}")" + elif [ -n "${INSTALL_VERSION}" ]; then + if [ "${SELECTED_RELEASE_CHANNEL}" = "stable" ]; then + netdata_agent="${NETDATA_STATIC_ARCHIVE_URL#"https://github.com/netdata/netdata/releases/download/v${INSTALL_VERSION}/"}" + else + netdata_agent="${NETDATA_STATIC_ARCHIVE_URL#"${NETDATA_TARBALL_BASEURL}/"}" + fi + else + if [ "${SELECTED_RELEASE_CHANNEL}" = "stable" ]; then + netdata_agent="${NETDATA_STATIC_ARCHIVE_URL#"https://github.com/netdata/netdata/releases/download/${latest}/"}" + else + netdata_agent="${NETDATA_STATIC_ARCHIVE_URL#"${NETDATA_TARBALL_BASEURL}/"}" + fi + fi + elif [ "${SYSARCH}" = "x86_64" ] && check_for_remote_file "${NETDATA_STATIC_ARCHIVE_OLD_URL}"; then + netdata_agent="${NETDATA_STATIC_ARCHIVE_OLD_URL#"https://github.com/netdata/netdata/releases/download/v${INSTALL_VERSION}/"}" + export NETDATA_STATIC_ARCHIVE_URL="${NETDATA_STATIC_ARCHIVE_OLD_URL}" + else + warning "There is no static build available for ${SYSARCH} CPUs. This usually means we simply do not currently provide static builds for ${SYSARCH} CPUs." + return 2 + fi + + if ! download "${NETDATA_STATIC_ARCHIVE_URL}" "${tmpdir}/${netdata_agent}"; then + fatal "Unable to download static build archive for ${SYSARCH}. ${BADNET_MSG}." F0208 + fi + + if ! download "${NETDATA_STATIC_ARCHIVE_CHECKSUM_URL}" "${tmpdir}/sha256sum.txt"; then + fatal "Unable to fetch checksums to verify static build archive. ${BADNET_MSG}." F0206 + fi + + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would validate SHA256 checksum of downloaded static build archive." + else + if [ -z "${INSTALL_VERSION}" ]; then + if ! grep "${netdata_agent}" "${tmpdir}/sha256sum.txt" | safe_sha256sum -c - > /dev/null 2>&1; then + fatal "Static binary checksum validation failed. ${BADCACHE_MSG}." F0207 + fi + fi + fi + + if [ "${INTERACTIVE}" -eq 0 ]; then + opts="${opts} --accept" + fi + + progress "Installing netdata" + # shellcheck disable=SC2086 + if ! run ${ROOTCMD} sh "${tmpdir}/${netdata_agent}" ${opts} -- ${NETDATA_INSTALLER_OPTIONS}; then + warning "Failed to install static build of Netdata on ${SYSARCH}." + run rm -rf /opt/netdata + return 2 + fi + + if [ "${DRY_RUN}" -ne 1 ]; then + install_type_file="/opt/netdata/etc/netdata/.install-type" + if [ -f "${install_type_file}" ]; then + ${ROOTCMD} sh -c "cat \"${install_type_file}\" > \"${tmpdir}/install-type\"" + ${ROOTCMD} chown "$(id -u)":"$(id -g)" "${tmpdir}/install-type" + # shellcheck disable=SC1090,SC1091 + . "${tmpdir}/install-type" + cat > "${tmpdir}/install-type" <<- EOF + INSTALL_TYPE='kickstart-static' + PREBUILT_ARCH='${PREBUILT_ARCH}' + EOF + ${ROOTCMD} chown netdata:netdata "${tmpdir}/install-type" + ${ROOTCMD} cp "${tmpdir}/install-type" "${install_type_file}" + fi + fi +} + +# ====================================================================== +# Local build install code + +set_source_archive_urls() { + if [ "$1" = "stable" ]; then + if [ -n "${INSTALL_VERSION}" ]; then + export NETDATA_SOURCE_ARCHIVE_URL="https://github.com/netdata/netdata/releases/download/v${INSTALL_VERSION}/netdata-v${INSTALL_VERSION}.tar.gz" + export NETDATA_SOURCE_ARCHIVE_CHECKSUM_URL="https://github.com/netdata/netdata/releases/download/v${INSTALL_VERSION}/sha256sums.txt" + else + latest="$(get_redirect "https://github.com/netdata/netdata/releases/latest")" + export NETDATA_SOURCE_ARCHIVE_URL="https://github.com/netdata/netdata/releases/download/${latest}/netdata-${latest}.tar.gz" + export NETDATA_SOURCE_ARCHIVE_CHECKSUM_URL="https://github.com/netdata/netdata/releases/download/${latest}/sha256sums.txt" + fi + else + if [ -n "${INSTALL_VERSION}" ]; then + export NETDATA_SOURCE_ARCHIVE_URL="${NETDATA_TARBALL_BASEURL}/netdata-v${INSTALL_VERSION}.tar.gz" + export NETDATA_SOURCE_ARCHIVE_CHECKSUM_URL="${NETDATA_TARBALL_BASEURL}/sha256sums.txt" + else + export NETDATA_SOURCE_ARCHIVE_URL="${NETDATA_TARBALL_BASEURL}/netdata-latest.tar.gz" + export NETDATA_SOURCE_ARCHIVE_CHECKSUM_URL="${NETDATA_TARBALL_BASEURL}/sha256sums.txt" + fi + fi +} + +install_local_build_dependencies() { + set_tmpdir + bash="$(command -v bash 2> /dev/null)" + + if [ -z "${bash}" ] || [ ! -x "${bash}" ]; then + warning "Unable to find a usable version of \`bash\` (required for local build)." + return 1 + fi + + if ! download "${PACKAGES_SCRIPT}" "${tmpdir}/install-required-packages.sh"; then + fatal "Failed to download dependency handling script for local build. ${BADNET_MSG}." F000D + fi + + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would run downloaded script to install required build dependencies..." + else + progress "Running downloaded script to install required build dependencies..." + fi + + if [ "${INTERACTIVE}" -eq 0 ]; then + opts="--dont-wait --non-interactive" + fi + + if [ "${SYSTYPE}" = "Darwin" ]; then + sudo="" + else + sudo="${ROOTCMD}" + fi + + # shellcheck disable=SC2086 + if ! run ${sudo} "${bash}" "${tmpdir}/install-required-packages.sh" ${opts} netdata; then + warning "Failed to install all required packages, but installation might still be possible." + fi +} + +build_and_install() { + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would attempt to build netdata..." + else + progress "Building netdata..." + fi + + echo "INSTALL_TYPE='kickstart-build'" > system/.install-type + + opts="${NETDATA_INSTALLER_OPTIONS}" + + if [ "${INTERACTIVE}" -eq 0 ]; then + opts="${opts} --dont-wait" + fi + + if [ "${SELECTED_RELEASE_CHANNEL}" = "stable" ]; then + opts="${opts} --stable-channel" + fi + + if [ "${NETDATA_REQUIRE_CLOUD}" -eq 1 ]; then + opts="${opts} --require-cloud" + elif [ "${NETDATA_DISABLE_CLOUD}" -eq 1 ]; then + opts="${opts} --disable-cloud" + fi + + # shellcheck disable=SC2086 + run_script ./netdata-installer.sh ${opts} + + case $? in + 1) + if [ -n "${EXIT_REASON}" ]; then + fatal "netdata-installer.sh failed to run: ${EXIT_REASON}" "${EXIT_CODE}" + else + fatal "netdata-installer.sh failed to run: Encountered an unhandled error in the installer code." I0000 + fi + ;; + 2) + fatal "Insufficient RAM to install netdata." F0008 + ;; + esac +} + +try_build_install() { + set_tmpdir + + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would attempt to install by building locally..." + else + progress "Attempting to install by building locally..." + fi + + if ! install_local_build_dependencies; then + return 1 + fi + + set_source_archive_urls "${SELECTED_RELEASE_CHANNEL}" + + if [ -n "${INSTALL_VERSION}" ]; then + if ! download "${NETDATA_SOURCE_ARCHIVE_URL}" "${tmpdir}/netdata-v${INSTALL_VERSION}.tar.gz"; then + fatal "Failed to download source tarball for local build. ${BADNET_MSG}." F000B + fi + elif ! download "${NETDATA_SOURCE_ARCHIVE_URL}" "${tmpdir}/netdata-latest.tar.gz"; then + fatal "Failed to download source tarball for local build. ${BADNET_MSG}." F000B + fi + + if ! download "${NETDATA_SOURCE_ARCHIVE_CHECKSUM_URL}" "${tmpdir}/sha256sum.txt"; then + fatal "Failed to download checksums for source tarball verification. ${BADNET_MSG}." F000C + fi + + if [ "${DRY_RUN}" -eq 1 ]; then + progress "Would validate SHA256 checksum of downloaded source archive." + else + if [ -z "${INSTALL_VERSION}" ]; then + # shellcheck disable=SC2086 + if ! grep netdata-latest.tar.gz "${tmpdir}/sha256sum.txt" | safe_sha256sum -c - > /dev/null 2>&1; then + fatal "Tarball checksum validation failed. ${BADCACHE_MSG}." F0005 + fi + fi + fi + + if [ -n "${INSTALL_VERSION}" ]; then + run tar -xf "${tmpdir}/netdata-v${INSTALL_VERSION}.tar.gz" -C "${tmpdir}" + rm -rf "${tmpdir}/netdata-v${INSTALL_VERSION}.tar.gz" > /dev/null 2>&1 + else + run tar -xf "${tmpdir}/netdata-latest.tar.gz" -C "${tmpdir}" + rm -rf "${tmpdir}/netdata-latest.tar.gz" > /dev/null 2>&1 + fi + + if [ "${DRY_RUN}" -ne 1 ]; then + cd "$(find "${tmpdir}" -mindepth 1 -maxdepth 1 -type d -name netdata-)" || fatal "Cannot change directory to netdata source tree" F0006 + fi + + if [ -x netdata-installer.sh ] || [ "${DRY_RUN}" -eq 1 ]; then + build_and_install || return 1 + else + # This case is needed because some platforms produce an extra directory on the source tarball extraction. + if [ "$(find . -mindepth 1 -maxdepth 1 -type d | wc -l)" -eq 1 ] && [ -x "$(find . -mindepth 1 -maxdepth 1 -type d)/netdata-installer.sh" ]; then + cd "$(find . -mindepth 1 -maxdepth 1 -type d)" && build_and_install || return 1 + else + fatal "Cannot install netdata from source (the source directory does not include netdata-installer.sh)." F0009 + fi + fi +} + +# ====================================================================== +# Offline install support code + +prepare_offline_install_source() { + if [ -e "${1}" ]; then + if [ ! -d "${1}" ]; then + fatal "${1} is not a directory, unable to prepare offline install source." F0503 + fi + else + run mkdir -p "${1}" || fatal "Unable to create target directory for offline install preparation." F0504 + fi + + run cd "${1}" || fatal "Failed to swtich to target directory for offline install preparation." F0505 + + if [ "${NETDATA_ONLY_NATIVE}" -ne 1 ] && [ "${NETDATA_ONLY_BUILD}" -ne 1 ]; then + set_static_archive_urls "${SELECTED_RELEASE_CHANNEL}" "x86_64" + + if check_for_remote_file "${NETDATA_STATIC_ARCHIVE_URL}"; then + for arch in ${STATIC_INSTALL_ARCHES}; do + set_static_archive_urls "${SELECTED_RELEASE_CHANNEL}" "${arch}" + + progress "Fetching ${NETDATA_STATIC_ARCHIVE_URL}" + if ! download "${NETDATA_STATIC_ARCHIVE_URL}" "netdata-${arch}-latest.gz.run"; then + warning "Failed to download static installer archive for ${arch}. ${BADNET_MSG}." + fi + done + legacy=0 + else + warning "Selected version of Netdata only provides static builds for x86_64. You will only be able to install on x86_64 systems with this offline install source." + progress "Fetching ${NETDATA_STATIC_ARCHIVE_OLD_URL}" + legacy=1 + + if ! download "${NETDATA_STATIC_ARCHIVE_OLD_URL}" "netdata-x86_64-latest.gz.run"; then + warning "Failed to download static installer archive for x86_64. ${BADNET_MSG}." + fi + fi + + progress "Fetching ${NETDATA_STATIC_ARCHIVE_CHECKSUM_URL}" + if ! download "${NETDATA_STATIC_ARCHIVE_CHECKSUM_URL}" "sha256sums.txt"; then + fatal "Failed to download checksum file. ${BADNET_MSG}." F0506 + fi + fi + + if [ "${legacy:-0}" -eq 1 ]; then + sed -e 's/netdata-latest.gz.run/netdata-x86_64-latest.gz.run' sha256sums.txt > sha256sums.tmp + mv sha256sums.tmp sha256sums.txt + fi + + if [ "${DRY_RUN}" -ne 1 ]; then + progress "Verifying checksums." + if ! grep -e "$(find . -name '*.gz.run')" sha256sums.txt | safe_sha256sum -c -; then + fatal "Checksums for offline install files are incorrect. ${BADCACHE_MSG}." F0507 + fi + else + progress "Would verify SHA256 checksums of downloaded installation files." + fi + + if [ "${DRY_RUN}" -ne 1 ]; then + progress "Preparing install script." + cat > "install.sh" <<-EOF + #!/bin/sh + dir=\$(CDPATH= cd -- "\$(dirname -- "\$0")" && pwd) + "\${dir}/kickstart.sh" --offline-install-source "\${dir}" \${@} + EOF + chmod +x "install.sh" + else + progress "Would create install script" + fi + + if [ "${DRY_RUN}" -ne 1 ]; then + progress "Copying kickstart script." + cp "${KICKSTART_SOURCE}" "kickstart.sh" + chmod +x "kickstart.sh" + else + progress "Would copy kickstart.sh to offline install source directory" + fi + + if [ "${DRY_RUN}" -ne 1 ]; then + progress "Saving release channel information." + echo "${SELECTED_RELEASE_CHANNEL}" > "channel" + else + progress "Would save release channel information to offline install source directory" + fi + + progress "Finished preparing offline install source directory at ${1}. You can now copy this directory to a target system and then run the script ‘install.sh’ from it to install on that system." +} + +# ====================================================================== +# Per system-type install logic + +install_on_linux() { + if [ "${NETDATA_ONLY_STATIC}" -ne 1 ] && [ "${NETDATA_ONLY_BUILD}" -ne 1 ] && [ -z "${NETDATA_OFFLINE_INSTALL_SOURCE}" ]; then + SELECTED_INSTALL_METHOD="native" + try_package_install + + case "$?" in + 0) + NETDATA_INSTALL_SUCCESSFUL=1 + INSTALL_PREFIX="/" + ;; + 1) + fatal "Unable to install on this system." F0300 + ;; + 2) + if [ "${NETDATA_ONLY_NATIVE}" -eq 1 ]; then + fatal "Could not install native binary packages." F0301 + else + warning "Could not install native binary packages, falling back to alternative installation method." + fi + ;; + esac + fi + + if [ "${NETDATA_ONLY_NATIVE}" -ne 1 ] && [ "${NETDATA_ONLY_BUILD}" -ne 1 ] && [ -z "${NETDATA_INSTALL_SUCCESSFUL}" ]; then + SELECTED_INSTALL_METHOD="static" + INSTALL_TYPE="kickstart-static" + try_static_install + + case "$?" in + 0) + NETDATA_INSTALL_SUCCESSFUL=1 + INSTALL_PREFIX="/opt/netdata" + ;; + 1) + fatal "Unable to install on this system." F0302 + ;; + 2) + if [ "${NETDATA_ONLY_STATIC}" -eq 1 ]; then + fatal "Could not install static build." F0303 + else + warning "Could not install static build, falling back to alternative installation method." + fi + ;; + esac + fi + + if [ "${NETDATA_ONLY_NATIVE}" -ne 1 ] && [ "${NETDATA_ONLY_STATIC}" -ne 1 ] && [ -z "${NETDATA_INSTALL_SUCCESSFUL}" ]; then + SELECTED_INSTALL_METHOD="build" + INSTALL_TYPE="kickstart-build" + try_build_install + + case "$?" in + 0) + NETDATA_INSTALL_SUCCESSFUL=1 + ;; + *) + fatal "Unable to install on this system." F0304 + ;; + esac + fi +} + +install_on_macos() { + if [ "${NETDATA_ONLY_NATIVE}" -eq 1 ]; then + fatal "User requested native package, but native packages are not available for macOS. Try installing without \`--only-native\` option." F0305 + elif [ "${NETDATA_ONLY_STATIC}" -eq 1 ]; then + fatal "User requested static build, but static builds are not available for macOS. Try installing without \`--only-static\` option." F0306 + else + SELECTED_INSTALL_METHOD="build" + INSTALL_TYPE="kickstart-build" + try_build_install + + case "$?" in + 0) + NETDATA_INSTALL_SUCCESSFUL=1 + ;; + *) + fatal "Unable to install on this system." F0307 + ;; + esac + fi +} + +install_on_freebsd() { + if [ "${NETDATA_ONLY_NATIVE}" -eq 1 ]; then + fatal "User requested native package, but native packages are not available for FreeBSD. Try installing without \`--only-native\` option." F0308 + elif [ "${NETDATA_ONLY_STATIC}" -eq 1 ]; then + fatal "User requested static build, but static builds are not available for FreeBSD. Try installing without \`--only-static\` option." F0309 + else + SELECTED_INSTALL_METHOD="build" + INSTALL_TYPE="kickstart-build" + try_build_install + + case "$?" in + 0) + NETDATA_INSTALL_SUCCESSFUL=1 + ;; + *) + fatal "Unable to install on this system." F030A + ;; + esac + fi +} + +# ====================================================================== +# Argument parsing code + +validate_args() { + check_claim_opts + + if [ -n "${NETDATA_OFFLINE_INSTALL_SOURCE}" ]; then + if [ "${NETDATA_ONLY_NATIVE}" -eq 1 ] || [ "${NETDATA_ONLY_BUILD}" -eq 1 ]; then + fatal "Offline installs are only supported for static builds currently." F0502 + fi + fi + + if [ -n "${LOCAL_BUILD_OPTIONS}" ]; then + if [ "${NETDATA_ONLY_BUILD}" -eq 1 ]; then + NETDATA_INSTALLER_OPTIONS="${NETDATA_INSTALLER_OPTIONS} ${LOCAL_BUILD_OPTIONS}" + else + fatal "Specifying local build options is only supported when the --build-only option is also specified." F0401 + fi + fi + + if [ -n "${STATIC_INSTALL_OPTIONS}" ]; then + if [ "${NETDATA_ONLY_STATIC}" -eq 1 ]; then + NETDATA_INSTALLER_OPTIONS="${NETDATA_INSTALLER_OPTIONS} ${STATIC_INSTALL_OPTIONS}" + else + fatal "Specifying installer options options is only supported when the --static-only option is also specified." F0402 + fi + fi + + if [ -n "${NETDATA_OFFLINE_INSTALL_SOURCE}" ] && [ -n "${INSTALL_VERSION}" ]; then + fatal "Specifying an install version alongside an offline install source is not supported." F050A + fi + + if [ "${NETDATA_AUTO_UPDATES}" = "default" ]; then + if [ -n "${NETDATA_OFFLINE_INSTALL_SOURCE}" ] || [ -n "${INSTALL_VERSION}" ]; then + AUTO_UPDATE=0 + else + AUTO_UPDATE=1 + fi + elif [ "${NETDATA_AUTO_UPDATES}" = 1 ]; then + AUTO_UPDATE=1 + else + AUTO_UPDATE=0 + fi + + if [ "${RELEASE_CHANNEL}" = "default" ]; then + if [ -n "${NETDATA_OFFLINE_INSTALL_SOURCE}" ]; then + SELECTED_RELEASE_CHANNEL="$(cat "${NETDATA_OFFLINE_INSTALL_SOURCE}/channel")" + + if [ -z "${SELECTED_RELEASE_CHANNEL}" ]; then + fatal "Could not find a release channel indicator in ${NETDATA_OFFLINE_INSTALL_SOURCE}." F0508 + fi + else + SELECTED_RELEASE_CHANNEL="${DEFAULT_RELEASE_CHANNEL}" + fi + else + if [ -n "${NETDATA_OFFLINE_INSTALL_SOURCE}" ] && [ "${RELEASE_CHANNEL}" != "$(cat "${NETDATA_OFFLINE_INSTALL_SOURCE}/channel")" ]; then + fatal "Release channal '${RELEASE_CHANNEL}' requested, but indicated offline installation source release channel is '$(cat "${NETDATA_OFFLINE_INSTALL_SOURCE}/channel")'." F0509 + fi + + SELECTED_RELEASE_CHANNEL="${RELEASE_CHANNEL}" + fi +} + +parse_args() { + if [ -n "${NETDATA_INSTALLER_OPTIONS}" ]; then + warning "Explicitly specifying additional installer options with NETDATA_INSTALLER_OPTIONS is deprecated. Please instead pass the options to the script using either --local-build-options or --static-install-options as appropriate." + fi + + while [ -n "${1}" ]; do + case "${1}" in + "--help") + usage + cleanup + trap - EXIT + exit 0 + ;; + "--no-cleanup") NO_CLEANUP=1 ;; + "--dont-wait"|"--non-interactive") INTERACTIVE=0 ;; + "--interactive") INTERACTIVE=1 ;; + "--dry-run") DRY_RUN=1 ;; + "--stable-channel") RELEASE_CHANNEL="stable" ;; + "--no-updates") NETDATA_AUTO_UPDATES=0 ;; + "--auto-update") NETDATA_AUTO_UPDATES="1" ;; + "--auto-update-method") + NETDATA_AUTO_UPDATE_TYPE="$(echo "${2}" | tr '[:upper:]' '[:lower:]')" + case "${NETDATA_AUTO_UPDATE_TYPE}" in + systemd|interval|crontab) + shift 1 + ;; + *) + echo "Unrecognized value for --auto-update-type. Valid values are: systemd, interval, crontab" + exit 1 + ;; + esac + ;; + "--reinstall") + NETDATA_REINSTALL=1 + NETDATA_COMMAND="reinstall" + ;; + "--reinstall-even-if-unsafe") + NETDATA_UNSAFE_REINSTALL=1 + NETDATA_COMMAND="unsafe-reinstall" + ;; + "--claim-only") + NETDATA_CLAIM_ONLY=1 + NETDATA_COMMAND="claim-only" + ;; + "--disable-cloud") + NETDATA_DISABLE_CLOUD=1 + NETDATA_REQUIRE_CLOUD=0 + ;; + "--require-cloud") + NETDATA_DISABLE_CLOUD=0 + NETDATA_REQUIRE_CLOUD=1 + ;; + "--dont-start-it") + NETDATA_NO_START=1 + NETDATA_INSTALLER_OPTIONS="${NETDATA_INSTALLER_OPTIONS} --dont-start-it" + ;; + "--disable-telemetry") + NETDATA_DISABLE_TELEMETRY="1" + NETDATA_INSTALLER_OPTIONS="${NETDATA_INSTALLER_OPTIONS} --disable-telemetry" + ;; + "--install") + warning "--install flag is deprecated and will be removed in a future version. Please use --install-prefix instead." + INSTALL_PREFIX="${2}" + shift 1 + ;; + "--install-prefix") + INSTALL_PREFIX="${2}" + shift 1 + ;; + "--old-install-prefix") + OLD_INSTALL_PREFIX="${2}" + shift 1 + ;; + "--install-version") + INSTALL_VERSION="${2}" + AUTO_UPDATE=0 + shift 1 + ;; + "--uninstall") + ACTION="uninstall" + NETDATA_COMMAND="uninstall" + ;; + "--reinstall-clean") + ACTION="reinstall-clean" + NETDATA_COMMAND="reinstall-clean" + ;; + "--repositories-only") + REPO_ACTION="repositories-only" + NETDATA_COMMAND="repositories" + ;; + "--native-only") + NETDATA_ONLY_NATIVE=1 + NETDATA_ONLY_STATIC=0 + NETDATA_ONLY_BUILD=0 + SELECTED_INSTALL_METHOD="native" + ;; + "--static-only") + NETDATA_ONLY_STATIC=1 + NETDATA_ONLY_NATIVE=0 + NETDATA_ONLY_BUILD=0 + SELECTED_INSTALL_METHOD="static" + ;; + "--build-only") + NETDATA_ONLY_BUILD=1 + NETDATA_ONLY_NATIVE=0 + NETDATA_ONLY_STATIC=0 + SELECTED_INSTALL_METHOD="build" + ;; + "--claim-token") + NETDATA_CLAIM_TOKEN="${2}" + shift 1 + ;; + "--claim-rooms") + NETDATA_CLAIM_ROOMS="${2}" + shift 1 + ;; + "--claim-url") + NETDATA_CLAIM_URL="${2}" + shift 1 + ;; + "--claim-"*) + optname="$(echo "${1}" | cut -d '-' -f 4-)" + case "${optname}" in + id|proxy|user|hostname) + NETDATA_CLAIM_EXTRA="${NETDATA_CLAIM_EXTRA} -${optname}=${2}" + shift 1 + ;; + verbose|insecure|noproxy|noreload|daemon-not-running) + NETDATA_CLAIM_EXTRA="${NETDATA_CLAIM_EXTRA} -${optname}" + ;; + *) + warning "Ignoring unrecognized claiming option ${optname}" + ;; + esac + ;; + "--local-build-options") + LOCAL_BUILD_OPTIONS="${2}" + shift 1 + ;; + "--static-install-options") + STATIC_INSTALL_OPTIONS="${2}" + shift 1 + ;; + "--prepare-offline-install-source") + if [ -n "${2}" ]; then + ACTION="prepare-offline" + NETDATA_COMMAND="prepare-offline" + OFFLINE_TARGET="${2}" + shift 1 + else + fatal "A target directory must be specified with the --prepare-offline-install-source option." F0500 + fi + ;; + "--offline-install-source") + if [ -d "${2}" ]; then + NETDATA_OFFLINE_INSTALL_SOURCE="${2}" + shift 1 + else + fatal "A source directory must be specified with the --offline-install-source option." F0501 + fi + ;; + *) + warning "Passing unrecognized option '${1}' to installer script. This behavior is deprecated and will be removed in the near future. If you intended to pass this option to the installer code, please use either --local-build-options or --static-install-options to specify it instead." + NETDATA_INSTALLER_OPTIONS="${NETDATA_INSTALLER_OPTIONS} ${1}" + ;; + esac + shift 1 + done + + validate_args +} + +# ====================================================================== +# Main program + +setup_terminal || echo > /dev/null + +# shellcheck disable=SC2068 +parse_args $@ + +confirm_root_support +get_system_info +confirm_install_prefix + +if [ -z "${ACTION}" ]; then + handle_existing_install +fi + +main diff --git a/packaging/installer/methods/cloud-providers.md b/packaging/installer/methods/cloud-providers.md new file mode 100644 index 0000000..bc5c9aa --- /dev/null +++ b/packaging/installer/methods/cloud-providers.md @@ -0,0 +1,126 @@ +<!-- +title: "Install Netdata on cloud providers" +description: "The Netdata Agent runs on all popular cloud providers, but often requires additional steps and configuration for full functionality." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/methods/cloud-providers.md +--> + +# Install Netdata on cloud providers + +Netdata is fully compatible with popular cloud providers like Google Cloud Platform (GCP), Amazon Web Services (AWS), +Azure, and others. You can install Netdata on cloud instances to monitor the apps/services running there, or use +multiple instances in a [parent-child streaming](/streaming/README.md) configuration. + +In some cases, using Netdata on these cloud providers requires unique installation or configuration steps. This page +aims to document some of those steps for popular cloud providers. + +> This document is a work-in-progress! If you find new issues specific to a cloud provider, or would like to help +> clarify the correct workaround, please [create an +> issue](https://github.com/netdata/netdata/issues/new?labels=feature+request,+needs+triage&template=feature_request.md) +> with your process and instructions on using the provider's interface to complete the workaround. + +- [Recommended installation methods for cloud providers](#recommended-installation-methods-for-cloud-providers) +- [Post-installation configuration](#post-installation-configuration) + - [Add a firewall rule to access Netdata's dashboard](#add-a-firewall-rule-to-access-netdatas-dashboard) + +## Recommended installation methods for cloud providers + +The best installation method depends on the instance's operating system, distribution, and version. For Linux instances, +we recommend the [`kickstart.sh` automatic installation script](kickstart.md). + +If you have issues with Netdata after installation, look to the sections below to find the issue you're experiencing, +followed by the solution for your provider. + +## Post-installation configuration + +Some cloud providers require you take additional steps to properly configure your instance or its networking to access +all of Netdata's features. + +### Add a firewall rule to access Netdata's dashboard + +If you cannot access Netdata's dashboard on your cloud instance via `http://HOST:19999`, and instead get an error page +from your browser that says, "This site can't be reached" (Chrome) or "Unable to connect" (Firefox), you may need to +configure your cloud provider's firewall. + +Cloud providers often create network-level firewalls that run separately from the instance itself. Both AWS and Google +Cloud Platform calls them Virtual Private Cloud (VPC) networks. These firewalls can apply even if you've disabled +firewalls on the instance itself. Because you can modify these firewalls only via the cloud provider's web interface, +it's easy to overlook them when trying to configure and access Netdata's dashboard. + +You can often confirm a firewall issue by querying the dashboard while connected to the instance via SSH: `curl +http://localhost:19999/api/v1/info`. If you see JSON output, Netdata is running properly. If you try the same `curl` +command from a remote system, and it fails, it's likely that a firewall is blocking your requests. + +Another option is to put Netdata behind web server, which will proxy requests through standard HTTP/HTTPS ports +(80/443), which are likely already open on your instance. We have a number of guides available: + +- [Apache](/docs/Running-behind-apache.md) +- [Nginx](/docs/Running-behind-nginx.md) +- [Caddy](/docs/Running-behind-caddy.md) +- [HAProxy](/docs/Running-behind-haproxy.md) +- [lighttpd](/docs/Running-behind-lighttpd.md) + +The next few sections outline how to add firewall rules to GCP, AWS, and Azure instances. + +#### Google Cloud Platform (GCP) + +To add a firewall rule, go to the [Firewall rules page](https://console.cloud.google.com/networking/firewalls/list) and +click **Create firewall rule**. + +The following configuration has previously worked for Netdata running on GCP instances +([see #7786](https://github.com/netdata/netdata/issues/7786)): + +```conf +Name: <name> +Type: Ingress +Targets: <name-tag> +Filters: 0.0.0.0/0 +Protocols/ports: 19999 +Action: allow +Priority: 1000 +``` + +Read GCP's [firewall documentation](https://cloud.google.com/vpc/docs/using-firewalls) for specific instructions on how +to create a new firewall rule. + +#### Amazon Web Services (AWS) / EC2 + +Sign in to the [AWS console](https://console.aws.amazon.com/) and navigate to the EC2 dashboard. Click on the **Security +Groups** link in the navigation, beneath the **Network & Security** heading. Find the Security Group your instance +belongs to, and either right-click on it or click the **Actions** button above to see a dropdown menu with **Edit +inbound rules**. + +Add a new rule with the following options: + +```conf +Type: Custom TCP +Protocol: TCP +Port Range: 19999 +Source: Anywhere +Description: Netdata +``` + +You can also choose **My IP** as the source if you prefer. + +Click **Save** to apply your new inbound firewall rule. + +#### Azure + +Sign in to the [Azure portal](https://portal.azure.com) and open the virtual machine running Netdata. Click on the +**Networking** link beneath the **Settings** header, then click on the **Add inbound security rule** button. + +Add a new rule with the following options: + +```conf +Source: Any +Source port ranges: 19999 +Destination: Any +Destination port ranges: 19999 +Protocol: TCP +Action: Allow +Priority: 310 +Name: Netdata +``` + +Click **Add** to apply your new inbound security rule. + + diff --git a/packaging/installer/methods/freebsd.md b/packaging/installer/methods/freebsd.md new file mode 100644 index 0000000..3523157 --- /dev/null +++ b/packaging/installer/methods/freebsd.md @@ -0,0 +1,107 @@ +<!-- +title: "Install Netdata on FreeBSD" +description: "Install Netdata on FreeBSD to monitor the health and performance of bare metal or VMs with thousands of real-time, per-second metrics." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/methods/freebsd.md +--> + +# Install Netdata on FreeBSD + +> 💡 This document is maintained by Netdata's community, and may not be completely up-to-date. Please double-check the +> details of the installation process, such as version numbers for downloadable packages, before proceeding. +> +> You can help improve this document by [submitting a +> PR](https://github.com/netdata/netdata/edit/master/packaging/installer/methods/freebsd.md) with your recommended +> improvements or changes. Thank you! + +## Install latest version + +This is how to install the latest Netdata version on FreeBSD: + +Install required packages (**need root permission**): + +```sh +pkg install bash e2fsprogs-libuuid git curl autoconf automake pkgconf pidof liblz4 libuv json-c cmake gmake +``` + +Download Netdata: + +```sh +fetch https://github.com/netdata/netdata/releases/download/v1.26.0/netdata-v1.26.0.tar.gz +``` + +> ⚠️ Verify the latest version by either navigating to [Netdata's latest +> release](https://github.com/netdata/netdata/releases/latest) or using `curl`: +> +> ```bash +> basename $(curl -Ls -o /dev/null -w %{url_effective} https://github.com/netdata/netdata/releases/latest) +> ``` + +Unzip the downloaded file: + +```sh +gunzip netdata*.tar.gz && tar xf netdata*.tar && rm -rf netdata*.tar +``` + +Install Netdata in `/opt/netdata`. If you want to enable automatic updates, add `--auto-update` or `-u` to install `netdata-updater` in `cron` (**need root permission**): + +```sh +cd netdata-v* && ./netdata-installer.sh --install /opt && cp /opt/netdata/usr/sbin/netdata-claim.sh /usr/sbin/ +``` + +You also need to enable the `netdata` service in `/etc/rc.conf`: + +```sh +sysrc netdata_enable="YES" +``` + +Finally, and very importantly, update Netdata using the script provided by the Netdata team (**need root permission**): + +```sh +cd /opt/netdata/usr/libexec/netdata/ && ./netdata-updater.sh +``` + +You can now access the Netdata dashboard by navigating to `http://NODE:19999`, replacing `NODE` with the IP address or hostname of your system. + + + +Starting with v1.30, Netdata collects anonymous usage information by default and sends it to a self hosted PostHog instance within the Netdata infrastructure. To read +more about the information collected and how to opt-out, check the [anonymous statistics +page](/docs/anonymous-statistics.md). + +## Updating the Agent on FreeBSD +If you have not passed the `--auto-update` or `-u` parameter for the installer to enable automatic updating, repeat the last step to update Netdata whenever a new version becomes available. +The `netdata-updater.sh` script will update your Agent. + +## Optional parameters to alter your installation +| parameters | Description | +|:-----:|-----------| +|`--install <path>`| Install netdata in `<path>.` Ex: `--install /opt` will put netdata in `/opt/netdata`| +| `--dont-start-it` | Do not (re)start netdata after installation| +| `--dont-wait` | Run installation in non-interactive mode| +| `--auto-update` or `-u` | Install netdata-updater in cron to update netdata automatically once per day| +| `--stable-channel` | Use packages from GitHub release pages instead of GCS (nightly updates). This results in less frequent updates| +| `--nightly-channel` | Use most recent nightly updates instead of GitHub releases. This results in more frequent updates| +| `--disable-go` | Disable installation of go.d.plugin| +| `--disable-ebpf` | Disable eBPF Kernel plugin (Default: enabled)| +| `--disable-cloud` | Disable all Netdata Cloud functionality| +| `--require-cloud` | Fail the install if it can't build Netdata Cloud support| +| `--enable-plugin-freeipmi` | Enable the FreeIPMI plugin. Default: enable it when libipmimonitoring is available| +| `--disable-plugin-freeipmi` | Enable the FreeIPMI plugin| +| `--disable-https` | Explicitly disable TLS support| +| `--disable-dbengine` | Explicitly disable DB engine support| +| `--enable-plugin-nfacct` | Enable nfacct plugin. Default: enable it when libmnl and libnetfilter_acct are available| +| `--disable-plugin-nfacct` | Disable nfacct plugin. Default: enable it when libmnl and libnetfilter_acct are available| +| `--enable-plugin-xenstat` | Enable the xenstat plugin. Default: enable it when libxenstat and libyajl are available| +| `--disable-plugin-xenstat` | Disable the xenstat plugin| +| `--disable-exporting-kinesis` | Disable AWS Kinesis exporting connector. Default: enable it when libaws_cpp_sdk_kinesis and libraries (it depends on are available)| +| `--enable-exporting-prometheus-remote-write` | Enable Prometheus remote write exporting connector. Default: enable it when libprotobuf and libsnappy are available| +| `--disable-exporting-prometheus-remote-write` | Disable Prometheus remote write exporting connector. Default: enable it when libprotobuf and libsnappy are available| +| `--enable-exporting-mongodb` | Enable MongoDB exporting connector. Default: enable it when libmongoc is available| +| `--disable-exporting-mongodb` | Disable MongoDB exporting connector| +| `--enable-lto` | Enable Link-Time-Optimization. Default: enabled| +| `--disable-lto` | Disable Link-Time-Optimization. Default: enabled| +| `--disable-x86-sse` | Disable SSE instructions. By default SSE optimizations are enabled| +| `--zlib-is-really-here` or `--libs-are-really-here` | If you get errors about missing zlib or libuuid but you know it is available, you might have a broken pkg-config. Use this option to proceed without checking pkg-config| +|`--disable-telemetry` | Use this flag to opt-out from our anonymous telemetry program. (DISABLE_TELEMETRY=1)| + + diff --git a/packaging/installer/methods/freenas.md b/packaging/installer/methods/freenas.md new file mode 100644 index 0000000..a69f1e3 --- /dev/null +++ b/packaging/installer/methods/freenas.md @@ -0,0 +1,24 @@ +<!-- +title: "Install Netdata on FreeNAS" +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/methods/freenas.md +--> + +# Install Netdata on FreeNAS + +On FreeNAS-Corral-RELEASE (>=10.0.3 and <11.3), Netdata is pre-installed. + +To use Netdata, the service will need to be enabled and started from the FreeNAS [CLI](https://github.com/freenas/cli). + +To enable the Netdata service: + +```sh +service netdata config set enable=true +``` + +To start the Netdata service: + +```sh +service netdata start +``` + + diff --git a/packaging/installer/methods/kickstart.md b/packaging/installer/methods/kickstart.md new file mode 100644 index 0000000..2555e4a --- /dev/null +++ b/packaging/installer/methods/kickstart.md @@ -0,0 +1,172 @@ +<!-- +title: "Install Netdata with kickstart.sh" +description: "The kickstart.sh script installs Netdata from source, including all dependencies required to connect to Netdata Cloud, with a single command." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/methods/kickstart.md +--> +import { OneLineInstallWget, OneLineInstallCurl } from '@site/src/components/OneLineInstall/' + +# Install Netdata with kickstart.sh + +  + +This page covers detailed instructions on using and configuring the automatic one-line installation script named +`kickstart.sh`. + +The kickstart script works on all Linux distributions and macOS environments. By default, automatic nightly updates are enabled. If you are installing on macOS, make sure to check the [install documentation for macOS](macos.md) before continuing. + +> If you are unsure whether you want nightly or stable releases, read the [installation guide](/packaging/installer/README.md#nightly-vs-stable-releases). +> If you want to turn off [automatic updates](/packaging/installer/README.md#automatic-updates), use the `--no-updates` option. You can find more installation options below. + +To install Netdata, run the following as your normal user: + +<OneLineInstallWget/> + +Or, if you have cURL but not wget (such as on macOS): + +<OneLineInstallCurl/> + + +## What does `kickstart.sh` do? + +The `kickstart.sh` script does the following after being downloaded and run using `sh`: + +- Determines what platform you are running on. +- Checks for an existing installation, and if found updates that instead of creating a new install. +- Attempts to install Netdata using our [official native binary packages](#native-packages). +- If there are no official native binary packages for your system (or installing that way failed), tries to install + using a [static build of Netdata](#static-builds) if one is available. +- If no static build is available, installs required dependencies and then attempts to install by + [building Netdata locally](#local-builds) (by downloading the sources and building them directly). +- Installs `netdata-updater.sh` to `cron.daily`, so your Netdata installation will be updated with new nightly + versions, unless you override that with an [optional parameter](#optional-parameters-to-alter-your-installation). +- Prints a message whether installation succeeded or failed for QA purposes. + +## Optional parameters to alter your installation + +The `kickstart.sh` script accepts a number of optional parameters to control how the installation process works: + +- `--non-interactive`: Don’t prompt for anything and assume yes whenever possible, overriding any automatic detection of an interactive run. +- `--interactive`: Act as if running interactively, even if automatic detection indicates a run is non-interactive. +- `--dont-wait`: Synonym for `--non-interactive` +- `--dry-run`: Show what the installer would do, but don’t actually do any of it. +- `--dont-start-it`: Don’t auto-start the daemon after installing. This parameter is not guaranteed to work. +- `--release-channel`: Specify a particular release channel to install from. Currently supported release channels are: + - `nightly`: Installs a nightly build (this is currently the default). + - `stable`: Installs a stable release. + - `default`: Explicitly request whatever the current default is. +- `--nightly-channel`: Synonym for `--release-channel nightly`. +- `--stable-channel`: Synonym for `--release-channel stable`. +- `--auto-update`: Enable automatic updates (this is the default). +- `--no-updates`: Disable automatic updates. +- `--disable-telemetry`: Disable anonymous statistics. +- `--repositories-only`: Only install appropriate repository configuration packages (only for native install). +- `--native-only`: Only install if native binary packages are available. +- `--static-only`: Only install if a static build is available. +- `--build-only`: Only install using a local build. +- `--reinstall`: If an existing install is found, reinstall instead of trying to update it in place. +- `--reinstall-even-if-unsafe`: Even try to reinstall if we don't think we can do so safely (implies `--reinstall`). +- `--disable-cloud`: For local builds, don’t build any of the cloud code at all. For native packages and static builds, + use runtime configuration to disable cloud support. +- `--require-cloud`: Only install if Netdata Cloud can be enabled. Overrides `--disable-cloud`. +- `--install`: Specify an installation prefix for local builds (by default, we use a sane prefix based on the type of system), this option is deprecated and will be removed in a future version, please use `--install-prefix` instead. +- `--install-prefix`: Specify an installation prefix for local builds (by default, we use a sane prefix based on the type of system). +- `--install-version`: Specify the version of Netdata to install. +- `--old-install-prefix`: Specify the custom local build's installation prefix that should be removed. +- `--uninstall`: Uninstall an existing installation of Netdata. +- `--reinstall-clean`: Performs an uninstall of Netdata and clean installation. +- `--local-build-options`: Specify additional options to pass to the installer code when building locally. Only valid if `--build-only` is also specified. +- `--static-install-options`: Specify additional options to pass to the static installer code. Only valid if --static-only is also specified. +- `--prepare-offline-install-source`: Instead of insallling the agent, prepare a directory that can be used to install on another system without needing to download anything. See our [offline installation documentation](/packaging/installer/methods/offline.md) for more info. + +Additionally, the following environment variables may be used to further customize how the script runs (most users +should not need to use special values for any of these): + +- `TMPDIR`: Used to specify where to put temporary files. On most systems, the default we select automatically + should be fine. The user running the script needs to both be able to write files to the temporary directory, + and run files from that location. +- `ROOTCMD`: Used to specify a command to use to run another command with root privileges if needed. By default + we try to use sudo, doas, or pkexec (in that order of preference), but if you need special options for one of + those to work, or have a different tool to do the same thing on your system, you can specify it here. +- `DISABLE_TELEMETRY`: If set to a value other than 0, behave as if `--disable-telemetry` was specified. + +### Connect node to Netdata Cloud during installation + +The `kickstart.sh` script accepts additional parameters to automatically [connect](/claim/README.md) your node to Netdata Cloud immediately after installation. + +> Note: You either need to run the command with root privileges or run it with the user that is running the agent. More details: [Connect an agent without root privileges](/claim/README.md#connect-an-agent-without-root-privileges) section. + +To automatically claim nodes after installation: + +1. Sign in to [Netdata Cloud](https://app.netdata.cloud/sign-in?cloudRoute=/spaces) +2. Go to the [Spaces management area](https://learn.netdata.cloud/docs/cloud/spaces#manage-spaces) +3. Click on **Connect Nodes** +4. Find the `token` and `rooms` strings and specify your nodes: + +- `--claim-token`: Specify a unique claiming token associated with your Space in Netdata Cloud to be used to connect to the node + after the install. +- `--claim-rooms`: Specify a comma-separated list of tokens for each War Room this node should appear in. +- `--claim-proxy`: Specify a proxy to use when connecting to the cloud in the form of `http://[user:pass@]host:ip` for an HTTP(S) proxy. + See [connecting through a proxy](/claim/README.md#connect-through-a-proxy) for details. +- `--claim-url`: Specify a URL to use when connecting to the cloud. Defaults to `https://api.netdata.cloud`. + +For example: + +```bash +wget -O /tmp/netdata-kickstart.sh https://my-netdata.io/kickstart.sh && sh /tmp/netdata-kickstart.sh --claim-token TOKEN --claim-rooms ROOM1,ROOM2 +``` + +### Native packages + +We publish official DEB/RPM packages for a number of common Linux distributions as part of our releases and nightly +builds. These packages are available for 64-bit x86 systems. Depending on the distribution and release they may +also be available for 32-bit x86, ARMv7, and AArch64 systems. If a native package is available, it will be used as the +default installation method. This allows you to handle Netdata updates as part of your usual system update procedure. + +If you want to enforce the usage of native packages and have the installer return a failure if they are not available, +you can do so by adding `--native-only` to the options you pass to the installer. + +### Static builds + +We publish pre-built static builds of Netdata for Linux systems. Currently, these are published for 64-bit x86, ARMv7, +AArch64, and POWER8+ hardware. These static builds are able to operate in a mostly self-contained manner and only +require a POSIX compliant shell and a supported init system. These static builds install under `/opt/netdata`. If +you are on a platform which we provide static builds for but do not provide native packages for, a static build +will be used by default for installation. + +If you want to enforce the usage of a static build and have the installer return a failure if one is not available, +you can do so by adding `--static-only` to the options you pass to the installer. + +### Local builds + +For systems which do not have available native packages or static builds, we support building Netdata locally on +the system it will be installed on. When using this approach, the installer will attempt to install any required +dependencies for building Netdata, though this may not always work correctly. + +If you want to enforce the usage of a local build (perhaps because you require a custom installation prefix, +which is not supported with native packages or static builds), you can do so by adding `--build-only` to the +options you pass to the installer. + + +## Verify script integrity + +To use `md5sum` to verify the integrity of the `kickstart.sh` script you will download using the one-line command above, +run the following: + +```bash +[ "<checksum-will-be-added-in-documentation-processing>" = "$(curl -Ss https://my-netdata.io/kickstart.sh | md5sum | cut -d ' ' -f 1)" ] && echo "OK, VALID" || echo "FAILED, INVALID" +``` + +If the script is valid, this command will return `OK, VALID`. + +## What's next? + +When you're finished with installation, check out our [single-node](/docs/quickstart/single-node.md) or +[infrastructure](/docs/quickstart/infrastructure.md) monitoring quickstart guides based on your use case. + +Or, skip straight to [configuring the Netdata Agent](/docs/configure/nodes.md). + +Read through Netdata's [documentation](https://learn.netdata.cloud/docs), which is structured based on actions and +solutions, to enable features like health monitoring, alarm notifications, long-term metrics storage, exporting to +external databases, and more. + + diff --git a/packaging/installer/methods/kubernetes.md b/packaging/installer/methods/kubernetes.md new file mode 100644 index 0000000..216703a --- /dev/null +++ b/packaging/installer/methods/kubernetes.md @@ -0,0 +1,197 @@ +<!-- +title: "Deploy Kubernetes monitoring with Netdata" +description: "Deploy Netdata to monitor a Kubernetes cluster to monitor the health, performance, resource utilization, and application metrics of a Kubernetes cluster in real time." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/methods/kubernetes.md +--> + +# Deploy Kubernetes monitoring with Netdata + +This document details how to install Netdata on an existing Kubernetes (k8s) cluster. By following these directions, you +will use Netdata's [Helm chart](https://github.com/netdata/helmchart) to create a Kubernetes monitoring deployment on +your cluster. + +The Helm chart installs one `parent` pod for storing metrics and managing alarm notifications, plus an additional +`child` pod for every node in the cluster, responsible for collecting metrics from the node, Kubernetes control planes, +pods/containers, and [supported application-specific +metrics](https://github.com/netdata/helmchart#service-discovery-and-supported-services). + +To deploy Kubernetes monitoring with Netdata, you need: + +- A working cluster running Kubernetes v1.9 or newer. +- The [kubectl](https://kubernetes.io/docs/reference/kubectl/overview/) command line tool, within [one minor version + difference](https://kubernetes.io/docs/tasks/tools/install-kubectl/#before-you-begin) of your cluster, on an + administrative system. +- The [Helm package manager](https://helm.sh/) v3.0.0 or newer on the same administrative system. + +## Install the Netdata Helm chart + +We recommend you install the Helm chart using our Helm repository. In the `helm install` command, replace `netdata` with +the release name of your choice. + +```bash +helm repo add netdata https://netdata.github.io/helmchart/ +helm install netdata netdata/netdata +``` + +Run `kubectl get services` and `kubectl get pods` to confirm that your cluster now runs a `netdata` service, one +parent pod, and multiple child pods. + +You've now installed Netdata on your Kubernetes cluster. Next, it's time to opt-in and enable the powerful Kubernetes +dashboards available in Netdata Cloud. + +## Connect your Kubernetes cluster to Netdata Cloud + +To start [Kubernetes monitoring](https://learn.netdata.cloud/docs/cloud/visualize/kubernetes/), you must first +[connect](/claim/README.md) your Kubernetes cluster to [Netdata Cloud](https://app.netdata.cloud). The connection process securely +connects your Kubernetes cluster to stream metrics data to Netdata Cloud, enabling Kubernetes-specific visualizations +like the health map and time-series composite charts. + +### New installations + +First, find the script to run an `helm install` command. You can get it by clicking on your Space's dropdown, then **Manage your Space**. +Click the **Nodes** tab and select the environment your node is running, in this case **kubernetes**, to reveal the script for your Space in Netdata Cloud. You need the `TOKEN` +and `ROOM` values. + +The script should be similar to: + +```bash +helm install netdata netdata/netdata --set parent.claiming.enabled="true" --set parent.claiming.token="TOKEN" --set parent.claiming.rooms="ROOM" --set child.claiming.enabled=true --set child.claiming.token="TOKEN" --set child.claiming.rooms="ROOM" +``` + +### Existing installations + +On an existing installation, you will need to override the configuration values by running the `helm upgrade` command and provide a file with the values to override. You can start with creating a file called `override.yml`. + +```bash +touch override.yml +``` + +Paste the following into your `override.yml` file, replacing instances of `ROOM` and `TOKEN` with those from the script from Netdata Cloud. These settings connect your `parent`/`child` nodes to Netdata Cloud and store more +metrics in the nodes' time-series databases. + +```yaml +parent: + claiming: + enabled: true + token: "TOKEN" + rooms: "ROOM" + +child: + claiming: + enabled: true + token: "TOKEN" + rooms: "ROOM" + configs: + netdata: + data: | + [global] + memory mode = ram + history = 3600 + [health] + enabled = no +``` + +> ❗ These override settings, along with the Helm chart's defaults, will retain an hour's worth of metrics (`history = +> 3600`, or `3600 seconds`) on each child node. Based on your metrics retention needs, and the resources available on +> your cluster, you may want to increase the `history` setting. + +Apply these new settings: + +```bash +helm upgrade -f override.yml netdata netdata/netdata +``` + +The cluster terminates the old pods and creates new ones with the proper persistence and connection configuration. You'll +see your nodes, containers, and pods appear in Netdata Cloud in a few seconds. + +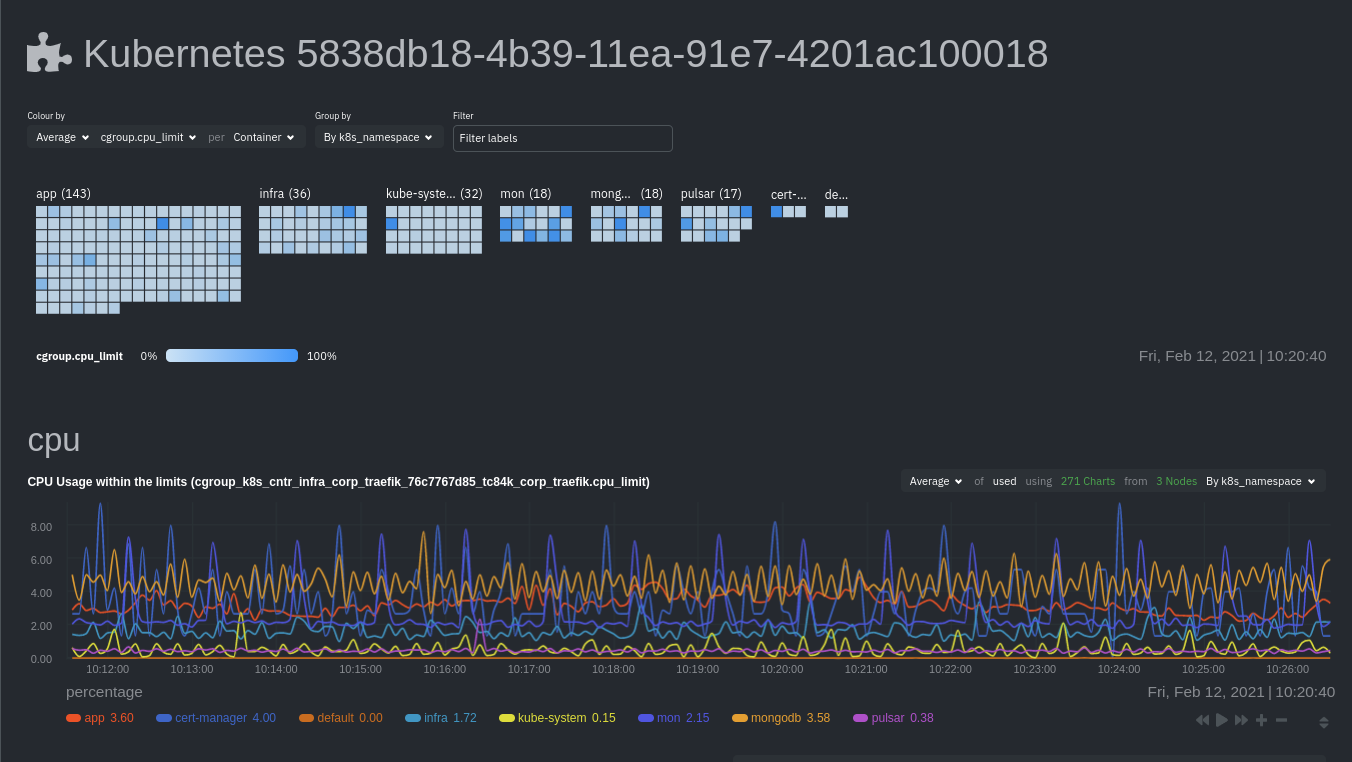 + +If you don't need to configure your Netdata deployment, [skip down](#whats-next) to see how Kubernetes monitoring works +in Netdata, in addition to more guides and resources. + +## Configure your Netdata monitoring deployment + +Read up on the various configuration options in the [Helm chart +documentation](https://github.com/netdata/helmchart#configuration) if you need to tweak your Kubernetes monitoring. + +Your first option is to create an `override.yml` file, if you haven't created one already for +[connect](#connect-your-kubernetes-cluster-to-netdata-cloud), then apply the new configuration to your cluster with `helm +upgrade`. + +```bash +helm upgrade -f override.yml netdata netdata/netdata +``` + +If you want to change only a single setting, use the `--set` argument with `helm upgrade`. For example, to change the +size of the persistent metrics volume on the parent node: + +```bash +helm upgrade --set parent.database.volumesize=4Gi netdata netdata/netdata +``` + +### Configure service discovery + +Netdata's [service discovery](https://github.com/netdata/agent-service-discovery/#service-discovery), installed as part +of the Helm chart installation, finds what services are running in a cluster's containers and automatically collects +service-level metrics from them. + +Service discovery supports [popular applications](https://github.com/netdata/helmchart#applications) and [Prometheus +endpoints](https://github.com/netdata/helmchart#prometheus-endpoints). + +If your cluster runs services on non-default ports or uses non-default names, you may need to configure service +discovery to start collecting metrics from your services. You have to edit the default ConfigMap that is shipped with +the Helmchart and deploy that to your cluster. + +First, copy the default file to your administrative system. + +```bash +curl https://raw.githubusercontent.com/netdata/helmchart/master/charts/netdata/sdconfig/child.yml -o child.yml +``` + +Edit the new `child.yml` file according to your needs. See the [Helm chart +configuration](https://github.com/netdata/helmchart#configuration) and the file itself for details. + +You can then run `helm upgrade` with the `--set-file` argument to use your configured `child.yml` file instead of the +default, changing the path if you copied it elsewhere. + +```bash +helm upgrade --set-file sd.child.configmap.from.value=./child.yml netdata netdata/netdata +``` + +Now that you pushed an edited ConfigMap to your cluster, service discovery should find and set up metrics collection +from your non-default service. + +## Update/reinstall the Netdata Helm chart + +If you update the Helm chart's configuration, run `helm upgrade` to redeploy your Netdata service, replacing `netdata` +with the name of the release, if you changed it upon installation: + +```bash +helm upgrade netdata netdata/netdata +``` + +To update Netdata's Helm chart to the latest version, run `helm repo update`, then deploy `upgrade` it`: + +```bash +helm repo update +helm upgrade netdata netdata/netdata +``` + +## What's next? + +[Start Kubernetes monitoring](https://learn.netdata.cloud/docs/cloud/visualize/kubernetes/) in Netdata Cloud, which +comes with meaningful visualizations out of the box. + +Read our guide, [_Kubernetes monitoring with Netdata: Overview and +visualizations_](/docs/guides/monitor/kubernetes-k8s-netdata.md), for a complete walkthrough of Netdata's Kubernetes +monitoring capabilities, including a health map of every container in your infrastructure, aggregated resource +utilization metrics, and application metrics. + +### Related reference documentation + +- [Netdata Cloud · Kubernetes monitoring](https://learn.netdata.cloud/docs/cloud/visualize/kubernetes/) +- [Netdata Helm chart](https://github.com/netdata/helmchart) +- [Netdata service discovery](https://github.com/netdata/agent-service-discovery/) + + diff --git a/packaging/installer/methods/macos.md b/packaging/installer/methods/macos.md new file mode 100644 index 0000000..a1b5f60 --- /dev/null +++ b/packaging/installer/methods/macos.md @@ -0,0 +1,111 @@ +<!-- +title: "Install Netdata on macOS" +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/methods/macos.md +--> + +# Install Netdata on macOS + +Netdata works on macOS, albeit with some limitations. +The number of charts displaying system metrics is limited, but you can use any of Netdata's [external plugins](/collectors/plugins.d/README.md) to monitor any services you might have installed on your macOS system. +You could also use a macOS system as the parent node in a [streaming configuration](/streaming/README.md). + +You can install Netdata in one of the three following ways: + +- **[Install Netdata with the our automatic one-line installation script (recommended)](#install-netdata-with-our-automatic-one-line-installation-script)**, +- [Install Netdata via Homebrew](#install-netdata-via-homebrew) +- [Install Netdata from source](#install-netdata-from-source) + +Each of these installation option requires [Homebrew](https://brew.sh/) for handling dependencies. + +> The Netdata Homebrew package is community-created and -maintained. +> Community-maintained packages _may_ receive support from Netdata, but are only a best-effort affair. Learn more about [Netdata's platform support policy](/packaging/PLATFORM_SUPPORT.md). + +## Install Netdata with our automatic one-line installation script + +**Local Netdata Agent installation** +To install Netdata using our automatic [kickstart](/packaging/installer/README.md#automatic-one-line-installation-script) open a new terminal and run: + +```bash +curl https://my-netdata.io/kickstart.sh > /tmp/netdata-kickstart.sh && sh /tmp/netdata-kickstart.sh +``` +The Netdata Agent is installed under `/usr/local/netdata`. Dependencies are handled via Homebrew. + +**Automatically connect to Netdata Cloud during installation** +<!-- Potential reuse: https://learn.netdata.cloud/docs/agent/claim#connect-an-agent-running-in-macos--> +<!--Potential reuse https://learn.netdata.cloud/docs/agent/packaging/installer/methods/kickstart#connect-node-to-netdata-cloud-during-installation The following information is copied from this link.--> + +The `kickstart.sh` script accepts additional parameters to automatically [connect](/claim/README.md) your node to Netdata +Cloud immediately after installation. Find the `token` and `rooms` strings by [signing in to Netdata +Cloud](https://app.netdata.cloud/sign-in?cloudRoute=/spaces), then clicking on **Connect Nodes** in the [Spaces management +area](https://learn.netdata.cloud/docs/cloud/spaces#manage-spaces). + +- `--claim-token`: Specify a unique claiming token associated with your Space in Netdata Cloud to be used to connect to the node + after the install. +- `--claim-rooms`: Specify a comma-separated list of tokens for each War Room this node should appear in. +- `--claim-proxy`: Specify a proxy to use when connecting to the cloud in the form of `http://[user:pass@]host:ip` for an HTTP(S) proxy. + See [connecting through a proxy](/claim/README.md#connect-through-a-proxy) for details. +- `--claim-url`: Specify a URL to use when connecting to the cloud. Defaults to `https://api.netdata.cloud`. + +For example: +```bash +curl https://my-netdata.io/kickstart.sh > /tmp/netdata-kickstart.sh && sh /tmp/netdata-kickstart.sh --install /usr/local/ --claim-token TOKEN --claim-rooms ROOM1,ROOM2 --claim-url https://api.netdata.cloud +``` +The Netdata Agent is installed under `/usr/local/netdata` on your machine. Your machine will also show up as a node in your Netdata Cloud. + +If you experience issues while claiming your node, follow the steps in our [Troubleshooting](/claim/README.md#troubleshooting) documentation. +## Install Netdata via Homebrew + +To install Netdata and all its dependencies, run Homebrew using the following command: + +```sh +brew install netdata +``` +Homebrew will place your Netdata configuration directory at `/usr/local/etc/netdata/`. + +Use the `edit-config` script and the files in this directory to configure Netdata. For reference, you can find stock configuration files at `/usr/local/Cellar/netdata/{NETDATA_VERSION}/lib/netdata/conf.d/`. + +Skip on ahead to the [What's next?](#whats-next) section to find links to helpful post-installation guides. + +## Install Netdata from source + +We don't recommend installing Netdata from source on macOS, as it can be difficult to configure and install dependencies manually. + +1. Open your terminal of choice and install the Xcode development packages: + + ```bash + xcode-select --install + ``` + +2. Click **Install** on the Software Update popup window that appears. +3. Use the same terminal session to install some of Netdata's prerequisites using Homebrew. If you don't want to use [Netdata Cloud](https://learn.netdata.cloud/docs/cloud/), you can omit `cmake`. + + ```bash + brew install ossp-uuid autoconf automake pkg-config libuv lz4 json-c openssl libtool cmake + ``` + +4. Download Netdata from our GitHub repository: + + ```bash + git clone https://github.com/netdata/netdata.git --recursive + ``` + +5. `cd` into the newly-created directory and then start the installer script: + + ```bash + cd netdata/ + sudo ./netdata-installer.sh --install /usr/local + ``` + +> Your Netdata configuration directory will be at `/usr/local/netdata/`. +> Your stock configuration directory will be at `/usr/local/lib/netdata/conf.d/`. +> The installer will also install a startup plist to start Netdata when your macOS system boots. + +## What's next? + +When you're finished with installation, check out our [single-node](/docs/quickstart/single-node.md) or +[infrastructure](/docs/quickstart/infrastructure.md) monitoring quickstart guides based on your use case. + +Or, skip straight to [configuring the Netdata Agent](/docs/configure/nodes.md). + + + diff --git a/packaging/installer/methods/manual.md b/packaging/installer/methods/manual.md new file mode 100644 index 0000000..d320753 --- /dev/null +++ b/packaging/installer/methods/manual.md @@ -0,0 +1,240 @@ +<!-- +title: "Install Netdata on Linux from a Git checkout" +description: "Use the Netdata Agent source code from GitHub, plus helper scripts to set up your system, to install Netdata without packages or binaries." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/methods/manual.md +--> + +# Install Netdata on Linux from a Git checkout + +To install the latest git version of Netdata, please follow these 2 steps: + +1. [Prepare your system](#prepare-your-system) + + Install the required packages on your system. + +2. [Install Netdata](#install-netdata) + + Download and install Netdata. You can also update it the same way. + +## Prepare your system + +Use our automatic requirements installer (_no need to be `root`_), which attempts to find the packages that +should be installed on your system to build and run Netdata. It supports a large variety of major Linux distributions +and other operating systems and is regularly tested. You can find this tool [here](https://raw.githubusercontent.com/netdata/netdata/master/packaging/installer/install-required-packages.sh) or run it directly with `bash <(curl -sSL https://raw.githubusercontent.com/netdata/netdata/master/packaging/installer/install-required-packages.sh)`. Otherwise read on for how to get requires packages manually: + +- **Alpine** Linux and its derivatives + - You have to install `bash` yourself, before using the installer. + +- **Gentoo** Linux and its derivatives + +- **Debian** Linux and its derivatives (including **Ubuntu**, **Mint**) + +- **Red Hat Enterprise Linux** and its derivatives (including **Fedora**, **CentOS**, **Amazon Machine Image**) + - Please note that for RHEL/CentOS you need + [EPEL](http://www.tecmint.com/how-to-enable-epel-repository-for-rhel-centos-6-5/). + In addition, RHEL/CentOS version 6 also need + [OKay](https://okay.com.mx/blog-news/rpm-repositories-for-centos-6-and-7.html) for package libuv version 1. + - CentOS 8 / RHEL 8 requires a bit of extra work. See the dedicated section below. + +- **SUSE** Linux and its derivatives (including **openSUSE**) + +- **SLE12** Must have your system registered with SUSE Customer Center or have the DVD. See + [#1162](https://github.com/netdata/netdata/issues/1162) + +Install the packages for having a **basic Netdata installation** (system monitoring and many applications, without `mysql` / `mariadb`, `named`, hardware sensors and `SNMP`): + +```sh +curl -Ss 'https://raw.githubusercontent.com/netdata/netdata/master/packaging/installer/install-required-packages.sh' >/tmp/install-required-packages.sh && bash /tmp/install-required-packages.sh -i netdata +``` + +Install all the required packages for **monitoring everything Netdata can monitor**: + +```sh +curl -Ss 'https://raw.githubusercontent.com/netdata/netdata/master/packaging/installer/install-required-packages.sh' >/tmp/install-required-packages.sh && bash /tmp/install-required-packages.sh -i netdata-all +``` + +If the above do not work for you, please [open a github +issue](https://github.com/netdata/netdata/issues/new?title=packages%20installer%20failed&labels=installation%20help&body=The%20experimental%20packages%20installer%20failed.%0A%0AThis%20is%20what%20it%20says:%0A%0A%60%60%60txt%0A%0Aplease%20paste%20your%20screen%20here%0A%0A%60%60%60) +with a copy of the message you get on screen. We are trying to make it work everywhere (this is also why the script +[reports back](https://github.com/netdata/netdata/issues/2054) success or failure for all its runs). + +--- + +This is how to do it by hand: + +```sh +# Debian / Ubuntu +apt-get install zlib1g-dev uuid-dev libuv1-dev liblz4-dev libssl-dev libelf-dev libmnl-dev libprotobuf-dev protobuf-compiler gcc g++ make git autoconf autoconf-archive autogen automake pkg-config curl python cmake + +# Fedora +dnf install zlib-devel libuuid-devel libuv-devel lz4-devel openssl-devel elfutils-libelf-devel libmnl-devel protobuf-devel protobuf-compiler gcc gcc-c++ make git autoconf autoconf-archive autogen automake pkgconfig curl findutils python cmake + +# CentOS / Red Hat Enterprise Linux +yum install autoconf automake curl gcc gcc-c++ git libmnl-devel libuuid-devel openssl-devel libuv-devel lz4-devel elfutils-libelf-devel protobuf protobuf-devel protobuf-compiler make nc pkgconfig python zlib-devel cmake + +# openSUSE +zypper install zlib-devel libuuid-devel libuv-devel liblz4-devel libopenssl-devel libelf-devel libmnl-devel protobuf-devel gcc gcc-c++ make git autoconf autoconf-archive autogen automake pkgconfig curl findutils python cmake +``` + +Once Netdata is compiled, to run it the following packages are required (already installed using the above commands): + +| package | description| +|:-----:|-----------| +| `libuuid` | part of `util-linux` for GUIDs management| +| `zlib` | gzip compression for the internal Netdata web server| +| `libuv` | Multi-platform support library with a focus on asynchronous I/O, version 1 or greater| + +*Netdata will fail to start without the above.* + +Netdata plugins and various aspects of Netdata can be enabled or benefit when these are installed (they are optional): + +| package |description| +|:-----:|-----------| +| `bash`|for shell plugins and **alarm notifications**| +| `curl`|for shell plugins and **alarm notifications**| +| `iproute` or `iproute2`|for monitoring **Linux traffic QoS**<br/>use `iproute2` if `iproute` reports as not available or obsolete| +| `python`|for most of the external plugins| +| `python-yaml`|used for monitoring **beanstalkd**| +| `python-beanstalkc`|used for monitoring **beanstalkd**| +| `python-dnspython`|used for monitoring DNS query time| +| `python-ipaddress`|used for monitoring **DHCPd**<br/>this package is required only if the system has python v2. python v3 has this functionality embedded| +| `python-mysqldb`<br/>or<br/>`python-pymysql`|used for monitoring **mysql** or **mariadb** databases<br/>`python-mysqldb` is a lot faster and thus preferred| +| `python-pymongo`|used for monitoring **mongodb** databases| +| `nodejs`|used for `node.js` plugins for monitoring **named** and **SNMP** devices| +| `lm-sensors`|for monitoring **hardware sensors**| +| `libelf`|for monitoring kernel-level metrics using eBPF| +| `libmnl`|for collecting netfilter metrics| +| `netcat`|for shell plugins to collect metrics from remote systems| + +*Netdata will greatly benefit if you have the above packages installed, but it will still work without them.* + +Netdata DB engine can be enabled when these are installed (they are optional): + +| package | description| +|:-----:|-----------| +| `liblz4` | Extremely fast compression algorithm, version r129 or greater| +| `openssl`| Cryptography and SSL/TLS toolkit| + +*Netdata will greatly benefit if you have the above packages installed, but it will still work without them.* + +Netdata Cloud support may require the following packages to be installed: + +| package | description | +|:---------:|--------------------------------------------------------------------------------------------------------------------------------------| +| `cmake` | Needed at build time if you aren't using your distribution's version of libwebsockets or are building on a platform other than Linux | +| `openssl` | Needed to secure communications with the Netdata Cloud | +| `protobuf`| Used for the new Cloud<->Agent binary protocol + +*Netdata will greatly benefit if you have the above packages installed, but it will still work without them.* + +### CentOS / RHEL 6.x + +On CentOS / RHEL 6.x, many of the dependencies for Netdata are only +available with versions older than what we need, so special setup is +required if manually installing packages. + +CentOS 6.x: + +- Enable the EPEL repo +- Enable the additional repo from [okay.network](https://okay.network/blog-news/rpm-repositories-for-centos-6-and-7.html) + +And install the minimum required dependencies. + +### CentOS / RHEL 8.x + +For CentOS / RHEL 8.x a lot of development packages have moved out into their +own separate repositories. Some other dependencies are either missing completely +or have to be sourced by 3rd-parties. + +CentOS 8.x: + +- Enable the PowerTools repo +- Enable the EPEL repo +- Enable the Extra repo from [OKAY](https://okay.network/blog-news/rpm-repositories-for-centos-6-and-7.html) + +And install the minimum required dependencies: + +```sh +# Enable config-manager +yum install -y 'dnf-command(config-manager)' + +# Enable PowerTools +yum config-manager --set-enabled powertools + +# Enable EPEL +yum install -y epel-release + +# Install Repo for libuv-devl (NEW) +yum install -y http://repo.okay.com.mx/centos/8/x86_64/release/okay-release-1-3.el8.noarch.rpm + +# Install Devel Packages +yum install autoconf automake curl gcc git cmake libuuid-devel openssl-devel libuv-devel lz4-devel make nc pkgconfig python3 zlib-devel + +``` + +## Install Netdata + +Do this to install and run Netdata: + +```sh +# download it - the directory 'netdata' will be created +git clone https://github.com/netdata/netdata.git --depth=100 --recursive +cd netdata + +# run script with root privileges to build, install, start Netdata +./netdata-installer.sh +``` + +- If you don't want to run it straight-away, add `--dont-start-it` option. + +- You can also append `--stable-channel` to fetch and install only the official releases from GitHub, instead of the nightly builds. + +- If you don't want to install it on the default directories, you can run the installer like this: `./netdata-installer.sh --install /opt`. This one will install Netdata in `/opt/netdata`. + +- If your server does not have access to the internet and you have manually put the installation directory on your server, you will need to pass the option `--disable-go` to the installer. The option will prevent the installer from attempting to download and install `go.d.plugin`. + +## Optional parameters to alter your installation + +`netdata-installer.sh` accepts a few parameters to customize your installation: + +- `--dont-wait`: Enable automated installs by not prompting for permission to install any required packages. +- `--dont-start-it`: Prevent the installer from starting Netdata automatically. +- `--stable-channel`: Automatically update only on the release of new major versions. +- `--nightly-channel`: Automatically update on every new nightly build. +- `--disable-telemetry`: Opt-out of [anonymous statistics](/docs/anonymous-statistics.md) we use to make + Netdata better. +- `--no-updates`: Prevent automatic updates of any kind. +- `--reinstall`: If an existing install is detected, reinstall instead of trying to update it. Note that this + cannot be used to change installation types. +- `--local-files`: Used for [offline installations](offline.md). Pass four file paths: the Netdata + tarball, the checksum file, the go.d plugin tarball, and the go.d plugin config tarball, to force kickstart run the + process using those files. This option conflicts with the `--stable-channel` option. If you set this _and_ + `--stable-channel`, Netdata will use the local files. + +### Connect node to Netdata Cloud during installation + +Unlike the [`kickstart.sh`](/packaging/installer/methods/kickstart.md), the `netdata-installer.sh` script does +not allow you to automatically [connect](/claim/README.md) your node to Netdata Cloud immediately after installation. + +See the [connect to cloud](/claim/README.md) doc for details on connecting a node with a manual installation of Netdata. + +### 'nonrepresentable section on output' errors + +Our current build process unfortunately has some issues when using certain configurations of the `clang` C compiler on Linux. + +If the installation fails with errors like `/bin/ld: externaldeps/libwebsockets/libwebsockets.a(context.c.o): relocation R_X86_64_32 against '.rodata.str1.1' can not be used when making a PIE object; recompile with -fPIC`, and you are trying to build with `clang` on Linux, you will need to build Netdata using GCC to get a fully functional install. + +In most cases, you can do this by running `CC=gcc ./netdata-installer.sh`. + +## What's next? + +When you're finished with installation, check out our [single-node](/docs/quickstart/single-node.md) or +[infrastructure](/docs/quickstart/infrastructure.md) monitoring quickstart guides based on your use case. + +Or, skip straight to [configuring the Netdata Agent](/docs/configure/nodes.md). + +Read through Netdata's [documentation](https://learn.netdata.cloud/docs), which is structured based on actions and +solutions, to enable features like health monitoring, alarm notifications, long-term metrics storage, exporting to +external databases, and more. + + diff --git a/packaging/installer/methods/offline.md b/packaging/installer/methods/offline.md new file mode 100644 index 0000000..5e92976 --- /dev/null +++ b/packaging/installer/methods/offline.md @@ -0,0 +1,66 @@ +<!-- +title: "Install Netdata on offline systems" +description: "Install the Netdata Agent on offline/air gapped systems to benefit from real-time, per-second monitoring without connecting to the internet." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/methods/offline.md +--> + +# Install Netdata on offline systems + +Our kickstart install script provides support for installing the Netdata Agent on systems which do not have a +usable internet connection by prefetching all of the required files so that they can be copied to the target system. +Currently, we only support using static installs with this method. There are tentative plans to support building +locally on offline systems as well, but there is currently no estimate of when this functionality may be implemented. + +Users who wish to use native packages on offline systems may be able to do so using whatever tooling their +distribution already provides for offline package management (such as `apt-offline` on Debian or Ubuntu systems), +but this is not officially supported. + +## Preparing the offline installation source + +The first step to installing Netdata on an offline system is to prepare the offline installation source. This can +be as a regular user from any internet connected system that has the following tools available: + +- cURL or wget +- sha256sum or shasum +- A standard POSIX compliant shell + +To prepare the offline installation source, simply run: + +```bash +wget -O /tmp/netdata-kickstart.sh https://my-netdata.io/kickstart.sh && sh /tmp/netdata-kickstart.sh --prepare-offline-install-source ./netdata-offline +``` + +or + +```bash +curl https://my-netdata.io/kickstart.sh > /tmp/netdata-kickstart.sh && sh /tmp/netdata-kickstart.sh --prepare-offline-install-source ./netdata-offline +``` + +> The exact name used for the directory does not matter, you can specify any other name you want in place of `./netdata-offline`. + +This will create a directory called `netdata-offline` in the current directory and place all the files required for an offline install in it. + +If you want to use a specific release channel (nightly or stable), it _must_ be specified on this step using the +apporpriate option for the kickstart script. + +## Installing on the target system + +Once you have prepared the offline install source, you need to copy the offline install source directory to the +target system. This can be done in any manner you like, as long as filenames are not changed. + +After copying the files, simply run the `install.sh` script located in the +offline install source directory. It accepts all the [same options as the kickstart +script](/packaging/installer/methods/kickstart.md#optional-parameters-to-alter-your-installation) for further +customization of the installation, though it will default to not enabling automatic updates (as they are not +supported on offline installs). + +## What's next? + +When you're finished with installation, check out our [single-node](/docs/quickstart/single-node.md) or +[infrastructure](/docs/quickstart/infrastructure.md) monitoring quickstart guides based on your use case. + +Or, skip straight to [configuring the Netdata Agent](/docs/configure/nodes.md). + +Read through Netdata's [documentation](https://learn.netdata.cloud/docs), which is structured based on actions and +solutions, to enable features like health monitoring, alarm notifications, long-term metrics storage, exporting to +external databases, and more. diff --git a/packaging/installer/methods/pfsense.md b/packaging/installer/methods/pfsense.md new file mode 100644 index 0000000..e055662 --- /dev/null +++ b/packaging/installer/methods/pfsense.md @@ -0,0 +1,83 @@ +<!-- +title: "Install Netdata on pfSense" +description: "Install Netdata on pfSense to monitor the health and performance of firewalls with thousands of real-time, per-second metrics." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/methods/pfsense.md +--> + +# Install Netdata on pfSense + +> 💡 This document is maintained by Netdata's community, and may not be completely up-to-date. Please double-check the +> details of the installation process, such as version numbers for downloadable packages, before proceeding. +> +> You can help improve this document by [submitting a +> PR](https://github.com/netdata/netdata/edit/master/packaging/installer/methods/pfsense.md) with your recommended +> improvements or changes. Thank you! + +## Install prerequisites/dependencies + +To install Netdata on pfSense, first run the following command (within a shell or under the **Diagnostics/Command** +prompt within the pfSense web interface). + +```bash +pkg install -y pkgconf bash e2fsprogs-libuuid libuv nano +``` + +Then run the following commands to download various dependencies from the FreeBSD repository. + +```sh +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/json-c-0.15_1.txz +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/py38-certifi-2021.10.8.txz +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/py38-asn1crypto-1.4.0.txz +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/py38-pycparser-2.20.txz +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/py38-cffi-1.14.6.txz +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/py38-six-1.16.0.txz +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/py38-cryptography-3.3.2.txz +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/py38-idna-2.10.txz +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/py38-openssl-20.0.1.txz +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/py38-pysocks-1.7.1.txz +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/py38-urllib3-1.26.7,1.txz +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/py38-yaml-5.4.1.txz +``` + +> ⚠️ If any of the above commands return a `Not Found` error, you need to manually search for the latest package in the +> [FreeBSD repository](https://www.freebsd.org/ports/). Search for the package's name, such as `py37-cffi`, find the +> latest version number, and update the command accordingly. + +> ⚠️ On pfSense 2.4.5, Python version 3.7 may be installed by the system, in which case you should should not install +> Python from the FreeBSD repository as instructed above. + +> ⚠️ If you are using the `apcupsd` collector, you need to make sure that apcupsd is up before starting Netdata. +> Otherwise a infinitely running `cat` process triggered by the default activated apcupsd charts plugin will eat up CPU +> and RAM (`/tmp/.netdata-charts.d-*/run-*`). This also applies to `OPNsense`. + +## Install Netdata + +You can now install Netdata from the FreeBSD repository. + +```bash +pkg add http://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/netdata-1.31.0_1.txz +``` + +> ⚠️ If the above command returns a `Not Found` error, you need to manually search for the latest version of Netdata in +> the [FreeBSD repository](https://www.freebsd.org/ports/). Search for `netdata`, find the latest version number, and +> update the command accordingly. + +You must edit `/usr/local/etc/netdata/netdata.conf` and change `bind to = 127.0.0.1` to `bind to = 0.0.0.0`. + +To start Netdata manually, run `service netdata onestart`. + +Visit the Netdata dashboard to confirm it's working: `http://<pfsenseIP>:19999` + +To start Netdata automatically every boot, add `service netdata onestart` as a Shellcmd entry within the pfSense web +interface under **Services/Shellcmd**. You'll need to install the Shellcmd package beforehand under **System/Package +Manager/Available Packages**. The Shellcmd Type should be set to `Shellcmd`. + Alternatively more information can be found in +<https://doc.pfsense.org/index.php/Installing_FreeBSD_Packages>, for achieving the same via the command line and +scripts. + +If you experience an issue with `/usr/bin/install` being absent in pfSense 2.3 or earlier, update pfSense or use a +workaround from <https://redmine.pfsense.org/issues/6643> + +**Note:** In pfSense, the Netdata configuration files are located under `/usr/local/etc/netdata`. + + diff --git a/packaging/installer/methods/source.md b/packaging/installer/methods/source.md new file mode 100644 index 0000000..d8f4f0b --- /dev/null +++ b/packaging/installer/methods/source.md @@ -0,0 +1,236 @@ +<!-- +title: "Manually build Netdata from source" +description: "Package maintainers and power users may be interested in manually building Netdata from source without using any of our installation scripts." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/methods/source.md +--> + +# Manually build Netdata from source + +These instructions are for advanced users and distribution package +maintainers. Unless this describes you, you almost certainly want +to follow [our guide for manually installing Netdata from a git +checkout](/packaging/installer/methods/manual.md) instead. + +## Required dependencies + +At a bare minimum, Netdata requires the following libraries and tools +to build and run successfully: + +- libuuid +- libuv version 1.0 or newer +- zlib +- GNU autoconf +- GNU automake +- GCC or Xcode (Clang is known to have issues in certain configurations, see [Using Clang](#using-clang)) +- A version of `make` compatible with GNU automake +- Git (we use git in the build system to generate version info, don't need a full install, just a working `git show` command) + +Additionally, the following build time features require additional dependencies: + +- TLS support for the web GUI: + - OpenSSL 1.0.2 or newer _or_ LibreSSL 3.0.0 or newer. +- dbengine metric storage: + - liblz4 r129 or newer + - OpenSSL 1.0 or newer (LibreSSL _amy_ work, but is largely untested). +- Netdata Cloud support: + - A working internet connection + - A recent version of CMake + - OpenSSL 1.0.2 or newer _or_ LibreSSL 3.0.0 or newer. + - JSON-C (may be provided by the user as shown below, or by the system) + - protobuf (Google Protocol Buffers) and protoc compiler + +## Preparing the source tree + +Certain features in Netdata require custom versions of specific libraries, +which the the build system will link statically into Netdata. These +libraries and their header files must be copied into specific locations +in the source tree to be used. + +### Netdata cloud +#### JSON-C + +Netdata requires the use of JSON-C for JSON parsing when using Netdata +Cloud. Netdata is able to use a system-provided copy of JSON-C, but +some systems may not provide it. If your system does not provide JSON-C, +you can do the following to prepare a copy for the build system: + +1. Verify the tag that Netdata expects to be used by checking the contents + of `packaging/jsonc.version` in your Netdata sources. +2. Obtain the sources for that version by either: + - Navigating to https://github.com/json-c/json-c and downloading + and unpacking the source code archive for that release. + - Cloning the repository with `git` and checking out the required tag. +3. Prepare the JSON-C sources by running `cmake -DBUILD_SHARED_LIBS=OFF .` + in the JSON-C source directory. +4. Build JSON-C by running `make` in the JSON-C source directory. +5. In the Netdata source directory, create a directory called + `externaldeps/jsonc`. +6. Copy `libjson-c.a` from the JSON-C source directory to + `externaldeps/jsonc/libjson-c.a` in the Netdata source tree. +7. Copy all of the header files (`*.h`) from the JSON-C source directory + to `externaldeps/jsonc/json-c` in the Netdata source tree. + +## Building Netdata + +Once the source tree has been prepared, Netdata is ready to be configured +and built. Netdata currently uses GNU autotools as it's primary build +system. To build Netdata this way: + +1. Run `autoreconf -ivf` in the Netdata source tree. +2. Run `./configure` in the Netdata source tree. +3. Run `make` in the Netdata source tree. + +### Configure options + +Netdata provides a number of build time configure options. This section +lists some of the ones you are most likely to need: + +- `--prefix`: Specify the prefix under which Netdata will be installed. +- `--with-webdir`: Specify a path relative to the prefix in which to + install the web UI files. +- `--disable-cloud`: Disables all Netdata Cloud functionality for + this build. + +### Using Clang + +Netdata is primarily developed using GCC, but in most cases we also +build just fine using Clang. Under some build configurations of Clang +itself, you may see build failures with the linker reporting errors +about `nonrepresentable section on output`. We currently do not have a +conclusive fix for this issue (the obvious fix leads to other issues which +we haven't been able to fix yet), and unfortunately the only workaround +is to use a different build of Clang or to use GCC. + +### Linking errors relating to OpenSSL + +Netdata's build system currently does not reliably support building +on systems which have multiple ABI incompatible versions of OpenSSL +installed. In such situations, you may encounter linking errors due to +Netdata trying to build against headers for one version but link to a +different version. + +## Additional components + +A full featured install of Netdata requires some additional components +which must be built and installed separately from the main Netdata +agent. All of these should be handled _after_ installing Netdata itself. + +### React dashboard + +The above build steps include a deprecated web UI for Netdata that lacks +support for Netdata Cloud. To get a fully featured dashboard, you must +install our new React dashboard. + +#### Installing the pre-built React dashboard + +We provide pre-built archives of the React dashboard for each release +(these are also used during our normal install process). To use one +of these: + +1. Verify the release version that Netdata expects to be used by checking + the contents of `packaging/dashboard.version` in your Netdata sources. +2. Go to https://github.com/netdata/dashboard/releases and download the + `dashboard.tar.gz` file for the required release. +3. Unpack the downloaded archive to a temporary directory. +4. Copy the contents of the `build` directory from the extracted + archive to `/usr/share/netdata/web` or the equivalent location for + your build of Netdata. This _will_ overwrite some files in the target + location. + +#### Building the React dashboard locally + +Alternatively, you may wish to build the React dashboard locally. Doing +so requires a recent version of Node.JS with a working install of +NPM. Once you have the required tools, do the following: + +1. Verify the release version that Netdata expects to be used by checking + the contents of `packaging/dashboard.version` in your Netdata sources. +2. Obtain the sources for that version by either: + - Navigating to https://github.com/netdata/dashboard and downloading + and unpacking the source code archive for that release. + - Cloning the repository with `git` and checking out the required tag. +3. Run `npm install` in the dashboard source tree. +4. Run `npm run build` in the dashboard source tree. +5. Copy the contents of the `build` directory just like step 4 of + installing the pre-built React dashboard. + +### Go collectors + +A number of the collectors for Netdata are written in Go instead of C, +and are developed in a separate repository from the mian Netdata code. +An installation without these collectors is still usable, but will be +unable to collect metrics for a number of network services the system +may be providing. You can either install a pre-built copy of these +collectors, or build them locally. + +#### Installing the pre-built Go collectors + +We provide pre-built binaries of the Go collectors for all the platforms +we officially support. To use one of these: + +1. Verify the release version that Netdata expects to be used by checking + the contents of `packaging/go.d.version` in your Netdata sources. +2. Go to https://github.com/netdata/go.d.plugin/releases, select the + required release, and download the `go.d.plugin-*.tar.gz` file + for your system type and CPu architecture and the `config.tar.gz` + configuration file archive. +3. Extract the `go.d.plugin-*.tar.gz` archive into a temporary + location, and then copy the single file in the archive to + `/usr/libexec/netdata/plugins.d` or the equivalent location for your + build of Netdata and rename it to `go.d.plugin`. +4. Extract the `config.tar.gz` archive to a temporarylocation and then + copy the contents of the archive to `/etc/netdata` or the equivalent + location for your build of Netdata. + +#### Building the Go collectors locally + +Alternatively, you may wish to build the Go collectors locally +yourself. Doing so requires a working installation of Golang 1.13 or +newer. Once you have the required tools, do the following: + +1. Verify the release version that Netdata expects to be used by checking + the contents of `packaging/go.d.version` in your Netdata sources. +2. Obtain the sources for that version by either: + - Navigating to https://github.com/netdata/go.d.plugin and downloading + and unpacking the source code archive for that release. + - Cloning the repository with `git` and checking out the required tag. +3. Run `make` in the go.d.plugin source tree. +4. Copy `bin/godplugin` to `/usr/libexec/netdata/plugins.d` or th + equivalent location for your build of Netdata and rename it to + `go.d.plugin`. +5. Copy the contents of the `config` directory to `/etc/netdata` or the + equivalent location for your build of Netdata. + +### eBPF collector + +On Linux systems, Netdata has support for using the kernel's eBPF +interface to monitor performance-related VFS, network, and process events, +allowing for insights into process lifetimes and file access +patterns. Using this functionality requires additional code managed in +a separate repository from the core Netdata agent. You can either install +a pre-built copy of the required code, or build it locally. + +#### Installing the pre-built eBPF code + +We provide pre-built copies of the eBPF code for 64-bit x86 systems +using glibc or musl. To use one of these: + +1. Verify the release version that Netdata expects to be used by checking + the contents of `packaging/ebpf.version` in your Netdata sources. +2. Go to https://github.com/netdata/kernel-collector/releases, select the + required release, and download the `netdata-kernel-collector-*.tar.xz` + file for the libc variant your system uses (either rmusl or glibc). +3. Extract the contents of the archive to a temporary location, and then + copy all of the `.o` and `.so.*` files and the contents of the `library/` + directory to `/usr/libexec/netdata/plugins.d` or the equivalent location + for your build of Netdata. + +#### Building the eBPF code locally + +Alternatively, you may wish to build the eBPF code locally yourself. For +instructions, please consult [the README file for our kernel-collector +repository](https://github.com/netdata/kernel-collector/blob/master/README.md), +which outlines both the required dependencies, as well as multiple +options for building the code. + + diff --git a/packaging/installer/methods/synology.md b/packaging/installer/methods/synology.md new file mode 100644 index 0000000..30ec303 --- /dev/null +++ b/packaging/installer/methods/synology.md @@ -0,0 +1,59 @@ +<!-- +title: "Install Netdata on Synology" +description: "The Netdata Agent can be installed on AMD64-compatible NAS systems using the 64-bit pre-compiled static binary." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/installer/methods/synology.md +--> + +# Install Netdata on Synology + +> 💡 This document is maintained by Netdata's community, and may not be completely up-to-date. Please double-check the +> details of the installation process, before proceeding. +> +> You can help improve this document by +> [submitting a PR](https://github.com/netdata/netdata/edit/master/packaging/installer/methods/synology.md) +> with your recommended improvements or changes. Thank you! + + +The good news is that our [one-line installation script](kickstart.md) works fine if your NAS is one that uses the amd64 architecture. It +will install the content into `/opt/netdata`, making future removal safe and simple. + +## Run as netdata user + +When Netdata is first installed, it will run as _root_. This may or may not be acceptable for you, and since other +installations run it as the `netdata` user, you might wish to do the same. This requires some extra work: + +1. Create a group `netdata` via the Synology group interface. Give it no access to anything. +2. Create a user `netdata` via the Synology user interface. Give it no access to anything and a random password. Assign + the user to the `netdata` group. Netdata will chuid to this user when running. +3. Change ownership of the following directories, as defined in [Netdata + Security](/docs/netdata-security.md#security-design): + +```sh +chown -R root:netdata /opt/netdata/usr/share/netdata +chown -R netdata:netdata /opt/netdata/var/lib/netdata /opt/netdata/var/cache/netdata +chown -R netdata:root /opt/netdata/var/log/netdata +``` + +4. Restart Netdata + +```sh +/etc/rc.netdata restart +``` + +## Create startup script + +Additionally, as of 2018/06/24, the Netdata installer doesn't recognize DSM as an operating system, so no init script is +installed. You'll have to do this manually: + +1. Add [this file](https://gist.github.com/oskapt/055d474d7bfef32c49469c1b53e8225f) as `/etc/rc.netdata`. Make it + executable with `chmod 0755 /etc/rc.netdata`. +2. Add or edit `/etc/rc.local` and add a line calling `/etc/rc.netdata` to have it start on boot: + +```conf +# Netdata startup +[ -x /etc/rc.netdata ] && /etc/rc.netdata start +``` + +3. Make sure `/etc/rc.netdata` is executable: `chmod 0755 /etc/rc.netdata`. + + diff --git a/packaging/installer/netdata-uninstaller.sh b/packaging/installer/netdata-uninstaller.sh new file mode 100755 index 0000000..45ec73f --- /dev/null +++ b/packaging/installer/netdata-uninstaller.sh @@ -0,0 +1,756 @@ +#!/bin/sh +# +# This is the netdata uninstaller script +# +# Variables needed by script and taken from '.environment' file: +# - NETDATA_PREFIX +# - NETDATA_ADDED_TO_GROUPS +# +# Copyright: SPDX-License-Identifier: GPL-3.0-or-later +# +# Author: Paweł Krupa <paulfantom@gmail.com> +# Author: Pavlos Emm. Katsoulakis <paul@netdata.cloud> +# +# Next unused error code: R0005 + +usage="$(basename "$0") [-h] [-f ] -- program to calculate the answer to life, the universe and everything + +where: + -e, --env path to environment file (defaults to '/etc/netdata/.environment' + -f, --force force uninstallation and do not ask any questions + -h show this help text + -y, --yes flag needs to be set to proceed with uninstallation" + +FILE_REMOVAL_STATUS=0 +ENVIRONMENT_FILE="/etc/netdata/.environment" +# shellcheck disable=SC2034 +INTERACTIVITY="-i" +YES=0 +while :; do + case "$1" in + -h | --help) + echo "$usage" >&2 + exit 1 + ;; + -f | --force) + INTERACTIVITY="-f" + shift + ;; + -y | --yes) + YES=1 + FLAG=-y + shift + ;; + -e | --env) + ENVIRONMENT_FILE="$2" + shift 2 + ;; + -*) + echo "$usage" >&2 + exit 1 + ;; + *) break ;; + esac +done + +if [ -n "${script_source}" ]; then + script_name="$(basename "${script_source}")" +else + script_name="netdata-uninstaller.sh" +fi + +info() { + echo >&2 "$(date) : INFO: ${script_name}: " "${1}" +} + +error() { + echo >&2 "$(date) : ERROR: ${script_name}: " "${1}" + if [ -n "${NETDATA_SAVE_WARNINGS}" ]; then + NETDATA_WARNINGS="${NETDATA_WARNINGS}\n - ${1}" + fi +} + +fatal() { + echo >&2 "$(date) : FATAL: ${script_name}: FAILED TO UNINSTALL NETDATA: " "${1}" + if [ -n "${NETDATA_SAVE_WARNINGS}" ]; then + NETDATA_WARNINGS="${NETDATA_WARNINGS}\n - ${1}" + fi + exit_reason "${1}" "${2}" + exit 1 +} + +exit_reason() { + if [ -n "${NETDATA_SAVE_WARNINGS}" ]; then + EXIT_REASON="${1}" + EXIT_CODE="${2}" + if [ -n "${NETDATA_PROPAGATE_WARNINGS}" ]; then + export EXIT_REASON + export EXIT_CODE + export NETDATA_WARNINGS + fi + fi +} + +if [ "$YES" != "1" ]; then + echo >&2 "This script will REMOVE netdata from your system." + echo >&2 "Run it again with --yes to do it." + exit_reason "User did not accept uninstalling." R0001 + exit 1 +fi + +if [ "$(id -u)" -ne 0 ]; then + error "This script SHOULD be run as root or otherwise it won't delete all installed components." + key="n" + read -r 1 -p "Do you want to continue as non-root user [y/n] ? " key + if [ "$key" != "y" ] && [ "$key" != "Y" ]; then + exit_reason "User cancelled uninstall." R0002 + exit 1 + fi +fi + +user_input() { + if [ "${INTERACTIVITY}" = "-i" ]; then + TEXT="$1 [y/n]" + + while true; do + echo "$TEXT" + read -r yn + + case "$yn" in + [Yy]*) return 0;; + [Nn]*) return 1;; + *) echo "Please answer yes or no.";; + esac + done + fi +} + +_cannot_use_tmpdir() { + testfile="$(TMPDIR="${1}" mktemp -q -t netdata-test.XXXXXXXXXX)" + ret=0 + + if [ -z "${testfile}" ]; then + return "${ret}" + fi + + if printf '#!/bin/sh\necho SUCCESS\n' > "${testfile}"; then + if chmod +x "${testfile}"; then + if [ "$("${testfile}")" = "SUCCESS" ]; then + ret=1 + fi + fi + fi + + rm -f "${testfile}" + return "${ret}" +} + +create_tmp_directory() { + if [ -z "${TMPDIR}" ] || _cannot_use_tmpdir "${TMPDIR}"; then + if _cannot_use_tmpdir /tmp; then + if _cannot_use_tmpdir "${PWD}"; then + fatal "Unable to find a usable temporary directory. Please set \$TMPDIR to a path that is both writable and allows execution of files and try again." R0003 + else + TMPDIR="${PWD}" + fi + else + TMPDIR="/tmp" + fi + fi + + mktemp -d -t netdata-kickstart-XXXXXXXXXX +} + +tmpdir="$(create_tmp_directory)" + +detect_existing_install() { + if pkg_installed netdata; then + ndprefix="/" + else + if [ -n "${INSTALL_PREFIX}" ]; then + searchpath="${INSTALL_PREFIX}/bin:${INSTALL_PREFIX}/sbin:${INSTALL_PREFIX}/usr/bin:${INSTALL_PREFIX}/usr/sbin:${PATH}" + searchpath="${INSTALL_PREFIX}/netdata/bin:${INSTALL_PREFIX}/netdata/sbin:${INSTALL_PREFIX}/netdata/usr/bin:${INSTALL_PREFIX}/netdata/usr/sbin:${searchpath}" + else + searchpath="${PATH}" + fi + + ndpath="$(PATH="${searchpath}" command -v netdata 2>/dev/null)" + + if [ -z "$ndpath" ] && [ -x /opt/netdata/bin/netdata ]; then + ndpath="/opt/netdata/bin/netdata" + fi + + if [ -n "${ndpath}" ]; then + ndprefix="$(dirname "$(dirname "${ndpath}")")" + fi + + if echo "${ndprefix}" | grep -Eq '/usr$'; then + ndprefix="$(dirname "${ndprefix}")" + fi + fi + + if [ -n "${ndprefix}" ]; then + typefile="${ndprefix}/etc/netdata/.install-type" + envfile="${ndprefix}/etc/netdata/.environment" + if [ -r "${typefile}" ]; then + ${ROOTCMD} sh -c "cat \"${typefile}\" > \"${tmpdir}/install-type\"" + # shellcheck disable=SC1090,SC1091 + . "${tmpdir}/install-type" + else + INSTALL_TYPE="unknown" + fi + + if [ "${INSTALL_TYPE}" = "unknown" ] || [ "${INSTALL_TYPE}" = "custom" ]; then + if [ -r "${envfile}" ]; then + ${ROOTCMD} sh -c "cat \"${envfile}\" > \"${tmpdir}/environment\"" + # shellcheck disable=SC1091 + . "${tmpdir}/environment" + if [ -n "${NETDATA_IS_STATIC_INSTALL}" ]; then + if [ "${NETDATA_IS_STATIC_INSTALL}" = "yes" ]; then + INSTALL_TYPE="legacy-static" + else + INSTALL_TYPE="legacy-build" + fi + fi + fi + fi + fi +} + +pkg_installed() { + case "${DISTRO_COMPAT_NAME}" in + debian|ubuntu) + dpkg-query --show --showformat '${Status}' "${1}" 2>&1 | cut -f 1 -d ' ' | grep -q '^install$' + return $? + ;; + centos|fedora|opensuse|ol) + rpm -q "${1}" > /dev/null 2>&1 + return $? + ;; + *) + return 1 + ;; + esac +} + +detect_existing_install + +if [ -x "$(command -v apt-get)" ] && [ "${INSTALL_TYPE}" = "binpkg-deb" ]; then + if dpkg -s netdata > /dev/null; then + echo "Found netdata native installation" + if user_input "Do you want to remove netdata? "; then + apt-get remove netdata ${FLAG} + fi + if dpkg -s netdata-repo-edge > /dev/null; then + if user_input "Do you want to remove netdata-repo-edge? "; then + apt-get remove netdata-repo-edge ${FLAG} + fi + fi + if dpkg -s netdata-repo > /dev/null; then + if user_input "Do you want to remove netdata-repo? "; then + apt-get remove netdata-repo ${FLAG} + fi + fi + exit 0 + fi +elif [ -x "$(command -v dnf)" ] && [ "${INSTALL_TYPE}" = "binpkg-rpm" ]; then + if rpm -q netdata > /dev/null; then + echo "Found netdata native installation." + if user_input "Do you want to remove netdata? "; then + dnf remove netdata ${FLAG} + fi + if rpm -q netdata-repo-edge > /dev/null; then + if user_input "Do you want to remove netdata-repo-edge? "; then + dnf remove netdata-repo-edge ${FLAG} + fi + fi + if rpm -q netdata-repo > /dev/null; then + if user_input "Do you want to remove netdata-repo? "; then + dnf remove netdata-repo ${FLAG} + fi + fi + exit 0 + fi +elif [ -x "$(command -v yum)" ] && [ "${INSTALL_TYPE}" = "binpkg-rpm" ]; then + if rpm -q netdata > /dev/null; then + echo "Found netdata native installation." + if user_input "Do you want to remove netdata? "; then + yum remove netdata ${FLAG} + fi + if rpm -q netdata-repo-edge > /dev/null; then + if user_input "Do you want to remove netdata-repo-edge? "; then + yum remove netdata-repo-edge ${FLAG} + fi + fi + if rpm -q netdata-repo > /dev/null; then + if user_input "Do you want to remove netdata-repo? "; then + yum remove netdata-repo ${FLAG} + fi + fi + exit 0 + fi +elif [ -x "$(command -v zypper)" ] && [ "${INSTALL_TYPE}" = "binpkg-rpm" ]; then + if [ "${FLAG}" = "-y" ]; then + FLAG=-n + fi + if zypper search -i netdata > /dev/null; then + echo "Found netdata native installation." + if user_input "Do you want to remove netdata? "; then + zypper ${FLAG} remove netdata + fi + if zypper search -i netdata-repo-edge > /dev/null; then + if user_input "Do you want to remove netdata-repo-edge? "; then + zypper ${FLAG} remove netdata-repo-edge + fi + fi + if zypper search -i netdata-repo > /dev/null; then + if user_input "Do you want to remove netdata-repo? "; then + zypper ${FLAG} remove netdata-repo + fi + fi + exit 0 + fi +fi + +# ----------------------------------------------------------------------------- +# portable service command + +service_cmd="$(command -v service 2> /dev/null)" +rcservice_cmd="$(command -v rc-service 2> /dev/null)" +systemctl_cmd="$(command -v systemctl 2> /dev/null)" +service() { + + cmd="${1}" + action="${2}" + + if [ -n "${systemctl_cmd}" ]; then + run "${systemctl_cmd}" "${action}" "${cmd}" + return $? + elif [ -n "${service_cmd}" ]; then + run "${service_cmd}" "${cmd}" "${action}" + return $? + elif [ -n "${rcservice_cmd}" ]; then + run "${rcservice_cmd}" "${cmd}" "${action}" + return $? + fi + return 1 +} + +# ----------------------------------------------------------------------------- + +setup_terminal() { + TPUT_RESET="" + TPUT_YELLOW="" + TPUT_WHITE="" + TPUT_BGRED="" + TPUT_BGGREEN="" + TPUT_BOLD="" + TPUT_DIM="" + + # Is stderr on the terminal? If not, then fail + test -t 2 || return 1 + + if command -v tput 1> /dev/null 2>&1; then + if [ $(($(tput colors 2> /dev/null))) -ge 8 ]; then + # Enable colors + TPUT_RESET="$(tput sgr 0)" + TPUT_YELLOW="$(tput setaf 3)" + TPUT_WHITE="$(tput setaf 7)" + TPUT_BGRED="$(tput setab 1)" + TPUT_BGGREEN="$(tput setab 2)" + TPUT_BOLD="$(tput bold)" + TPUT_DIM="$(tput dim)" + fi + fi + + return 0 +} +setup_terminal || echo > /dev/null + +ESCAPED_PRINT_METHOD= +if printf "%s " test > /dev/null 2>&1; then + ESCAPED_PRINT_METHOD="printfq" +fi +escaped_print() { + if [ "${ESCAPED_PRINT_METHOD}" = "printfq" ]; then + printf "%s " "${@}" + else + printf "%s" "${*}" + fi + return 0 +} + +run_logfile="/dev/null" +run() { + user="${USER--}" + dir="${PWD}" + + if [ "$(id -u)" = "0" ]; then + info="[root ${dir}]# " + info_console="[${TPUT_DIM}${dir}${TPUT_RESET}]# " + else + info="[${user} ${dir}]$ " + info_console="[${TPUT_DIM}${dir}${TPUT_RESET}]$ " + fi + + { + printf "%s" "${info}" + escaped_print "${@}" + printf "%s" " ... " + } >> "${run_logfile}" + + printf "%s" "${info_console}${TPUT_BOLD}${TPUT_YELLOW}" >&2 + escaped_print >&2 "${@}" + printf "%s\n" "${TPUT_RESET}" >&2 + + "${@}" + + ret=$? + if [ ${ret} -ne 0 ]; then + printf >&2 "%s FAILED %s\n\n" "${TPUT_BGRED}${TPUT_WHITE}${TPUT_BOLD}" "${TPUT_RESET}" + printf >> "${run_logfile}" "FAILED with exit code %s\n" "${ret}" + NETDATA_WARNINGS="${NETDATA_WARNINGS}\n - Command \"${*}\" failed with exit code ${ret}." + else + printf >&2 "%s OK %s\n\n" "${TPUT_BGGREEN}${TPUT_WHITE}${TPUT_BOLD}" "${TPUT_RESET}" + printf >> "${run_logfile}" "OK\n" + fi + + return ${ret} +} + +portable_del_group() { + groupname="${1}" + + # Check if group exist + info "Removing ${groupname} user group ..." + + # Linux + if command -v groupdel 1> /dev/null 2>&1; then + if grep -q "${groupname}" /etc/group; then + run groupdel "${groupname}" && return 0 + else + info "Group ${groupname} already removed in a previous step." + return 0 + fi + fi + + # mac OS + if command -v dseditgroup 1> /dev/null 2>&1; then + if dseditgroup -o read netdata 1> /dev/null 2>&1; then + run dseditgroup -o delete "${groupname}" && return 0 + else + info "Could not find group ${groupname}, nothing to do" + return 0 + fi + fi + + error "Group ${groupname} was not automatically removed, you might have to remove it manually" + return 1 +} + +issystemd() { + pids='' + p='' + myns='' + ns='' + systemctl='' + + # if the directory /lib/systemd/system OR /usr/lib/systemd/system (SLES 12.x) does not exit, it is not systemd + if [ ! -d /lib/systemd/system ] && [ ! -d /usr/lib/systemd/system ]; then + return 1 + fi + + # if there is no systemctl command, it is not systemd + systemctl=$(command -v systemctl 2> /dev/null) + if [ -z "${systemctl}" ] || [ ! -x "${systemctl}" ]; then + return 1 + fi + + # if pid 1 is systemd, it is systemd + [ "$(basename "$(readlink /proc/1/exe)" 2> /dev/null)" = "systemd" ] && return 0 + + # if systemd is not running, it is not systemd + pids=$(safe_pidof systemd 2> /dev/null) + [ -z "${pids}" ] && return 1 + + # check if the running systemd processes are not in our namespace + myns="$(readlink /proc/self/ns/pid 2> /dev/null)" + for p in ${pids}; do + ns="$(readlink "/proc/${p}/ns/pid" 2> /dev/null)" + + # if pid of systemd is in our namespace, it is systemd + [ -n "${myns}" ] && [ "${myns}" = "${ns}" ] && return 0 + done + + # else, it is not systemd + return 1 +} + +portable_del_user() { + username="${1}" + info "Deleting ${username} user account ..." + + # Linux + if command -v userdel 1> /dev/null 2>&1; then + run userdel -f "${username}" && return 0 + fi + + # mac OS + if command -v sysadminctl 1> /dev/null 2>&1; then + run sysadminctl -deleteUser "${username}" && return 0 + fi + + error "User ${username} could not be deleted from system, you might have to remove it manually" + return 1 +} + +portable_del_user_from_group() { + groupname="${1}" + username="${2}" + + # username is not in group + info "Deleting ${username} user from ${groupname} group ..." + + # Linux + if command -v gpasswd 1> /dev/null 2>&1; then + run gpasswd -d "netdata" "${group}" && return 0 + fi + + # FreeBSD + if command -v pw 1> /dev/null 2>&1; then + run pw groupmod "${groupname}" -d "${username}" && return 0 + fi + + # BusyBox + if command -v delgroup 1> /dev/null 2>&1; then + run delgroup "${username}" "${groupname}" && return 0 + fi + + # mac OS + if command -v dseditgroup 1> /dev/null 2>&1; then + run dseditgroup -o delete -u "${username}" "${groupname}" && return 0 + fi + + error "Failed to delete user ${username} from group ${groupname} !" + return 1 +} + +quit_msg() { + echo + if [ "$FILE_REMOVAL_STATUS" -eq 0 ]; then + fatal "Failed to completely remove Netdata from this system." R0004 + else + info "Netdata files were successfully removed from your system" + fi +} + +rm_file() { + FILE="$1" + if [ -f "${FILE}" ]; then + if user_input "Do you want to delete this file '$FILE' ? "; then + run rm -v "${FILE}" + fi + fi +} + +rm_dir() { + DIR="$1" + if [ -n "$DIR" ] && [ -d "$DIR" ]; then + if user_input "Do you want to delete this directory '$DIR' ? "; then + run rm -v -f -R "${DIR}" + fi + fi +} + +safe_pidof() { + pidof_cmd="$(command -v pidof 2> /dev/null)" + if [ -n "${pidof_cmd}" ]; then + ${pidof_cmd} "${@}" + return $? + else + ps -acxo pid,comm | + sed "s/^ *//g" | + grep netdata | + cut -d ' ' -f 1 + return $? + fi +} + +pidisnetdata() { + if [ -d /proc/self ]; then + if [ -z "$1" ] || [ ! -f "/proc/$1/stat" ]; then + return 1 + fi + [ "$(cut -d '(' -f 2 "/proc/$1/stat" | cut -d ')' -f 1)" = "netdata" ] && return 0 + return 1 + fi + return 0 +} + +stop_netdata_on_pid() { + pid="${1}" + ret=0 + count=0 + + pidisnetdata "${pid}" || return 0 + + info "Stopping netdata on pid ${pid} ..." + while [ -n "$pid" ] && [ ${ret} -eq 0 ]; do + if [ ${count} -gt 24 ]; then + error "Cannot stop the running netdata on pid ${pid}." + return 1 + fi + + count=$((count + 1)) + + pidisnetdata "${pid}" || ret=1 + if [ ${ret} -eq 1 ]; then + break + fi + + if [ ${count} -lt 12 ]; then + run kill "${pid}" 2> /dev/null + ret=$? + else + run kill -9 "${pid}" 2> /dev/null + ret=$? + fi + + test ${ret} -eq 0 && printf >&2 "." && sleep 5 + + done + + echo >&2 + if [ ${ret} -eq 0 ]; then + error "SORRY! CANNOT STOP netdata ON PID ${pid} !" + return 1 + fi + + info "netdata on pid ${pid} stopped." + return 0 +} + +netdata_pids() { + p='' + ns='' + + myns="$(readlink /proc/self/ns/pid 2> /dev/null)" + + for p in \ + $(cat /var/run/netdata.pid 2> /dev/null) \ + $(cat /var/run/netdata/netdata.pid 2> /dev/null) \ + $(safe_pidof netdata 2> /dev/null); do + ns="$(readlink "/proc/${p}/ns/pid" 2> /dev/null)" + + if [ -z "${myns}" ] || [ -z "${ns}" ] || [ "${myns}" = "${ns}" ]; then + pidisnetdata "${p}" && echo "${p}" + fi + done +} + +stop_all_netdata() { + p='' + stop_success=0 + + if [ "$(id -u)" -eq 0 ]; then + uname="$(uname 2> /dev/null)" + + # Any of these may fail, but we need to not bail if they do. + if issystemd; then + if systemctl stop netdata; then + stop_success=1 + sleep 5 + fi + elif [ "${uname}" = "Darwin" ]; then + if launchctl stop netdata; then + stop_success=1 + sleep 5 + fi + elif [ "${uname}" = "FreeBSD" ]; then + if /etc/rc.d/netdata stop; then + stop_success=1 + sleep 5 + fi + else + if service netdata stop; then + stop_success=1 + sleep 5 + fi + fi + fi + + if [ "$stop_success" = "0" ]; then + if [ -n "$(netdata_pids)" ] && [ -n "$(command -v netdatacli)" ]; then + netdatacli shutdown-agent + sleep 20 + fi + + for p in $(netdata_pids); do + # shellcheck disable=SC2086 + stop_netdata_on_pid ${p} + done + fi +} + +trap quit_msg EXIT + +# shellcheck source=/dev/null +# shellcheck disable=SC1090 +. "${ENVIRONMENT_FILE}" || exit 1 + +#### STOP NETDATA +info "Stopping a possibly running netdata..." +stop_all_netdata + +#### REMOVE NETDATA FILES +rm_file /etc/logrotate.d/netdata +rm_file /etc/systemd/system/netdata.service +rm_file /lib/systemd/system/netdata.service +rm_file /usr/lib/systemd/system/netdata.service +rm_file /etc/systemd/system/netdata-updater.service +rm_file /lib/systemd/system/netdata-updater.service +rm_file /usr/lib/systemd/system/netdata-updater.service +rm_file /etc/systemd/system/netdata-updater.timer +rm_file /lib/systemd/system/netdata-updater.timer +rm_file /usr/lib/systemd/system/netdata-updater.timer +rm_file /etc/init.d/netdata +rm_file /etc/periodic/daily/netdata-updater +rm_file /etc/cron.daily/netdata-updater +rm_file /etc/cron.d/netdata-updater + + +if [ -n "${NETDATA_PREFIX}" ] && [ -d "${NETDATA_PREFIX}" ]; then + rm_dir "${NETDATA_PREFIX}" +else + rm_file "/usr/sbin/netdata" + rm_file "/usr/sbin/netdatacli" + rm_file "/tmp/netdata-ipc" + rm_file "/usr/sbin/netdata-claim.sh" + rm_dir "/usr/share/netdata" + rm_dir "/usr/libexec/netdata" + rm_dir "/var/lib/netdata" + rm_dir "/var/cache/netdata" + rm_dir "/var/log/netdata" + rm_dir "/etc/netdata" +fi + +FILE_REMOVAL_STATUS=1 + +#### REMOVE NETDATA USER FROM ADDED GROUPS +if [ -n "$NETDATA_ADDED_TO_GROUPS" ]; then + if user_input "Do you want to delete 'netdata' from following groups: '$NETDATA_ADDED_TO_GROUPS' ? "; then + for group in $NETDATA_ADDED_TO_GROUPS; do + portable_del_user_from_group "${group}" "netdata" + done + fi +fi + +#### REMOVE USER +if user_input "Do you want to delete 'netdata' system user ? "; then + portable_del_user "netdata" || : +fi + +### REMOVE GROUP +if user_input "Do you want to delete 'netdata' system group ? "; then + portable_del_group "netdata" || : +fi diff --git a/packaging/installer/netdata-updater.sh b/packaging/installer/netdata-updater.sh new file mode 100755 index 0000000..d018d67 --- /dev/null +++ b/packaging/installer/netdata-updater.sh @@ -0,0 +1,953 @@ +#!/bin/sh + +# Netdata updater utility +# +# Variables needed by script: +# - PATH +# - CFLAGS +# - LDFLAGS +# - MAKEOPTS +# - IS_NETDATA_STATIC_BINARY +# - NETDATA_CONFIGURE_OPTIONS +# - REINSTALL_OPTIONS +# - NETDATA_TARBALL_URL +# - NETDATA_TARBALL_CHECKSUM_URL +# - NETDATA_TARBALL_CHECKSUM +# - NETDATA_PREFIX +# - NETDATA_LIB_DIR +# +# Optional environment options: +# +# - TMPDIR (set to a usable temporary directory) +# - NETDATA_NIGHTLIES_BASEURL (set the base url for downloading the dist tarball) +# +# Copyright: 2018-2020 Netdata Inc. +# SPDX-License-Identifier: GPL-3.0-or-later +# +# Author: Paweł Krupa <paulfantom@gmail.com> +# Author: Pavlos Emm. Katsoulakis <paul@netdata.cloud> +# Author: Austin S. Hemmelgarn <austin@netdata.cloud> + +# Next unused error code: U001B + +set -e + +PACKAGES_SCRIPT="https://raw.githubusercontent.com/netdata/netdata/master/packaging/installer/install-required-packages.sh" + +script_dir="$(CDPATH='' cd -- "$(dirname -- "$0")" && pwd -P)" + +if [ -x "${script_dir}/netdata-updater" ]; then + script_source="${script_dir}/netdata-updater" +else + script_source="${script_dir}/netdata-updater.sh" +fi + +PATH="${PATH}:/usr/local/bin:/usr/local/sbin" + +if [ ! -t 1 ]; then + INTERACTIVE=0 +else + INTERACTIVE=1 +fi + +if [ -n "${script_source}" ]; then + script_name="$(basename "${script_source}")" +else + script_name="netdata-updater.sh" +fi + +info() { + echo >&3 "$(date) : INFO: ${script_name}: " "${1}" +} + +warning() { + echo >&3 "$(date) : WARNING: ${script_name}: " "${@}" +} + +error() { + echo >&3 "$(date) : ERROR: ${script_name}: " "${1}" + if [ -n "${NETDATA_SAVE_WARNINGS}" ]; then + NETDATA_WARNINGS="${NETDATA_WARNINGS}\n - ${1}" + fi +} + +fatal() { + echo >&3 "$(date) : FATAL: ${script_name}: FAILED TO UPDATE NETDATA: " "${1}" + if [ -n "${NETDATA_SAVE_WARNINGS}" ]; then + NETDATA_WARNINGS="${NETDATA_WARNINGS}\n - ${1}" + fi + exit_reason "${1}" "${2}" + exit 1 +} + +exit_reason() { + if [ -n "${NETDATA_SAVE_WARNINGS}" ]; then + EXIT_REASON="${1}" + EXIT_CODE="${2}" + if [ -n "${NETDATA_PROPAGATE_WARNINGS}" ]; then + if [ -n "${NETDATA_SCRIPT_STATUS_PATH}" ]; then + { + echo "EXIT_REASON=\"${EXIT_REASON}\"" + echo "EXIT_CODE=\"${EXIT_CODE}\"" + echo "NETDATA_WARNINGS=\"${NETDATA_WARNINGS}\"" + } >> "${NETDATA_SCRIPT_STATUS_PATH}" + else + export EXIT_REASON + export EXIT_CODE + export NETDATA_WARNINGS + fi + fi + fi +} + +issystemd() { + # if the directory /lib/systemd/system OR /usr/lib/systemd/system (SLES 12.x) does not exit, it is not systemd + if [ ! -d /lib/systemd/system ] && [ ! -d /usr/lib/systemd/system ]; then + return 1 + fi + + # if there is no systemctl command, it is not systemd + systemctl=$(command -v systemctl 2> /dev/null) + if [ -z "${systemctl}" ] || [ ! -x "${systemctl}" ]; then + return 1 + fi + + # if pid 1 is systemd, it is systemd + [ "$(basename "$(readlink /proc/1/exe)" 2> /dev/null)" = "systemd" ] && return 0 + + # if systemd is not running, it is not systemd + pids=$(safe_pidof systemd 2> /dev/null) + [ -z "${pids}" ] && return 1 + + # check if the running systemd processes are not in our namespace + myns="$(readlink /proc/self/ns/pid 2> /dev/null)" + for p in ${pids}; do + ns="$(readlink "/proc/${p}/ns/pid" 2> /dev/null)" + + # if pid of systemd is in our namespace, it is systemd + [ -n "${myns}" ] && [ "${myns}" = "${ns}" ] && return 0 + done + + # else, it is not systemd + return 1 +} + +_get_intervaldir() { + if [ -d /etc/cron.daily ]; then + echo /etc/cron.daily + elif [ -d /etc/periodic/daily ]; then + echo /etc/periodic/daily + else + return 1 + fi + + return 0 +} + +_get_scheduler_type() { + if _get_intervaldir > /dev/null ; then + echo 'interval' + elif issystemd ; then + echo 'systemd' + elif [ -d /etc/cron.d ] ; then + echo 'crontab' + else + echo 'none' + fi +} + +install_build_dependencies() { + bash="$(command -v bash 2> /dev/null)" + + if [ -z "${bash}" ] || [ ! -x "${bash}" ]; then + error "Unable to find a usable version of \`bash\` (required for local build)." + return 1 + fi + + info "Fetching dependency handling script..." + download "${PACKAGES_SCRIPT}" "./install-required-packages.sh" || true + + if [ ! -s "./install-required-packages.sh" ]; then + error "Downloaded dependency installation script is empty." + else + info "Running dependency handling script..." + + opts="--dont-wait --non-interactive" + + # shellcheck disable=SC2086 + if ! "${bash}" "./install-required-packages.sh" ${opts} netdata >&3 2>&3; then + error "Installing build dependencies failed. The update should still work, but you might be missing some features." + fi + fi +} + +enable_netdata_updater() { + updater_type="$(echo "${1}" | tr '[:upper:]' '[:lower:]')" + case "${updater_type}" in + systemd|interval|crontab) + updater_type="${1}" + ;; + "") + updater_type="$(_get_scheduler_type)" + ;; + *) + fatal "Unrecognized updater type ${updater_type} requested. Supported types are 'systemd', 'interval', and 'crontab'." U0001 + ;; + esac + + case "${updater_type}" in + "systemd") + if issystemd; then + systemctl enable netdata-updater.timer + + info "Auto-updating has been ENABLED using a systemd timer unit.\n" + info "If the update process fails, the failure will be logged to the systemd journal just like a regular service failure." + info "Successful updates should produce empty logs." + else + error "Systemd-based auto-update scheduling requested, but this does not appear to be a systemd system. Auto-updates have NOT been enabled." + return 1 + fi + ;; + "interval") + if _get_intervaldir > /dev/null; then + ln -sf "${NETDATA_PREFIX}/usr/libexec/netdata/netdata-updater.sh" "$(_get_intervaldir)/netdata-updater" + + info "Auto-updating has been ENABLED through cron, updater script linked to $(_get_intervaldir)/netdata-updater\n" + info "If the update process fails and you have email notifications set up correctly for cron on this system, you should receive an email notification of the failure." + info "Successful updates will not send an email." + else + error "Interval-based auto-update scheduling requested, but I could not find an interval scheduling directory. Auto-updates have NOT been enabled." + return 1 + fi + ;; + "crontab") + if [ -d "/etc/cron.d" ]; then + cat > "/etc/cron.d/netdata-updater" <<-EOF + 2 57 * * * root ${NETDATA_PREFIX}/netdata-updater.sh + EOF + + info "Auto-updating has been ENABLED through cron, using a crontab at /etc/cron.d/netdata-updater\n" + info "If the update process fails and you have email notifications set up correctly for cron on this system, you should receive an email notification of the failure." + info "Successful updates will not send an email." + else + error "Crontab-based auto-update scheduling requested, but there is no '/etc/cron.d'. Auto-updates have NOT been enabled." + return 1 + fi + ;; + *) + error "Unable to determine what type of auto-update scheduling to use. Auto-updates have NOT been enabled." + return 1 + esac + + return 0 +} + +disable_netdata_updater() { + if issystemd && ( systemctl list-units --full -all | grep -Fq "netdata-updater.timer" ) ; then + systemctl disable netdata-updater.timer + fi + + if [ -d /etc/cron.daily ]; then + rm -f /etc/cron.daily/netdata-updater.sh + rm -f /etc/cron.daily/netdata-updater + fi + + if [ -d /etc/periodic/daily ]; then + rm -f /etc/periodic/daily/netdata-updater.sh + rm -f /etc/periodic/daily/netdata-updater + fi + + if [ -d /etc/cron.d ]; then + rm -f /etc/cron.d/netdata-updater + fi + + info "Auto-updates have been DISABLED." + + return 0 +} + +str_in_list() { + printf "%s\n" "${2}" | tr ' ' "\n" | grep -qE "^${1}\$" + return $? +} + +safe_sha256sum() { + # Within the context of the installer, we only use -c option that is common between the two commands + # We will have to reconsider if we start non-common options + if command -v shasum > /dev/null 2>&1; then + shasum -a 256 "$@" + elif command -v sha256sum > /dev/null 2>&1; then + sha256sum "$@" + else + fatal "I could not find a suitable checksum binary to use" U0002 + fi +} + +cleanup() { + if [ -n "${logfile}" ]; then + cat >&2 "${logfile}" + rm "${logfile}" + fi + + if [ -n "$ndtmpdir" ] && [ -d "$ndtmpdir" ]; then + rm -rf "$ndtmpdir" + fi +} + +_cannot_use_tmpdir() { + testfile="$(TMPDIR="${1}" mktemp -q -t netdata-test.XXXXXXXXXX)" + ret=0 + + if [ -z "${testfile}" ] ; then + return "${ret}" + fi + + if printf '#!/bin/sh\necho SUCCESS\n' > "${testfile}" ; then + if chmod +x "${testfile}" ; then + if [ "$("${testfile}" 2>/dev/null)" = "SUCCESS" ] ; then + ret=1 + fi + fi + fi + + rm -f "${testfile}" + return "${ret}" +} + +create_tmp_directory() { + if [ -n "${NETDATA_TMPDIR_PATH}" ]; then + echo "${NETDATA_TMPDIR_PATH}" + else + if [ -z "${NETDATA_TMPDIR}" ] || _cannot_use_tmpdir "${NETDATA_TMPDIR}" ; then + if [ -z "${TMPDIR}" ] || _cannot_use_tmpdir "${TMPDIR}" ; then + if _cannot_use_tmpdir /tmp ; then + if _cannot_use_tmpdir "${PWD}" ; then + fatal "Unable to find a usable temporary directory. Please set \$TMPDIR to a path that is both writable and allows execution of files and try again." U0003 + else + TMPDIR="${PWD}" + fi + else + TMPDIR="/tmp" + fi + fi + else + TMPDIR="${NETDATA_TMPDIR}" + fi + + mktemp -d -t netdata-updater-XXXXXXXXXX + fi +} + +_safe_download() { + url="${1}" + dest="${2}" + if command -v curl > /dev/null 2>&1; then + curl -sSL --connect-timeout 10 --retry 3 "${url}" > "${dest}" + return $? + elif command -v wget > /dev/null 2>&1; then + wget -T 15 -O - "${url}" > "${dest}" + return $? + else + return 255 + fi +} + +download() { + url="${1}" + dest="${2}" + + _safe_download "${url}" "${dest}" + ret=$? + + if [ ${ret} -eq 0 ]; then + return 0 + elif [ ${ret} -eq 255 ]; then + fatal "I need curl or wget to proceed, but neither is available on this system." U0004 + else + fatal "Cannot download ${url}" U0005 + fi +} + +get_netdata_latest_tag() { + dest="${1}" + url="https://github.com/netdata/netdata/releases/latest" + + if command -v curl >/dev/null 2>&1; then + tag=$(curl "${url}" -s -L -I -o /dev/null -w '%{url_effective}' | grep -m 1 -o '[^/]*$') + elif command -v wget >/dev/null 2>&1; then + tag=$(wget --max-redirect=0 "${url}" 2>&1 | grep Location | cut -d ' ' -f2 | grep -m 1 -o '[^/]*$') + else + fatal "I need curl or wget to proceed, but neither of them are available on this system." U0006 + fi + + echo "${tag}" >"${dest}" +} + +newer_commit_date() { + info "Checking if a newer version of the updater script is available." + + commit_check_url="https://api.github.com/repos/netdata/netdata/commits?path=packaging%2Finstaller%2Fnetdata-updater.sh&page=1&per_page=1" + python_version_check="from __future__ import print_function;import sys,json;data = json.load(sys.stdin);print(data[0]['commit']['committer']['date'] if isinstance(data, list) else '')" + + if command -v jq > /dev/null 2>&1; then + commit_date="$(_safe_download "${commit_check_url}" /dev/stdout | jq '.[0].commit.committer.date' 2>/dev/null | tr -d '"')" + elif command -v python > /dev/null 2>&1;then + commit_date="$(_safe_download "${commit_check_url}" /dev/stdout | python -c "${python_version_check}")" + elif command -v python3 > /dev/null 2>&1;then + commit_date="$(_safe_download "${commit_check_url}" /dev/stdout | python3 -c "${python_version_check}")" + fi + + if [ -z "${commit_date}" ] ; then + return 0 + elif [ "$(uname)" = "Linux" ]; then + commit_date="$(date -d "${commit_date}" +%s)" + else # assume BSD-style `date` if we are not on Linux + commit_date="$(/bin/date -j -f "%Y-%m-%dT%H:%M:%SZ" "${commit_date}" +%s 2>/dev/null)" + + if [ -z "${commit_date}" ]; then + return 0 + fi + fi + + if [ -e "${script_source}" ]; then + script_date="$(date -r "${script_source}" +%s)" + else + script_date="$(date +%s)" + fi + + [ "${commit_date}" -ge "${script_date}" ] +} + +self_update() { + if [ -z "${NETDATA_NO_UPDATER_SELF_UPDATE}" ] && newer_commit_date; then + info "Downloading newest version of updater script." + + ndtmpdir=$(create_tmp_directory) + cd "$ndtmpdir" || exit 1 + + if _safe_download "https://raw.githubusercontent.com/netdata/netdata/master/packaging/installer/netdata-updater.sh" ./netdata-updater.sh; then + chmod +x ./netdata-updater.sh || exit 1 + export ENVIRONMENT_FILE="${ENVIRONMENT_FILE}" + force_update="" + [ "$NETDATA_FORCE_UPDATE" = "1" ] && force_update="--force-update" + exec ./netdata-updater.sh --not-running-from-cron --no-updater-self-update "$force_update" --tmpdir-path "$(pwd)" + else + error "Failed to download newest version of updater script, continuing with current version." + fi + fi +} + +parse_version() { + r="${1}" + if echo "${r}" | grep -q '^v.*'; then + # shellcheck disable=SC2001 + # XXX: Need a regex group substitution here. + r="$(echo "${r}" | sed -e 's/^v\(.*\)/\1/')" + fi + + tmpfile="$(mktemp)" + echo "${r}" | tr '-' ' ' > "${tmpfile}" + read -r v b _ < "${tmpfile}" + + if echo "${b}" | grep -vEq "^[0-9]+$"; then + b="0" + fi + + echo "${v}" | tr '.' ' ' > "${tmpfile}" + read -r maj min patch _ < "${tmpfile}" + + rm -f "${tmpfile}" + + printf "%03d%03d%03d%05d" "${maj}" "${min}" "${patch}" "${b}" +} + +get_latest_version() { + if [ "${RELEASE_CHANNEL}" = "stable" ]; then + get_netdata_latest_tag /dev/stdout + else + download "$NETDATA_NIGHTLIES_BASEURL/latest-version.txt" /dev/stdout + fi +} + +validate_environment_file() { + if [ -n "${NETDATA_PREFIX+SET_BUT_NULL}" ] && [ -n "${REINSTALL_OPTIONS+SET_BUT_NULL}" ]; then + return 0 + else + fatal "Environment file located at ${ENVIRONMENT_FILE} is not valid, unable to update." U0007 + fi +} + +update_available() { + if [ "$NETDATA_FORCE_UPDATE" = "1" ]; then + info "Force update requested" + return 0 + fi + basepath="$(dirname "$(dirname "$(dirname "${NETDATA_LIB_DIR}")")")" + searchpath="${basepath}/bin:${basepath}/sbin:${basepath}/usr/bin:${basepath}/usr/sbin:${PATH}" + searchpath="${basepath}/netdata/bin:${basepath}/netdata/sbin:${basepath}/netdata/usr/bin:${basepath}/netdata/usr/sbin:${searchpath}" + ndbinary="$(PATH="${searchpath}" command -v netdata 2>/dev/null)" + + if [ -z "${ndbinary}" ]; then + current_version=0 + else + current_version="$(parse_version "$(${ndbinary} -v | cut -f 2 -d ' ')")" + fi + + latest_tag="$(get_latest_version)" + latest_version="$(parse_version "${latest_tag}")" + path_version="$(echo "${latest_tag}" | cut -f 1 -d "-")" + + # If we can't get the current version for some reason assume `0` + current_version="${current_version:-0}" + + # If we can't get the latest version for some reason assume `0` + latest_version="${latest_version:-0}" + + info "Current Version: ${current_version}" + info "Latest Version: ${latest_version}" + + if [ "${latest_version}" -gt 0 ] && [ "${current_version}" -gt 0 ] && [ "${current_version}" -ge "${latest_version}" ]; then + info "Newest version (current=${current_version} >= latest=${latest_version}) is already installed" + return 1 + else + info "Update available" + return 0 + fi +} + +set_tarball_urls() { + filename="netdata-latest.tar.gz" + + if [ "$2" = "yes" ]; then + if [ -e /opt/netdata/etc/netdata/.install-type ]; then + # shellcheck disable=SC1091 + . /opt/netdata/etc/netdata/.install-type + filename="netdata-${PREBUILT_ARCH}-latest.gz.run" + else + filename="netdata-x86_64-latest.gz.run" + fi + fi + + if [ "$1" = "stable" ]; then + latest="$(get_netdata_latest_tag /dev/stdout)" + export NETDATA_TARBALL_URL="https://github.com/netdata/netdata/releases/download/$latest/${filename}" + export NETDATA_TARBALL_CHECKSUM_URL="https://github.com/netdata/netdata/releases/download/$latest/sha256sums.txt" + else + export NETDATA_TARBALL_URL="$NETDATA_NIGHTLIES_BASEURL/${filename}" + export NETDATA_TARBALL_CHECKSUM_URL="$NETDATA_NIGHTLIES_BASEURL/sha256sums.txt" + fi +} + +update_build() { + [ -z "${logfile}" ] && info "Running on a terminal - (this script also supports running headless from crontab)" + + RUN_INSTALLER=0 + ndtmpdir=$(create_tmp_directory) + cd "$ndtmpdir" || fatal "Failed to change current working directory to ${ndtmpdir}" U0016 + + install_build_dependencies + + if update_available; then + download "${NETDATA_TARBALL_CHECKSUM_URL}" "${ndtmpdir}/sha256sum.txt" >&3 2>&3 + download "${NETDATA_TARBALL_URL}" "${ndtmpdir}/netdata-latest.tar.gz" + if [ -n "${NETDATA_TARBALL_CHECKSUM}" ] && + grep "${NETDATA_TARBALL_CHECKSUM}" sha256sum.txt >&3 2>&3 && + [ "$NETDATA_FORCE_UPDATE" != "1" ]; then + info "Newest version is already installed" + else + if ! grep netdata-latest.tar.gz sha256sum.txt | safe_sha256sum -c - >&3 2>&3; then + fatal "Tarball checksum validation failed. Stopping netdata upgrade and leaving tarball in ${ndtmpdir}\nUsually this is a result of an older copy of the tarball or checksum file being cached somewhere upstream and can be resolved by retrying in an hour." U0008 + fi + NEW_CHECKSUM="$(safe_sha256sum netdata-latest.tar.gz 2> /dev/null | cut -d' ' -f1)" + tar -xf netdata-latest.tar.gz >&3 2>&3 + rm netdata-latest.tar.gz >&3 2>&3 + if [ -z "$path_version" ]; then + latest_tag="$(get_latest_version)" + path_version="$(echo "${latest_tag}" | cut -f 1 -d "-")" + fi + cd "$(find . -maxdepth 1 -type d -name "netdata-${path_version}*" | head -n 1)" || fatal "Failed to switch to build directory" U0017 + RUN_INSTALLER=1 + fi + fi + + # We got the sources, run the update now + if [ ${RUN_INSTALLER} -eq 1 ]; then + # signal netdata to start saving its database + # this is handy if your database is big + possible_pids=$(pidof netdata) + do_not_start= + if [ -n "${possible_pids}" ]; then + # shellcheck disable=SC2086 + kill -USR1 ${possible_pids} + else + # netdata is currently not running, so do not start it after updating + do_not_start="--dont-start-it" + fi + + env="env TMPDIR=${TMPDIR}" + + if [ -n "${NETDATA_SELECTED_DASHBOARD}" ]; then + env="${env} NETDATA_SELECTED_DASHBOARD=${NETDATA_SELECTED_DASHBOARD}" + fi + + if [ ! -x ./netdata-installer.sh ]; then + if [ "$(find . -mindepth 1 -maxdepth 1 -type d | wc -l)" -eq 1 ] && [ -x "$(find . -mindepth 1 -maxdepth 1 -type d)/netdata-installer.sh" ]; then + cd "$(find . -mindepth 1 -maxdepth 1 -type d)" || fatal "Failed to switch to build directory" U0018 + fi + fi + + if [ -e "${NETDATA_PREFIX}/etc/netdata/.install-type" ] ; then + install_type="$(cat "${NETDATA_PREFIX}"/etc/netdata/.install-type)" + else + install_type="INSTALL_TYPE='legacy-build'" + fi + + if [ "${INSTALL_TYPE}" = "custom" ] && [ -f "${NETDATA_PREFIX}" ]; then + install_type="INSTALL_TYPE='legacy-build'" + fi + + info "Re-installing netdata..." + export NETDATA_SAVE_WARNINGS=1 + export NETDATA_PROPAGATE_WARNINGS=1 + export NETDATA_WARNINGS="${NETDATA_WARNINGS}" + export NETDATA_SCRIPT_STATUS_PATH="${NETDATA_SCRIPT_STATUS_PATH}" + # shellcheck disable=SC2086 + if ! ${env} ./netdata-installer.sh ${REINSTALL_OPTIONS} --dont-wait ${do_not_start} >&3 2>&3; then + if [ -r "${NETDATA_SCRIPT_STATUS_PATH}" ]; then + # shellcheck disable=SC1090 + . "${NETDATA_SCRIPT_STATUS_PATH}" + rm -f "${NETDATA_SCRIPT_STATUS_PATH}" + fi + if [ -n "${EXIT_REASON}" ]; then + fatal "Failed to rebuild existing netdata install: ${EXIT_REASON}" "U${EXIT_CODE}" + else + fatal "Failed to rebuild existing netdata reinstall." UI0000 + fi + fi + + # We no longer store checksum info here. but leave this so that we clean up all environment files upon next update. + sed -i '/NETDATA_TARBALL/d' "${ENVIRONMENT_FILE}" + + info "Updating tarball checksum info" + echo "${NEW_CHECKSUM}" > "${NETDATA_LIB_DIR}/netdata.tarball.checksum" + + echo "${install_type}" > "${NETDATA_PREFIX}/etc/netdata/.install-type" + fi + + rm -rf "${ndtmpdir}" >&3 2>&3 + [ -n "${logfile}" ] && rm "${logfile}" && logfile= + + return 0 +} + +update_static() { + ndtmpdir="$(create_tmp_directory)" + PREVDIR="$(pwd)" + + info "Entering ${ndtmpdir}" + cd "${ndtmpdir}" || fatal "Failed to change current working directory to ${ndtmpdir}" U0019 + + if update_available; then + sysarch="$(uname -m)" + download "${NETDATA_TARBALL_CHECKSUM_URL}" "${ndtmpdir}/sha256sum.txt" + download "${NETDATA_TARBALL_URL}" "${ndtmpdir}/netdata-${sysarch}-latest.gz.run" + if ! grep "netdata-${sysarch}-latest.gz.run" "${ndtmpdir}/sha256sum.txt" | safe_sha256sum -c - > /dev/null 2>&1; then + fatal "Static binary checksum validation failed. Stopping netdata installation and leaving binary in ${ndtmpdir}\nUsually this is a result of an older copy of the file being cached somewhere and can be resolved by simply retrying in an hour." U000A + fi + + if [ -e /opt/netdata/etc/netdata/.install-type ] ; then + install_type="$(cat /opt/netdata/etc/netdata/.install-type)" + else + install_type="INSTALL_TYPE='legacy-static'" + fi + + # Do not pass any options other than the accept, for now + # shellcheck disable=SC2086 + if sh "${ndtmpdir}/netdata-${sysarch}-latest.gz.run" --accept -- ${REINSTALL_OPTIONS} >&3 2>&3; then + rm -r "${ndtmpdir}" + else + info "NOTE: did not remove: ${ndtmpdir}" + fi + + echo "${install_type}" > /opt/netdata/etc/netdata/.install-type + fi + + if [ -e "${PREVDIR}" ]; then + info "Switching back to ${PREVDIR}" + cd "${PREVDIR}" + fi + [ -n "${logfile}" ] && rm "${logfile}" && logfile= + exit 0 +} + +update_binpkg() { + os_release_file= + if [ -s "/etc/os-release" ] && [ -r "/etc/os-release" ]; then + os_release_file="/etc/os-release" + elif [ -s "/usr/lib/os-release" ] && [ -r "/usr/lib/os-release" ]; then + os_release_file="/usr/lib/os-release" + else + fatal "Cannot find an os-release file ..." U000B + fi + + # shellcheck disable=SC1090 + . "${os_release_file}" + + DISTRO="${ID}" + + supported_compat_names="debian ubuntu centos fedora opensuse" + + if str_in_list "${DISTRO}" "${supported_compat_names}"; then + DISTRO_COMPAT_NAME="${DISTRO}" + else + case "${DISTRO}" in + opensuse-leap) + DISTRO_COMPAT_NAME="opensuse" + ;; + cloudlinux|almalinux|rocky|rhel) + DISTRO_COMPAT_NAME="centos" + ;; + *) + DISTRO_COMPAT_NAME="unknown" + ;; + esac + fi + + if [ "${INTERACTIVE}" = "0" ]; then + interactive_opts="-y" + env="DEBIAN_FRONTEND=noninteractive" + else + interactive_opts="" + env="" + fi + + case "${DISTRO_COMPAT_NAME}" in + debian) + pm_cmd="apt-get" + repo_subcmd="update" + upgrade_cmd="--only-upgrade install" + pkg_install_opts="${interactive_opts}" + repo_update_opts="${interactive_opts}" + pkg_installed_check="dpkg -s" + INSTALL_TYPE="binpkg-deb" + ;; + ubuntu) + pm_cmd="apt-get" + repo_subcmd="update" + upgrade_cmd="--only-upgrade install" + pkg_install_opts="${interactive_opts}" + repo_update_opts="${interactive_opts}" + pkg_installed_check="dpkg -s" + INSTALL_TYPE="binpkg-deb" + ;; + centos) + if command -v dnf > /dev/null; then + pm_cmd="dnf" + repo_subcmd="makecache" + else + pm_cmd="yum" + fi + upgrade_cmd="upgrade" + pkg_install_opts="${interactive_opts}" + repo_update_opts="${interactive_opts}" + pkg_installed_check="rpm -q" + INSTALL_TYPE="binpkg-rpm" + ;; + fedora) + if command -v dnf > /dev/null; then + pm_cmd="dnf" + repo_subcmd="makecache" + else + pm_cmd="yum" + fi + upgrade_cmd="upgrade" + pkg_install_opts="${interactive_opts}" + repo_update_opts="${interactive_opts}" + pkg_installed_check="rpm -q" + INSTALL_TYPE="binpkg-rpm" + ;; + opensuse) + pm_cmd="zypper" + repo_subcmd="--gpg-auto-import-keys refresh" + upgrade_cmd="upgrade" + pkg_install_opts="${interactive_opts} --allow-unsigned-rpm" + repo_update_opts="" + pkg_installed_check="rpm -q" + INSTALL_TYPE="binpkg-rpm" + ;; + *) + warning "We do not provide native packages for ${DISTRO}." + return 2 + ;; + esac + + if [ -n "${repo_subcmd}" ]; then + # shellcheck disable=SC2086 + env ${env} ${pm_cmd} ${repo_subcmd} ${repo_update_opts} >&3 2>&3 || fatal "Failed to update repository metadata." U000C + fi + + for repopkg in netdata-repo netdata-repo-edge; do + if ${pkg_installed_check} ${repopkg} > /dev/null 2>&1; then + # shellcheck disable=SC2086 + env ${env} ${pm_cmd} ${upgrade_cmd} ${pkg_install_opts} ${repopkg} >&3 2>&3 || fatal "Failed to update Netdata repository config." U000D + # shellcheck disable=SC2086 + if [ -n "${repo_subcmd}" ]; then + env ${env} ${pm_cmd} ${repo_subcmd} ${repo_update_opts} >&3 2>&3 || fatal "Failed to update repository metadata." U000E + fi + fi + done + + # shellcheck disable=SC2086 + env ${env} ${pm_cmd} ${upgrade_cmd} ${pkg_install_opts} netdata >&3 2>&3 || fatal "Failed to update Netdata package." U000F + [ -n "${logfile}" ] && rm "${logfile}" && logfile= + return 0 +} + +# Simple function to encapsulate original updater behavior. +update_legacy() { + set_tarball_urls "${RELEASE_CHANNEL}" "${IS_NETDATA_STATIC_BINARY}" + if [ "${IS_NETDATA_STATIC_BINARY}" = "yes" ]; then + update_static && exit 0 + else + update_build && exit 0 + fi +} + +logfile= +ndtmpdir= + +trap cleanup EXIT + +if [ -t 2 ]; then + # we are running on a terminal + # open fd 3 and send it to stderr + exec 3>&2 +else + # we are headless + # create a temporary file for the log + logfile="$(mktemp -t netdata-updater.log.XXXXXX)" + # open fd 3 and send it to logfile + exec 3> "${logfile}" +fi + +: "${ENVIRONMENT_FILE:=THIS_SHOULD_BE_REPLACED_BY_INSTALLER_SCRIPT}" + +if [ "${ENVIRONMENT_FILE}" = "THIS_SHOULD_BE_REPLACED_BY_INSTALLER_SCRIPT" ]; then + if [ -r "${script_dir}/../../../etc/netdata/.environment" ] || [ -r "${script_dir}/../../../etc/netdata/.install-type" ]; then + ENVIRONMENT_FILE="${script_dir}/../../../etc/netdata/.environment" + elif [ -r "/etc/netdata/.environment" ] || [ -r "/etc/netdata/.install-type" ]; then + ENVIRONMENT_FILE="/etc/netdata/.environment" + elif [ -r "/opt/netdata/etc/netdata/.environment" ] || [ -r "/opt/netdata/etc/netdata/.install-type" ]; then + ENVIRONMENT_FILE="/opt/netdata/etc/netdata/.environment" + else + envpath="$(find / -type d \( -path /sys -o -path /proc -o -path /dev \) -prune -false -o -path '*netdata/.environment' -type f 2> /dev/null | head -n 1)" + itpath="$(find / -type d \( -path /sys -o -path /proc -o -path /dev \) -prune -false -o -path '*netdata/.install-type' -type f 2> /dev/null | head -n 1)" + if [ -r "${envpath}" ]; then + ENVIRONMENT_FILE="${envpath}" + elif [ -r "${itpath}" ]; then + ENVIRONMENT_FILE="$(dirname "${itpath}")/.environment" + else + fatal "Cannot find environment file or install type file, unable to update." U0010 + fi + fi +fi + +if [ -r "${ENVIRONMENT_FILE}" ] ; then + # shellcheck source=/dev/null + . "${ENVIRONMENT_FILE}" || fatal "Failed to source ${ENVIRONMENT_FILE}" U0014 +fi + +if [ -r "$(dirname "${ENVIRONMENT_FILE}")/.install-type" ]; then + # shellcheck source=/dev/null + . "$(dirname "${ENVIRONMENT_FILE}")/.install-type" || fatal "Failed to source $(dirname "${ENVIRONMENT_FILE}")/.install-type" U0015 +fi + +while [ -n "${1}" ]; do + case "${1}" in + --not-running-from-cron) NETDATA_NOT_RUNNING_FROM_CRON=1 ;; + --no-updater-self-update) NETDATA_NO_UPDATER_SELF_UPDATE=1 ;; + --force-update) NETDATA_FORCE_UPDATE=1 ;; + --non-interactive) INTERACTIVE=0 ;; + --interactive) INTERACTIVE=1 ;; + --tmpdir-path) + NETDATA_TMPDIR_PATH="${2}" + shift 1 + ;; + --enable-auto-updates) + enable_netdata_updater "${2}" + exit $? + ;; + --disable-auto-updates) + disable_netdata_updater + exit $? + ;; + *) + fatal "Unrecognized option ${1}" U001A + ;; + esac + + shift 1 +done + +# Random sleep to alleviate stampede effect of Agents upgrading +# and disconnecting/reconnecting at the same time (or near to). +# But only we're not a controlling terminal (tty) +# Randomly sleep between 1s and 60m +if [ ! -t 1 ] && [ -z "${NETDATA_NOT_RUNNING_FROM_CRON}" ]; then + rnd="$(awk ' + BEGIN { srand() + printf("%d\n", 3600 * rand()) + }')" + sleep $(((rnd % 3600) + 1)) +fi + +# We dont expect to find lib dir variable on older installations, so load this path if none found +export NETDATA_LIB_DIR="${NETDATA_LIB_DIR:-${NETDATA_PREFIX}/var/lib/netdata}" + +# Source the tarball checksum, if not already available from environment (for existing installations with the old logic) +[ -z "${NETDATA_TARBALL_CHECKSUM}" ] && [ -f "${NETDATA_LIB_DIR}/netdata.tarball.checksum" ] && NETDATA_TARBALL_CHECKSUM="$(cat "${NETDATA_LIB_DIR}/netdata.tarball.checksum")" + +# Grab the nightlies baseurl (defaulting to our Google Storage bucket) +export NETDATA_NIGHTLIES_BASEURL="${NETDATA_NIGHTLIES_BASEURL:-https://storage.googleapis.com/netdata-nightlies}" + +if echo "$INSTALL_TYPE" | grep -qv ^binpkg && [ "${INSTALL_UID}" != "$(id -u)" ]; then + fatal "You are running this script as user with uid $(id -u). We recommend to run this script as root (user with uid 0)" U0011 +fi + +self_update + +# shellcheck disable=SC2153 +case "${INSTALL_TYPE}" in + *-build) + validate_environment_file + set_tarball_urls "${RELEASE_CHANNEL}" "${IS_NETDATA_STATIC_BINARY}" + update_build && exit 0 + ;; + *-static*) + validate_environment_file + set_tarball_urls "${RELEASE_CHANNEL}" "${IS_NETDATA_STATIC_BINARY}" + update_static && exit 0 + ;; + *binpkg*) + update_binpkg && exit 0 + ;; + "") # Fallback case for no `.install-type` file. This just works like the old install type detection. + validate_environment_file + update_legacy + ;; + custom) + # At this point, we _should_ have a valid `.environment` file, but it's best to just check. + # If we do, then behave like the legacy updater. + if validate_environment_file && [ -n "${IS_NETDATA_STATIC_BINARY}" ]; then + update_legacy + else + fatal "This script does not support updating custom installations without valid environment files." U0012 + fi + ;; + oci) + fatal "This script does not support updating Netdata inside our official Docker containers, please instead update the container itself." U0013 + ;; + *) + fatal "Unrecognized installation type (${INSTALL_TYPE}), unable to update." U0014 + ;; +esac diff --git a/packaging/jsonc.checksums b/packaging/jsonc.checksums new file mode 100644 index 0000000..6005f45 --- /dev/null +++ b/packaging/jsonc.checksums @@ -0,0 +1 @@ +ec4eb70e0f6c0d707b9b1ec646cf7c860f4abb3562a90ea6e4d78d177fd95303 json-c-0.14-20200419.tar.gz diff --git a/packaging/jsonc.version b/packaging/jsonc.version new file mode 100644 index 0000000..29b5619 --- /dev/null +++ b/packaging/jsonc.version @@ -0,0 +1 @@ +0.14-20200419 diff --git a/packaging/libbpf.checksums b/packaging/libbpf.checksums new file mode 100644 index 0000000..9a8b8f8 --- /dev/null +++ b/packaging/libbpf.checksums @@ -0,0 +1 @@ +63fe4ac3f6807e8ff4cd3af2ffae0091eb177fb7f6aca2f03d3f201a609b988c v1.0.1_netdata.tar.gz diff --git a/packaging/libbpf.version b/packaging/libbpf.version new file mode 100644 index 0000000..bb58ffc --- /dev/null +++ b/packaging/libbpf.version @@ -0,0 +1 @@ +1.0.1_netdata diff --git a/packaging/libbpf_0_0_9.checksums b/packaging/libbpf_0_0_9.checksums new file mode 100644 index 0000000..d4ff87a --- /dev/null +++ b/packaging/libbpf_0_0_9.checksums @@ -0,0 +1 @@ +fc33402ba33c8f8c5aa18afbb86a9932965886f2906c50e8f2110a1a2126e3ee v0.0.9_netdata-1.tar.gz diff --git a/packaging/libbpf_0_0_9.version b/packaging/libbpf_0_0_9.version new file mode 100644 index 0000000..d236290 --- /dev/null +++ b/packaging/libbpf_0_0_9.version @@ -0,0 +1 @@ +0.0.9_netdata-1 diff --git a/packaging/maintainers/README.md b/packaging/maintainers/README.md new file mode 100644 index 0000000..249436d --- /dev/null +++ b/packaging/maintainers/README.md @@ -0,0 +1,86 @@ +<!-- +title: "Package Maintainers" +date: 2020-03-31 +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/maintainers/README.md +--> + +# Package Maintainers + +This page tracks the package maintainers for Netdata, for various operating systems and versions. + +> Feel free to update it, so that it reflects the current status. + +--- + +## Official Linux Distributions + +| Linux Distribution | Netdata Version | Maintainer | Related URL | +| :-: | :-: | :-: | :-- | +| Arch Linux | Release | @svenstaro | [netdata @ Arch Linux](https://www.archlinux.org/packages/community/x86_64/netdata/) | +| Arch Linux AUR | Git | @sanskritfritz | [netdata @ AUR](https://aur.archlinux.org/packages/netdata-git/) | +| Gentoo Linux | Release + Git | @candrews | [netdata @ gentoo](https://github.com/gentoo/gentoo/tree/master/net-analyzer/netdata) | +| Debian | Release | @lhw @FedericoCeratto | [netdata @ debian](http://salsa.debian.org/debian/netdata) | +| Slackware | Release | @willysr | [netdata @ slackbuilds](https://slackbuilds.org/repository/14.2/system/netdata/) | +| Ubuntu | | | | +| Red Hat / Fedora / CentOS | | | | +| SUSE SLE / openSUSE Tumbleweed & Leap | | | [netdata @ SUSE OpenBuildService](https://software.opensuse.org/package/netdata) | + +--- + +## FreeBSD + +| System | Initial PR | Core Developer | Package Maintainer +|:-:|:-:|:-:|:-:| +| FreeBSD | #1321 | @vlvkobal|@mmokhi + +--- + +## macOS + +| System | URL | Core Developer | Package Maintainer +|:-:|:-:|:-:|:-:| +| macOS Homebrew Formula|[link](https://github.com/Homebrew/homebrew-core/blob/master/Formula/netdata.rb)|@vlvkobal|@rickard-von-essen + +--- + +## Unofficial Linux Packages + +| Linux Distribution | Netdata Version | Maintainer | Related URL | +| :-: | :-: | :-: | :-- | +| Ubuntu | Release | @gslin | [netdata @ gslin ppa](https://launchpad.net/~gslin/+archive/ubuntu/netdata) https://github.com/netdata/netdata/issues/69#issuecomment-217458543 | +--- + +## Embedded Linux + +| Embedded Linux | Netdata Version | Maintainer | Related URL | +| :-: | :-: | :-: | :-- | +| ASUSTOR NAS | ? | William Lin | https://www.asustor.com/apps/app_detail?id=532 | +| OpenWRT | Release | @nitroshift | [openwrt package](https://github.com/openwrt/packages/tree/master/admin/netdata) | +| ReadyNAS | Release | @NAStools | https://github.com/nastools/netdata | +| QNAP | Release | QNAP_Stephane | https://forum.qnap.com/viewtopic.php?t=121518 | +| DietPi | Release | @Fourdee | https://github.com/Fourdee/DietPi | + +--- + +## Linux Containers + +| Containers | Netdata Version | Maintainer | Related URL | +| :-: | :-: | :-: | :-- | +| Docker | Git | @titpetric | https://github.com/titpetric/netdata | + +--- + +## Automation Systems + +| Automation Systems | Netdata Version | Maintainer | Related URL | +| :-: | :-: | :-: | :-- | +| Ansible | git | @jffz | https://galaxy.ansible.com/jffz/netdata/ | +| Chef | ? | @sergiopena | https://github.com/sergiopena/netdata-cookbook | + +--- + +## Packages summary from repology.org + +[](https://repology.org/metapackage/netdata/versions) + + diff --git a/packaging/makeself/README.md b/packaging/makeself/README.md new file mode 100644 index 0000000..055b6c1 --- /dev/null +++ b/packaging/makeself/README.md @@ -0,0 +1,54 @@ +<!-- +title: "Netdata static binary build" +description: "Users can build the static 64-bit binary package that we ship with every release of the open-source Netdata Agent for debugging or specialize purposes." +custom_edit_url: https://github.com/netdata/netdata/edit/master/packaging/makeself/README.md +--> + +# Netdata static binary build + +To build the static binary 64-bit distribution package, run: + +```bash +cd /path/to/netdata.git +./packaging/makeself/build-x86_64-static.sh +``` + +The program will: + +1. setup a new docker container with Alpine Linux +2. install the required alpine packages (the build environment, needed libraries, etc) +3. download and compile third party apps that are packaged with Netdata (`bash`, `curl`, etc) +4. compile Netdata + +Once finished, a file named `netdata-vX.X.X-gGITHASH-x86_64-DATE-TIME.run` will be created in the current directory. This is the Netdata binary package that can be run to install Netdata on any other computer. + +--- + +## building binaries with debug info + +To build Netdata binaries with debugging / tracing information in them, use: + +```bash +cd /path/to/netdata.git +./packaging/makeself/build-x86_64-static.sh debug +``` + +These binaries are not optimized (they are a bit slower), they have certain features disables (like log flood protection), other features enables (like `debug flags`) and are not stripped (the binary files are bigger, since they now include source code tracing information). + +### debugging Netdata binaries + +Once you have installed a binary package with debugging info, you will need to install `valgrind` and run this command to start Netdata: + +```bash +PATH="/opt/netdata/bin:${PATH}" valgrind --undef-value-errors=no /opt/netdata/bin/srv/netdata -D +``` + +The above command, will run Netdata under `valgrind`. While Netdata runs under `valgrind` it will be 10x slower and use a lot more memory. + +If Netdata crashes, `valgrind` will print a stack trace of the issue. Open a github issue to let us know. + +To stop Netdata while it runs under `valgrind`, press Control-C on the console. + +> If you omit the parameter `--undef-value-errors=no` to valgrind, you will get hundreds of errors about conditional jumps that depend on uninitialized values. This is normal. Valgrind has heuristics to prevent it from printing such errors for system libraries, but for the static Netdata binary, all the required libraries are built into Netdata. So, valgrind cannot apply its heuristics and prints them. + + diff --git a/packaging/makeself/build-static.sh b/packaging/makeself/build-static.sh new file mode 100755 index 0000000..f9f635c --- /dev/null +++ b/packaging/makeself/build-static.sh @@ -0,0 +1,58 @@ +#!/usr/bin/env bash + +# SPDX-License-Identifier: GPL-3.0-or-later + +# shellcheck source=./packaging/installer/functions.sh +. "$(dirname "$0")"/../installer/functions.sh || exit 1 + +BUILDARCH="${1}" + +set -e + +platform="$("$(dirname "${0}")/uname2platform.sh" "${BUILDARCH}")" + +if [ -z "${platform}" ]; then + exit 1 +fi + +if command -v docker > /dev/null 2>&1; then + docker="docker" +elif command -v podman > /dev/null 2>&1; then + docker="podman" +else + echo "Could not find a usable OCI runtime, need either Docker or Podman." + exit 1 +fi + +DOCKER_IMAGE_NAME="netdata/static-builder" + +if [ "${BUILDARCH}" != "$(uname -m)" ] && [ "$(uname -m)" = 'x86_64' ] && [ -z "${SKIP_EMULATION}" ]; then + ${docker} run --rm --privileged multiarch/qemu-user-static --reset -p yes || exit 1 +fi + +if ${docker} inspect "${DOCKER_IMAGE_NAME}" > /dev/null 2>&1; then + if ${docker} image inspect "${DOCKER_IMAGE_NAME}" | grep -q 'Variant'; then + img_platform="$(${docker} image inspect "${DOCKER_IMAGE_NAME}" --format '{{.Os}}/{{.Architecture}}/{{.Variant}}')" + else + img_platform="$(${docker} image inspect "${DOCKER_IMAGE_NAME}" --format '{{.Os}}/{{.Architecture}}')" + fi + + if [ "${img_platform}" != "${platform}" ]; then + ${docker} image rm "${DOCKER_IMAGE_NAME}" || exit 1 + fi +fi + +if ! ${docker} inspect "${DOCKER_IMAGE_NAME}" > /dev/null 2>&1; then + ${docker} pull --platform "${platform}" "${DOCKER_IMAGE_NAME}" +fi + +# Run the build script inside the container +if [ -t 1 ]; then + run ${docker} run --rm -e BUILDARCH="${BUILDARCH}" -a stdin -a stdout -a stderr -i -t -v "$(pwd)":/netdata:rw \ + "${DOCKER_IMAGE_NAME}" \ + /bin/sh /netdata/packaging/makeself/build.sh "${@}" +else + run ${docker} run --rm -e BUILDARCH="${BUILDARCH}" -v "$(pwd)":/netdata:rw \ + -e GITHUB_ACTIONS="${GITHUB_ACTIONS}" "${DOCKER_IMAGE_NAME}" \ + /bin/sh /netdata/packaging/makeself/build.sh "${@}" +fi diff --git a/packaging/makeself/build-x86_64-static.sh b/packaging/makeself/build-x86_64-static.sh new file mode 100755 index 0000000..59d2078 --- /dev/null +++ b/packaging/makeself/build-x86_64-static.sh @@ -0,0 +1,7 @@ +#!/usr/bin/env bash + +# SPDX-License-Identifier: GPL-3.0-or-later + +SCRIPT_DIR="$( cd "$( dirname "${BASH_SOURCE[0]}" )" &> /dev/null && pwd )" + +"${SCRIPT_DIR}/build-static.sh" x86_64 "${@}" diff --git a/packaging/makeself/build.sh b/packaging/makeself/build.sh new file mode 100755 index 0000000..3ac600e --- /dev/null +++ b/packaging/makeself/build.sh @@ -0,0 +1,65 @@ +#!/usr/bin/env sh +# SPDX-License-Identifier: GPL-3.0-or-later + +# ----------------------------------------------------------------------------- +# parse command line arguments + +set -e + +export NETDATA_BUILD_WITH_DEBUG=0 + +while [ -n "${1}" ]; do + case "${1}" in + debug) + export NETDATA_BUILD_WITH_DEBUG=1 + ;; + + *) ;; + + esac + + shift +done + +# ----------------------------------------------------------------------------- + +# First run install-alpine-packages.sh under alpine linux to install +# the required packages. build-x86_64-static.sh will do this for you +# using docker. + +mkdir -p /usr/src +cp -va /netdata /usr/src/netdata +chown -R root:root /usr/src/netdata + +cd /usr/src/netdata/packaging/makeself || exit 1 + +git clean -dxf +git submodule foreach --recursive git clean -dxf + +cat >&2 << EOF +This program will create a self-extracting shell package containing +a statically linked netdata, able to run on any 64bit Linux system, +without any dependencies from the target system. + +It can be used to have netdata running in no-time, or in cases the +target Linux system cannot compile netdata. +EOF + +if [ ! -d tmp ]; then + mkdir tmp || exit 1 +else + rm -rf tmp/* +fi + +if [ -z "${GITHUB_ACTIONS}" ]; then + export GITHUB_ACTIONS=false +fi + +if ! ./run-all-jobs.sh "$@"; then + printf >&2 "Build failed." + exit 1 +fi + +mkdir -p /netdata/artifacts +cp -va /usr/src/netdata/artifacts/* /netdata/artifacts/ +chown -R "$(stat -c '%u:%g' /netdata)" /netdata/artifacts/ diff --git a/packaging/makeself/functions.sh b/packaging/makeself/functions.sh new file mode 100755 index 0000000..31c28d8 --- /dev/null +++ b/packaging/makeself/functions.sh @@ -0,0 +1,104 @@ +#!/usr/bin/env bash +# SPDX-License-Identifier: GPL-3.0-or-later + +# ----------------------------------------------------------------------------- + +# allow running the jobs by hand +[ -z "${NETDATA_BUILD_WITH_DEBUG}" ] && export NETDATA_BUILD_WITH_DEBUG=0 +[ -z "${NETDATA_INSTALL_PATH}" ] && export NETDATA_INSTALL_PATH="${1-/opt/netdata}" +[ -z "${NETDATA_MAKESELF_PATH}" ] && NETDATA_MAKESELF_PATH="$(dirname "${0}")/../.." +[ "${NETDATA_MAKESELF_PATH:0:1}" != "/" ] && NETDATA_MAKESELF_PATH="$(pwd)/${NETDATA_MAKESELF_PATH}" +[ -z "${NETDATA_SOURCE_PATH}" ] && export NETDATA_SOURCE_PATH="${NETDATA_MAKESELF_PATH}/../.." +export NETDATA_MAKESELF_PATH NETDATA_MAKESELF_PATH +export NULL= + +# make sure the path does not end with / +if [ "${NETDATA_INSTALL_PATH:$((${#NETDATA_INSTALL_PATH} - 1)):1}" = "/" ]; then + export NETDATA_INSTALL_PATH="${NETDATA_INSTALL_PATH:0:$((${#NETDATA_INSTALL_PATH} - 1))}" +fi + +# find the parent directory +NETDATA_INSTALL_PARENT="$(dirname "${NETDATA_INSTALL_PATH}")" +export NETDATA_INSTALL_PARENT + +# ----------------------------------------------------------------------------- + +# bash strict mode +set -euo pipefail + +# ----------------------------------------------------------------------------- + +fetch() { + local dir="${1}" url="${2}" sha256="${3}" key="${4}" + local tar="${dir}.tar.gz" + local cache="${NETDATA_SOURCE_PATH}/artifacts/cache/${BUILDARCH}/${key}" + + if [ -d "${NETDATA_MAKESELF_PATH}/tmp/${dir}" ]; then + rm -rf "${NETDATA_MAKESELF_PATH}/tmp/${dir}" + fi + + if [ -d "${cache}/${dir}" ]; then + echo "Found cached copy of build directory for ${key}, using it." + cp -a "${cache}/${dir}" "${NETDATA_MAKESELF_PATH}/tmp/" + CACHE_HIT=1 + else + echo "No cached copy of build directory for ${key} found, fetching sources instead." + + if [ ! -f "${NETDATA_MAKESELF_PATH}/tmp/${tar}" ]; then + run wget -O "${NETDATA_MAKESELF_PATH}/tmp/${tar}" "${url}" + fi + + # Check SHA256 of gzip'd tar file (apparently alpine's sha256sum requires + # two empty spaces between the checksum and the file's path) + set +e + echo "${sha256} ${NETDATA_MAKESELF_PATH}/tmp/${tar}" | sha256sum -c -s + local rc=$? + if [ ${rc} -ne 0 ]; then + echo >&2 "SHA256 verification of tar file ${tar} failed (rc=${rc})" + echo >&2 "expected: ${sha256}, got $(sha256sum "${NETDATA_MAKESELF_PATH}/tmp/${tar}")" + exit 1 + fi + set -e + + cd "${NETDATA_MAKESELF_PATH}/tmp" + run tar -zxpf "${tar}" + cd - + + CACHE_HIT=0 + fi + + run cd "${NETDATA_MAKESELF_PATH}/tmp/${dir}" +} + +store_cache() { + key="${1}" + src="${2}" + + cache="${NETDATA_SOURCE_PATH}/artifacts/cache/${BUILDARCH}/${key}" + + if [ "${CACHE_HIT:-0}" -eq 0 ]; then + if [ -d "${cache}" ]; then + rm -rf "${cache}" + fi + + mkdir -p "${cache}" + + cp -a "${src}" "${cache}" + fi +} + +# ----------------------------------------------------------------------------- + +# load the functions of the netdata-installer.sh +# shellcheck source=packaging/installer/functions.sh +. "${NETDATA_SOURCE_PATH}/packaging/installer/functions.sh" + +# ----------------------------------------------------------------------------- + +# debug +echo "ME=${0}" +echo "NETDATA_INSTALL_PARENT=${NETDATA_INSTALL_PARENT}" +echo "NETDATA_INSTALL_PATH=${NETDATA_INSTALL_PATH}" +echo "NETDATA_MAKESELF_PATH=${NETDATA_MAKESELF_PATH}" +echo "NETDATA_SOURCE_PATH=${NETDATA_SOURCE_PATH}" +echo "PROCESSORS=$(nproc)" diff --git a/packaging/makeself/install-alpine-packages.sh b/packaging/makeself/install-alpine-packages.sh new file mode 100755 index 0000000..d797433 --- /dev/null +++ b/packaging/makeself/install-alpine-packages.sh @@ -0,0 +1,49 @@ +#!/usr/bin/env sh +# +# Installation script for the alpine host +# to prepare the static binary +# +# Copyright: SPDX-License-Identifier: GPL-3.0-or-later +# +# Author: Paul Emm. Katsoulakis <paul@netdata.cloud> + +apk update || exit 1 +apk upgrade || exit 1 + +# Add required APK packages +apk add --no-cache -U \ + alpine-sdk \ + autoconf \ + automake \ + bash \ + binutils \ + cmake \ + curl \ + elfutils-dev \ + gcc \ + git \ + gnutls-dev \ + gzip \ + jq \ + libelf-static \ + libmnl-dev \ + libnetfilter_acct-dev \ + libtool \ + libuv-dev \ + libuv-static \ + lz4-dev \ + lz4-static \ + make \ + ncurses \ + netcat-openbsd \ + openssh \ + pkgconfig \ + protobuf-dev \ + snappy-dev \ + snappy-static \ + util-linux-dev \ + wget \ + xz \ + zlib-dev \ + zlib-static || + exit 1 diff --git a/packaging/makeself/install-or-update.sh b/packaging/makeself/install-or-update.sh new file mode 100755 index 0000000..be2b2f7 --- /dev/null +++ b/packaging/makeself/install-or-update.sh @@ -0,0 +1,266 @@ +#!/usr/bin/env bash + +# SPDX-License-Identifier: GPL-3.0-or-later + +# shellcheck source=./packaging/makeself/functions.sh +. "$(dirname "${0}")"/functions.sh + +export LC_ALL=C +umask 002 + +# Be nice on production environments +renice 19 $$ > /dev/null 2> /dev/null + +NETDATA_PREFIX="/opt/netdata" +NETDATA_USER_CONFIG_DIR="${NETDATA_PREFIX}/etc/netdata" + +# ----------------------------------------------------------------------------- +if [ -d /opt/netdata/etc/netdata.old ]; then + progress "Found old etc/netdata directory, reinstating this" + [ -d /opt/netdata/etc/netdata.new ] && rm -rf /opt/netdata/etc/netdata.new + mv -f /opt/netdata/etc/netdata /opt/netdata/etc/netdata.new + mv -f /opt/netdata/etc/netdata.old /opt/netdata/etc/netdata + + progress "Trigger stock config clean up" + rm -f /opt/netdata/etc/netdata/.installer-cleanup-of-stock-configs-done +fi + +STARTIT=1 +REINSTALL_OPTIONS="" +RELEASE_CHANNEL="nightly" # check .travis/create_artifacts.sh before modifying + +while [ "${1}" ]; do + case "${1}" in + "--dont-start-it") + STARTIT=0 + REINSTALL_OPTIONS="${REINSTALL_OPTIONS} ${1}" + ;; + "--auto-update" | "-u") ;; + "--stable-channel") + RELEASE_CHANNEL="stable" + REINSTALL_OPTIONS="${REINSTALL_OPTIONS} ${1}" + ;; + "--nightly-channel") + RELEASE_CHANNEL="nightly" + REINSTALL_OPTIONS="${REINSTALL_OPTIONS} ${1}" + ;; + "--disable-telemetry") + NETDATA_DISABLE_TELEMETRY=1 + REINSTALL_OPTIONS="${REINSTALL_OPTIONS} ${1}" + ;; + + *) echo >&2 "Unknown option '${1}'. Ignoring it." ;; + esac + shift 1 +done + +if [ ! "${DISABLE_TELEMETRY:-0}" -eq 0 ] || + [ -n "$DISABLE_TELEMETRY" ] || + [ ! "${DO_NOT_TRACK:-0}" -eq 0 ] || + [ -n "$DO_NOT_TRACK" ]; then + NETDATA_DISABLE_TELEMETRY=1 + REINSTALL_OPTIONS="${REINSTALL_OPTIONS} --disable-telemetry" +fi + +deleted_stock_configs=0 +if [ ! -f "etc/netdata/.installer-cleanup-of-stock-configs-done" ]; then + + # ----------------------------------------------------------------------------- + progress "Deleting stock configuration files from user configuration directory" + + declare -A configs_signatures=() + source "system/configs.signatures" + + if [ ! -d etc/netdata ]; then + run mkdir -p etc/netdata + fi + + md5sum="$(command -v md5sum 2> /dev/null || command -v md5 2> /dev/null)" + while IFS= read -r -d '' x; do + # find it relative filename + f="${x/etc\/netdata\//}" + + # find the stock filename + t="${f/.conf.old/.conf}" + t="${t/.conf.orig/.conf}" + + if [ -n "${md5sum}" ]; then + # find the checksum of the existing file + md5="$(${md5sum} < "${x}" | cut -d ' ' -f 1)" + #echo >&2 "md5: ${md5}" + + # check if it matches + if [ "${configs_signatures[${md5}]}" = "${t}" ]; then + # it matches the default + run rm -f "${x}" + deleted_stock_configs=$((deleted_stock_configs + 1)) + fi + fi + done < <(find etc -type f) + + touch "etc/netdata/.installer-cleanup-of-stock-configs-done" +fi + +# ----------------------------------------------------------------------------- +progress "Attempt to create user/group netdata/netadata" + +NETDATA_WANTED_GROUPS="docker nginx varnish haproxy adm nsd proxy squid ceph nobody I2C" +NETDATA_ADDED_TO_GROUPS="" +# Default user/group +NETDATA_USER="root" +NETDATA_GROUP="root" + +if portable_add_group netdata; then + if portable_add_user netdata "/opt/netdata"; then + progress "Add user netdata to required user groups" + for g in ${NETDATA_WANTED_GROUPS}; do + # shellcheck disable=SC2086 + if portable_add_user_to_group ${g} netdata; then + NETDATA_ADDED_TO_GROUPS="${NETDATA_ADDED_TO_GROUPS} ${g}" + else + run_failed "Failed to add netdata user to secondary groups" + fi + done + NETDATA_USER="netdata" + NETDATA_GROUP="netdata" + else + run_failed "I could not add user netdata, will be using root" + fi +else + run_failed "I could not add group netdata, so no user netdata will be created as well. Netdata run as root:root" +fi + +# ----------------------------------------------------------------------------- +progress "Install logrotate configuration for netdata" + +install_netdata_logrotate || run_failed "Cannot install logrotate file for netdata." + +# ----------------------------------------------------------------------------- +progress "Telemetry configuration" + +# Opt-out from telemetry program +if [ -n "${NETDATA_DISABLE_TELEMETRY}" ]; then + run touch "${NETDATA_USER_CONFIG_DIR}/.opt-out-from-anonymous-statistics" +else + printf "You can opt out from anonymous statistics via the --disable-telemetry option, or by creating an empty file %s \n\n" "${NETDATA_USER_CONFIG_DIR}/.opt-out-from-anonymous-statistics" +fi + +# ----------------------------------------------------------------------------- +progress "Install netdata at system init" + +install_netdata_service || run_failed "Cannot install netdata init service." + +set_netdata_updater_channel || run_failed "Cannot set netdata updater tool release channel to '${RELEASE_CHANNEL}'" + +# ----------------------------------------------------------------------------- +progress "Install (but not enable) netdata updater tool" +install_netdata_updater || run_failed "Cannot install netdata updater tool." + +# ----------------------------------------------------------------------------- +progress "creating quick links" + +dir_should_be_link() { + local p="${1}" t="${2}" d="${3}" old + + old="${PWD}" + cd "${p}" || return 0 + + if [ -e "${d}" ]; then + if [ -h "${d}" ]; then + run rm "${d}" + else + run mv -f "${d}" "${d}.old.$$" + fi + fi + + run ln -s "${t}" "${d}" + cd "${old}" +} + +dir_should_be_link . bin sbin +dir_should_be_link usr ../bin bin +dir_should_be_link usr ../bin sbin +dir_should_be_link usr . local + +dir_should_be_link . etc/netdata netdata-configs +dir_should_be_link . usr/share/netdata/web netdata-web-files +dir_should_be_link . usr/libexec/netdata netdata-plugins +dir_should_be_link . var/lib/netdata netdata-dbs +dir_should_be_link . var/cache/netdata netdata-metrics +dir_should_be_link . var/log/netdata netdata-logs + +dir_should_be_link etc/netdata ../../usr/lib/netdata/conf.d orig + +if [ ${deleted_stock_configs} -gt 0 ]; then + dir_should_be_link etc/netdata ../../usr/lib/netdata/conf.d "000.-.USE.THE.orig.LINK.TO.COPY.AND.EDIT.STOCK.CONFIG.FILES" +fi + +# ----------------------------------------------------------------------------- +progress "fix permissions" + +run chmod g+rx,o+rx /opt +run chown -R ${NETDATA_USER}:${NETDATA_GROUP} /opt/netdata + +# ----------------------------------------------------------------------------- + +progress "changing plugins ownership and setting setuid" + +for x in apps.plugin freeipmi.plugin ioping cgroup-network ebpf.plugin perf.plugin slabinfo.plugin nfacct.plugin xenstat.plugin; do + f="usr/libexec/netdata/plugins.d/${x}" + + if [ -f "${f}" ]; then + run chown root:${NETDATA_GROUP} "${f}" + run chmod 4750 "${f}" + fi +done + +if [ -f "usr/libexec/netdata/plugins.d/go.d.plugin" ] && command -v setcap 1>/dev/null 2>&1; then + run setcap "cap_net_admin+epi cap_net_raw=eip" "usr/libexec/netdata/plugins.d/go.d.plugin" +fi + +# fix the fping binary +if [ -f bin/fping ]; then + run chown root:${NETDATA_GROUP} bin/fping + run chmod 4750 bin/fping +fi + +# ----------------------------------------------------------------------------- + +echo "Configure TLS certificate paths" +if [ ! -L /opt/netdata/etc/ssl ] && [ -d /opt/netdata/etc/ssl ] ; then + echo "Preserving existing user configuration for TLS" +else + if [ -d /etc/pki/tls ] ; then + echo "Using /etc/pki/tls for TLS configuration and certificates" + ln -sf /etc/pki/tls /opt/netdata/etc/ssl + elif [ -d /etc/ssl ] ; then + echo "Using /etc/ssl for TLS configuration and certificates" + ln -sf /etc/ssl /opt/netdata/etc/ssl + else + echo "Using bundled TLS configuration and certificates" + ln -sf /opt/netdata/share/ssl /opt/netdata/etc/ssl + fi +fi + +# ----------------------------------------------------------------------------- + +echo "Save install options" +grep -qv 'IS_NETDATA_STATIC_BINARY="yes"' "${NETDATA_PREFIX}/etc/netdata/.environment" || echo IS_NETDATA_STATIC_BINARY=\"yes\" >> "${NETDATA_PREFIX}/etc/netdata/.environment" +sed -i "s/REINSTALL_OPTIONS=\".*\"/REINSTALL_OPTIONS=\"${REINSTALL_OPTIONS}\"/" "${NETDATA_PREFIX}/etc/netdata/.environment" + +# ----------------------------------------------------------------------------- +if [ ${STARTIT} -eq 0 ]; then + create_netdata_conf "${NETDATA_PREFIX}/etc/netdata/netdata.conf" + netdata_banner "is installed now!" +else + progress "starting netdata" + + if ! restart_netdata "${NETDATA_PREFIX}/bin/netdata"; then + create_netdata_conf "${NETDATA_PREFIX}/etc/netdata/netdata.conf" + netdata_banner "is installed and running now!" + else + create_netdata_conf "${NETDATA_PREFIX}/etc/netdata/netdata.conf" "http://localhost:19999/netdata.conf" + netdata_banner "is installed now!" + fi +fi +run chmod 0644 "${NETDATA_PREFIX}/etc/netdata/netdata.conf" diff --git a/packaging/makeself/jobs/10-prepare-destination.install.sh b/packaging/makeself/jobs/10-prepare-destination.install.sh new file mode 100755 index 0000000..4686841 --- /dev/null +++ b/packaging/makeself/jobs/10-prepare-destination.install.sh @@ -0,0 +1,23 @@ +#!/usr/bin/env bash +# SPDX-License-Identifier: GPL-3.0-or-later + +# shellcheck source=packaging/makeself/functions.sh +. "$(dirname "${0}")/../functions.sh" "${@}" || exit 1 + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::group::Preparing build environment" || true + +[ -d "${NETDATA_INSTALL_PATH}.old" ] && run rm -rf "${NETDATA_INSTALL_PATH}.old" +[ -d "${NETDATA_INSTALL_PATH}" ] && run mv -f "${NETDATA_INSTALL_PATH}" "${NETDATA_INSTALL_PATH}.old" + +run mkdir -p "${NETDATA_INSTALL_PATH}/bin" +run mkdir -p "${NETDATA_INSTALL_PATH}/usr" +run cd "${NETDATA_INSTALL_PATH}" || exit 1 +run ln -s bin sbin +run cd "${NETDATA_INSTALL_PATH}/usr" || exit 1 +run ln -s ../bin bin +run ln -s ../sbin sbin +run ln -s . local + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::endgroup::" || true diff --git a/packaging/makeself/jobs/20-openssl.install.sh b/packaging/makeself/jobs/20-openssl.install.sh new file mode 100755 index 0000000..5d9aa06 --- /dev/null +++ b/packaging/makeself/jobs/20-openssl.install.sh @@ -0,0 +1,48 @@ +#!/usr/bin/env bash +# SPDX-License-Identifier: GPL-3.0-or-later + +# shellcheck source=packaging/makeself/functions.sh +. "$(dirname "${0}")/../functions.sh" "${@}" || exit 1 + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::group::Building OpenSSL" || true + +version="$(cat "$(dirname "${0}")/../openssl.version")" + +export CFLAGS='-fno-lto -pipe' +export LDFLAGS='-static' +export PKG_CONFIG="pkg-config --static" + +if [ -d "${NETDATA_MAKESELF_PATH}/tmp/openssl" ]; then + rm -rf "${NETDATA_MAKESELF_PATH}/tmp/openssl" +fi + +if [ -d "${NETDATA_MAKESELF_PATH}/tmp/openssl" ]; then + rm -rf "${NETDATA_MAKESELF_PATH}/tmp/openssl" +fi + +cache="${NETDATA_SOURCE_PATH}/artifacts/cache/${BUILDARCH}/openssl" + +if [ -d "${cache}" ]; then + echo "Found cached copy of build directory for openssl, using it." + cp -a "${cache}/openssl" "${NETDATA_MAKESELF_PATH}/tmp/" + CACHE_HIT=1 +else + echo "No cached copy of build directory for openssl found, fetching sources instead." + run git clone --branch "${version}" --single-branch --depth 1 git://git.openssl.org/openssl.git "${NETDATA_MAKESELF_PATH}/tmp/openssl" + CACHE_HIT=0 +fi + +cd "${NETDATA_MAKESELF_PATH}/tmp/openssl" || exit 1 + +if [ "${CACHE_HIT:-0}" -eq 0 ]; then + run ./config -static no-tests --prefix=/openssl-static --openssldir=/opt/netdata/etc/ssl + run make -j "$(nproc)" +fi + +run make -j "$(nproc)" install_sw + +store_cache openssl "${NETDATA_MAKESELF_PATH}/tmp/openssl" + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::endgroup::" || true diff --git a/packaging/makeself/jobs/50-bash-5.1.16.install.sh b/packaging/makeself/jobs/50-bash-5.1.16.install.sh new file mode 100755 index 0000000..d9f6e5b --- /dev/null +++ b/packaging/makeself/jobs/50-bash-5.1.16.install.sh @@ -0,0 +1,49 @@ +#!/usr/bin/env bash +# SPDX-License-Identifier: GPL-3.0-or-later + +# shellcheck source=packaging/makeself/functions.sh +. "$(dirname "${0}")/../functions.sh" "${@}" || exit 1 + +version="5.1.16" + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::group::building bash" || true + +fetch "bash-${version}" "http://ftp.gnu.org/gnu/bash/bash-${version}.tar.gz" \ + 5bac17218d3911834520dad13cd1f85ab944e1c09ae1aba55906be1f8192f558 bash + +export CFLAGS="-pipe" +export PKG_CONFIG_PATH="/openssl-static/lib/pkgconfig" + +if [ "${CACHE_HIT:-0}" -eq 0 ]; then + run ./configure \ + --prefix="${NETDATA_INSTALL_PATH}" \ + --without-bash-malloc \ + --enable-static-link \ + --enable-net-redirections \ + --enable-array-variables \ + --disable-progcomp \ + --disable-profiling \ + --disable-nls \ + --disable-dependency-tracking + + run make clean + run make -j "$(nproc)" + + cat > examples/loadables/Makefile <<-EOF + all: + clean: + install: + EOF +fi + +run make install + +store_cache bash "${NETDATA_MAKESELF_PATH}/tmp/bash-${version}" + +if [ "${NETDATA_BUILD_WITH_DEBUG}" -eq 0 ]; then + run strip "${NETDATA_INSTALL_PATH}"/bin/bash +fi + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::endgroup::" || true diff --git a/packaging/makeself/jobs/50-curl-7.82.0.install.sh b/packaging/makeself/jobs/50-curl-7.82.0.install.sh new file mode 100755 index 0000000..251d350 --- /dev/null +++ b/packaging/makeself/jobs/50-curl-7.82.0.install.sh @@ -0,0 +1,62 @@ +#!/usr/bin/env bash +# SPDX-License-Identifier: GPL-3.0-or-later + +# shellcheck source=packaging/makeself/functions.sh +. "$(dirname "${0}")/../functions.sh" "${@}" || exit 1 + +version="7.82.0" + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::group::Building cURL" || true + +fetch "curl-${version}" "https://curl.haxx.se/download/curl-${version}.tar.gz" \ + 910cc5fe279dc36e2cca534172c94364cf3fcf7d6494ba56e6c61a390881ddce curl + +export CFLAGS="-I/openssl-static/include -pipe" +export LDFLAGS="-static -L/openssl-static/lib" +export PKG_CONFIG="pkg-config --static" +export PKG_CONFIG_PATH="/openssl-static/lib/pkgconfig" + +if [ "${CACHE_HIT:-0}" -eq 0 ]; then + run autoreconf -fi + + run ./configure \ + --prefix="${NETDATA_INSTALL_PATH}" \ + --enable-optimize \ + --disable-shared \ + --enable-static \ + --enable-http \ + --disable-ldap \ + --disable-ldaps \ + --enable-proxy \ + --disable-dict \ + --disable-telnet \ + --disable-tftp \ + --disable-pop3 \ + --disable-imap \ + --disable-smb \ + --disable-smtp \ + --disable-gopher \ + --enable-ipv6 \ + --enable-cookies \ + --with-ca-fallback \ + --with-openssl \ + --disable-dependency-tracking + + # Curl autoconf does not honour the curl_LDFLAGS environment variable + run sed -i -e "s/LDFLAGS =/LDFLAGS = -all-static/" src/Makefile + + run make clean + run make -j "$(nproc)" +fi + +run make install + +store_cache curl "${NETDATA_MAKESELF_PATH}/tmp/curl-${version}" + +if [ "${NETDATA_BUILD_WITH_DEBUG}" -eq 0 ]; then + run strip "${NETDATA_INSTALL_PATH}"/bin/curl +fi + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::group::Preparing build environment" || true diff --git a/packaging/makeself/jobs/50-fping-5.1.install.sh b/packaging/makeself/jobs/50-fping-5.1.install.sh new file mode 100755 index 0000000..644b552 --- /dev/null +++ b/packaging/makeself/jobs/50-fping-5.1.install.sh @@ -0,0 +1,45 @@ +#!/usr/bin/env bash +# SPDX-License-Identifier: GPL-3.0-or-later + +# shellcheck source=packaging/makeself/functions.sh +. "$(dirname "${0}")/../functions.sh" "${@}" || exit 1 + +version="5.1" + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::group::Building fping" || true + +fetch "fping-${version}" "https://fping.org/dist/fping-${version}.tar.gz" \ + 1ee5268c063d76646af2b4426052e7d81a42b657e6a77d8e7d3d2e60fd7409fe fping + +export CFLAGS="-static -I/openssl-static/include -pipe" +export LDFLAGS="-static -L/openssl-static/lib" +export PKG_CONFIG_PATH="/openssl-static/lib/pkgconfig" + +if [ "${CACHE_HIT:-0}" -eq 0 ]; then + run ./configure \ + --prefix="${NETDATA_INSTALL_PATH}" \ + --enable-ipv4 \ + --enable-ipv6 \ + --disable-dependency-tracking + + cat > doc/Makefile <<-EOF + all: + clean: + install: + EOF + + run make clean + run make -j "$(nproc)" +fi + +run make install + +store_cache fping "${NETDATA_MAKESELF_PATH}/tmp/fping-${version}" + +if [ "${NETDATA_BUILD_WITH_DEBUG}" -eq 0 ]; then + run strip "${NETDATA_INSTALL_PATH}"/bin/fping +fi + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::endgroup::" || true diff --git a/packaging/makeself/jobs/50-ioping-1.2.install.sh b/packaging/makeself/jobs/50-ioping-1.2.install.sh new file mode 100755 index 0000000..160f45b --- /dev/null +++ b/packaging/makeself/jobs/50-ioping-1.2.install.sh @@ -0,0 +1,32 @@ +#!/usr/bin/env bash +# SPDX-License-Identifier: GPL-3.0-or-later + +# shellcheck source=packaging/makeself/functions.sh +. "$(dirname "${0}")/../functions.sh" "${@}" || exit 1 + +version='1.2' + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::group::Building ioping" || true + +fetch "ioping-${version}" "https://github.com/koct9i/ioping/archive/v${version}.tar.gz" \ + d3e4497c653a1e96df67c72ce2b70da18e9f5e3b93179a5bb57a6e30ceacfa75 ioping + +export CFLAGS="-static -pipe" + +if [ "${CACHE_HIT:-0}" -eq 0 ]; then + run make clean + run make -j "$(nproc)" +fi + +run mkdir -p "${NETDATA_INSTALL_PATH}"/usr/libexec/netdata/plugins.d/ +run install -o root -g root -m 4750 ioping "${NETDATA_INSTALL_PATH}"/usr/libexec/netdata/plugins.d/ + +store_cache ioping "${NETDATA_MAKESELF_PATH}/tmp/ioping-${version}" + +if [ "${NETDATA_BUILD_WITH_DEBUG}" -eq 0 ]; then + run strip "${NETDATA_INSTALL_PATH}"/usr/libexec/netdata/plugins.d/ioping +fi + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::endgroup::" || true diff --git a/packaging/makeself/jobs/70-netdata-git.install.sh b/packaging/makeself/jobs/70-netdata-git.install.sh new file mode 100755 index 0000000..ea6902a --- /dev/null +++ b/packaging/makeself/jobs/70-netdata-git.install.sh @@ -0,0 +1,58 @@ +#!/usr/bin/env bash +# SPDX-License-Identifier: GPL-3.0-or-later + +# shellcheck source=./packaging/makeself/functions.sh +. "${NETDATA_MAKESELF_PATH}"/functions.sh "${@}" || exit 1 + +cd "${NETDATA_SOURCE_PATH}" || exit 1 + +if [ "${NETDATA_BUILD_WITH_DEBUG}" -eq 0 ]; then + export CFLAGS="-static -O2 -I/openssl-static/include -pipe" +else + export CFLAGS="-static -O1 -pipe -ggdb -Wall -Wextra -Wformat-signedness -fstack-protector-all -D_FORTIFY_SOURCE=2 -DNETDATA_INTERNAL_CHECKS=1 -I/openssl-static/include" +fi + +export LDFLAGS="-static -L/openssl-static/lib" + +# We export this to 'yes', installer sets this to .environment. +# The updater consumes this one, so that it can tell whether it should update a static install or a non-static one +export IS_NETDATA_STATIC_BINARY="yes" + +# Set eBPF LIBC to "static" to bundle the `-static` variant of the kernel-collector +export EBPF_LIBC="static" +export PKG_CONFIG_PATH="/openssl-static/lib/pkgconfig" + +# Set correct CMake flags for building against non-System OpenSSL +# See: https://github.com/warmcat/libwebsockets/blob/master/READMEs/README.build.md +export CMAKE_FLAGS="-DOPENSSL_ROOT_DIR=/openssl-static -DOPENSSL_LIBRARIES=/openssl-static/lib -DCMAKE_INCLUDE_DIRECTORIES_PROJECT_BEFORE=/openssl-static -DLWS_OPENSSL_INCLUDE_DIRS=/openssl-static/include -DLWS_OPENSSL_LIBRARIES=/openssl-static/lib/libssl.a;/openssl-static/lib/libcrypto.a" + +run ./netdata-installer.sh \ + --install "${NETDATA_INSTALL_PARENT}" \ + --dont-wait \ + --dont-start-it \ + --require-cloud \ + --use-system-protobuf \ + --dont-scrub-cflags-even-though-it-may-break-things \ + --one-time-build + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::group::Finishing netdata install" || true + +# Properly mark the install type +cat > "${NETDATA_INSTALL_PATH}/etc/netdata/.install-type" <<-EOF + INSTALL_TYPE='manual-static' + PREBUILT_ARCH='${BUILDARCH}' + EOF + +# Remove the netdata.conf file from the tree. It has hard-coded sensible defaults builtin. +run rm -f "${NETDATA_INSTALL_PATH}/etc/netdata/netdata.conf" + +# Ensure the netdata binary is in fact statically linked +if run readelf -l "${NETDATA_INSTALL_PATH}"/bin/netdata | grep 'INTERP'; then + printf >&2 "Ooops. %s is not a statically linked binary!\n" "${NETDATA_INSTALL_PATH}"/bin/netdata + ldd "${NETDATA_INSTALL_PATH}"/bin/netdata + exit 1 +fi + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::endgroup::" || true diff --git a/packaging/makeself/jobs/90-netdata-runtime-check.sh b/packaging/makeself/jobs/90-netdata-runtime-check.sh new file mode 100755 index 0000000..a3c94ff --- /dev/null +++ b/packaging/makeself/jobs/90-netdata-runtime-check.sh @@ -0,0 +1,54 @@ +#!/usr/bin/env bash +# SPDX-License-Identifier: GPL-3.0-or-later + +# shellcheck source=./packaging/makeself/functions.sh +. "${NETDATA_MAKESELF_PATH}"/functions.sh "${@}" || exit 1 + +dump_log() { + cat ./netdata.log +} + +wait_for() { + host="${1}" + port="${2}" + name="${3}" + timeout="30" + + if command -v nc > /dev/null ; then + netcat="nc" + elif command -v netcat > /dev/null ; then + netcat="netcat" + else + printf "Unable to find a usable netcat command.\n" + return 1 + fi + + printf "Waiting for %s on %s:%s ... " "${name}" "${host}" "${port}" + + sleep 30 + + i=0 + while ! ${netcat} -z "${host}" "${port}"; do + sleep 1 + if [ "$i" -gt "$timeout" ]; then + printf "Timed out!\n" + return 1 + fi + i="$((i + 1))" + done + printf "OK\n" +} + +trap dump_log EXIT + +"${NETDATA_INSTALL_PATH}/bin/netdata" -D > ./netdata.log 2>&1 & + +wait_for localhost 19999 netdata || exit 1 + +curl -sS http://127.0.0.1:19999/api/v1/info > ./response || exit 1 + +cat ./response + +jq '.version' ./response || exit 1 + +trap - EXIT diff --git a/packaging/makeself/jobs/99-makeself.install.sh b/packaging/makeself/jobs/99-makeself.install.sh new file mode 100755 index 0000000..d29d058 --- /dev/null +++ b/packaging/makeself/jobs/99-makeself.install.sh @@ -0,0 +1,111 @@ +#!/usr/bin/env bash +# SPDX-License-Identifier: GPL-3.0-or-later + +# shellcheck source=packaging/makeself/functions.sh +. "$(dirname "${0}")/../functions.sh" "${@}" || exit 1 + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::group::Building self-extracting archive" || true + +run cd "${NETDATA_SOURCE_PATH}" || exit 1 + +# ----------------------------------------------------------------------------- +# find the netdata version + +VERSION="$("${NETDATA_INSTALL_PARENT}/netdata/bin/netdata" -v | cut -f 2 -d ' ')" + +if [ "${VERSION}" == "" ]; then + echo >&2 "Cannot find version number. Create makeself executable from source code with git tree structure." + exit 1 +fi + +# ----------------------------------------------------------------------------- +# copy the files needed by makeself installation + +run mkdir -p "${NETDATA_INSTALL_PATH}/system" + +run cp \ + packaging/makeself/post-installer.sh \ + packaging/makeself/install-or-update.sh \ + packaging/installer/functions.sh \ + configs.signatures \ + system/netdata-init-d \ + system/netdata-lsb \ + system/netdata-openrc \ + system/netdata.logrotate \ + system/netdata.service \ + "${NETDATA_INSTALL_PATH}/system/" + +# ----------------------------------------------------------------------------- +# create a wrapper to start our netdata with a modified path + +run mkdir -p "${NETDATA_INSTALL_PATH}/bin/srv" + +run mv "${NETDATA_INSTALL_PATH}/bin/netdata" \ + "${NETDATA_INSTALL_PATH}/bin/srv/netdata" || exit 1 + +cat > "${NETDATA_INSTALL_PATH}/bin/netdata" << EOF +#!${NETDATA_INSTALL_PATH}/bin/bash +export NETDATA_BASH_LOADABLES="DISABLE" +export PATH="${NETDATA_INSTALL_PATH}/bin:\${PATH}" +exec "${NETDATA_INSTALL_PATH}/bin/srv/netdata" "\${@}" +EOF +run chmod 755 "${NETDATA_INSTALL_PATH}/bin/netdata" + +# ----------------------------------------------------------------------------- +# copy the SSL/TLS configuration and certificates from the build system + +run cp -a /etc/ssl "${NETDATA_INSTALL_PATH}/share/ssl" + +# ----------------------------------------------------------------------------- +# remove the links to allow untaring the archive + +run rm "${NETDATA_INSTALL_PATH}/sbin" \ + "${NETDATA_INSTALL_PATH}/usr/bin" \ + "${NETDATA_INSTALL_PATH}/usr/sbin" \ + "${NETDATA_INSTALL_PATH}/usr/local" + +# ----------------------------------------------------------------------------- +# create the makeself archive + +run sed "s|NETDATA_VERSION|${VERSION}|g" < "${NETDATA_MAKESELF_PATH}/makeself.lsm" > "${NETDATA_MAKESELF_PATH}/makeself.lsm.tmp" + +run "${NETDATA_MAKESELF_PATH}/makeself.sh" \ + --gzip \ + --complevel 9 \ + --notemp \ + --needroot \ + --target "${NETDATA_INSTALL_PATH}" \ + --header "${NETDATA_MAKESELF_PATH}/makeself-header.sh" \ + --lsm "${NETDATA_MAKESELF_PATH}/makeself.lsm.tmp" \ + --license "${NETDATA_MAKESELF_PATH}/makeself-license.txt" \ + --help-header "${NETDATA_MAKESELF_PATH}/makeself-help-header.txt" \ + "${NETDATA_INSTALL_PATH}" \ + "${NETDATA_INSTALL_PATH}.gz.run" \ + "netdata, the real-time performance and health monitoring system" \ + ./system/post-installer.sh + +run rm "${NETDATA_MAKESELF_PATH}/makeself.lsm.tmp" + +# ----------------------------------------------------------------------------- +# copy it to the netdata build dir + +FILE="netdata-${BUILDARCH}-${VERSION}.gz.run" + +run mkdir -p artifacts +run mv "${NETDATA_INSTALL_PATH}.gz.run" "artifacts/${FILE}" + +[ -f "netdata-${BUILDARCH}-latest.gz.run" ] && rm "netdata-${BUILDARCH}-latest.gz.run" +run ln -s "artifacts/${FILE}" "netdata-${BUILDARCH}-latest.gz.run" + +if [ "${BUILDARCH}" = "x86_64" ]; then + [ -f "netdata-latest.gz.run" ] && rm "netdata-latest.gz.run" + run ln -s "artifacts/${FILE}" "netdata-latest.gz.run" + [ -f "artifacts/netdata-${VERSION}.gz.run" ] && rm "netdata-${VERSION}.gz.run" + run ln -s "./${FILE}" "artifacts/netdata-${VERSION}.gz.run" +fi + +# shellcheck disable=SC2015 +[ "${GITHUB_ACTIONS}" = "true" ] && echo "::endgroup::" || true + +echo >&2 "Self-extracting installer moved to 'artifacts/${FILE}'" diff --git a/packaging/makeself/makeself-header.sh b/packaging/makeself/makeself-header.sh new file mode 100755 index 0000000..0af3219 --- /dev/null +++ b/packaging/makeself/makeself-header.sh @@ -0,0 +1,556 @@ +# SPDX-License-Identifier: GPL-3.0-or-later +# shellcheck shell=sh +# shellcheck disable=SC2154,SC2039 +cat << EOF > "$archname" +#!/bin/sh +# This script was generated using Makeself $MS_VERSION + +ORIG_UMASK=\`umask\` +if test "$KEEP_UMASK" = n; then + umask 077 +fi + +CRCsum="$CRCsum" +MD5="$MD5sum" +TMPROOT=\${TMPDIR:=/tmp} +USER_PWD="\$PWD"; export USER_PWD + +label="$LABEL" +script="$SCRIPT" +scriptargs="$SCRIPTARGS" +licensetxt="$LICENSE" +helpheader='$HELPHEADER' +targetdir="$archdirname" +filesizes="$filesizes" +keep="$KEEP" +nooverwrite="$NOOVERWRITE" +quiet="n" +accept="n" +nodiskspace="n" +export_conf="$EXPORT_CONF" + +print_cmd_arg="" +if type printf > /dev/null; then + print_cmd="printf" +elif test -x /usr/ucb/echo; then + print_cmd="/usr/ucb/echo" +else + print_cmd="echo" +fi + +if test -d /usr/xpg4/bin; then + PATH=/usr/xpg4/bin:\$PATH + export PATH +fi + +unset CDPATH + +MS_Printf() +{ + \$print_cmd \$print_cmd_arg "\$1" +} + +MS_PrintLicense() +{ + if test x"\$licensetxt" != x; then + echo "\$licensetxt" + if test x"\$accept" != xy; then + while true + do + MS_Printf "Please type y to accept, n otherwise: " + read yn + if test x"\$yn" = xn; then + keep=n + eval \$finish; exit 1 + break; + elif test x"\$yn" = xy; then + break; + fi + done + fi + fi +} + +MS_diskspace() +{ + ( + df -kP "\$1" | tail -1 | awk '{ if (\$4 ~ /%/) {print \$3} else {print \$4} }' + ) +} + +MS_dd() +{ + blocks=\`expr \$3 / 1024\` + bytes=\`expr \$3 % 1024\` + dd if="\$1" ibs=\$2 skip=1 obs=1024 conv=sync 2> /dev/null | \\ + { test \$blocks -gt 0 && dd ibs=1024 obs=1024 count=\$blocks ; \\ + test \$bytes -gt 0 && dd ibs=1 obs=1024 count=\$bytes ; } 2> /dev/null +} + +MS_dd_Progress() +{ + if test x"\$noprogress" = xy; then + MS_dd \$@ + return \$? + fi + file="\$1" + offset=\$2 + length=\$3 + pos=0 + bsize=4194304 + while test \$bsize -gt \$length; do + bsize=\`expr \$bsize / 4\` + done + blocks=\`expr \$length / \$bsize\` + bytes=\`expr \$length % \$bsize\` + ( + dd ibs=\$offset skip=1 2>/dev/null + pos=\`expr \$pos \+ \$bsize\` + MS_Printf " 0%% " 1>&2 + if test \$blocks -gt 0; then + while test \$pos -le \$length; do + dd bs=\$bsize count=1 2>/dev/null + pcent=\`expr \$length / 100\` + pcent=\`expr \$pos / \$pcent\` + if test \$pcent -lt 100; then + MS_Printf "\b\b\b\b\b\b\b" 1>&2 + if test \$pcent -lt 10; then + MS_Printf " \$pcent%% " 1>&2 + else + MS_Printf " \$pcent%% " 1>&2 + fi + fi + pos=\`expr \$pos \+ \$bsize\` + done + fi + if test \$bytes -gt 0; then + dd bs=\$bytes count=1 2>/dev/null + fi + MS_Printf "\b\b\b\b\b\b\b" 1>&2 + MS_Printf " 100%% " 1>&2 + ) < "\$file" +} + +MS_Help() +{ + cat << EOH >&2 +\${helpheader}Makeself version $MS_VERSION + 1) Getting help or info about \$0 : + \$0 --help Print this message + \$0 --info Print embedded info : title, default target directory, embedded script ... + \$0 --lsm Print embedded lsm entry (or no LSM) + \$0 --list Print the list of files in the archive + \$0 --check Checks integrity of the archive + + 2) Running \$0 : + \$0 [options] [--] [additional arguments to embedded script] + with following options (in that order) + --confirm Ask before running embedded script + --quiet Do not print anything except error messages + --accept Accept the license + --noexec Do not run embedded script + --keep Do not erase target directory after running + the embedded script + --noprogress Do not show the progress during the decompression + --nox11 Do not spawn an xterm + --nochown Do not give the extracted files to the current user + --nodiskspace Do not check for available disk space + --target dir Extract directly to a target directory + directory path can be either absolute or relative + --tar arg1 [arg2 ...] Access the contents of the archive through the tar command + -- Following arguments will be passed to the embedded script +EOH +} + +MS_Check() +{ + OLD_PATH="\$PATH" + PATH=\${GUESS_MD5_PATH:-"\$OLD_PATH:/bin:/usr/bin:/sbin:/usr/local/ssl/bin:/usr/local/bin:/opt/openssl/bin"} + MD5_ARG="" + MD5_PATH=\`exec <&- 2>&-; which md5sum || command -v md5sum || type md5sum\` + test -x "\$MD5_PATH" || MD5_PATH=\`exec <&- 2>&-; which md5 || command -v md5 || type md5\` + test -x "\$MD5_PATH" || MD5_PATH=\`exec <&- 2>&-; which digest || command -v digest || type digest\` + PATH="\$OLD_PATH" + + if test x"\$quiet" = xn; then + MS_Printf "Verifying archive integrity..." + fi + offset=\`head -n $SKIP "\$1" | wc -c | tr -d " "\` + verb=\$2 + i=1 + for s in \$filesizes + do + crc=\`echo \$CRCsum | cut -d" " -f\$i\` + if test -x "\$MD5_PATH"; then + if test x"\`basename \$MD5_PATH\`" = xdigest; then + MD5_ARG="-a md5" + fi + md5=\`echo \$MD5 | cut -d" " -f\$i\` + if test x"\$md5" = x00000000000000000000000000000000; then + test x"\$verb" = xy && echo " \$1 does not contain an embedded MD5 checksum." >&2 + else + md5sum=\`MS_dd_Progress "\$1" \$offset \$s | eval "\$MD5_PATH \$MD5_ARG" | cut -b-32\`; + if test x"\$md5sum" != x"\$md5"; then + echo "Error in MD5 checksums: \$md5sum is different from \$md5" >&2 + exit 2 + else + test x"\$verb" = xy && MS_Printf " MD5 checksums are OK." >&2 + fi + crc="0000000000"; verb=n + fi + fi + if test x"\$crc" = x0000000000; then + test x"\$verb" = xy && echo " \$1 does not contain a CRC checksum." >&2 + else + sum1=\`MS_dd_Progress "\$1" \$offset \$s | CMD_ENV=xpg4 cksum | awk '{print \$1}'\` + if test x"\$sum1" = x"\$crc"; then + test x"\$verb" = xy && MS_Printf " CRC checksums are OK." >&2 + else + echo "Error in checksums: \$sum1 is different from \$crc" >&2 + exit 2; + fi + fi + i=\`expr \$i + 1\` + offset=\`expr \$offset + \$s\` + done + if test x"\$quiet" = xn; then + echo " All good." + fi +} + +UnTAR() +{ + if test x"\$quiet" = xn; then + tar \$1vf - $UNTAR_EXTRA 2>&1 || { echo " ... Extraction failed." > /dev/tty; kill -15 \$$; } + else + tar \$1f - $UNTAR_EXTRA 2>&1 || { echo Extraction failed. > /dev/tty; kill -15 \$$; } + fi +} + +finish=true +xterm_loop= +noprogress=$NOPROGRESS +nox11=$NOX11 +copy=$COPY +ownership=y +verbose=n + +initargs="\$@" + +while true +do + case "\$1" in + -h | --help) + MS_Help + exit 0 + ;; + -q | --quiet) + quiet=y + noprogress=y + shift + ;; + --accept) + accept=y + shift + ;; + --info) + echo Identification: "\$label" + echo Target directory: "\$targetdir" + echo Uncompressed size: $USIZE KB + echo Compression: $COMPRESS + echo Date of packaging: $DATE + echo Built with Makeself version $MS_VERSION on $OSTYPE + echo Build command was: "$MS_COMMAND" + if test x"\$script" != x; then + echo Script run after extraction: + echo " " \$script \$scriptargs + fi + if test x"$copy" = xcopy; then + echo "Archive will copy itself to a temporary location" + fi + if test x"$NEED_ROOT" = xy; then + echo "Root permissions required for extraction" + fi + if test x"$KEEP" = xy; then + echo "directory \$targetdir is permanent" + else + echo "\$targetdir will be removed after extraction" + fi + exit 0 + ;; + --dumpconf) + echo LABEL=\"\$label\" + echo SCRIPT=\"\$script\" + echo SCRIPTARGS=\"\$scriptargs\" + echo archdirname=\"$archdirname\" + echo KEEP=$KEEP + echo NOOVERWRITE=$NOOVERWRITE + echo COMPRESS=$COMPRESS + echo filesizes=\"\$filesizes\" + echo CRCsum=\"\$CRCsum\" + echo MD5sum=\"\$MD5\" + echo OLDUSIZE=$USIZE + echo OLDSKIP=$((SKIP + 1)) + exit 0 + ;; + --lsm) +cat << EOLSM +EOF +eval "$LSM_CMD" +cat << EOF >> "$archname" +EOLSM + exit 0 + ;; + --list) + echo Target directory: \$targetdir + offset=\`head -n $SKIP "\$0" | wc -c | tr -d " "\` + for s in \$filesizes + do + MS_dd "\$0" \$offset \$s | eval "$GUNZIP_CMD" | UnTAR t + offset=\`expr \$offset + \$s\` + done + exit 0 + ;; + --tar) + offset=\`head -n $SKIP "\$0" | wc -c | tr -d " "\` + arg1="\$2" + if ! shift 2; then MS_Help; exit 1; fi + for s in \$filesizes + do + MS_dd "\$0" \$offset \$s | eval "$GUNZIP_CMD" | tar "\$arg1" - "\$@" + offset=\`expr \$offset + \$s\` + done + exit 0 + ;; + --check) + MS_Check "\$0" y + exit 0 + ;; + --confirm) + verbose=y + shift + ;; + --noexec) + script="" + shift + ;; + --keep) + keep=y + shift + ;; + --target) + keep=y + targetdir=\${2:-.} + if ! shift 2; then MS_Help; exit 1; fi + ;; + --noprogress) + noprogress=y + shift + ;; + --nox11) + nox11=y + shift + ;; + --nochown) + ownership=n + shift + ;; + --nodiskspace) + nodiskspace=y + shift + ;; + --xwin) + if test "$NOWAIT" = n; then + finish="echo Press Return to close this window...; read junk" + fi + xterm_loop=1 + shift + ;; + --phase2) + copy=phase2 + shift + ;; + --) + shift + break ;; + -*) + echo Unrecognized flag : "\$1" >&2 + MS_Help + exit 1 + ;; + *) + break ;; + esac +done + +if test x"\$quiet" = xy -a x"\$verbose" = xy; then + echo Cannot be verbose and quiet at the same time. >&2 + exit 1 +fi + +if test x"$NEED_ROOT" = xy -a \`id -u\` -ne 0; then + echo "Administrative privileges required for this archive (use su or sudo)" >&2 + exit 1 +fi + +if test x"\$copy" \!= xphase2; then + MS_PrintLicense +fi + +case "\$copy" in +copy) + tmpdir=\$TMPROOT/makeself.\$RANDOM.\`date +"%y%m%d%H%M%S"\`.\$\$ + mkdir "\$tmpdir" || { + echo "Could not create temporary directory \$tmpdir" >&2 + exit 1 + } + SCRIPT_COPY="\$tmpdir/makeself" + echo "Copying to a temporary location..." >&2 + cp "\$0" "\$SCRIPT_COPY" + chmod +x "\$SCRIPT_COPY" + cd "\$TMPROOT" + exec "\$SCRIPT_COPY" --phase2 -- \$initargs + ;; +phase2) + finish="\$finish ; rm -rf \`dirname \$0\`" + ;; +esac + +if test x"\$nox11" = xn; then + if tty -s; then # Do we have a terminal? + : + else + if test x"\$DISPLAY" != x -a x"\$xterm_loop" = x; then # No, but do we have X? + if xset q > /dev/null 2>&1; then # Check for valid DISPLAY variable + GUESS_XTERMS="xterm gnome-terminal rxvt dtterm eterm Eterm xfce4-terminal lxterminal kvt konsole aterm terminology" + for a in \$GUESS_XTERMS; do + if type \$a >/dev/null 2>&1; then + XTERM=\$a + break + fi + done + chmod a+x \$0 || echo Please add execution rights on \$0 + if test \`echo "\$0" | cut -c1\` = "/"; then # Spawn a terminal! + exec \$XTERM -title "\$label" -e "\$0" --xwin "\$initargs" + else + exec \$XTERM -title "\$label" -e "./\$0" --xwin "\$initargs" + fi + fi + fi + fi +fi + +if test x"\$targetdir" = x.; then + tmpdir="." +else + if test x"\$keep" = xy; then + if test x"\$nooverwrite" = xy && test -d "\$targetdir"; then + echo "Target directory \$targetdir already exists, aborting." >&2 + exit 1 + fi + if test x"\$quiet" = xn; then + echo "Creating directory \$targetdir" >&2 + fi + tmpdir="\$targetdir" + dashp="-p" + else + tmpdir="\$TMPROOT/selfgz\$\$\$RANDOM" + dashp="" + fi + mkdir \$dashp \$tmpdir || { + echo 'Cannot create target directory' \$tmpdir >&2 + echo 'You should try option --target dir' >&2 + eval \$finish + exit 1 + } +fi + +location="\`pwd\`" +if test x"\$SETUP_NOCHECK" != x1; then + MS_Check "\$0" +fi +offset=\`head -n $SKIP "\$0" | wc -c | tr -d " "\` + +if test x"\$verbose" = xy; then + MS_Printf "About to extract $USIZE KB in \$tmpdir ... Proceed ? [Y/n] " + read yn + if test x"\$yn" = xn; then + eval \$finish; exit 1 + fi +fi + +if test x"\$quiet" = xn; then + MS_Printf "Uncompressing \$label" +fi +res=3 +if test x"\$keep" = xn; then + trap 'echo Signal caught, cleaning up >&2; cd \$TMPROOT; /bin/rm -rf \$tmpdir; eval \$finish; exit 15' 1 2 3 15 +fi + +if test x"\$nodiskspace" = xn; then + leftspace=\`MS_diskspace \$tmpdir\` + if test -n "\$leftspace"; then + if test "\$leftspace" -lt $USIZE; then + echo + echo "Not enough space left in "\`dirname \$tmpdir\`" (\$leftspace KB) to decompress \$0 ($USIZE KB)" >&2 + echo "Use --nodiskspace option to skip this check and proceed anyway" >&2 + if test x"\$keep" = xn; then + echo "Consider setting TMPDIR to a directory with more free space." + fi + eval \$finish; exit 1 + fi + fi +fi + +for s in \$filesizes +do + if MS_dd_Progress "\$0" \$offset \$s | eval "$GUNZIP_CMD" | ( cd "\$tmpdir"; umask \$ORIG_UMASK ; UnTAR xp ) 1>/dev/null; then + if test x"\$ownership" = xy; then + (cd "\$tmpdir"; chown -R \`id -u\` .; chgrp -R \`id -g\` .) + fi + else + echo >&2 + echo "Unable to decompress \$0" >&2 + eval \$finish; exit 1 + fi + offset=\`expr \$offset + \$s\` +done +if test x"\$quiet" = xn; then + echo +fi + +cd "\$tmpdir" +res=0 +if test x"\$script" != x; then + if test x"\$export_conf" = x"y"; then + MS_BUNDLE="\$0" + MS_LABEL="\$label" + MS_SCRIPT="\$script" + MS_SCRIPTARGS="\$scriptargs" + MS_ARCHDIRNAME="\$archdirname" + MS_KEEP="\$KEEP" + MS_NOOVERWRITE="\$NOOVERWRITE" + MS_COMPRESS="\$COMPRESS" + export MS_BUNDLE MS_LABEL MS_SCRIPT MS_SCRIPTARGS + export MS_ARCHDIRNAME MS_KEEP MS_NOOVERWRITE MS_COMPRESS + fi + + if test x"\$verbose" = x"y"; then + MS_Printf "OK to execute: \$script \$scriptargs \$* ? [Y/n] " + read yn + if test x"\$yn" = x -o x"\$yn" = xy -o x"\$yn" = xY; then + eval "\"\$script\" \$scriptargs \"\\\$@\""; res=\$?; + fi + else + eval "\"\$script\" \$scriptargs \"\\\$@\""; res=\$? + fi + if test "\$res" -ne 0; then + test x"\$verbose" = xy && echo "The program '\$script' returned an error code (\$res)" >&2 + fi +fi +if test x"\$keep" = xn; then + cd \$TMPROOT + /bin/rm -rf \$tmpdir +fi +eval \$finish; exit \$res +EOF diff --git a/packaging/makeself/makeself-help-header.txt b/packaging/makeself/makeself-help-header.txt new file mode 100644 index 0000000..8ed15e2 --- /dev/null +++ b/packaging/makeself/makeself-help-header.txt @@ -0,0 +1,49 @@ + + ^ + |.-. .-. .-. .-. . netdata + | '-' '-' '-' '-' real-time performance monitoring, done right! + +----+-----+-----+-----+-----+-----+-----+-----+-----+-----+-----+-----+---> + + (C) Copyright 2017, Costa Tsaousis + All rights reserved + Released under GPL v3+ + + You are about to install netdata to this system. + netdata will be installed at: + + /opt/netdata + + The following changes will be made to your system: + + # USERS / GROUPS + User 'netdata' and group 'netdata' will be added, if not present. + + # LOGROTATE + This file will be installed if logrotate is present. + + - /etc/logrotate.d/netdata + + # SYSTEM INIT + This file will be installed if this system runs with systemd: + + - /lib/systemd/system/netdata.service + + or, for older CentOS, Debian/Ubuntu or OpenRC Gentoo: + + - /etc/init.d/netdata will be created + + + This package can also update a netdata installation that has been + created with another version of it. + + Your netdata configuration will be retained. + After installation, netdata will be (re-)started. + + netdata re-distributes a lot of open source software components. + Check its full license at: + https://github.com/netdata/netdata/blob/master/LICENSE.md + + Anonymous stat collection and reporting to Netdata is enabled + by default. To disable, pass --disable-telemetry option to the installer + or export the environment variable DISABLE_TELEMETRY to a non-zero or non-empty + value (e.g export DISABLE_TELEMETRY=1). diff --git a/packaging/makeself/makeself-license.txt b/packaging/makeself/makeself-license.txt new file mode 100644 index 0000000..b844e9a --- /dev/null +++ b/packaging/makeself/makeself-license.txt @@ -0,0 +1,44 @@ + + ^ + |.-. .-. .-. .-. . netdata + | '-' '-' '-' '-' real-time performance monitoring, done right! + +----+-----+-----+-----+-----+-----+-----+-----+-----+-----+-----+-----+---> + + (C) Copyright 2017, Costa Tsaousis + All rights reserved + Released under GPL v3+ + + You are about to install netdata to this system. + netdata will be installed at: + + /opt/netdata + + The following changes will be made to your system: + + # USERS / GROUPS + User 'netdata' and group 'netdata' will be added, if not present. + + # LOGROTATE + This file will be installed if logrotate is present. + + - /etc/logrotate.d/netdata + + # SYSTEM INIT + This file will be installed if this system runs with systemd: + + - /lib/systemd/system/netdata.service + + or, for older CentOS, Debian/Ubuntu or OpenRC Gentoo: + + - /etc/init.d/netdata will be created + + + This package can also update a netdata installation that has been + created with another version of it. + + Your netdata configuration will be retained. + After installation, netdata will be (re-)started. + + netdata re-distributes a lot of open source software components. + Check its full license at: + https://github.com/netdata/netdata/blob/master/LICENSE diff --git a/packaging/makeself/makeself.lsm b/packaging/makeself/makeself.lsm new file mode 100644 index 0000000..6bd4703 --- /dev/null +++ b/packaging/makeself/makeself.lsm @@ -0,0 +1,16 @@ +Begin3 +Title: netdata +Version: NETDATA_VERSION +Description: netdata is a system for distributed real-time performance and health monitoring. + It provides unparalleled insights, in real-time, of everything happening on the + system it runs (including applications such as web and database servers), using + modern interactive web dashboards. netdata is fast and efficient, designed to + permanently run on all systems (physical & virtual servers, containers, IoT + devices), without disrupting their core function. +Keywords: real-time performance and health monitoring +Author: Costa Tsaousis (costa@tsaousis.gr) +Maintained-by: Costa Tsaousis (costa@tsaousis.gr) +Original-site: https://my-netdata.io/ +Platform: Unix +Copying-policy: GPL +End diff --git a/packaging/makeself/makeself.sh b/packaging/makeself/makeself.sh new file mode 100755 index 0000000..1581f49 --- /dev/null +++ b/packaging/makeself/makeself.sh @@ -0,0 +1,621 @@ +#!/bin/sh +# SPDX-License-Identifier: GPL-3.0-or-later +# +# Makeself version 2.3.x +# by Stephane Peter <megastep@megastep.org> +# +# Utility to create self-extracting tar.gz archives. +# The resulting archive is a file holding the tar.gz archive with +# a small Shell script stub that uncompresses the archive to a temporary +# directory and then executes a given script from within that directory. +# +# Makeself home page: http://makeself.io/ +# +# Version 2.0 is a rewrite of version 1.0 to make the code easier to read and maintain. +# +# Version history : +# - 1.0 : Initial public release +# - 1.1 : The archive can be passed parameters that will be passed on to +# the embedded script, thanks to John C. Quillan +# - 1.2 : Package distribution, bzip2 compression, more command line options, +# support for non-temporary archives. Ideas thanks to Francois Petitjean +# - 1.3 : More patches from Bjarni R. Einarsson and Francois Petitjean: +# Support for no compression (--nocomp), script is no longer mandatory, +# automatic launch in an xterm, optional verbose output, and -target +# archive option to indicate where to extract the files. +# - 1.4 : Improved UNIX compatibility (Francois Petitjean) +# Automatic integrity checking, support of LSM files (Francois Petitjean) +# - 1.5 : Many bugfixes. Optionally disable xterm spawning. +# - 1.5.1 : More bugfixes, added archive options -list and -check. +# - 1.5.2 : Cosmetic changes to inform the user of what's going on with big +# archives (Quake III demo) +# - 1.5.3 : Check for validity of the DISPLAY variable before launching an xterm. +# More verbosity in xterms and check for embedded command's return value. +# Bugfix for Debian 2.0 systems that have a different "print" command. +# - 1.5.4 : Many bugfixes. Print out a message if the extraction failed. +# - 1.5.5 : More bugfixes. Added support for SETUP_NOCHECK environment variable to +# bypass checksum verification of archives. +# - 1.6.0 : Compute MD5 checksums with the md5sum command (patch from Ryan Gordon) +# - 2.0 : Brand new rewrite, cleaner architecture, separated header and UNIX ports. +# - 2.0.1 : Added --copy +# - 2.1.0 : Allow multiple tarballs to be stored in one archive, and incremental updates. +# Added --nochown for archives +# Stopped doing redundant checksums when not necessary +# - 2.1.1 : Work around insane behavior from certain Linux distros with no 'uncompress' command +# Cleaned up the code to handle error codes from compress. Simplified the extraction code. +# - 2.1.2 : Some bug fixes. Use head -n to avoid problems. +# - 2.1.3 : Bug fixes with command line when spawning terminals. +# Added --tar for archives, allowing to give arbitrary arguments to tar on the contents of the archive. +# Added --noexec to prevent execution of embedded scripts. +# Added --nomd5 and --nocrc to avoid creating checksums in archives. +# Added command used to create the archive in --info output. +# Run the embedded script through eval. +# - 2.1.4 : Fixed --info output. +# Generate random directory name when extracting files to . to avoid problems. (Jason Trent) +# Better handling of errors with wrong permissions for the directory containing the files. (Jason Trent) +# Avoid some race conditions (Ludwig Nussel) +# Unset the $CDPATH variable to avoid problems if it is set. (Debian) +# Better handling of dot files in the archive directory. +# - 2.1.5 : Made the md5sum detection consistent with the header code. +# Check for the presence of the archive directory +# Added --encrypt for symmetric encryption through gpg (Eric Windisch) +# Added support for the digest command on Solaris 10 for MD5 checksums +# Check for available disk space before extracting to the target directory (Andreas Schweitzer) +# Allow extraction to run asynchronously (patch by Peter Hatch) +# Use file descriptors internally to avoid error messages (patch by Kay Tiong Khoo) +# - 2.1.6 : Replaced one dot per file progress with a realtime progress percentage and a spinning cursor (Guy Baconniere) +# Added --noprogress to prevent showing the progress during the decompression (Guy Baconniere) +# Added --target dir to allow extracting directly to a target directory (Guy Baconniere) +# - 2.2.0 : Many bugfixes, updates and contributions from users. Check out the project page on Github for the details. +# - 2.3.0 : Option to specify packaging date to enable byte-for-byte reproducibility. (Marc Pawlowsky) +# +# (C) 1998-2017 by Stephane Peter <megastep@megastep.org> +# +# This software is released under the terms of the GNU GPL version 2 and above +# Please read the license at http://www.gnu.org/copyleft/gpl.html +# + +MS_VERSION=2.3.1 +MS_COMMAND="$0" +unset CDPATH + +for f in "${1+"$@"}"; do + MS_COMMAND="$MS_COMMAND \\\\ + \\\"$f\\\"" +done + +# For Solaris systems +if test -d /usr/xpg4/bin; then + PATH=/usr/xpg4/bin:$PATH + export PATH +fi + +# Procedures + +MS_Usage() +{ + echo "Usage: $0 [params] archive_dir file_name label startup_script [args]" + echo "params can be one or more of the following :" + echo " --version | -v : Print out Makeself version number and exit" + echo " --help | -h : Print out this help message" + echo " --tar-quietly : Suppress verbose output from the tar command" + echo " --quiet | -q : Do not print any messages other than errors." + echo " --gzip : Compress using gzip (default if detected)" + echo " --pigz : Compress with pigz" + echo " --bzip2 : Compress using bzip2 instead of gzip" + echo " --pbzip2 : Compress using pbzip2 instead of gzip" + echo " --xz : Compress using xz instead of gzip" + echo " --lzo : Compress using lzop instead of gzip" + echo " --lz4 : Compress using lz4 instead of gzip" + echo " --compress : Compress using the UNIX 'compress' command" + echo " --complevel lvl : Compression level for gzip pigz xz lzo lz4 bzip2 and pbzip2 (default 9)" + echo " --base64 : Instead of compressing, encode the data using base64" + echo " --gpg-encrypt : Instead of compressing, encrypt the data using GPG" + echo " --gpg-asymmetric-encrypt-sign" + echo " : Instead of compressing, asymmetrically encrypt and sign the data using GPG" + echo " --gpg-extra opt : Append more options to the gpg command line" + echo " --ssl-encrypt : Instead of compressing, encrypt the data using OpenSSL" + echo " --nocomp : Do not compress the data" + echo " --notemp : The archive will create archive_dir in the" + echo " current directory and uncompress in ./archive_dir" + echo " --needroot : Check that the root user is extracting the archive before proceeding" + echo " --copy : Upon extraction, the archive will first copy itself to" + echo " a temporary directory" + echo " --append : Append more files to an existing Makeself archive" + echo " The label and startup scripts will then be ignored" + echo " --target dir : Extract directly to a target directory" + echo " directory path can be either absolute or relative" + echo " --nooverwrite : Do not extract the archive if the specified target directory exists" + echo " --current : Files will be extracted to the current directory" + echo " Both --current and --target imply --notemp" + echo " --tar-extra opt : Append more options to the tar command line" + echo " --untar-extra opt : Append more options to the during the extraction of the tar archive" + echo " --nomd5 : Don't calculate an MD5 for archive" + echo " --nocrc : Don't calculate a CRC for archive" + echo " --header file : Specify location of the header script" + echo " --follow : Follow the symlinks in the archive" + echo " --noprogress : Do not show the progress during the decompression" + echo " --nox11 : Disable automatic spawn of a xterm" + echo " --nowait : Do not wait for user input after executing embedded" + echo " program from an xterm" + echo " --lsm file : LSM file describing the package" + echo " --license file : Append a license file" + echo " --help-header file : Add a header to the archive's --help output" + echo " --packaging-date date" + echo " : Use provided string as the packaging date" + echo " instead of the current date." + echo + echo " --keep-umask : Keep the umask set to shell default, rather than overriding when executing self-extracting archive." + echo " --export-conf : Export configuration variables to startup_script" + echo + echo "Do not forget to give a fully qualified startup script name" + echo "(i.e. with a ./ prefix if inside the archive)." + exit 1 +} + +# Default settings +if type gzip 2>&1 > /dev/null; then + COMPRESS=gzip +else + COMPRESS=Unix +fi +COMPRESS_LEVEL=9 +KEEP=n +CURRENT=n +NOX11=n +NOWAIT=n +APPEND=n +TAR_QUIETLY=n +KEEP_UMASK=n +QUIET=n +NOPROGRESS=n +COPY=none +NEED_ROOT=n +TAR_ARGS=cvf +TAR_EXTRA="" +GPG_EXTRA="" +DU_ARGS=-ks +HEADER=`dirname "$0"`/makeself-header.sh +TARGETDIR="" +NOOVERWRITE=n +DATE=`LC_ALL=C date` +EXPORT_CONF=n + +# LSM file stuff +LSM_CMD="echo No LSM. >> \"\$archname\"" + +while true +do + case "$1" in + --version | -v) + echo Makeself version $MS_VERSION + exit 0 + ;; + --pbzip2) + COMPRESS=pbzip2 + shift + ;; + --bzip2) + COMPRESS=bzip2 + shift + ;; + --gzip) + COMPRESS=gzip + shift + ;; + --pigz) + COMPRESS=pigz + shift + ;; + --xz) + COMPRESS=xz + shift + ;; + --lzo) + COMPRESS=lzo + shift + ;; + --lz4) + COMPRESS=lz4 + shift + ;; + --compress) + COMPRESS=Unix + shift + ;; + --base64) + COMPRESS=base64 + shift + ;; + --gpg-encrypt) + COMPRESS=gpg + shift + ;; + --gpg-asymmetric-encrypt-sign) + COMPRESS=gpg-asymmetric + shift + ;; + --gpg-extra) + GPG_EXTRA="$2" + if ! shift 2; then MS_Help; exit 1; fi + ;; + --ssl-encrypt) + COMPRESS=openssl + shift + ;; + --nocomp) + COMPRESS=none + shift + ;; + --complevel) + COMPRESS_LEVEL="$2" + if ! shift 2; then MS_Help; exit 1; fi + ;; + --notemp) + KEEP=y + shift + ;; + --copy) + COPY=copy + shift + ;; + --current) + CURRENT=y + KEEP=y + shift + ;; + --tar-extra) + TAR_EXTRA="$2" + if ! shift 2; then MS_Help; exit 1; fi + ;; + --untar-extra) + UNTAR_EXTRA="$2" + if ! shift 2; then MS_Help; exit 1; fi + ;; + --target) + TARGETDIR="$2" + KEEP=y + if ! shift 2; then MS_Help; exit 1; fi + ;; + --nooverwrite) + NOOVERWRITE=y + shift + ;; + --needroot) + NEED_ROOT=y + shift + ;; + --header) + HEADER="$2" + if ! shift 2; then MS_Help; exit 1; fi + ;; + --license) + LICENSE=`cat $2` + if ! shift 2; then MS_Help; exit 1; fi + ;; + --follow) + TAR_ARGS=cvhf + DU_ARGS=-ksL + shift + ;; + --noprogress) + NOPROGRESS=y + shift + ;; + --nox11) + NOX11=y + shift + ;; + --nowait) + NOWAIT=y + shift + ;; + --nomd5) + NOMD5=y + shift + ;; + --nocrc) + NOCRC=y + shift + ;; + --append) + APPEND=y + shift + ;; + --lsm) + LSM_CMD="cat \"$2\" >> \"\$archname\"" + if ! shift 2; then MS_Help; exit 1; fi + ;; + --packaging-date) + DATE="$2" + if ! shift 2; then MS_Help; exit 1; fi + ;; + --help-header) + HELPHEADER=`sed -e "s/'/'\\\\\''/g" $2` + if ! shift 2; then MS_Help; exit 1; fi + [ -n "$HELPHEADER" ] && HELPHEADER="$HELPHEADER +" + ;; + --tar-quietly) + TAR_QUIETLY=y + shift + ;; + --keep-umask) + KEEP_UMASK=y + shift + ;; + --export-conf) + EXPORT_CONF=y + shift + ;; + -q | --quiet) + QUIET=y + shift + ;; + -h | --help) + MS_Usage + ;; + -*) + echo Unrecognized flag : "$1" + MS_Usage + ;; + *) + break + ;; + esac +done + +if test $# -lt 1; then + MS_Usage +else + if test -d "$1"; then + archdir="$1" + else + echo "Directory $1 does not exist." >&2 + exit 1 + fi +fi +archname="$2" + +if test "$QUIET" = "y" || test "$TAR_QUIETLY" = "y"; then + if test "$TAR_ARGS" = "cvf"; then + TAR_ARGS="cf" + elif test "$TAR_ARGS" = "cvhf";then + TAR_ARGS="chf" + fi +fi + +if test "$APPEND" = y; then + if test $# -lt 2; then + MS_Usage + fi + + # Gather the info from the original archive + OLDENV=`sh "$archname" --dumpconf` + if test $? -ne 0; then + echo "Unable to update archive: $archname" >&2 + exit 1 + else + eval "$OLDENV" + fi +else + if test "$KEEP" = n -a $# = 3; then + echo "ERROR: Making a temporary archive with no embedded command does not make sense!" >&2 + echo >&2 + MS_Usage + fi + # We don't want to create an absolute directory unless a target directory is defined + if test "$CURRENT" = y; then + archdirname="." + elif test x$TARGETDIR != x; then + archdirname="$TARGETDIR" + else + archdirname=`basename "$1"` + fi + + if test $# -lt 3; then + MS_Usage + fi + + LABEL="$3" + SCRIPT="$4" + test "x$SCRIPT" = x || shift 1 + shift 3 + SCRIPTARGS="$*" +fi + +if test "$KEEP" = n -a "$CURRENT" = y; then + echo "ERROR: It is A VERY DANGEROUS IDEA to try to combine --notemp and --current." >&2 + exit 1 +fi + +case $COMPRESS in +gzip) + GZIP_CMD="gzip -c$COMPRESS_LEVEL" + GUNZIP_CMD="gzip -cd" + ;; +pigz) + GZIP_CMD="pigz -$COMPRESS_LEVEL" + GUNZIP_CMD="gzip -cd" + ;; +pbzip2) + GZIP_CMD="pbzip2 -c$COMPRESS_LEVEL" + GUNZIP_CMD="bzip2 -d" + ;; +bzip2) + GZIP_CMD="bzip2 -$COMPRESS_LEVEL" + GUNZIP_CMD="bzip2 -d" + ;; +xz) + GZIP_CMD="xz -c$COMPRESS_LEVEL" + GUNZIP_CMD="xz -d" + ;; +lzo) + GZIP_CMD="lzop -c$COMPRESS_LEVEL" + GUNZIP_CMD="lzop -d" + ;; +lz4) + GZIP_CMD="lz4 -c$COMPRESS_LEVEL" + GUNZIP_CMD="lz4 -d" + ;; +base64) + GZIP_CMD="base64" + GUNZIP_CMD="base64 -d -i" + ;; +gpg) + GZIP_CMD="gpg $GPG_EXTRA -ac -z$COMPRESS_LEVEL" + GUNZIP_CMD="gpg -d" + ;; +gpg-asymmetric) + GZIP_CMD="gpg $GPG_EXTRA -z$COMPRESS_LEVEL -es" + GUNZIP_CMD="gpg --yes -d" + ;; +openssl) + GZIP_CMD="openssl aes-256-cbc -a -salt -md sha256" + GUNZIP_CMD="openssl aes-256-cbc -d -a -md sha256" + ;; +Unix) + GZIP_CMD="compress -cf" + GUNZIP_CMD="exec 2>&-; uncompress -c || test \\\$? -eq 2 || gzip -cd" + ;; +none) + GZIP_CMD="cat" + GUNZIP_CMD="cat" + ;; +esac + +tmpfile="${TMPDIR:=/tmp}/mkself$$" + +if test -f "$HEADER"; then + oldarchname="$archname" + archname="$tmpfile" + # Generate a fake header to count its lines + SKIP=0 + . "$HEADER" + SKIP=`cat "$tmpfile" |wc -l` + # Get rid of any spaces + SKIP=`expr $SKIP` + rm -f "$tmpfile" + if test "$QUIET" = "n";then + echo Header is $SKIP lines long >&2 + fi + + archname="$oldarchname" +else + echo "Unable to open header file: $HEADER" >&2 + exit 1 +fi + +if test "$QUIET" = "n";then + echo +fi + +if test "$APPEND" = n; then + if test -f "$archname"; then + echo "WARNING: Overwriting existing file: $archname" >&2 + fi +fi + +USIZE=`du $DU_ARGS "$archdir" | awk '{print $1}'` + +if test "." = "$archdirname"; then + if test "$KEEP" = n; then + archdirname="makeself-$$-`date +%Y%m%d%H%M%S`" + fi +fi + +test -d "$archdir" || { echo "Error: $archdir does not exist."; rm -f "$tmpfile"; exit 1; } +if test "$QUIET" = "n";then + echo About to compress $USIZE KB of data... + echo Adding files to archive named \"$archname\"... +fi +exec 3<> "$tmpfile" +( cd "$archdir" && ( tar $TAR_EXTRA -$TAR_ARGS - . | eval "$GZIP_CMD" >&3 ) ) || \ + { echo Aborting: archive directory not found or temporary file: "$tmpfile" could not be created.; exec 3>&-; rm -f "$tmpfile"; exit 1; } +exec 3>&- # try to close the archive + +fsize=`cat "$tmpfile" | wc -c | tr -d " "` + +# Compute the checksums + +md5sum=00000000000000000000000000000000 +crcsum=0000000000 + +if test "$NOCRC" = y; then + if test "$QUIET" = "n";then + echo "skipping crc at user request" + fi +else + crcsum=`cat "$tmpfile" | CMD_ENV=xpg4 cksum | sed -e 's/ /Z/' -e 's/ /Z/' | cut -dZ -f1` + if test "$QUIET" = "n";then + echo "CRC: $crcsum" + fi +fi + +if test "$NOMD5" = y; then + if test "$QUIET" = "n";then + echo "skipping md5sum at user request" + fi +else + # Try to locate a MD5 binary + OLD_PATH=$PATH + PATH=${GUESS_MD5_PATH:-"$OLD_PATH:/bin:/usr/bin:/sbin:/usr/local/ssl/bin:/usr/local/bin:/opt/openssl/bin"} + MD5_ARG="" + MD5_PATH=`exec <&- 2>&-; which md5sum || command -v md5sum || type md5sum` + test -x "$MD5_PATH" || MD5_PATH=`exec <&- 2>&-; which md5 || command -v md5 || type md5` + test -x "$MD5_PATH" || MD5_PATH=`exec <&- 2>&-; which digest || command -v digest || type digest` + PATH=$OLD_PATH + if test -x "$MD5_PATH"; then + if test `basename ${MD5_PATH}`x = digestx; then + MD5_ARG="-a md5" + fi + md5sum=`cat "$tmpfile" | eval "$MD5_PATH $MD5_ARG" | cut -b-32`; + if test "$QUIET" = "n";then + echo "MD5: $md5sum" + fi + else + if test "$QUIET" = "n";then + echo "MD5: none, MD5 command not found" + fi + fi +fi + +if test "$APPEND" = y; then + mv "$archname" "$archname".bak || exit + + # Prepare entry for new archive + filesizes="$filesizes $fsize" + CRCsum="$CRCsum $crcsum" + MD5sum="$MD5sum $md5sum" + USIZE=`expr $USIZE + $OLDUSIZE` + # Generate the header + . "$HEADER" + # Append the original data + tail -n +$OLDSKIP "$archname".bak >> "$archname" + # Append the new data + cat "$tmpfile" >> "$archname" + + chmod +x "$archname" + rm -f "$archname".bak + if test "$QUIET" = "n";then + echo Self-extractable archive \"$archname\" successfully updated. + fi +else + filesizes="$fsize" + CRCsum="$crcsum" + MD5sum="$md5sum" + + # Generate the header + . "$HEADER" + + # Append the compressed tar data after the stub + if test "$QUIET" = "n";then + echo + fi + cat "$tmpfile" >> "$archname" + chmod +x "$archname" + if test "$QUIET" = "n";then + echo Self-extractable archive \"$archname\" successfully created. + fi +fi +rm -f "$tmpfile" diff --git a/packaging/makeself/openssl.version b/packaging/makeself/openssl.version new file mode 100644 index 0000000..ad1bcee --- /dev/null +++ b/packaging/makeself/openssl.version @@ -0,0 +1 @@ +OpenSSL_1_1_1n diff --git a/packaging/makeself/post-installer.sh b/packaging/makeself/post-installer.sh new file mode 100755 index 0000000..38cc41e --- /dev/null +++ b/packaging/makeself/post-installer.sh @@ -0,0 +1,11 @@ +#!/bin/sh +# SPDX-License-Identifier: GPL-3.0-or-later + +# This script is started using the shell of the system +# and executes our 'install-or-update.sh' script +# using the netdata supplied, statically linked BASH +# +# so, at 'install-or-update.sh' we are always sure +# we run under BASH v4. + +./bin/bash system/install-or-update.sh "${@}" diff --git a/packaging/makeself/run-all-jobs.sh b/packaging/makeself/run-all-jobs.sh new file mode 100755 index 0000000..dd123c2 --- /dev/null +++ b/packaging/makeself/run-all-jobs.sh @@ -0,0 +1,42 @@ +#!/usr/bin/env bash +# SPDX-License-Identifier: GPL-3.0-or-later + +set -e + +LC_ALL=C +umask 002 + +# ----------------------------------------------------------------------------- +# prepare the environment for the jobs + +# installation directory +export NETDATA_INSTALL_PATH="${1-/opt/netdata}" + +# our source directory +NETDATA_MAKESELF_PATH="$(dirname "${0}")" +export NETDATA_MAKESELF_PATH +if [ "${NETDATA_MAKESELF_PATH:0:1}" != "/" ]; then + NETDATA_MAKESELF_PATH="$(pwd)/${NETDATA_MAKESELF_PATH}" + export NETDATA_MAKESELF_PATH +fi + +# netdata source directory +export NETDATA_SOURCE_PATH="${NETDATA_MAKESELF_PATH}/../.." + +# make sure ${NULL} is empty +export NULL= + +# ----------------------------------------------------------------------------- + +cd "${NETDATA_MAKESELF_PATH}" || exit 1 + +# shellcheck source=packaging/makeself/functions.sh +. ./functions.sh "${@}" || exit 1 + +for x in jobs/*.install.sh; do + progress "running ${x}" + "${x}" "${NETDATA_INSTALL_PATH}" +done + +echo >&2 "All jobs for static packaging done successfully." +exit 0 diff --git a/packaging/makeself/uname2platform.sh b/packaging/makeself/uname2platform.sh new file mode 100755 index 0000000..7eab706 --- /dev/null +++ b/packaging/makeself/uname2platform.sh @@ -0,0 +1,18 @@ +#!/bin/sh +# +# SPDX-License-Identifier: GPL-3.0-or-later + +set -e + +BUILDARCH="${1}" + +case "${BUILDARCH}" in + x86_64) echo "linux/amd64" ;; + armv7l) echo "linux/arm/v7" ;; + aarch64) echo "linux/arm64/v8" ;; + ppc64le) echo "linux/ppc64le" ;; + *) + echo "Unknown target architecture '${BUILDARCH}'." >&2 + exit 1 + ;; +esac diff --git a/packaging/protobuf.checksums b/packaging/protobuf.checksums new file mode 100644 index 0000000..4a025c5 --- /dev/null +++ b/packaging/protobuf.checksums @@ -0,0 +1 @@ +89ac31a93832e204db6d73b1e80f39f142d5747b290f17340adce5be5b122f94 protobuf-cpp-3.19.4.tar.gz diff --git a/packaging/protobuf.version b/packaging/protobuf.version new file mode 100644 index 0000000..de24dee --- /dev/null +++ b/packaging/protobuf.version @@ -0,0 +1 @@ +3.19.4 diff --git a/packaging/repoconfig/Makefile b/packaging/repoconfig/Makefile new file mode 100644 index 0000000..d0f246a --- /dev/null +++ b/packaging/repoconfig/Makefile @@ -0,0 +1,31 @@ +FILES = netdata.list netdata-edge.list netdata-archive-keyring.gpg netdata-edge-archive-keyring.gpg netdata-repoconfig-archive-keyring.gpg + +all: $(FILES) + +netdata.list: netdata.list.in + cp netdata.list.in netdata.list + set -a && . /etc/os-release && sed -i -e "s/__DISTRO__/$${ID}/" -e "s/__SUITE__/$${VERSION_CODENAME}/" -e "s/__VARIANT__//" netdata.list + +netdata-edge.list: netdata.list.in + cp netdata.list.in netdata-edge.list + set -a && . /etc/os-release && sed -i -e "s/__DISTRO__/$${ID}/" -e "s/__SUITE__/$${VERSION_CODENAME}/" -e "s/__VARIANT__/-edge/" netdata-edge.list + +netdata-archive-keyring.gpg: + curl -L https://packagecloud.io/netdata/netdata/gpgkey | gpg --dearmor > netdata-archive-keyring.gpg + +netdata-edge-archive-keyring.gpg: + curl -L https://packagecloud.io/netdata/netdata-edge/gpgkey | gpg --dearmor > netdata-edge-archive-keyring.gpg + +netdata-repoconfig-archive-keyring.gpg: + curl -L https://packagecloud.io/netdata/netdata-repoconfig/gpgkey | gpg --dearmor > netdata-repoconfig-archive-keyring.gpg + +debian/tmp: + mkdir -p debian/tmp + +install: $(FILES) debian/tmp + cp $(FILES) debian/tmp/ + +clean: + rm -f $(FILES) + +.PHONY: clean diff --git a/packaging/repoconfig/build-deb.sh b/packaging/repoconfig/build-deb.sh new file mode 100755 index 0000000..97f929a --- /dev/null +++ b/packaging/repoconfig/build-deb.sh @@ -0,0 +1,49 @@ +#!/bin/sh + +# Extract distro info from /etc/os-release +DISTVERS="$(awk -F'"' '/VERSION_ID=/ {print $2}' /etc/os-release)" +DISTNAME="$(awk -F'=' '/^ID=/ {print $2}' /etc/os-release)" + +# Needed because dpkg is stupid and tries to configure things interactively if it sees a terminal. +export DEBIAN_FRONTEND=noninteractive + +# Pull in our dependencies +apt update || exit 1 +apt upgrade -y || exit 1 +apt install -y build-essential debhelper curl gnupg || exit 1 + +# Run the builds in an isolated source directory. +# This removes the need for cleanup, and ensures anything the build does +# doesn't muck with the user's sources. +cp -a /netdata/packaging/repoconfig /usr/src || exit 1 +cd /usr/src/repoconfig || exit 1 + +# pre/post options are after 1.18.8, is simpler to just check help for their existence than parsing version +if dpkg-buildpackage --help | grep "\-\-post\-clean" 2> /dev/null > /dev/null; then + dpkg-buildpackage --post-clean --pre-clean -b -us -uc || exit 1 +else + dpkg-buildpackage -b -us -uc || exit 1 +fi + +# Embed distro info in package name. +# This is required to make the repo actually standards compliant wthout packageclouds hacks. +distid="${DISTNAME}${DISTVERS}" +for pkg in /usr/src/*.deb; do + pkgname="$(basename "${pkg}" .deb)" + name="$(echo "${pkgname}" | cut -f 1 -d '_')" + version="$(echo "${pkgname}" | cut -f 2 -d '_')" + arch="$(echo "${pkgname}" | cut -f 3 -d '_')" + + newname="$(dirname "${pkg}")/${name}_${version}+${distid}_${arch}.deb" + mv "${pkg}" "${newname}" +done + +# Copy the built packages to /netdata/artifacts (which may be bind-mounted) +# Also ensure /netdata/artifacts exists and create it if it doesn't +[ -d /netdata/artifacts ] || mkdir -p /netdata/artifacts +cp -a /usr/src/*.deb /netdata/artifacts/ || exit 1 + +# Correct ownership of the artifacts. +# Without this, the artifacts directory and it's contents end up owned +# by root instead of the local user on Linux boxes +chown -R --reference=/netdata /netdata/artifacts diff --git a/packaging/repoconfig/build-rpm.sh b/packaging/repoconfig/build-rpm.sh new file mode 100755 index 0000000..6c07c66 --- /dev/null +++ b/packaging/repoconfig/build-rpm.sh @@ -0,0 +1,26 @@ +#!/bin/sh + +prefix='/root/rpmbuild' + +if command -v dnf > /dev/null ; then + dnf distro-sync -y --nodocs || exit 1 + dnf install -y --nodocs --setopt=install_weak_deps=False rpm-build || exit 1 +elif command -v yum > /dev/null ; then + yum distro-sync -y || exit 1 + yum install -y rpm-build || exit 1 +elif command -v zypper > /dev/null ; then + zypper update -y || exit 1 + zypper install -y rpm-build || exit 1 + prefix="/usr/src/packages" +fi + +mkdir -p "${prefix}/BUILD" "${prefix}/RPMS" "${prefix}/SRPMS" "${prefix}/SPECS" "${prefix}/SOURCES" || exit 1 +cp -a /netdata/packaging/repoconfig/netdata-repo.spec "${prefix}/SPECS" || exit 1 +cp -a /netdata/packaging/repoconfig/* "${prefix}/SOURCES/" || exit 1 + +rpmbuild -bb --rebuild "${prefix}/SPECS/netdata-repo.spec" || exit 1 + +[ -d /netdata/artifacts ] || mkdir -p /netdata/artifacts +find "${prefix}/RPMS/" -type f -name '*.rpm' -exec cp '{}' /netdata/artifacts \; || exit 1 + +chown -R --reference=/netdata /netdata/artifacts diff --git a/packaging/repoconfig/debian/changelog b/packaging/repoconfig/debian/changelog new file mode 100644 index 0000000..57c12d7 --- /dev/null +++ b/packaging/repoconfig/debian/changelog @@ -0,0 +1,12 @@ +netdata-repo (1-2) unstable; urgency=medium + + * Fixed package file naming for repo layout compliance + + -- Netdata Builder <bot@netdata.cloud> Mon, 6 Jun 2022 09:30:00 -0500 + +netdata-repo (1-1) unstable; urgency=medium + + * Initial Release + + -- Netdata Builder <bot@netdata.cloud> Mon, 14 Jun 2021 08:00:00 -0500 + diff --git a/packaging/repoconfig/debian/compat b/packaging/repoconfig/debian/compat new file mode 100644 index 0000000..ec63514 --- /dev/null +++ b/packaging/repoconfig/debian/compat @@ -0,0 +1 @@ +9 diff --git a/packaging/repoconfig/debian/control b/packaging/repoconfig/debian/control new file mode 100644 index 0000000..5fdcf14 --- /dev/null +++ b/packaging/repoconfig/debian/control @@ -0,0 +1,19 @@ +Source: netdata-repo +Section: net +Priority: optional +Maintainer: Netdata Builder <bot@netdata.cloud> +Standards-Version: 3.9.6 +Build-Depends: debhelper (>= 9), curl, gnupg +Homepage: https://netdata.cloud + +Package: netdata-repo +Architecture: all +Depends: apt-transport-https, debian-archive-keyring, gnupg +Conflicts: netdata-repo-edge +Description: Configuration for the official Netdata Stable package repository. + +Package: netdata-repo-edge +Architecture:all +Depends: apt-transport-https, debian-archive-keyring, gnupg +Conflicts: netdata-repo +Description: Configuration for the official Netdata Edge package repository. diff --git a/packaging/repoconfig/debian/copyright b/packaging/repoconfig/debian/copyright new file mode 100644 index 0000000..193b45e --- /dev/null +++ b/packaging/repoconfig/debian/copyright @@ -0,0 +1,10 @@ +Format: http://www.debian.org/doc/packaging-manuals/copyright-format/1.0/ +Upstream-Name: Netdata +Upstream-Contact: Costa Tsaousis <costa@netdata.cloud> +Source: https://github.com/netdata/netdata + +Files: * +Copyright: 2021 Netdata Inc. +License: GPL-3+ + On Debian systems, the complete text of the GNU General Public + License version 3 can be found in /usr/share/common-licenses/GPL-3. diff --git a/packaging/repoconfig/debian/rules b/packaging/repoconfig/debian/rules new file mode 100755 index 0000000..0151b96 --- /dev/null +++ b/packaging/repoconfig/debian/rules @@ -0,0 +1,21 @@ +#!/usr/bin/make -f + +TOP = $(CURDIR)/debian/netdata-repo +TOP_EDGE = $(CURDIR)/debian/netdata-repo-edge +TEMPTOP = $(CURDIR)/debian/tmp + +%: + dh $@ + +override_dh_configure: + true + +override_dh_install: + mkdir -p $(TOP)/etc/apt/sources.list.d $(TOP)/etc/apt/trusted.gpg.d/ + mv -f $(TEMPTOP)/netdata.list $(TOP)/etc/apt/sources.list.d + mv -f $(TEMPTOP)/netdata-archive-keyring.gpg $(TOP)/etc/apt/trusted.gpg.d + cp $(TEMPTOP)/netdata-repoconfig-archive-keyring.gpg $(TOP)/etc/apt/trusted.gpg.d + mkdir -p $(TOP_EDGE)/etc/apt/sources.list.d $(TOP_EDGE)/etc/apt/trusted.gpg.d/ + mv -f $(TEMPTOP)/netdata-edge.list $(TOP_EDGE)/etc/apt/sources.list.d + mv -f $(TEMPTOP)/netdata-edge-archive-keyring.gpg $(TOP_EDGE)/etc/apt/trusted.gpg.d + cp $(TEMPTOP)/netdata-repoconfig-archive-keyring.gpg $(TOP_EDGE)/etc/apt/trusted.gpg.d diff --git a/packaging/repoconfig/debian/source/format b/packaging/repoconfig/debian/source/format new file mode 100644 index 0000000..163aaf8 --- /dev/null +++ b/packaging/repoconfig/debian/source/format @@ -0,0 +1 @@ +3.0 (quilt) diff --git a/packaging/repoconfig/netdata-edge.repo.centos b/packaging/repoconfig/netdata-edge.repo.centos new file mode 100644 index 0000000..af56384 --- /dev/null +++ b/packaging/repoconfig/netdata-edge.repo.centos @@ -0,0 +1,21 @@ +[netdata-edge] +name=Netdata Edge +baseurl=https://packagecloud.io/netdata/netdata-edge/el/$releasever/$basearch +repo_gpgcheck=1 +gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata-edge/gpgkey +enabled=1 +sslverify=1 +sslcacert=/etc/pki/tls/certs/ca-bundle.crt +priority=50 + +[netdata-repoconfig] +name=Netdata Repository Config +baseurl=https://packagecloud.io/netdata/netdata-repoconfig/el/$releasever/$basearch +repo_gpgcheck=1 +gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata-repoconfig/gpgkey +enabled=1 +sslverify=1 +sslcacert=/etc/pki/tls/certs/ca-bundle.crt +priority=50 diff --git a/packaging/repoconfig/netdata-edge.repo.fedora b/packaging/repoconfig/netdata-edge.repo.fedora new file mode 100644 index 0000000..902e00c --- /dev/null +++ b/packaging/repoconfig/netdata-edge.repo.fedora @@ -0,0 +1,21 @@ +[netdata-edge] +name=Netdata Edge +baseurl=https://packagecloud.io/netdata/netdata-edge/fedora/$releasever/$basearch +repo_gpgcheck=1 +gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata-edge/gpgkey +enabled=1 +sslverify=1 +sslcacert=/etc/pki/tls/certs/ca-bundle.crt +priority=50 + +[netdata-repoconfig] +name=Netdata Repository Config +baseurl=https://packagecloud.io/netdata/netdata-repoconfig/fedora/$releasever/$basearch +repo_gpgcheck=1 +gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata-repoconfig/gpgkey +enabled=1 +sslverify=1 +sslcacert=/etc/pki/tls/certs/ca-bundle.crt +priority=50 diff --git a/packaging/repoconfig/netdata-edge.repo.ol b/packaging/repoconfig/netdata-edge.repo.ol new file mode 100644 index 0000000..1d1ea40 --- /dev/null +++ b/packaging/repoconfig/netdata-edge.repo.ol @@ -0,0 +1,21 @@ +[netdata-edge] +name=Netdata Edge +baseurl=https://packagecloud.io/netdata/netdata-edge/ol/$releasever/$basearch +repo_gpgcheck=1 +gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata-edge/gpgkey +enabled=1 +sslverify=1 +sslcacert=/etc/pki/tls/certs/ca-bundle.crt +priority=50 + +[netdata-repoconfig] +name=Netdata Repository Config +baseurl=https://packagecloud.io/netdata/netdata-repoconfig/ol/$releasever/$basearch +repo_gpgcheck=1 +gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata-repoconfig/gpgkey +enabled=1 +sslverify=1 +sslcacert=/etc/pki/tls/certs/ca-bundle.crt +priority=50 diff --git a/packaging/repoconfig/netdata-edge.repo.suse b/packaging/repoconfig/netdata-edge.repo.suse new file mode 100644 index 0000000..94db12a --- /dev/null +++ b/packaging/repoconfig/netdata-edge.repo.suse @@ -0,0 +1,19 @@ +[netdata-edge] +name=Netdata Edge +baseurl=https://packagecloud.io/netdata/netdata-edge/opensuse/$releasever/$basearch +repo_gpgcheck=1 +pkg_gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata-edge/gpgkey +enabled=1 +type=rpm-md +autorefresh=1 + +[netdata-repoconfig] +name=Netdata Repoconfig +baseurl=https://packagecloud.io/netdata/netdata-repoconfig/opensuse/$releasever/$basearch +repo_gpgcheck=1 +pkg_gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata-repoconfig/gpgkey +enabled=1 +type=rpm-md +autorefresh=1 diff --git a/packaging/repoconfig/netdata-repo.spec b/packaging/repoconfig/netdata-repo.spec new file mode 100644 index 0000000..3e5f66b --- /dev/null +++ b/packaging/repoconfig/netdata-repo.spec @@ -0,0 +1,102 @@ +%{?rhel:%global centos_ver %rhel} + +Name: netdata-repo +Version: 1 +Release: 2 +Summary: Netdata stable repositories configuration. + +Group: System Environment/Base +License: GPLv2 + +Source0: netdata.repo.fedora +Source1: netdata-edge.repo.fedora +Source2: netdata.repo.suse +Source3: netdata-edge.repo.suse +Source4: netdata.repo.centos +Source5: netdata-edge.repo.centos +Source6: netdata.repo.ol +Source7: netdata-edge.repo.ol + +BuildArch: noarch + +%if 0%{?centos_ver} && 0%{?centos_ver} < 8 +Requires: yum-plugin-priorities +%endif + +# Overlapping file installs +Conflicts: netdata-repo-edge + +%description +This package contains the official Netdata package repository configuration for stable versions of Netdata. + +%prep +%setup -q -c -T + +%if 0%{?fedora} +install -pm 644 %{SOURCE0} ./netdata.repo +install -pm 644 %{SOURCE1} ./netdata-edge.repo +%endif + +%if 0%{?suse_version} +install -pm 644 %{SOURCE2} ./netdata.repo +install -pm 644 %{SOURCE3} ./netdata-edge.repo +%endif + +%if 0%{?centos_ver} +install -pm 644 %{SOURCE4} ./netdata.repo +install -pm 644 %{SOURCE5} ./netdata-edge.repo +%endif + +%if 0%{?oraclelinux} +install -pm 644 %{SOURCE6} ./netdata.repo +install -pm 644 %{SOURCE7} ./netdata-edge.repo +%endif + +%build +true + +%install +rm -rf $RPM_BUILD_ROOT + +%if 0%{?suse_version} +install -dm 755 $RPM_BUILD_ROOT%{_sysconfdir}/zypp/repos.d +install -pm 644 netdata.repo $RPM_BUILD_ROOT%{_sysconfdir}/zypp/repos.d +install -pm 644 netdata-edge.repo $RPM_BUILD_ROOT%{_sysconfdir}/zypp/repos.d +%else +install -dm 755 $RPM_BUILD_ROOT%{_sysconfdir}/yum.repos.d +install -pm 644 netdata.repo $RPM_BUILD_ROOT%{_sysconfdir}/yum.repos.d +install -pm 644 netdata-edge.repo $RPM_BUILD_ROOT%{_sysconfdir}/yum.repos.d +%endif + +%clean +rm -rf $RPM_BUILD_ROOT + +%files +%if 0%{?suse_version} +%attr(644,root,root) /etc/zypp/repos.d/netdata.repo +%else +%attr(644,root,root) /etc/yum.repos.d/netdata.repo +%endif + +%package edge +Summary: Netdata nightly repositories configuration. +Group: System Environment/Base + +# Overlapping file installs +Conflicts: netdata-repo + +%description edge +This package contains the official Netdata package repository configuration for nightly versions of Netdata. + +%files edge +%if 0%{?suse_version} +%attr(644,root,root) /etc/zypp/repos.d/netdata-edge.repo +%else +%attr(644,root,root) /etc/yum.repos.d/netdata-edge.repo +%endif + +%changelog +* Mon Jun 6 2022 Austin Hemmelgarn <austin@netdata.cloud> 1-2 +- Bump release to keep in sync with DEB package. +* Mon Jun 14 2021 Austin Hemmelgarn <austin@netdata.cloud> 1-1 +- Initial revision diff --git a/packaging/repoconfig/netdata.list.in b/packaging/repoconfig/netdata.list.in new file mode 100644 index 0000000..9c3ddba --- /dev/null +++ b/packaging/repoconfig/netdata.list.in @@ -0,0 +1,2 @@ +deb https://packagecloud.io/netdata/netdata__VARIANT__/__DISTRO__/ __SUITE__ main +deb https://packagecloud.io/netdata/netdata-repoconfig/__DISTRO__/ __SUITE__ main diff --git a/packaging/repoconfig/netdata.repo.centos b/packaging/repoconfig/netdata.repo.centos new file mode 100644 index 0000000..d9cb2bc --- /dev/null +++ b/packaging/repoconfig/netdata.repo.centos @@ -0,0 +1,21 @@ +[netdata] +name=Netdata +baseurl=https://packagecloud.io/netdata/netdata/el/$releasever/$basearch +repo_gpgcheck=1 +gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata/gpgkey +enabled=1 +sslverify=1 +sslcacert=/etc/pki/tls/certs/ca-bundle.crt +priority=50 + +[netdata-repoconfig] +name=Netdata Repository Config +baseurl=https://packagecloud.io/netdata/netdata-repoconfig/el/$releasever/$basearch +repo_gpgcheck=1 +gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata-repoconfig/gpgkey +enabled=1 +sslverify=1 +sslcacert=/etc/pki/tls/certs/ca-bundle.crt +priority=50 diff --git a/packaging/repoconfig/netdata.repo.fedora b/packaging/repoconfig/netdata.repo.fedora new file mode 100644 index 0000000..82ec6ea --- /dev/null +++ b/packaging/repoconfig/netdata.repo.fedora @@ -0,0 +1,21 @@ +[netdata] +name=Netdata +baseurl=https://packagecloud.io/netdata/netdata/fedora/$releasever/$basearch +repo_gpgcheck=1 +gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata/gpgkey +enabled=1 +sslverify=1 +sslcacert=/etc/pki/tls/certs/ca-bundle.crt +priority=50 + +[netdata-repoconfig] +name=Netdata Repository Config +baseurl=https://packagecloud.io/netdata/netdata-repoconfig/fedora/$releasever/$basearch +repo_gpgcheck=1 +gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata-repoconfig/gpgkey +enabled=1 +sslverify=1 +sslcacert=/etc/pki/tls/certs/ca-bundle.crt +priority=50 diff --git a/packaging/repoconfig/netdata.repo.ol b/packaging/repoconfig/netdata.repo.ol new file mode 100644 index 0000000..763504b --- /dev/null +++ b/packaging/repoconfig/netdata.repo.ol @@ -0,0 +1,21 @@ +[netdata] +name=Netdata +baseurl=https://packagecloud.io/netdata/netdata/ol/$releasever/$basearch +repo_gpgcheck=1 +gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata/gpgkey +enabled=1 +sslverify=1 +sslcacert=/etc/pki/tls/certs/ca-bundle.crt +priority=50 + +[netdata-repoconfig] +name=Netdata Repository Config +baseurl=https://packagecloud.io/netdata/netdata-repoconfig/ol/$releasever/$basearch +repo_gpgcheck=1 +gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata-repoconfig/gpgkey +enabled=1 +sslverify=1 +sslcacert=/etc/pki/tls/certs/ca-bundle.crt +priority=50 diff --git a/packaging/repoconfig/netdata.repo.suse b/packaging/repoconfig/netdata.repo.suse new file mode 100644 index 0000000..55ad73e --- /dev/null +++ b/packaging/repoconfig/netdata.repo.suse @@ -0,0 +1,19 @@ +[netdata] +name=Netdata +baseurl=https://packagecloud.io/netdata/netdata/opensuse/$releasever/$basearch +repo_gpgcheck=1 +pkg_gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata/gpgkey +enabled=1 +type=rpm-md +autorefresh=1 + +[netdata-repoconfig] +name=Netdata Repoconfig +baseurl=https://packagecloud.io/netdata/netdata-repoconfig/opensuse/$releasever/$basearch +repo_gpgcheck=1 +pkg_gpgcheck=0 +gpgkey=https://packagecloud.io/netdata/netdata-repoconfig/gpgkey +enabled=1 +type=rpm-md +autorefresh=1 diff --git a/packaging/version b/packaging/version new file mode 100644 index 0000000..094f172 --- /dev/null +++ b/packaging/version @@ -0,0 +1 @@ +v1.37.1 |
